We may not have the course you’re looking for. If you enquire or give us a call on 01344203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

From spotting vulnerabilities to streamlining processes, IT Auditors are the heroes behind trustworthy tech operations. They dive deep into the heart of an organisation’s IT infrastructure, ensuring compliance and fortifying digital defences. If you have the ambition of taking on this powerful role, the IT Auditor Interview Questions and answers outlined in this blog will help you out.
These IT Auditor Interview Questions will help you brush up on your IT Auditing expertise and showcase your technical expertise, analytical thinking and confidence in protecting an organisation’s digital infrastructure. So read on and shine in your next interview!
Table of Contents
1) Most Common IT Auditor Interview Questions and Answers
a) How would you define IT Auditing, and why does it play a crucial role in modern organisations?
b) What are the key responsibilities of an IT Auditor within an organisation?
c) Can you explain what Risk Assessment means in the context of IT Auditing?
d) How do internal IT Audits differ from external IT Audits?
e) Why are sampling techniques used during an IT Audit?
f) Why is compliance such an important aspect of IT Auditing?
g) What are the main components that make up a comprehensive IT Audit report?
h) Could you describe what IT General Controls (ITGCs) are and why they matter?
i) What advantages does an IT Audit bring to an organisation’s overall operations and security?
j) What are the primary categories or types of IT Audits?
2) Conclusion
Most Common IT Auditor Interview Questions and Answers
This section covers the most frequently asked IT Auditor Interview Questions and the ideal answers that will help you stand out. From technical know-how to smart Risk Assessment strategies, get ready to impress your interviewer:
How would you define IT Auditing, and why does it play a crucial role in modern organisations?

What are the key responsibilities of an IT Auditor within an organisation?

Here are the roles played by an IT Auditor in an organisation:
1) They review information systems, networks and applications to verify compliance with policies and regulations.
2) They identify potential security and operational risks within a variety of IT environments.
3) They recommend practical improvements to boost system integrity and efficiency.
4) They ensure that Cyber Security measures align with organisational and industry standards.
5) They support management in maintaining reliable, secure and compliant IT operations.
Can you explain what Risk Assessment means in the context of IT Auditing?

“Risk Assessment involves identifying and evaluating potential threats that could impact information systems. As an Auditor, I analyse the likelihood and impact of these risks, then prioritise areas that need stronger controls or immediate attention.”
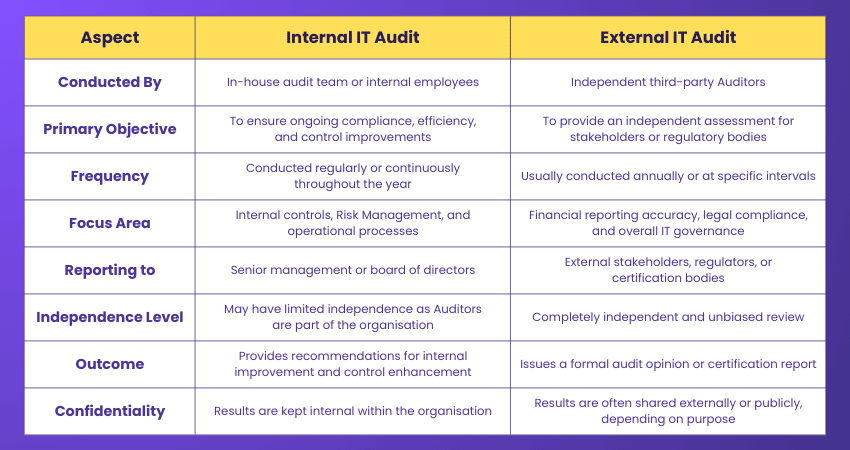
How do internal IT Audits differ from external IT Audits?

Here are the key differences between internal and external IT Audits:
Why are sampling techniques used during an IT Audit?

“Sampling helps the Auditors assess large datasets efficiently. Instead of checking every record, I can select representative samples to test for controls, accuracy and compliance. It saves time while maintaining the reliability of audits.”
Why is compliance such an important aspect of IT Auditing?

“Compliance ensures an organisation follows laws, standards, and internal policies like GDPR or ISO 27001. It’s crucial for avoiding legal penalties, maintaining trust and ensuring ethical handling of sensitive data.”
What are the main components that make up a comprehensive IT Audit report?

Here are the components of an IT Audit report:
1) Audit Scope: It defines the systems and processes covered during the audit.
2) Objectives: It outlines the key goals, such as assessing control effectiveness or compliance.
3) Findings: It summarises issues identified, control weaknesses or areas of improvement.
4) Risk Ratings: It classifies findings based on severity or business impact.
5) Recommendations: It provides actionable steps to address identified gaps and strengthen systems.
6) Management Response: It includes feedback or corrective actions proposed by management.
What are IT General Controls (ITGCs)?

“IT General Controls are foundational safeguards that ensure system integrity. They cover areas like Access Management, change control, backup procedures, and incident response, which are essentially the backbone of IT Security and governance.”
What advantages does an IT Audit bring to an organisation’s overall operations and security?

