We may not have the course you’re looking for. If you enquire or give us a call on 01344203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Ensuring the security of your company's assets starts by having a clear understanding of what you possess and where is it. How can this be accomplished? That is when an Asset Inventory for ISO 27001 steps in. This isn't just a basic list; rather, it's a tactical instrument created to protect your business.
An Asset Inventory extends beyond just listing hardware and software items. It consists of essential details, important staff members, and all critical resources in your company. Every asset is given a specific owner who oversees its safety and quality. This stockpile acts as your primary defence, allowing you to efficiently control risks and safeguard confidential information.
This inventory serves as the cornerstone of a strong Information Security Management System (ISMS), going beyond just a form of protection. It assists in guaranteeing that your company complies with regulations and maintains a robust, secure defence against possible dangers.
Are you prepared to improve your company's security measures? Begin by creating a detailed Asset Inventory. This blog will walk you through the required steps to guard your assets and ensure the security of your business.
Table of Contents
1) What are Assets According to ISO 27001?
2) Why are Assets Important for Information Security Management?
3) Steps to Create an Asset Inventory for ISO 27001
4) Who Should Be the Asset Owner?
5) What are the Four Domains of ISO 27001?
6) What are the Three P's of ISO 27001?
7) Conclusion
What are Assets According to ISO 27001?
In the context of ISO 27001, assets are defined as anything valuable to an organisation that requires protection as part of its information security efforts. These assets can be both physical and digital, encompassing hardware, software, information, people, services, and even locations.
The standard underscores that an effective Information Security Management System (ISMS) starts with identifying all assets involved in storing, processing, or transmitting sensitive information. A thorough asset inventory ensures that every item or component that could impact information security is accounted for. This comprehensive approach facilitates better risk assessment, control implementation, and ongoing monitoring.
Here are the key types of assets under ISO 27001:
a) Hardware: Servers, laptops, mobile devices, network equipment
b) Software: Operating systems, applications, productivity tools
c) Information: Paper documents, digital records, databases
d) People: Employees, contractors, consultants with access to sensitive data
e) Services: Internal and third-party services like cloud storage or email hosting
f) Locations: Physical premises, remote work environments, data centres
Why are Assets Important for Information Security Management?
Assets are essential to Information Security Management as they encompass the components that store, access, or process valuable information. Without identifying these assets, an organisation cannot effectively assess security risks or implement necessary protective measures. ISO 27001 emphasises the importance of creating a detailed asset inventory, which forms the basis for risk assessments and the broader Information Security Management System (ISMS).
Understanding Assets Helps Organisations:
a) Identify vulnerabilities in people, systems, or processes
b) Understand how threats could exploit those vulnerabilities
c) Evaluate the possibility and consequences of potential security incidents
d) Apply targeted security controls to mitigate risks
Here’s Why This is so Important:
a) Supports Risk Management: Assets are directly linked to the risk assessment process. Knowing what you have helps determine what can go wrong and how to prevent it.
b) Improves Decision-making: A clear view of assets enables better resource allocation for security initiatives.
c) Helps Meet ISO 27001 Requirements: Developing and maintaining an asset inventory is essential for certification.
d) Enhances Incident Response: When incidents occur, knowing which assets are affected allows for faster and more effective response.
