We may not have the course you’re looking for. If you enquire or give us a call on 01344203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Have you ever shared your details online and wondered, “Is my data really safe?” From shopping apps to healthcare records, your personal info is floating in digital space and someone must keep it protected. That’s where ISO 27001 comes in. If you’ve ever asked yourself What is ISO 27001, think of it as the security blueprint trusted by companies worldwide to keep your data safe and sound.
So, What is ISO 27001 in action? It’s a global standard that helps organisations manage risks, protect data, and build trust. In this blog, we’ll cover what ISO 27001 is, its benefits, key principles, the 14 implementation phases, ISMS explained, and its core requirements.
Table of Contents
1) What is ISO 27001?
2) The Purpose of ISO 27001
3) The Importance of ISO 27001
4) What Is the Difference Between ISO 27001:2013 And ISO 27001:2022?
5) The Benefits of ISO 27001
6) The Principles of ISO 27001
7) How does ISO 27001 Work?
8) Requirements of ISO 27001
9) Other Supporting ISO Standards
10) Is ISO 27001 Mandatory?
11) Conclusion
What is ISO 27001?
ISO 27001 is the leading International Standard for Information Security Management. It was jointly developed by the International Organisation for Standardisation (ISO) and the International Electrotechnical Commission (IEC); two globally recognised bodies known for publishing widely accepted international standards.
To fully grasp the purpose of ISO 27001, it's helpful to understand its place within the broader ISO/IEC 27000 series, a family of standards focused on information security. Among them, ISO 27001 stands out as the core standard.
Officially titled "ISO/IEC 27001 Information Security, Cybersecurity and Privacy Protection Information Security Management Systems Requirements", it outlines the framework for establishing, maintaining, and enhancing a powerful Information Security Management System (ISMS).
The Purpose of ISO 27001
1) Protects Valuable Information: It helps organisations secure sensitive data with a clear and proven framework.
2) Builds Customer Trust: Certification shows clients and partners that their data is protected, improving credibility and confidence.
3) Boosts Career Opportunities: Individuals can become certified to demonstrate their skills in managing or auditing information security systems.
4) Globally Recognised: As an international standard, ISO 27001 ISMS is accepted worldwide, helping organisations and professionals access new markets.
5) Supports Legal Compliance: It helps meet data protection laws and industry regulations.
6) Enhances Business Reputation: Certification signals a serious commitment to security, which can lead to stronger partnerships and more business.
The Importance of ISO 27001
ISO 27001 plays a key role in helping organisations prove they take information security seriously. It also offers professionals a way to show their expertise in managing and auditing secure systems.
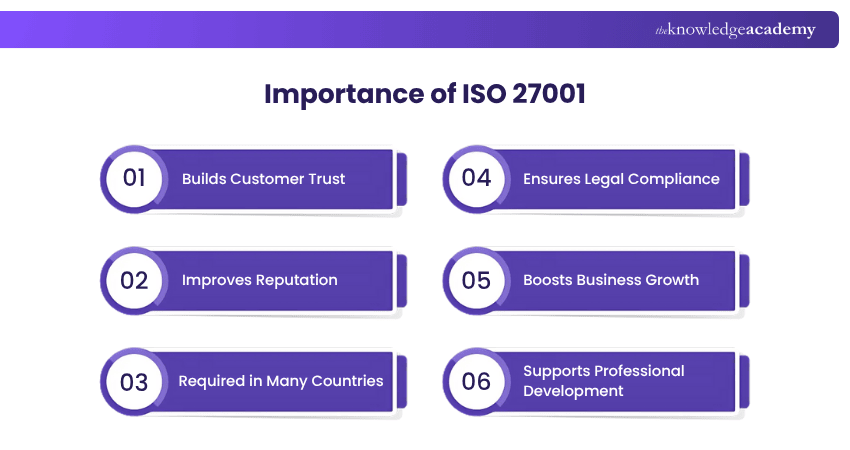
1) Builds Customer Trust: Certification shows clients that your organisation protects their data properly.
