We may not have the course you’re looking for. If you enquire or give us a call on 01344203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Have you ever received an email or message that looked official but asked you to click a suspicious link or share personal details? Many people face this situation online every day. This is where understanding What is Phishing becomes important. Phishing is a cyberattack where criminals impersonate trusted sources to trick users into revealing sensitive information, such as banking details, or personal data.
As more of our daily activities move online, these attacks are becoming increasingly common and sophisticated. Understanding What is Phishing helps individuals and organisations recognise suspicious messages and avoid falling into traps set by cybercriminals. In this blog, you will learn about Phishing, its types, how it works, how to detect one, and more.
Table of Contents
1) What is a Phishing Attack?
2) Let’s Understand How Phishing Works
3) Types of Phishing Attacks
4) How to Recognise a Phishing Attack?
5) How to Minimise the Risks of Phishing Attacks in Your Organisation?
6) How to Protect Yourself from Phishing Attacks?
7) Conclusion
What is a Phishing Attack?
Phishing is a cyberattack where criminals pose as legitimate organisations to trick people into revealing sensitive data. Phishing refers to a deceptive practice where attackers use fake emails, websites, or text messages to steal sensitive details such as passwords, financial data, or personal information.
The stolen information is misused for identity theft, financial fraud, or gaining unauthorised system access. As Phishing exploits human error rather than technical weaknesses, it remains a widespread Cyber Security threat. Awareness, vigilance, and strong security practices are crucial to safeguard individuals and organisations.
Let’s Understand How Phishing Works
Phishing works by deceiving people into trusting messages that appear to come from legitimate sources. Usually, attackers contact victims through different channels to make the message look convincing. Some common methods are listed below:
1) Emails: Fake emails that imitate trusted organisations and ask users to click links or download attachments.
2) Phone Calls: Scammers pose as officials or support agents to obtain sensitive information.
3) Text Messages: Messages that create urgency and direct users to suspicious links.
4) Fake Websites or Social Media Messages: Pages designed to look real and trick users into entering personal details.
The aim of these cyberattacks is to persuade the victim to take a specific action. It may include sharing passwords, entering personal details, or changing payment information. In many cases Phishing messages contain links or attachments that install malware, such as viruses or spyware, which can steal data or give cybercriminals access to the victim’s device.
Types of Phishing Attacks
Below, we outline the most common types of Phishing campaigns, how they operate across email, SMS, and voice channels, and the red flags that help you spot and stop them early. Let’s look at them below:
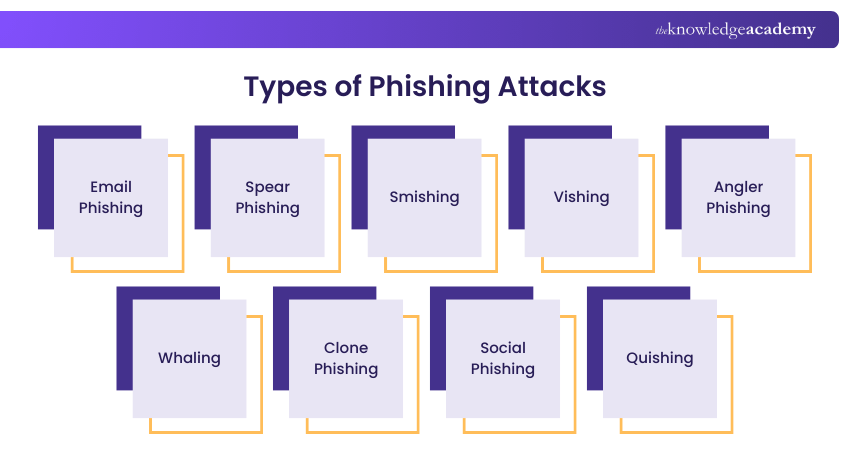
1) Email Phishing
Email Phishing is the most common type of Phishing technique. Attackers send fraudulent emails that appear to come from legitimate organisations, often containing malicious links or attachments. The goal is to trick recipients into revealing sensitive information or downloading malware.
2) Spear Phishing
Spear Phishing is a targeted form of Phishing aimed at specific individuals or organisations. Unlike generic email Phishing, these attacks are highly personalised, using details about the victim to make the message more convincing. This increases the likelihood of success and data theft.
3) Smishing
Smishing is a Phishing technique that uses SMS or text messages to trick victims into clicking on malicious links or sharing sensitive information. These messages often appear to come from trusted organisations like banks or delivery services.
