We may not have the course you’re looking for. If you enquire or give us a call on 01344203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Your organisation’s data is like the heartbeat of your business, powerful, vital, and worth protecting at all costs. But in today’s digital jungle, threats lurk everywhere, waiting to strike. That’s where ISO 27001 Controls come in as a fortress of smart, adaptable security measures designed to keep your data safe, your compliance on point, and your business thriving.
Imagine having a toolkit that not only shields your information but also builds trust with clients and partners. With ISO 27001 Controls, you get just that a proven way to outsmart cyber risks and stay ahead in a constantly changing world. This blog will take you through the categories of ISO 27001, simplifying complex concepts and explaining the statement of applicability clearly.
Table of Contents
1) What is ISO 27001 Annex A?
2) What is the Purpose of Annex A?
3) How Many ISO 27001 Controls are Present?
4) The 4 Themes of ISO 27001 Controls
5) What New Controls Does ISO 27001:2022 Introduce?
6) Who Implements the Annex A Controls?
7) Is it Necessary to Adopt ISO 27001 in an Organisation?
8) What is the Statement of Applicability in ISO 27001?
9) Conclusion
What is ISO 27001 Annex A?
ISO 27001 Annex A is an important section of the ISO/IEC 27001:2022 standard. It lists the information security controls that organisations can use to manage and eliminate risks. These controls are the policies and processes to safeguard data and strengthen the ISMS (Information Security Management System).
The 2022 update includes a total of 93 controls. They are grouped into four categories: Organisational, People, Physical and Technological. Compared to the 2013 version that had 114 controls across 14 domains, the recent one has a simpler structure. Annex A helps organisations to select relevant controls based on their security and risk assessment needs.
What is the Purpose of Annex A?
The purpose of Annex A in ISO 27001 Controls is to provide organisations with a structured list of security controls. These controls address identified risks during the ISMS planning stage. For a better understanding Annex A, it is essential to look at Clause 6: Planning in ISO 27001. This clause requires organisations to identify risks and plan actions to mitigate the chance of these risks.
Annex A supports this requirement of Clause 6: Planning by providing a systematic catalogue of 93 controls. These are utilised by organisations as preventive actions for information security risk. Annex A gives a reliable point, ensuring risk assessment is consistent and relevant with industry practices.
How Many ISO 27001 Controls are Present?
The Controls in Annex A of 27001 are divided into 4 categories. For effective Risk Management, these 4 categories have 93 ISO 27001 Controls outlined as tools. The controls can be applied based on the results of the Risk Assessment of your organisation.
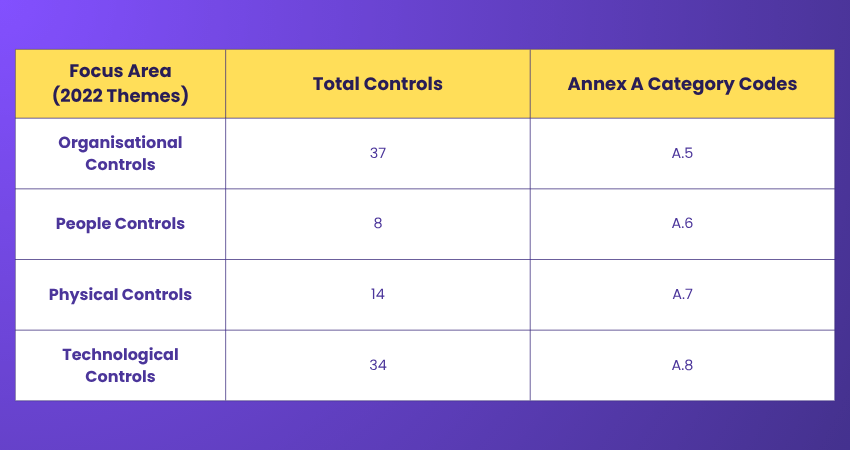
The objective of this framework is to safeguard the integrity, confidentiality, and availability of information. To understand which areas of organisation the Control sets are related to, check the following ISO 27001 Controls list of Annex A controls breakdown.
The 4 Themes of ISO 27001 Controls
ISO 27001 groups its controls into four clear categories or themes, each addressing a different aspect of Information Security Management. Let’s explore them in detail:
1) Annex A.5: Organisational Controls (37 Controls)
These controls cover governance and operational security areas that do not sit under people, physical, or technical domains. They include Identity Management, defined roles and responsibilities, Risk Management and evidence collection. Additions in ISO 27001:2022 include:
a) Threat intelligence (5.7)
b) Information security for cloud services (5.23)
c) ICT readiness for business continuity (5.30)
2) Annex A.6: People Controls (8 Controls)
People controls focus on how employees and contractors handle sensitive information in their daily activities. This area includes:
a) Secure remote working
b) Screening
c) Confidentiality agreements
d) Onboarding and offboarding processes
e) Clear responsibilities for reporting security incidents
3) Annex A.7: Physical Controls (14 Controls)
Physical controls address the protection of facilities, equipment, and physical assets. They cover areas such as secure premises monitoring, maintenance and protection of storage media. These controls aim to reduce risks from physical and environmental threats like theft, damage, or natural events. An addition here is Physical security monitoring (7.4).
4) Annex A.8: Technological Controls (34 Controls)
Technological controls focus on safeguarding information systems through technical means. They include access control, encryption, network security, Configuration Management and data protection techniques. ISO 27001:2022 introduces several new controls, such as:
a) Data masking (8.1)
b) Configuration Management (8.9)
c) Information deletion (8.10)
d) Data leakage prevention (8.12)
e) Monitoring activities (8.16)
f) Web filtering (8.23)
g) Secure coding (8.28)
Data leakage prevention and web filtering are particularly important for reducing exposure to modern cyber threats.
Gain insights into effective auditing techniques and practices with our ISO 27001 Internal Auditor Training – Register now!
What New Controls Does ISO 27001:2022 Introduce?
The ISO 27001:2022 update introduces eleven new controls, distributed across organisational, physical, and technological domains, to strengthen information security:
1) A.5.7 Threat Intelligence: It focuses on gathering and analysing threat-related information to proactively protect information assets.
2) A.5.23 Information Security for the Use of Cloud Services: It requires organisations to define, implement and monitor security controls for cloud-based environments.
3) A.5.30 ICT Readiness for Business Continuity: It ensures that ICT continuity planning supports organisational resilience during disruptions.
4) A.7.4 Physical Security Monitoring: It emphasises the use of monitoring mechanisms to detect and deter unauthorised physical access.
5) A.8.9 Configuration Management: It introduces structured control over documenting, implementing and auditing system configurations.
6) A.8.10 Information Deletion: It addresses secure data deletion in line with legal, regulatory, and business requirements.
7) A.8.11 Data Masking: It promotes masking techniques to protect personally identifiable information and support compliance.
8) A.8.12 Data Leakage Prevention: It focuses on technical controls to identify and prevent unauthorised data disclosure or extraction.
9) A.8.16 Monitoring Activities: It strengthens continuous monitoring to detect abnormal behaviour and respond to incidents.
10) A.8.23 Web Filtering: It requires controls to restrict access to potentially harmful external websites.
11) A.8.28 Secure Coding: It promotes secure development practices to reduce vulnerabilities arising from poor coding methods.
Who Implements the Annex A Controls?
Implementing ISO 27001:2022 Annex A controls requires collaboration across the entire organisation. Generally, the IT department handles technical areas, such as system configuration and Access Management. Still, strong information security depends on the combined efforts of different teams for effectively managing people, process and technology.