2) Improves Reputation: Being certified demonstrates professionalism and a strong commitment to security.
3) Required in Many Countries: Nations like the UK, US, Canada, Japan, and Australia often mandate ISO certifications for certain businesses.
4) Ensures Legal Compliance: It helps meet local and international laws and industry regulations.
5) Boosts Business Growth: Reliable and secure operations make it easier to win new clients and enter global markets.
6) Supports Professional Development: Individuals can get certified to prove their skills in auditing or managing an ISMS, increasing job opportunities.
What Is the Difference Between ISO 27001:2013 And ISO 27001:2022?
The ISO 27001 has been refined over the years to suit contemporary information security threats. The 2022 edition is a revised version of the ISO 27001:2013 standard, meant to bring the framework into closer relationship with the current threat environment without materially altering the main structure and management system requirements.
The most notable difference is Annex A controls. The 114 controls, categorised under 14 domains, of ISO 27001:2013 were replaced, with ISO 27001:2022, with 93 controls that are grouped together and subdivided into four broad themes (Organisational, People, Physical, and Technological), and 11 new controls that reflect emerging risks, including cloud services, threat intelligence, and physical monitoring.
Although the requirements of the management system (4-10) do not change significantly in both versions, the 2022 update gives more priority to risk-based thinking, more rigorous process criteria, and alignment with other ISO management requirements. This assists organisations to enhance operations planning, cope with emergent risks, and relate security controls to business objectives much better.
The Benefits of ISO 27001
There are many advantages of the ISO 27001 certification, such as increased security, reduced operating costs, and the enforcement of an effective ISO 27001 Access Control Policy to enhance data protection. Some of its other essential benefits are listed below:
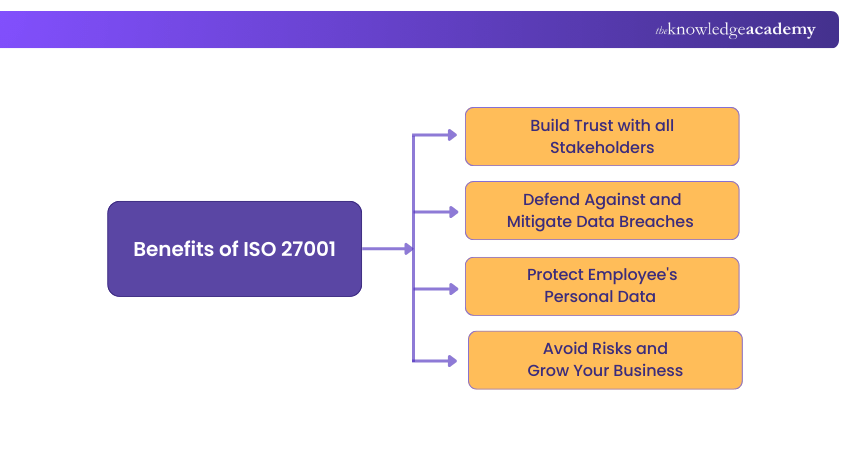
Build Trust with all Stakeholders
The presence of ISO 27001 will indicate that your organisation adheres to established practices of information security, and your customers, partners and stakeholders will be assured that their valuable information is in safe hands. Certification is an indication of a desire to protect sensitive data, which may assist in enhancing the trust in your security posture.
Defend Against and Mitigate Data Breaches
The standard establishes security control policies and procedures that assist in mitigating the risk of unauthorised access, loss of data, and breaches. Although it does not ensure complete prevention, ISO 27001 enhances the manner in which your organisation detects, responds, and handles security breaches.
Protect Employee's Personal Data
The information security measures provided in ISO 27001 also address internal information like personal information of employees. Compliance means being open regarding the security practice and making sure that the employees are aware of how their information is secured and ensuring that they give it an informed consent.