4) Vishing
Vishing involves attackers making fraudulent phone calls to manipulate victims into revealing confidential details such as account numbers, passwords, or credit card data. Criminals often impersonate legitimate authorities or companies to gain trust quickly.
5) Angler Phishing
Angler Phishing attacks are carried out with the help of social media accounts. Here, the attacker uses a fake social media account similar to any other reputable organisation’s social media account. Besides, the profile picture of this account is identical to the actual organisation’s social media account.
6) Whaling
Whaling is a targeted Phishing attack aimed at high-profile individuals such as CEOs, directors, or senior executives. These attacks often involve highly personalised emails crafted to steal sensitive business data or authorise fraudulent transactions.
7) Clone Phishing
Clone phishing occurs when attackers copy a legitimate email previously sent to the victim, replace the original links or attachments with malicious ones, and resend it. Because the email looks familiar, victims are more likely to trust and act on it.
8) Social Phishing
Social Phishing occurs when scammers use social media platforms, such as Facebook, Instagram, or X, to steal personal information. They may create fake profiles or impersonate friends and organisations to send messages with malicious links or requests for sensitive details.
9) Quishing
Quishing is a Phishing attack that uses fake Quick Response (QR) codes to direct users to harmful websites. These codes may appear in emails, messages, or public places. Sometimes scammers replace real QR codes with fake ones to steal payment or personal data.
Learn to detect and stop fraud with analytics by joining the Fraud Analytics Training today!
How to Recognise a Phishing Attack?
Recognising the warning signs of Phishing attacks is an important step to protect yourself from cyber threats. Paying attention to certain indicators can help users identify cyberthreats and avoid sharing sensitive information. Let’s look at the signs below to better understand What is Phishing:

1) Unexpected Messages: Emails or messages that appear suddenly from organisations that generally contact you in a different way.
2) Unusual Tone or Greeting: Messages that sound overly casual, too friendly, or informal when they should be professional.
3) Spelling or Grammar Mistakes: Poorly written content and formatting that may indicate the message is not from a legitimate source.
4) Urgent or Threatening Language: Messages pressuring you to act quickly, such as claiming unpaid taxes or account suspension.
5) Suspicious Email Addresses: Slight misspellings or unusual domain names that imitate legitimate companies.
6) Unexpected Attachments: Files or links included in emails that may contain malware or harmful software.
Build smarter defence strategies with our Cyber Security Risk Management Course – Register today!
How to Minimise the Risks of Phishing Attacks in Your Organisation?
Reducing the threat of phishing requires a proactive and layered approach. Organisations can strengthen their defences by focusing on employee awareness, deploying advanced security measures, and enforcing strict access controls, as highlighted in the strategies below:
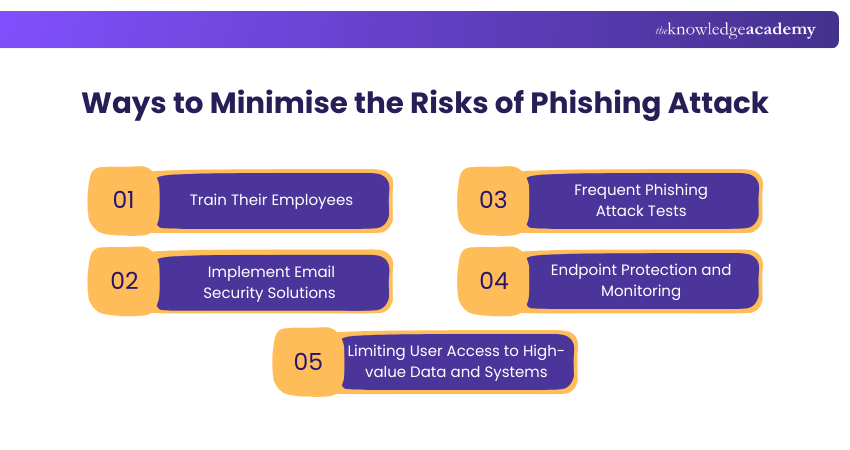
1) Train Their Employees
It is essential to impart training to your employees frequently. As a result, it will help your employees to understand how Phishing is done. Your employees will also be able to identify any Phishing signs. Eventually, it will enable them to report any suspicious activities to the IT Team.
