We may not have the course you’re looking for. If you enquire or give us a call on 01344203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

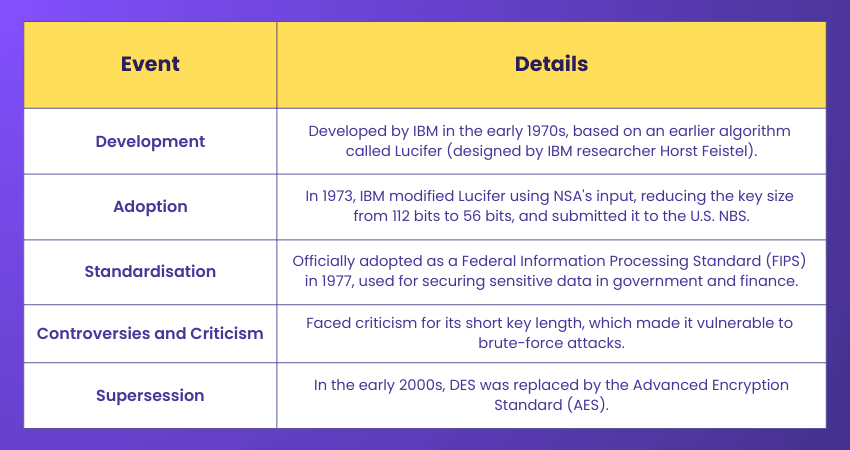
For the Data Encryption pros or general tech enthusiasts, the Data Encryption Standard (DES) is a delightful blast from the past. Once reigning as the gold standard for Encryption, DES was the go-to option for keeping information secure in the digital realm. But as technology evolved, so did the ingenuity of techniques to break its shield.
While the Data Encryption Standard is now considered outdated, its importance as the forefather of modern encryption standards can't be denied. This blog dives deep into the story of DES, spotlighting all it offered to the digital landscape at its prime. So read on and get a glimpse of a groundbreaking era in Cryptography.
Table of Contents
1) Understanding Data Encryption Standard (DES)
2) How Does DES Work?
3) The Working Mechanism of Data Encryption Standard (DES)
4) Implementing Data Encryption Standards in Your Organisation
5) Benefits of Data Encryption Standard (DES)
6) Drawbacks of the Data Encryption Standard (DES)
7) Why is DES Unsafe?
8) Successors to DES
9) Legacy of DES
10) Conclusion
Understanding Data Encryption Standard (DES)
The Data Encryption Standard is a symmetric block cipher algorithm developed by IBM. Being symmetric means the same algorithm and key are used for both encryption and decryption. The block cipher indicates it processes data in fixed-size blocks rather than bit by bit. DES encrypts data in 64-bit blocks, taking a 64-bit plaintext input and producing a 64-bit ciphertext output.
How Does DES Work?
As discussed above, DES is a symmetric block cipher, which means it uses the same secret key for both encryption and decryption. This key must be known to both the sender and the receiver. While once it was the industry standard, DES is now considered weak and has been replaced by the Advanced Encryption Standard (AES) for better security.
Key Features of Data Encryption Standard (DES)
DES has numerous distinctive features that contributed to its widespread utility:
1) Symmetric Kyptiey Encron: DES uses the same key for encryption and decryption which must be kept secret to maintain the data's security.
2) Block Cipher: DES encrypts data in chunks rather than bit by bit. It processes data in fixed-size blocks of 64 bits.
3) 56-bit Key Length: The DES algorithm uses a 56-bit key, providing a standardised method for safeguarding digital communications.
4) Feistel Structure: DES operates on a Feistel network. This network divides the data block into two halves and processes the two through multiple rounds of substitution and permutation.
The Working Mechanism of Data Encryption Standard (DES)
DES has played a significant role in securing information and systems. Though currently considered obsolete, understanding DES can still be beneficial as it's responsible for laying the groundwork for modern cryptology. The working mechanism of DES consists of processes such as Encryption, decryption and key generation, which are explained below:
1) Encryption Process
The encryption process consists of the following steps:
1) Initial Permutation (IP): First, the plaintext data is subjected to a permutation that rearranges the bits to increase diffusion.
2) Round Function (F): DES uses 16 rounds of processing, and each round involves:
a) Expansion: The right half of the data block is expanded from 32 to 48 bits.
b) Key Mixing: The expanded right half is XORed by a subkey derived from the main key.
c) Substitution: The XORed result is passed through a series of substitution boxes, called S-boxes, that reduce the 48-bit block back to 32 bits.
d) Permutation: A permutation function scrambles the bits further.
3) Swapping Halves: Following each round, the two halves of the data block are swapped.
4) Final Permutation (FP): Following the final round, the data block is subjected to a final permutation that produces the ciphertext.
2) Decryption Process
The decryption process in DES is essentially the reverse of encryption that applies the same keys in reverse order and retrieves the original plaintext from the ciphertext.
3) Key Generation
The key generation process involves creating a 56-bit key from an original 64-bit key by removing every 8th bit. This key is then utilised in various stages of the encryption and decryption processes.
Looking to mitigate the risks of digital manipulation? Sign up for our Social Engineering Training!
Implementing Data Encryption Standards in Your Organisation
Protecting sensitive information is important for every business. By using DES, you can keep your data safe from unauthorised access and ensure its confidentiality and integrity, whether it’s stored on-premises, in the cloud, or shared online. Here are the key steps to follow:
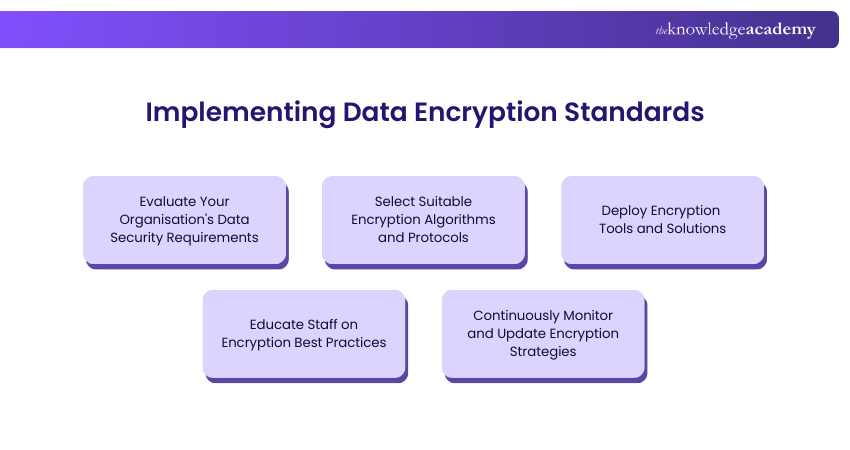
1) Identify what data your organisation uses, how sensitive it is, and what laws or rules apply before choosing encryption.
2) Choose suitable encryption methods like AES for protecting data and RSA or Elliptic Curve Cryptography (ECC) for secure communication.
3) Use encryption tools that work well with your systems and manage encryption keys safely.
4) Teach employees why encryption matters and how to use it correctly.
5) Regularly review and update the encryption methods to stay protected from new security threats.
Become an expert at identifying and mitigating digital threats with our comprehensive Cyber Security Risk Management Course - Sign up now!
Benefits of Data Encryption Standard (DES)
DES offered numerous benefits during its time, including the following:

1) Standardisation: As a federally adopted standard, DES offered a uniform method for Encryption, which simplified integration across various systems.
2) Simplicity: The block cipher structure and symmetric key approach made it relatively easy to implement and understand DES.
3) Widespread Adoption: Once DES was adopted by the National Institute of Standards and Technology (NIST), it ensured its use in diverse applications. These applications ranged from securing government communications to safeguarding financial transactions.
4) Data Confidentiality: DES keeps sensitive information safe by changing readable data (plaintext) into an unreadable format (ciphertext). Only authorised users with the suitable key can decrypt and access the original data.
5) Symmetric Key Simplicity: Since DES has the same key for both encryption and decryption, it simplifies the encryption process. This makes implementation and usage easier compared to some complex asymmetric algorithms.
Drawbacks of the Data Encryption Standard (DES)
While DES was groundbreaking for its time, it possessed significant limitations that resulted in its eventual replacement:
1) Key Length: The 56-bit key length is too short by modern standards, making DES susceptible to brute-force attacks.
2) Computational Power: Advancements in computational power have rendered DES insecure, because modern computers can quickly crack DES-encrypted data.
3) Replacement: In 2001, DES was succeeded by the AES standard, which offers longer key lengths and stronger security features.
Learn the best practices for securing digital data with our Computer Forensics Foundation Training – Join soon!
Why is DES Unsafe?
The DES is considered unsafe today due to its short key length. Although it uses a 64-bit key, only 56 bits are effective. This makes it vulnerable to brute-force attacks where attackers try every possible key. With modern computing power, DES encryption can be cracked within hours or even minutes.
Additionally, DES does not provide strong resistance against advanced cryptographic attacks like differential and linear cryptanalysis. As data volumes and security needs grew, DES could no longer meet modern security standards.
Successors to DES
To address DES’s weaknesses, several replacements were introduced. The first was Triple DES (3DES), which applies the DES algorithm three times using two or three different keys, extending the effective key length to 112–168 bits. While 3DES improved security, it is slower and still vulnerable to meet-in-the-middle attacks.
The true replacement came in 2001 with the Advanced Encryption Standard (AES), developed by the National Institute of Standards and Technology (NIST). AES offers 128-, 192-, and 256-bit keys, providing stronger security and faster performance.
Lock your digital doors before Hackers knock. Sign up for our Cyber Security Courses and stay one step ahead!
Legacy of DES
Despite being obsolete, DES played an important role in shaping modern Cryptography. Before its introduction, encryption was largely limited to military and government use. DES changed this by making encryption a public standard, encouraging professionals to study, analyse, and attempt to break the algorithm.
Its open design helped foster the growth of the Cyber Security industry and laid the foundation for advanced encryption techniques. Although no longer secure, DES’s impact on the history of Cryptography remains significant and enduring.
Conclusion
The Data Encryption Standard marked a turning point in the history of data security by introducing a widely adopted, standardised encryption method. Though it has now been replaced by stronger algorithms like Triple DES and the AES, its contribution to the development of modern Cryptography remains invaluable. It laid the foundation for today’s advanced encryption practices and inspired innovation in data protection.
Respond to cyber threats with confidence in our up-to-date Cyber Security Awareness Course - Sign up now!
Frequently Asked Questions
Which is the Most Recommended Encryption Standard?