Avoid Risks and Grow Your Business
Through detection, evaluation, and management of risks in an ISMS, ISO 27001 assists organisations in mitigating weaknesses that can cause an organisation to face financial losses. Such a risk-based strategy makes financial impacts fewer as well as more resilient, competitive, and able to grow over time.
Build core auditing and compliance skills with our ISO 27001 Internal Auditor Course – Join now!
The Principles of ISO 27001
ISO 27001 is built on three key principles that guide the effective use of an ISMS to reduce security risks. These are essential for protecting data and maintaining trust within and outside the organisation.
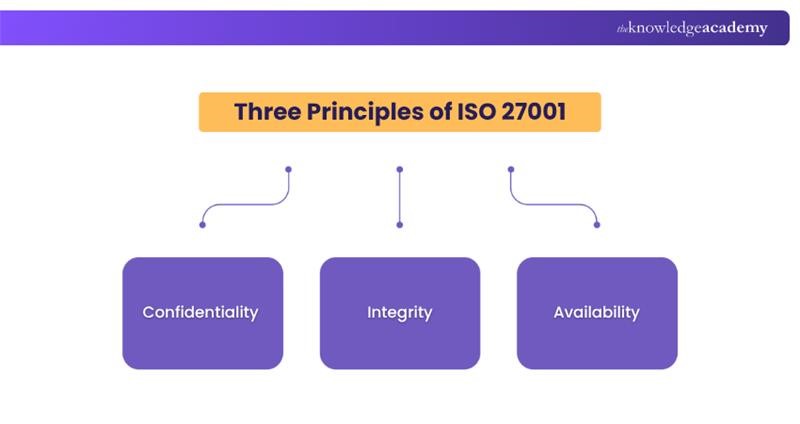
a) Confidentiality: Only authorised people should have access to sensitive information.
b) Integrity: Data must be accurate and protected from unauthorised changes.
c) Availability:Information should be accessible to authorised users whenever needed.
Secure Your Data – Download the ISO 27001 Information Security PDF!
How does ISO 27001 Work?
ISO 27001 works through a structured, risk-based management system approach:
1) Define the ISMS Scope: Identify the organisational context, stakeholders, and the boundaries of the Information Security Management System.
2) Conduct Risk Assessment: Identify information assets, analyse threats and vulnerabilities, and evaluate associated risks.
3) Select and Implement Controls: Apply appropriate security controls (Annex A) to treat identified risks.
4) Document Policies and Procedures: Establish formal processes to ensure consistent security practices.
5) Monitor and Review Performance: Conduct internal audits, management reviews, and performance evaluations.
6) Continual Improvement: Use the Plan-Do-Check-Act cycle to enhance security controls and adapt to evolving risks.
This structured approach ensures information security remains aligned with business objectives and continuously improves over time.
Sign up for our ISO 27001 Foundation Course and acquire foundational knowledge on ISO 27001 & Information Security!
Requirements of ISO 27001
ISO 27001 is divided into two parts:
1) The first includes 11 clauses:
a) Clauses 0-3 covers introduction, terms, references, and scope
b) Clauses 4-10 focuses on compliance requirements.
2) The second part, Annexure A, provides guidelines for 93 control objectives and is optional, addressing Risk Management.
Necessary Requirements
There are many benefits to getting ISO 27001 compliance. In this section, Let's learn about clauses four to ten necessary ISO 27001 Requirements to achieve ISO 27001 compliance:
a) Clause 4
Before defining the ISMS scope, it is necessary to understand the organisation's context. First, identify any internal and external problems. These issues can be anything from a simple regulatory issue to a much more severe issue.
b) Clause 5
This clause primarily focuses on the leadership aspect of an organisation. Effective Information Systems Management is dependent on the Upper Management's commitment. These objectives could be anything from supporting the people who contributed to the ISMS to supplying the resources necessary for the ISMS.