Organisations should help employees to identify trust badges and security stickers used by antivirus or Cyber Security companies. The employees should interact only with websites with stickers or trust badges. Trust badges and security stickers indicate a website is concerned about its safety and isn’t malicious or fake.
2) Implement Email Security Solutions
Organisations should use modern email filtering solutions. An email filtering solution offers protection against malware and malicious links attached to emails. These links help to detect emails that include malicious attachments, links, inappropriate language, and spam content as they indicate Phishing attacks.
Additionally, email security solutions block suspicious emails automatically. Besides, these emails implement sandboxing technology to filter out emails that consist of malicious code. This helps organisations reduce the risk of Phishing attacks and protect sensitive data from cybercriminals.
3) Frequent Phishing Attack Tests
Phishing tests help security teams to measure the effectiveness of a security awareness training program. It also helps users to determine the source and nature of the attack. These simulated tests allow organisations to observe how employees respond to suspicious emails or links in a controlled environment.
Regular Phishing simulations allow organisations to identify gaps in employee awareness and response. These tests help employees become familiar with Phishing techniques and improve their ability to recognise and report suspicious emails or messages.
4) Endpoint Protection and Monitoring
Endpoint is a physical device that facilitates the exchange of information between different computer networks. The organisation's use of numerous personal devices and cloud-based services is introducing several new endpoints.
However, these endpoints need to be appropriately secured. So, security teams should identify endpoints that are vulnerable to attacks beforehand. Security teams should monitor endpoints regularly to find out security threats. Consequently, they should implement a security solution on compromised devices.
5) Limiting User Access to High-value Data and Systems
The objective of the Phishing method is to trick a human computer operator. Primarily, privileged user accounts are targeted by cybercriminals. Organisations can encrypt their data and systems to prevent the leakage of sensitive data.
Additionally, organisations should apply strict access control policies so that employees can only access the information necessary for their roles. Limiting permissions reduces the risk of attackers gaining access to critical systems or sensitive data.
Outsmart human-based threats with our Social Engineering Training – Get Started Now!
How to Protect Yourself From Phishing Attacks?
Phishing is designed to trick users into revealing sensitive information or clicking harmful links. Let’s look at key precautionary ways below:
1) Think Before You Click: Avoid clicking on links in unexpected emails or messages. Instead, check the link’s URL or visit the official website directly through a search engine.
2) Avoid Sharing Personal Information: Never provide sensitive details, such as passwords, bank information, or personal data, through email or unknown websites. If you are unsure, contact the organisation directly through its official channels.
3) Check if the Website is Secure: Before submitting any information online, ensure the website uses “https” and has a valid security certificate, which indicates a secure connection.
4) Install Firewalls: Firewalls help block suspicious traffic and act as a barrier against Phishing attempts. Using both desktop and network firewalls can provide stronger protection.
5) Report Phishing Attempts: If you receive a phishing message, report it to the relevant fraud reporting authority. If you believe your financial information may be compromised, contact your bank immediately to prevent further loss.
Conclusion
In today’s world, cybercriminals constantly look for new ways to deceive users and steal sensitive information. This is why understanding What is Phishing is crucial more than ever. By recognising common types, spotting warning signs, and following simple prevention tips, you can keep yourself alert, protect your data, and reduce the risk of falling victim to online scams.
Build strong cyber defence skills today by joining the Cyber Security Courses now!
Frequently Asked Questions
How does Phishing Differ from Pretexting?

Phishing deceives victims through fake emails, texts, or websites to steal sensitive data, while pretexting relies on fabricated stories or impersonation to gain trust and extract information. Both are social engineering tactics, but phishing uses digital lures, whereas pretexting depends on direct manipulation.
Can Phishing Be Considered a Cybercrime?

Yes, phishing is a recognised cybercrime. It involves fraudulent attempts to obtain confidential data such as login credentials, financial details, or personal information through deceptive emails, websites, or messages. Since it exploits victims for illegal gain, it is punishable under cybersecurity and criminal laws worldwide.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Training, including Cyber Security Awareness Training, Cyber Security Risk Management Course, and Incident Reporting Training. These courses cater to different skill levels, providing comprehensive insights into Multi-factor Authentication.
Our IT Security & Data Protection Blogs cover a range of topics related to Cyber Security, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Cyber Security skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Certified Cyber Security Professional (CCS-PRO)
Certified Cyber Security Professional (CCS-PRO)
Fri 24th Jul 2026
Fri 9th Oct 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


