We may not have the course you’re looking for. If you enquire or give us a call on 01344203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.
Every organisation handling sensitive data needs a clear way to show how it protects that information. That’s where the ISO 27001 Statement of Applicability comes in. It's not just paperwork; It’s a smart, structured record of your chosen security controls and the reasons behind them.
Whether you're preparing for certification or simply enhancing your ISMS, the ISO 27001 Statement of Applicability is a must-have. It helps you stay compliant, clearly communicate your risk decisions, and prove you're serious about information security. In this blog, we’ll breakdown how it works and why it’s such a vital part of the ISO 27001 journey.
Table of Contents
1) What is the ISO 27001 Statement of Applicability?
2) Why is the ISO 27001 Statement of Applicability important?
3) ISO 27001 Control List and Its Applications
4) How to Write an ISO 27001 Statement of Applicability?
5) ISO 27001 Statement of Applicability Example
6) How Often Should the SoA Be Updated?
7) Can I Remove Controls from the ISO 27001 Statement of Applicability?
8) Conclusion
What is the ISO 27001 Statement of Applicability?
The ISO 27001 Statement of Applicability (SoA) is a key document that outlines the security controls from Annex A of the ISO 27001 standard. It identifies which controls are applied within your organisation and which are excluded, along with clear reasons based on risk assessment and business needs.
As an essential part of the Information Security Management System (ISMS), the SoA provides visibility into how selected controls address identified risks. It also serves as important evidence during audits, helping organisations demonstrate compliance and maintain a transparent and structured approach to information security.
Why is the ISO 27001 Statement of Applicability important?
The ISO 27001 Statement of Applicability is crucial because it connects your risk assessment to the specific controls your organisation employs. It ensures that your information security measures are relevant and well-documented.
Key Reasons Why the ISO 27001 SoA is Important:
a) Demonstrates Compliance: Serves as formal evidence during audits to show alignment with ISO 27001 requirements.
b) Links Risks to Controls: Clearly connects identified risks with the selected Annex A controls.
c) Provides Justification: Explains why each control is included or excluded, supporting transparency.
d) Supports Audits and Reviews: Facilitates easier and more effective internal and external assessments.
e) Clarifies Implementation: Shows the current status of each control implemented, planned, or not applicable.
f) Assigns Accountability: Identifies responsible individuals or teams for each control.
g) Aligns with Business Needs: Ensures controls reflect your organisation’s unique risk environment.
h) Improves Governance: Enhances visibility and informed decision-making within the ISMS framework.
Take control of your organisation's Information security with our ISO 27001 Internal Auditor Course - register now!
ISO 27001 Control List and Its Applications
Within ISO 27001, there is a set of controls, specifically in Annex A, that organisations can use to address various Information security risks. These controls are divided into 14 categories, each addressing a different aspect of information security. Here is a list of controls in ISO 27001 along, with their general uses:
1) Information Security Policies (A.5): Defines and communicates information security policies and objectives.
2) Organisation of Information Security (A.6): Establishes roles and responsibilities to maintain information security within the organisation.
3) Human Resource Security (A.7): Ensures employees and contractors are aware of and compliant with security policies.
4) Asset Management (A.8): Identifies, classifies, and manages information assets effectively.
5) Access Control (A.9): Controls access to information systems and data, ensuring authorised access and preventing unauthorised access.
6) Cryptography (A.10): Protects sensitive information through encryption and cryptographic controls.
7) Physical and Environmental Security (A.11): Secures physical facilities and equipment to prevent unauthorised access, damage, or interference.
8) Operations Security (A.12): Ensures the secure operation of information systems and data.
9) Communications Security (A.13): Protects the confidentiality and integrity of data during transmission.
10) System Acquisition, Development, and Maintenance (A.14): Integrates security into the Software Development Lifecycle and procurement processes.
11) Supplier Relationships (A.15): Ensures that suppliers and third-party partners meet Information security requirements.
12) Information Security Incident Management (A.16): Establishes an incident response plan to properly address security breaches and incidents.
13) Information Security Continuity (A.17): Develops and maintains business continuity and disaster recovery plans.
14) Compliance (A.18): Ensures compliance with legal, regulatory, and contractual requirements concerned with Information security.
Want to gain the expertise to lead and conduct a successful ISO 27001 audit? Sign up for our ISO 27001 Lead Auditor Course today!
How to Write an ISO 27001 Statement of Applicability?
Now that we have discussed what a Statement of Applicability is, why it is essential and what it should include, we will now discuss the steps to write one.
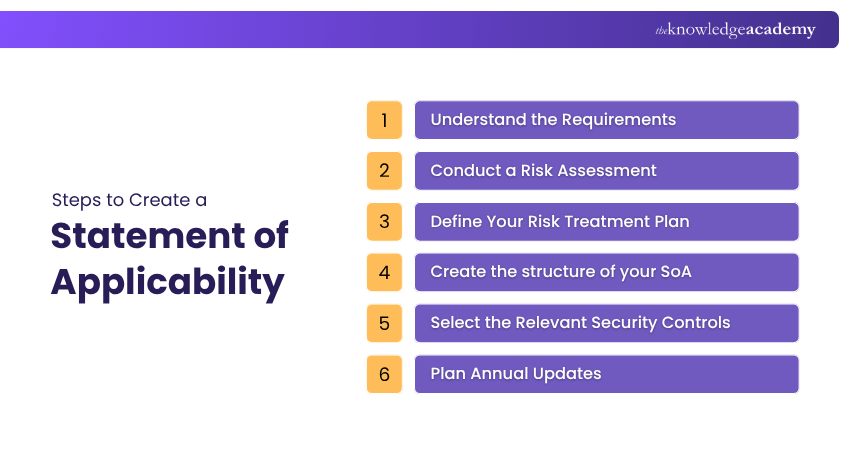
1) Understand the Requirements
The first step to writing an effective ISO 27001 Statement of Applicability is understanding the requirements that can be overwhelming if one is new to ISO 27001 Checklist or Information security standards in general. Nevertheless, a comprehensive understanding of these requirements will help ensure that your Statement of Applicability is accurate and complete.
2) Conduct a Risk Assessment
Before preparing an ISO 27001 Statement of Applicability, it is important to carry out a thorough risk assessment. This step helps identify and evaluate potential information security risks that could impact your organisation. If a risk assessment has already been completed, its findings can be used as a foundation to support the SoA.
3) Define Your Risk Treatment Plan
At this stage, you establish how identified risks will be managed by defining an appropriate risk treatment approach. This includes selecting suitable security controls, such as encryption or access controls, to reduce or mitigate risks effectively. By aligning these measures with your risk assessment, you can clearly determine which controls are required to protect your organisation’s information systems.
4) Create the structure of your SoA
In this step, you organise your Statement of Applicability into a clear and structured format. This typically includes listing all Annex A controls, indicating whether each control is applicable or not, providing justification for inclusion or exclusion, and noting the implementation status. A well-structured SoA ensures clarity, supports audits, and makes it easier to track how controls are applied across your organisation.
5) Select the Relevant Security Controls
Every organisation is different, meaning that it has its unique set of risks to which it is most vulnerable. This, in turn, means that every organisation will have a unique set of controls that it will have to adopt to strengthen its ISO 27001 Physical Security against potential risks.
For instance, if you run a large manufacturing business with multiple warehouses where inventory is always being shipped out or returned to storage, the physical access controls could be a part of your ISO 27001 Statement of Applicability. However, other companies may find that they do not face many physical security risks and that another set of controls is at the top of their priority list.
6) Plan Annual Updates
Planning annual updates for the Statement of Applicability is important to ensure it remains accurate and aligned with your organisation's evolving needs. As business operations, regulatory requirements, and risk profiles change over time, regular reviews become crucial.
These updates help confirm that selected controls remain relevant, ownership is current, and all changes are properly documented. Additionally, they support smoother ISO 27001 requirements, surveillance audits and re-certification processes.
Want to elevate your organisation's Cyber Security practices? Register for our industry-leading ISO 27001 Internal Auditor Course - today!
ISO 27001 Statement of Applicability Example
An ISO 27001 Statement of Applicability (SoA) example typically presents a structured list of all Annex A controls, showing whether each control is applicable, along with a clear justification and its implementation status. It acts like a checklist that explains which security measures an organisation has chosen and why certain controls are excluded based on risk and business needs.
In practice, an SoA example often includes columns such as control ID, control name, applicability (yes or no), justification, and implementation status. This format helps organisations clearly demonstrate how their selected controls address specific risks and provides auditors with a transparent view of their information security approach.
How Often Should the SoA Be Updated?
The Statement of Applicability (SoA) should be reviewed and updated at least once a year to ensure it remains aligned with your organisation’s current risk environment and security controls.
In addition, updates should be made whenever there are significant changes such as new risks, business or technology updates, audit findings, or security incidents. Keeping the SoA regularly updated helps maintain compliance and ensures your ISMS reflects the latest security requirements.
Can I Remove Controls from the ISO 27001 Statement of Applicability?
Yes, you can exclude controls from the ISO 27001 Statement of Applicability, but only if they are justifiably not applicable based on your organisation’s risk assessment, legal, regulatory, or contractual requirements. Properly conducting and documenting this process often starts with how you Develop an Asset Inventory for ISO 27001, ensuring each exclusion is clearly recorded and explained in the SoA.
Conclusion
A well-presented and easy-to-understand about What is ISO 27001 Statement of Applicability shows the relationship between the relevant and implemented Annex A controls given the risks and information assets in the Scope. It assures an Auditor or any other interested party that an organisation is taking its Information security Management seriously, especially if it is all joined into a holistic information security Management System.
Take the first step towards securing your organisation's information with our comprehensive ISO 27001 Foundation Course.
Frequently Asked Questions
What Documents Do Certification Bodies Require for ISO 27001 SoA?