Here are the key benefits of an IT Audit:
1) Improves Security: IT Audit identifies vulnerabilities and makes the organisation’s Cyber Security framework stronger.
2) Ensures Compliance: It confirms adherence to laws, regulations and industry standards such as GDPR or ISO 27001.
3) Improves Efficiency: It streamlines all IT operations by detecting redundant and ineffective processes.
4) Reduces Risk: It highlights potential threats and helps implement effective risk mitigation strategies.
5) Builds Trust: It boosts confidence among stakeholders, clients and partners through transparent IT governance.
6) Supports Decision-Making: It provides management with data-driven insights for better IT and business planning.
What are the primary categories or types of IT Audits?

The general categories of IT Audit are as follows:
1) Systems and Applications Audit: This evaluates software systems for data accuracy, reliability and security.
2) General Controls Audit: It reviews overall IT infrastructure, including access controls, backups and Change Management.
3) Development Audit: It assesses system development processes to confirm proper documentation, testing, and control implementation.
4) Compliance Audit: It ensures adherence to internal policies, legal requirements, and industry standards.
How would you describe a systems development audit?

“Systems Development Audit is an audit conducted during the design or development of a system. It’s conducted to ensure that the proper controls, documentation and testing are in place. It helps prevent errors and ensures the system meets business and security requirements.”
Embrace CISA as the mindset for mastering IT governance with our comprehensive CISA Training - register now and elevate trust in IT systems!
What does a systems and Applications Audit involve?

“This audit assesses Software Applications and their supporting systems. It reviews data accuracy, access permissions, and operational reliability to ensure everything functions securely and aligns with business goals. It also confirms that applications meet compliance requirements and maintain proper documentation. Regular reviews help identify performance issues and potential security gaps early.”
Why is a firewall considered essential for ensuring network security?

“A firewall acts as the first line of defence against unauthorised access. It monitors and filters both incoming and outgoing network traffic. This ensures that only legitimate data passes through and protects the network from external threats. Firewalls also help detect suspicious activity and prevent malware from spreading across systems. They are essential for maintaining a secure and controlled network environment.”
What policies and controls secure mobile devices?

“Policies like strong passwords, encryption and remote wipe are essential. Mobile Device Management (MDM) solutions also help monitor, update and secure company data on employee devices.”
How would you approach auditing a large or complex IT project?

“I’d start the auditing by understanding the project’s objectives and risks, then review documentation, controls, and milestones. Continuous communication with the project team ensures alignment. Finally, I will assess the deliverables against the established security and compliance benchmarks.”
How do you stay updated on the latest IT Audit trends and technologies?

“I follow reputable cybersecurity blogs and industry news platforms to stay informed about emerging threats. I also attend webinars and workshops to learn from experts and real-world case studies. Additionally, I engage actively in professional communities like ISACA and (ISC)² to exchange insights with peers. I regularly review updates to frameworks such as COBIT, NIST, and ISO 27001.”
Set the gold standard for compliance in IT with our ISO 20000 Lead Auditor Training - Sign up now!
How would you assess the effectiveness of an organisation’s disaster recovery plan?

“I’d review the plan’s documentation, test restoration procedures and evaluate response times. A practical simulation or table-top exercise often reveals how ready the organisation truly is for real disruptions.”
Explain the COBIT framework and its relevance in IT Auditing

“COBIT provides a governance and management framework for IT systems. It helps align IT goals with business objectives while ensuring strong control, Risk Management and compliance practices across the organisation.”
What is a Control Self-assessment (CSA), and how does it fit into IT Auditing?

“CSA allows departments to evaluate their own controls before an external audit. It promotes accountability, early detection of issues, and a stronger culture of risk awareness within the organisation. It also helps management spot process weaknesses early, which saves time during formal audits. By promoting teamwork and open communication between departments, CSA improves overall governance and supports continuous improvement across the organisation.”
Describe the steps involved in performing an IT Risk Assessment

Here are the steps involved in performing an IT Risk Assessment:
1) Listing all critical systems, applications, and data that need protection.
2) Determining potential internal and external risks that could impact these assets.
3) Identifying weaknesses in systems, processes or controls that threats could exploit.
4) Measuring how probable each risk is and how severe its effect could be.
5) Ranking risks based on their overall significance to the organisation.
6) Recommending suitable controls or safeguards to reduce risk exposure.
7) Continuously reassessing risks and update controls as new threats emerge.
Describe the challenges of auditing cloud-based systems and solutions

“Key challenges include shared responsibility models, data residency concerns, and limited visibility into cloud service provider controls. Understanding vendor agreements and assessing third-party certifications are essential for gaining proper assurance.”
Explain the principles of continuous auditing and monitoring in IT

“Continuous auditing and monitoring in IT mean using automated tools to check systems, controls and activities in real time. This helps identify issues or risks as soon as they happen instead of waiting for scheduled audits. It allows quicker responses, improves the accuracy and helps organisations stay compliant.”
Keep a check on the pulse of IT Service health with ease. Sign up for our ISO 20000 Internal Auditor Course now!
Explain the concept of privilege escalation in IT security

“Privilege escalation occurs when a user gains higher access rights than intended, either through a system flaw or misuse. It’s a serious risk because it can lead to data breaches or unauthorised changes.”
What are the security vulnerabilities that an IT Audit can identify?