c) Clause 6
It is all about planning the security policy. While planning, you should consider the risks and opportunities involved. The risks can be identified by conducting a risk assessment. It will give a basic idea of how to create a security policy. An organisation's information security goals should rely on risk assessment. These goals should also align with the organisation's primary goals and be informed throughout the company.
d) Clause 7
This clause focuses on the support aspect of the ISMS. Proper documentation of information using the ISO 27001 guidelines is essential. Maintaining documentation improves the chances of ISMS success. Other key supporting factors include resources, the ability of employees, knowledge, and dialogue.
e) Clause 8
This clause is all about the operations and processes necessary to implement Information Security. The Upper Management should focus on processes like planning, risk assessment and mitigation to implement the organisation's security policy.
f) Clause 9
Perhaps the most important requirement of ISO 27001 is performance evaluation. It involves tracking, evaluation, and analysis of the ISMS. You can evaluate other performance-related metrics with internal audits. The Upper Management should frequently evaluate the performance of ISMS.
g) Clause 10
Once the performance evaluation is completed, you will have to look at ways to improve it. Any action that hinders the performance of the ISMS should be taken with proper measures. This will further improve performance and ensure business continuity.
Get your free copy of the ISO/IEC 27002 PDF today! Learn how to improve Information Security Management System effectively.
How to Fulfil These Requirements and Achieve ISO 27001 Compliance?
Getting ISO Certification like ISO 27001 Certification is a big commitment and requires a lot of work. However, once certified, its benefits can outweigh the efforts. It involves an extensive review of the organisation's ISMS and whether it can fulfil the specific requirements of ISO.
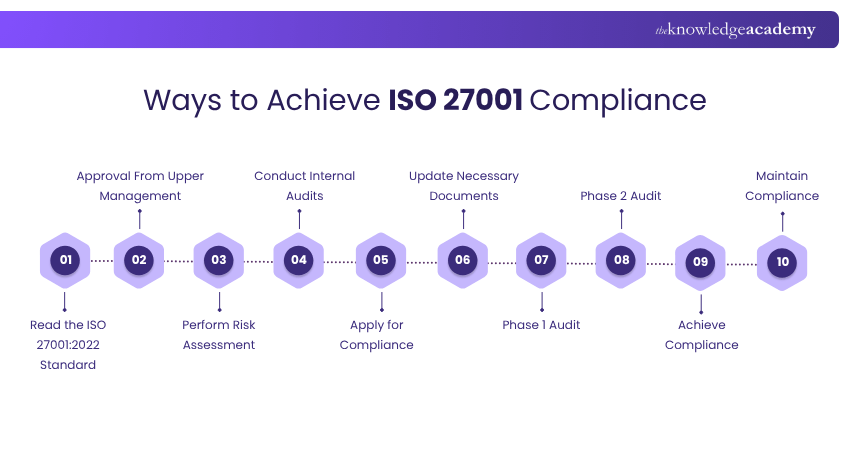
Achieving ISO 27001 compliance involves a structured step-by-step approach:
1) Read the ISO 27001:2022 Standard: Begin by understanding the full requirements of the standard.
2) Approval from Upper Management: Get leadership support to allocate resources and drive the process.
3) Perform Risk Assessment: Identify potential threats, vulnerabilities, and their impact on your organisation.
4) Conduct Internal Audits: Review current practices to ensure they align with ISO expectations.
5) Apply for Compliance: Start the formal process with a certification body.
6) Update Necessary Documents: Ensure all policies, procedures, and records are complete and accurate.
7) Phase 1 Audit: Undergo an initial review to confirm documentation meets ISO 27001 standards.
8) Phase 2 Audit: The auditor evaluates how well your ISMS is implemented and maintained.
9) Achievement: Upon successful audit, you’ll be certified as ISO 27001 compliant.
10) Maintain Compliance: Continue regular reviews, updates, and internal audits to uphold your certification.
Advance your Cybersecurity proficiency with our ISO 27002 Training Register now!