Steps to Create an Asset Inventory for ISO 27001
Let'sdive deeper into the steps involved in creating an Asset Inventory for ISO 27001, focusing on the specific actions and considerations at each stage:
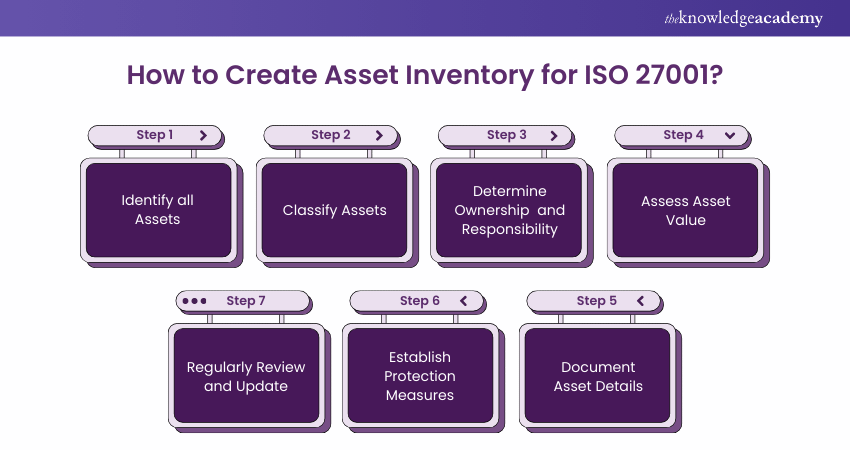
Step 1: IdentifyAll Assets
To build a robust Asset Inventory for ISO 27001 Compliance, start by conducting a comprehensive assessment. Form a cross-functional team involving IT, operations, finance, legal, and other relevant departments to ensure all Assets are accounted for. Interviews with key personnel are vital, including IT staff, department heads, and end-users who utilise Assets. Review existing records, contracts, and documentation like invoices and procurement records.
Additionally, physical inspections are performed to identify hardware assets that are not documented elsewhere. Leverage Asset Management software and tools to scan and recognise digital Assets such as software, databases, and configurations. This holistic approach ensures no Asset is overlooked.
Unlock the Secrets to ISO 27001 Success with our ISO 27001 Foundation Course - Register now!
Step 2: Classify Assets
Once you've compiled a comprehensive list of Assets, the next step is classification. ISO 27001 suggests categorising Assets into types such as hardware, software, data, personnel, and facilities. Each Asset should be designated with a unique identifier to facilitate tracking and management. This classification is instrumental in prioritising Assets for security measures and resource allocation.
By distinguishing between hardware, software, data, and other Asset types, organisations can tailor their security measures to address the particular vulnerabilities and threats associated with each category. This step is essential for establishing a strong foundation for effective asset management and protection.
Step 3: DetermineOwnership and Responsibility
Assigning ownership and responsibility is pivotal to establishing accountability for Asset security and maintenance. Clearly identify individuals or departments responsible for owning each Asset. Ownership implies the authority to make decisions regarding the Asset. Beyond ownership, define specific roles and responsibilities associated with each Asset.
IT staff may be responsible for maintenance, while security teams oversee data protection. End-users may have responsibilities related to adhering to security policies. This step ensures that everyone involved in Asset Management understands their role, fostering a culture of responsibility and accountability. Effective Asset ownership and responsibility enhance the security posture of the organisation.
Boost your organisation's cybersecurity with your choice from our extensive ISO 27001 Courses - sign up now!
Step 4: Assess Asset Value
Assessing the value of Assets to the organisation is vital for prioritisation and resource allocation. Asset value encompasses financial, reputational, legal, and operational dimensions. Financially, calculate the Asset's cost, replacement value, and potential repair expenses. Consider how the loss of an Asset could impact the organisation's reputation and brand.
Evaluate whether Assets are subject to legal requirements or industry regulations, as non-compliance may result in fines and legal issues. Additionally, gauge the operational importance of Assets. Some Assets are critical for business continuity, making them top priorities for protection. Understanding Asset value guides effective decision-making in security measures and risk management.
Step 5: Document Asset Details
Creating detailed records for each Asset is essential for comprehensive Asset Management. Documentation should be accurate, up-to-date, and easily accessible to relevant stakeholders. Each Asset should have a unique identifier, such as a serial number or Asset tag. Descriptions should be detailed, encompassing make, model, configuration, and specifications.
Physical location must be documented to facilitate Asset tracking. Version or configuration details are crucial, especially for software and hardware. Note down the security controls in place for each Asset, including access controls, encryption, and monitoring. This detailed documentation makes sure that all stakeholders have access to the essential information required for Asset Management and protection.
Step 6: Establish Protection Measures
These measures should align with the organisation's overarching security policy. They may encompass various aspects of security, including access controls, encryption, regular backups, security patching, and monitoring systems.
Tailor security measures to the unique attributes and importance of each Asset. Critical Assets may require more robust protection, while less critical ones may need lighter controls. The goal is to create a layered security approach that adequately safeguards Assets against potential threats and vulnerabilities. Adequate protection measures are crucial for maintaining the confidentiality, integrity, and availability of Assets.