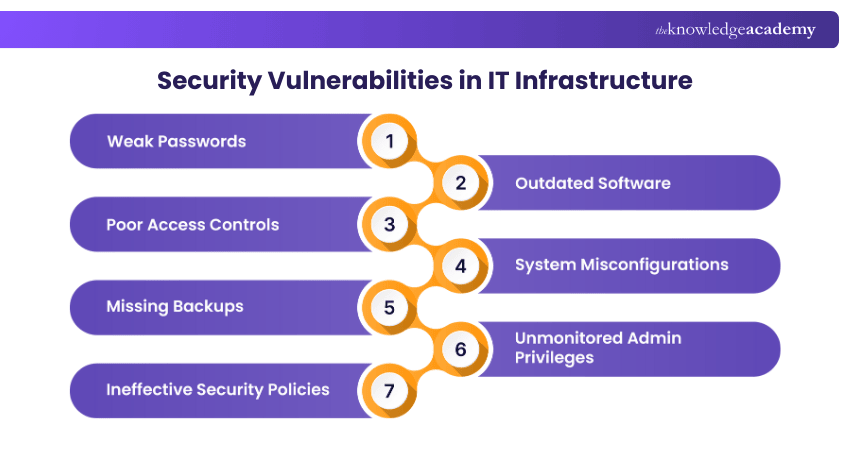
Here are the security vulnerabilities that can be identified with an IT Audit:
1) Weak Passwords: It can identify the use of simple or reused passwords that compromise system security.
2) Outdated Software: It can detect unpatched or obsolete systems that increase the risk of attacks.
3) Poor Access Controls: It highlights excessive user permissions or lack of role-based Access Management.
4) System Misconfigurations: It finds incorrect settings that may expose the networks or data.
5) Missing Backups: It reveals gaps in backup processes that threaten data recovery.
6) Unmonitored Admin Privileges: It flags uncontrolled administrative access that can lead to misuse or breaches.
7) Ineffective Security Policies: It identifies unclear or outdated policies that fail to address current threats.
What is the main difference between compliance and substantive testing in IT Audit?

“Compliance testing checks whether the processes and controls are being followed correctly. Meanwhile substantive testing verifies the actual data accuracy and control performance. Together, they confirm both the procedural compliance and operational reliability in audit results.”
Why are continuous monitoring tools important in an organisation?

“Continuous monitoring tools are important because they help detect anomalies, policy violations, and performance issues in real time. They reduce response time to incidents and provide ongoing assurance of system integrity.”
The company is facing challenges related to complying with data protection laws. How can you help them comply and maintain the law?

“I’d begin with a compliance gap analysis. I'd implement encryption and strict access controls, and update privacy policies. Staff training and regular audits will help me ensure long-term compliance. Additionally, continuous monitoring keeps data handling aligned with GDPR and other laws.”
The organisation is expanding globally, and you need to examine the security and compliance levels of international subsidiaries. How would you describe this project?

I’d approach it as a comprehensive global compliance and Security Audit focused on bringing all subsidiaries under a unified governance framework. Here's how I'll approach it:
1) I will begin by assessing each subsidiary’s local regulatory requirements and industry standards.
2) I will evaluate their access controls and cybersecurity practices to identify gaps or inconsistencies.
3) I'll develop a standardised compliance checklist to ensure uniform security policies across regions.
4) I'll collaborate with local IT and compliance teams to address regional challenges while maintaining global consistency.
5) Finally, I will compile a consolidated report highlighting the strengths, risks and improvement opportunities.
Become the armour for your organisation’s most valuable information assets. Sign up for our ISO 27005 Lead Auditor Training now!
You suspect there is a case of fraud in the organisation. How will you investigate and what steps will you take to prevent fraud in the future?

“If I suspect fraud, my first step would be to secure system logs and preserve digital evidence to avoid tampering. I’d then analyse access trails and transaction histories to trace any unusual activity. Additionally, interviews with key employees would help gather insights and confirm my findings. After identifying the root cause, I’d recommend strengthening internal controls and tightening user access management.”
The company is considering a BYOD (Bring Your Own Device) policy. What concerns and security measures will you address in implementing this system?

“When implementing a BYOD policy, I would first focus on the main risks, such as data leaks, unauthorised access or malware infections. To manage these risks, I’d suggest using Mobile Device Management (MDM) tools to monitor and secure devices, along with strong encryption and authentication measures to protect data. Clear policies must define what types of devices can be used and what security settings are required.”






 Top Rated Course
Top Rated Course



 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