Other Supporting ISO Standards
ISO 27001 Framework is considered an important standard among the ISO 27000 Standards. It specifies what is necessary to achieve and how to achieve it. However, many frameworks have been developed to overcome this problem and provide additional guidelines. In the context of ISO 27001 vs ISO 27002, there are many supporting Standards available for ISO 27001. These standards capitalise on areas that ISO 27001 doesn’t explain in detail. Some of these Standards are listed below:
a) ISO 27002: It provides recommendations to implement the Annex A controls list. Apart from this, it also provides guidelines on how to apply these controls.
b) ISO 27004: It gives recommendations for the estimation of information security. Plus, it describes how to determine if the ISMS achieved its targets.
c) ISO 27005: ISO 27005 provides suggestions for risk management in information security. It is very similar to ISO 27001 and is considered a proper alternative. It explains how to conduct a risk assessment and mitigate similar risks.
d) ISO 27017: It gives instructions for information security in cloud-based systems.
e) ISO 27018: It gives suggestions for privacy protection in cloud-based systems.
f) ISO 27031: It gives recommendations for ensuring business continuity for information and communication technologies. ISO 27031 is a unique Standard connecting information security and business continuity.
Enhance your information security with the ISO 27001 Policies and Procedures PDF—download today!
Is ISO 27001 Mandatory?
ISO 27001 is not mandatory by law for all organisations, but it is often required in specific industries or for certain government contracts. Many companies choose to adopt it voluntarily to demonstrate their commitment to information security, meet client expectations, and gain a competitive edge. While not legally enforced, ISO 27001 is widely recognised as a best-practice standard for protecting sensitive data and building trust with stakeholders.
What are the Four Themes of ISO 27001?
ISO 27001:2022 organises its 93 controls into four key themes: Organisational, People, Physical, and Technological. This streamlined structure helps businesses manage risks more clearly by covering policies, staff responsibilities, physical security, and technical safeguards like access control and encryption for effective information protection.
Explore a structured path to auditing success with ISO 9001 Internal Auditor Training. Join now!
Conclusion
ISO 27001 provides a clear, reliable framework to manage information security and build lasting trust. From reducing risks to meeting compliance needs, it strengthens your organisation from within. Understanding What is ISO 27001 helps you take a proactive approach to data protection, making your business more resilient, efficient, and trusted in today’s digital landscape.
Gain expertise in evaluating and improving information security practices. Join our ISO 27001 Lead Auditor Training now!
Frequently Asked Questions
What’s the Difference Between ISO 27001 Compliance and Certification?

ISO 27001 compliance occurs when an organisation follows the standard’s best practices without formal verification. While certification involves an accredited body auditing the organisation to confirm full adherence to ISO 27001, leading to a recognised certificate that demonstrates compliance.
How Long Will Your ISO 27001 Certification Last?

Your ISO 27001 certification is legal for three years. However, to maintain it, your organisation must undergo annual surveillance audits to ensure ongoing compliance. After three years, a recertification audit is required to renew the certification.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various ISO 27001 Trainings, including the ISO 27001 Foundation, ISO 27001 Lead Auditor, and ISO 27001 Internal Auditor. These courses cater to different skill levels, providing comprehensive insights into ISO 27001 2022 Latest Version.
Our IT Security & Data Protection Blogs cover a range of topics related to Information Security and Regulatory Standards, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Compliance Management skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

Hailey Davis is an ISO compliance expert with over 10 years of experience in audit, quality management systems (QMS), and regulatory compliance. She has worked with various industries, including manufacturing, healthcare, and technology, ensuring organisations achieve and maintain ISO certifications. Hailey’s content provides practical, actionable insights on navigating compliance challenges and improving business processes.
View Detail
Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 ISO 27001 Foundation
ISO 27001 Foundation
Mon 6th Jul 2026
Mon 3rd Aug 2026
Mon 7th Sep 2026
Mon 5th Oct 2026
Mon 2nd Nov 2026
Mon 7th Dec 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


