We may not have the course you’re looking for. If you enquire or give us a call on 01344203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

The digital world offers incredible speed and convenience, but it also hides constant risks. Every click, connection, and transaction carries the possibility of evolving cyber threats. When a cyberattack strikes, every second counts. This is where robust Incident Response comes in, acting as your safeguard and working like a digital fire brigade rushing in to contain the chaos before it spreads.
So, what does Incident Response really involve? It is more than just a technical fix; it is a coordinated strategy built on preparation, rapid action, and smart recovery. In this blog, you will explore its key phases and the advanced technologies that power it, giving your organisation the resilience to face any cyber challenge.
Table of Contents
1) What is Incident Response?
2) What is an Incident Response Plan (IRP)?
3) Why is an Incident Response Important?
4) The Six Phases of the Incident Response Lifecycle
5) Incident Response Technologies
6) What are Incident Response Services?
7) Incident Response Automation
8) Conclusion
What is Incident Response?
Incident Response, also known as Cyber Security Incident Response, is the process that an organisation uses to detect and respond to cyber threats, breaches or attacks. A well-defined Incident Response plan helps teams quickly contain the issues and reduce potential damage.
Its main goal is to prevent cyberattacks and minimise their impact on business operations and costs. While Incident Response focuses on the technical aspects of handling security incidents, overall Incident Management also involves leadership, HR and legal teams in addressing major situations.
What is an Incident Response Plan (IRP)?
An Incident Response Plan refers to a detailed document which outlines the steps to follow during each phase of an Incident Response. It defines the roles, responsibilities, communication methods, and standard procedures for handling security incidents. This plan must use clear and consistent language to avoid confusion with similar terms. Three key terms to define are:
1) Event: Any change in system status, settings or communication, such as a server request or data deletion.
2) Alert: A notification triggered by an event, indicating unusual or important activity, like an unused port being accessed or low storage space.
3) Incident: An event that poses a threat to the system, such as stolen credentials or malware installation.
Why is an Incident Response Important?
Without a strong Incident Response process, organisations are often caught off guard when security incidents occur. This can result in poorly coordinated efforts, longer recovery times, financial loss, and serious reputational damage. Below are the key reasons why Incident Response is so important:
1) Incident Response goes beyond quick technical fixes and supports wider business continuity.
2) It allows response strategies to match the organisation’s specific risk tolerance.
3) It connects technical teams with leadership for faster and better decision-making.
4) It reduces downtime, operational disruption, and financial or data losses.
5) It shows regulators, customers, and investors that the organisation can manage incidents effectively.
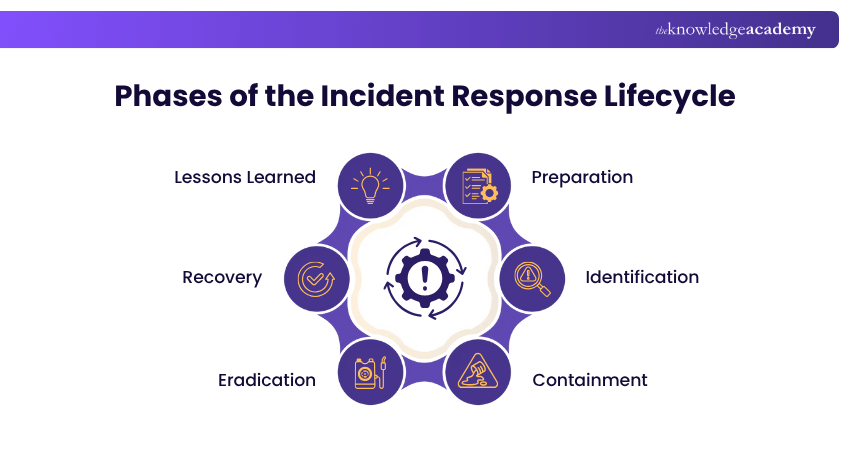
The Six Phases of the Incident Response Lifecycle
The Incident Response life cycle is made up of six key phases. These provide a structured way for organisations to react to and recover from Cyber Security incidents. Let's explore them:
1) Preparation
This phase involves:
1) Developing clear policies, procedures, and tools to support effective Incident Response.
2) Creating a detailed Incident Response plan outlining the steps to take during an incident.
3) Using plan templates to suit the organisation’s specific structure and requirements.
4) Establishing a dedicated Incident Response team with defined roles and responsibilities.
5) Setting up communication channels and escalation procedures for efficient coordination.
6) Implementing security monitoring systems to detect potential threats early.
7) Deploying detection and analysis tools to identify and assess suspicious activities.
2) Identification
The second phase involves:
1) Detecting and classifying potential security incidents based on their severity levels.