Certification bodies typically require the ISO 27001 Statement of Applicability (SoA). It lists all Annex A controls, states their applicability, explains exclusions, and shows implementation status aligned with the risk assessment and treatment plan.
What’s the Difference Between ISO 27001 SoA and Scope?

The Scope of ISO 27001 defines the boundaries of the Information Security Management System (ISMS), specifying what parts of the organisation, assets, and processes are covered. The Statement of Applicability (SoA) lists the security controls chosen, justifies their inclusion or exclusion, and other details of their implementation status.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various ISO 27001 Training Courses, including the ISO 27001 Foundation Course, ISO 27001 Lead Auditor, and ISO 27001 Internal Auditor. These courses cater to different skill levels, providing comprehensive insights into Compliance Objectives: Features, Benefits & Use Cases.
Our ISO & Compliance Blogs cover a range of topics related to certification and regulatory standards, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your compliance skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

The Knowledge Academy is a world-leading provider of professional training courses, offering globally recognised qualifications across a wide range of subjects. With expert trainers, up-to-date course material, and flexible learning options, we aim to empower professionals and organisations to achieve their goals through continuous learning.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 ISO 27001 Foundation
ISO 27001 Foundation
Mon 6th Jul 2026
Mon 3rd Aug 2026
Mon 7th Sep 2026
Mon 5th Oct 2026
Mon 2nd Nov 2026
Mon 7th Dec 2026





 Top Rated Course
Top Rated Course








 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