Step 7: Regularly Review and Update
An Asset Inventory is a document that requires continuous attention and maintenance. It should undergo regular reviews and updates to remain accurate and effective. Document any changes or additions to Assets as they occur. This could include acquiring new Assets, decommissioning old ones, or modifying existing configurations.
Conduct periodic assessments of Asset value and the effectiveness of security controls to ensure they remain accurate and appropriate. Regular security testing, like vulnerability assessments and penetration testing, helps identify and mitigate vulnerabilities promptly. These ongoing efforts ensure that the Asset Inventory remains a valuable tool in protecting the organisation's Assets and maintaining information security compliance.
Who Should Be the Asset Owner?
Under ISO 27001, an asset owner is the person accountable for ensuring an information asset is properly managed and protected. This includes making sure the asset is identified, classified, and listed in the organisation’s asset inventory. They also take part in assessing risks and are responsible for ensuring that the right security measures are in place.
This role is typically given to someone who has direct oversight or a strong understanding of the asset like a department lead, IT administrator, or someone who created or manages the information. Although they may delegate routine tasks, the asset owner remains responsible for the asset’s overall security and alignment with ISO 27001 requirements.
Key Responsibilities of an Asset Owner:
a) Identifying and registering the asset
b) Classifying the asset and assigning sensitivity levels
c) Participating in risk assessments
d) Ensuring appropriate security controls are in place
e) Managing the asset throughout its lifecycle
f) Overseeing secure disposal when the asset is no longer needed
What are the Four Domains of ISO 27001?
The four key domains of ISO 27001 are People, Processes, Technology, and Physical Infrastructure. These domains ensure a holistic approach to information security by addressing human behaviour, organisational procedures, technical controls, and physical safeguards. Together, they help protect information assets and support a robust ISMS.
What are the Three P's of ISO 27001?
The Three P’s of ISO 27001 are People, Processes, and Technology. These elements form the foundation of a strong Information Security Management System. They ensure that human factors, procedural controls, and technical measures work together to protect an organisation’s information assets effectively.
Conclusion
In conclusion, developing an Asset Inventory for ISO 27001 is more than a compliance requirement; it is a vital step in protecting your organisation’s most valuable assets. By meticulously identifying, classifying, and valuing these assets, your organisation can implement robust security measures, effectively mitigating potential threats and vulnerabilities. This proactive strategy ensures your organisation remains resilient and well-protected in an increasingly complex security landscape.
Elevate your Cyber Security skills with ourISO 27001 Lead Auditor Course – Join now!
Frequently Asked Questions
What are the Primary Assets of ISO 27001?

In ISO 27001, primary assets encompass information, people, software, hardware, services, and physical locations. These assets are vital to business operations and must be protected to ensure the confidentiality, integrity, and availability of information.
What are the Best Practices for Creating an Asset Inventory in ISO 27001?

To create an effective Asset Inventory for ISO 27001, follow these best practices:
a) Clearly define asset categories
b) Regularly update the inventory
c) Involve relevant stakeholders
d) Use automated tracking tools
e) Link all assets to specific security controls
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various ISO 27001 Training, including the ISO 27001 Foundation Course, ISO 27001 Lead Auditor Course, and ISO 27001 Internal Auditor. These courses cater to different skill levels, providing comprehensive insights into the Benefits of Compliance.
Our ISO & Compliance Blogs cover a range of topics related to ISO, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your ISO & Compliance skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

Hailey Davis is an ISO compliance expert with over 10 years of experience in audit, quality management systems (QMS), and regulatory compliance. She has worked with various industries, including manufacturing, healthcare, and technology, ensuring organisations achieve and maintain ISO certifications. Hailey’s content provides practical, actionable insights on navigating compliance challenges and improving business processes.
View Detail
Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 ISO 27001 Foundation
ISO 27001 Foundation
Mon 6th Jul 2026
Mon 3rd Aug 2026
Mon 7th Sep 2026
Mon 5th Oct 2026
Mon 2nd Nov 2026
Mon 7th Dec 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