2) Monitoring systems, applications and networks continuously for unusual activity.
3) Collecting and analysing security logs, alerts and event data to identify possible threats.
4) Triaging incidents to determine their nature, urgency, and impact.
5) Prioritising incidents using predefined criteria to ensure timely and effective response.
Learn to break barriers and build stronger defences with our Ethical Hacking Professional Course – Sign up now!
3) Containment
This is what needs to be done in this phase:
1) Focusing on limiting the spread of the security incident.
2) Implementing short-term containment measures, such as isolating affected systems or devices.
3) Applying long-term strategies to strengthen defences and prevent recurrence.
4) Blocking malicious traffic, suspicious connections and unauthorised access attempts.
5) Applying necessary security patches and updates to close Vulnerabilities in Cyber Security.
6) Collecting and preserving digital evidence for detailed investigation and analysis.
4) Eradication
The eradication phase entails the following:
1) Determining the incident's root cause of to prevent it from recurring.
2) Removing malware, infected files and any malicious code from affected systems.
3) Closing vulnerabilities and patching security gaps that allowed the breach to occur.
4) Resetting user passwords and revoking any compromised credentials.
5) Rebuilding or restoring affected systems using clean and verified backups.
6) Verifying that the environment is completely free from threats before moving to recovery.
5) Recovery
This penultimate phase involves the following:
1) Restoring systems, data and configurations from secure and verified backups.
2) Testing and validating the integrity and functionality of restored systems.
3) Monitoring systems closely for any signs of re-infection or lingering vulnerabilities.
4) Ensuring normal operations resume safely and securely.
5) Communicating recovery progress and final resolution to stakeholders and management.
6) Documenting all actions taken during recovery for future reference and improvement.
6) Lessons Learned
This is the final and it involves the following:
1) Conducting a post-incident review to evaluate how the response was handled.
2) Analysing strengths, weaknesses and areas for improvement across the Incident Response process.
3) Updating Incident Response plans and documentation based on the findings.
4) Providing additional training and resources to strengthen the response team’s skills.
5) Using IT Service Management (ITSM) tools to automate response workflows.
6) Improving coordination and response speed across all six phases of the Incident Response life cycle.
Keep cyber chaos at bay with our Cyber Security Training - Sign up now and master the art of digital defence!
Incident Response Technologies
An effective Incident Response plan not only defines the steps for handling security incidents but also specifies the technologies and tools used to automate and streamline key workflows. Below are some of the most widely used Incident Response technologies:
1) User and Entity Behaviour Analytics (UEBA)
UEBA tools use Machine Learning and behavioural analytics to detect unusual activity by users or devices. They are handy for identifying insider threats or attackers using stolen credentials. They often integrate with SIEM, EDR and XDR systems for deeper analysis.
2) Extended Detection and Response (XDR)
XDR brings a unified approach to the table regarding threat detection and threat response. They are ideal to handle an organisation’s hybrid environment. By integrating data from numerous security tools and sources, XDR eliminates silos and automates the responses across the threat landscape.
3) Attack Surface Management (ASM)
Attack Surface Management tools automate the continuous discovery and remediation of vulnerabilities across all digital assets. They help identify unmonitored systems, uncover hidden network connections and map relationships between assets to reduce exposure to attacks.
4) Endpoint Detection and Response (EDR)
EDR solutions protect endpoint devices against those advanced threats that bypass traditional antivirus software. They collect data from endpoints continuously, analyse it in real time to detect suspicious activity and automatically respond to prevent potential damage.