Blowfish, Triple-DES algorithm and Advanced Encryption Standard (AES) algorithm are among the most recommended encrypted standards.
What are the Three Types of Encryption Standards?

The three main types of encryption standards are:
a) Symmetric Encryption: Examples include Advanced Encryption Standard (AES) and Triple Data Encryption Standard (3DES).
b) Asymmetric Encryption: Rivest-Shamir-Adleman(RSA) is one of the best examples.
c) Hashing: Examples include Secure Hash Algorithm (SHA) and Message Digest Algorithm 5 (MD5).
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 19 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Courses, including Introduction to System and Network Security Training, Cyber Security Awareness Course and the Fraud Analytics Training Course. These courses cater to different skill levels, providing comprehensive insights into the Cyber Resilience Framework.
Our IT Security & Data Protection Blogs cover a range of topics related to the Data Encryption Standard, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Data Protection skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

The Knowledge Academy is a world-leading provider of professional training courses, offering globally recognised qualifications across a wide range of subjects. With expert trainers, up-to-date course material, and flexible learning options, we aim to empower professionals and organisations to achieve their goals through continuous learning.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Introduction to System and Network Security
Introduction to System and Network Security
Fri 28th Aug 2026
Fri 13th Nov 2026





 Top Rated Course
Top Rated Course








 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