Key roles include:
1) Information Security Officer:
Oversees the implementation, ensuring controls align with organisational security objectives and compliance standards. They also coordinate cross-department efforts to maintain a strong security posture.
2) IT Department:
Responsible for technical controls like data protection and system security. They monitor systems continuously to detect and respond to potential threats.
3) Human Resources:
Manages personnel-related security, including onboarding, training, and offboarding. HR ensures employees understand their security responsibilities from day one.
4) Legal and Compliance:
Ensures controls adhere to legal, regulatory, and contractual obligations. They stay updated on changing laws to keep the organisation compliant.
5) All Employees:
Play an active role by following policies, reporting incidents, and participating in security training. Their vigilance helps prevent security breaches and protects organisational data.
Such cross-functional collaboration is essential for the successful adoption and maintenance of Annex A controls. This fosters a robust security culture throughout the organisation.
Understand the process for conducting internal audits and managing corrective actions. Join our ISO 27001 Lead Implementer Training now!
Is It Necessary to Adopt ISO 27001 in an Organisation?
While not mandatory, ISO 27001 greatly enhances information security. It protects cloud, paper, and digital data, reduces costs from weak defences and improves cyber-attack resilience. It also safeguards data integrity and helps manage tech risks, making it a smart move for stronger security and compliance.
What is the Statement of Applicability in ISO 27001?
The Statement of Applicability (SoA) is a crucial ISO 27001 document that lists all Annex A controls, showing which are implemented or excluded based on risk assessment and business needs. It also details each control’s status, providing a clear overview of the organisation’s security measures. The SoA is vital for compliance audits and managing the ISMS effectively.
Conclusion
ISO 27001 Controls provide a comprehensive framework to protect information assets and manage risks effectively. By adopting ISO 27001 Annex A controls, organisations can ensure compliance, enhance protection, and build resilience against cyber threats. Proper implementation of ISO 27001 Annex A controls is essential for maintaining a powerful Information Security Management system. It also plays an important role in safeguarding sensitive data in today’s digital landscape.
Become an expert in ISO 27001 audits. Register in our ISO 27001 Lead Auditor Course today!
Frequently Asked Questions
How Many ISO 27001 Controls Are There?

There are in total of 93 controls. Previously, ISO 27001:2013 had 114 controls, but after ISO 27001:2022, it has been reduced to 93 controls, grouped into four categories: Organisational, People. Technological and Physical.
What is the ISO 27001 Framework?

ISO 27001 Framework is an international standard that guides organisations to manage information security through ISMS. It covers risk assessment, security policies, roles, processes and reduces risks.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 19 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various ISO 27001 Courses, including the ISO 27001 Foundation Course, ISO 27001 Internal Auditor Course and the ISO 27001 Lead Auditor Course. These courses cater to different skill levels, providing comprehensive insights into ISO.
Our ISO & Compliance Blogs cover a range of topics related to ISO 27001 Controls, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your ISO knowledge base, The Knowledge Academy's diverse courses and informative blogs have got you covered.

Hailey Davis is an ISO compliance expert with over 10 years of experience in audit, quality management systems (QMS), and regulatory compliance. She has worked with various industries, including manufacturing, healthcare, and technology, ensuring organisations achieve and maintain ISO certifications. Hailey’s content provides practical, actionable insights on navigating compliance challenges and improving business processes.
View Detail
Upcoming ISO & Compliance Resources Batches & Dates
Date
 ISO 27001 Foundation
ISO 27001 Foundation
Mon 6th Jul 2026
Mon 3rd Aug 2026
Mon 7th Sep 2026
Mon 5th Oct 2026
Mon 2nd Nov 2026
Mon 7th Dec 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