5) Security Information and Event Management (SIEM)
SIEM systems gather and correlate data from multiple sources like firewalls, vulnerability scanners and network devices. By consolidating alerts, SIEM helps security teams reduce alert fatigue and focus on genuine threats that require urgent attention.
6) Security Orchestration, Automation and Response (SOAR)
SOAR platforms help security teams create automated playbooks that coordinate multiple security tools and actions during an incident. These platforms improve the efficiency by standardising workflows and automating repetitive response tasks where possible.
What are Incident Response Services?
Incident Response Services are specialised solutions designed to support an organisation’s internal security team. These services are typically offered on a retainer basis with a monthly fee and a defined scope of support. Most providers operate under a Service Level Agreement (SLA). Here’s how these services are delivered:
1) Incident Response Playbooks
In Incident Response, playbooks can serve as scripts that outline the exact steps to take when managing security incidents. These playbooks can be followed manually by team members or executed automatically by security systems. Playbooks can be used for:
1) Manual Processes: They provide step-by-step guidance on which tools to use, what actions to take and who is responsible for each task. These are typically documented digitally or in print.
2) Automated Processes: They function as coded workflows integrated into security systems. When an alert is triggered, the playbook automatically executes predefined actions such as isolating endpoints or blocking IPs.
2) Incident Response Platforms
Beyond the playbooks, organisations can improve their security operations with Incident Response platforms. These are software solutions designed to assist every stage of the response process. These platforms integrate with existing tools and provide a centralised environment for managing incidents. Here are the key features of Incident Response platforms:

Incident Response Automation
Speed and precision are necessary elements of Incident Response because teams must quickly detect threats and activate response plans. However, investigating every single alert in real time can be an uphill battle as it can lead to delayed detection or missed incidents, causing greater damage. By automating various parts of the Incident Response process, you can reduce response times and human error.
Automation can perform the following functions:
1) Rapidly triage alerts to identify real incidents.
2) Collect and centralise key data for faster investigations.
3) Execute response actions, such as isolating affected systems or blocking malicious IP addresses.
Conclusion
More than just a recovery plan, Incident Response is a mindset that breeds readiness and resilience. By understanding its phases and leveraging the associated advanced technologies, organisations can turn any bit of chaos into lasting control. A strong Incident Response strategy preserves trust and ensures that the business bounces back stronger after every challenge.
Incident reporting starts with awareness and ends with action. Master the whole process in our Incident Reporting Training - Sign up now!
Frequently Asked Questions
What is the Blue Team in Incident Response?

The Blue Team refers to a group of Cyber Security professionals who defend an organisation’s networks and systems against a range of attacks. They identify and respond to security incidents in real time. Their goal is to detect vulnerabilities and ensure that the organisation is always prepared to fend off cyber threats.
What is an Incident Response Plan Template?

An Incident Response Plan Template is a pre-structured document. It outlines how to prepare for, detect, respond to and recover from various Cyber Security incidents. It defines the roles, communication protocols and response actions in a step-by-step manner. Organisations use it as a framework to build customised plans to fit their specific security environment.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 19 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Training, including the Incident Response Training, Incident Reporting training and the Cyber Security Risk Management Course. These courses cater to different skill levels, providing comprehensive insights into Spyware.
Our IT Security & Data Protection Blogs cover a range of topics related to Incident Response, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Incident Response knowledge, The Knowledge Academy's diverse courses and informative blogs have got you covered.
Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Incident Response Training
Incident Response Training
Fri 17th Apr 2026
Fri 14th Aug 2026
Fri 27th Nov 2026







 Top Rated Course
Top Rated Course



 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


