We may not have the course you’re looking for. If you enquire or give us a call on 01344203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

A GDPR Data Breach is not just about missing files. The incident disrupts essential trust elements, which include accountability and responsibility, in a society where data functions as the primary value asset. From a minor error to a full-fledged cyberattack, the ability to deal under GDPR guidelines is necessary.
This blog explores GDPR Data Breach Management, why it matters, and how to stay compliant. Therefore, this helps protect people and organisations, becoming confident trustees of the digital trust.
Table of Contents
1) What is a Data Breach Under the GDPR?
2) What is a Personal Data Breach?
3) Types of Data Breach
4) Penalty for a Data Breach
5) What are GDPR Violations?
6) What are the 4 actions of a data breach?
7) Conclusion
What is a Data Breach Under the GDPR?
The GDPR defines a Data Breach as any security incident which leads to the unauthorised loss of personal data through accidental or illegal means, or through intentional data destruction or modification, or through unauthorised data disclosure or access. The definition of the term extends beyond hacking because it includes all human errors, system breakdowns, and actual record loss situations.
The simplest way to breach security occurs when someone sends personal data to an incorrect email recipient, loses a laptop, or leaves files unprotected. The important factor in this case shows that personal data has been compromised through methods which destroy its protected status and make it vulnerable through three security dimensions.
What is a Personal Data Breach?
A personal Data Breach is a security incident that affects the confidentiality, integrity, or availability of Personal Data. In simple terms, it happens when personal information is lost, destroyed, changed, or shared without permission, or when data becomes unavailable in a way that causes real harm to individuals.
Personal Data Breaches can occur for many reasons, including:
a) Unauthorised access by a third party
b) Intentional or accidental actions, or inaction, by a Data Controller or processor
c) Sending Personal Data to the wrong recipient
d) Loss or theft of devices that store Personal Data
e) Unauthorised changes made to Personal Data
f) Loss of access to Personal Data that results in serious negative consequences for individuals
Protect Personal Data with Confidence. Join our Data Privacy Awareness Course today!
Types of Data Breach
GDPR needs controllers to promptly delete Personal Data when there is no lawful basis for storage. The rules aim to prevent excessive retention and ensure proper data destruction and adherence to these guidelines. Now let’s explore the most prevalent types of Data Breach:
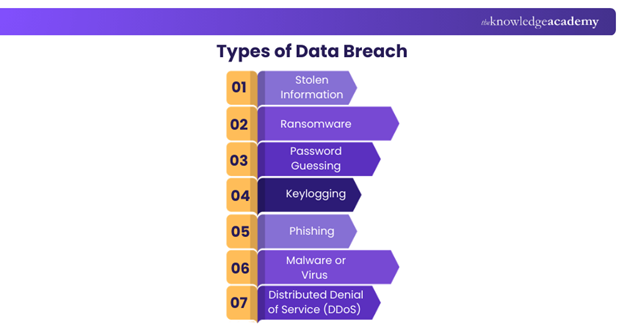
Stolen Information
Stolen information occurs when sensitive data like customer records, financial details or confidential business documents, is illegally accessed and taken without any permission. This categoy of breach can lead to identity theft, financial fraud and heavy reputational damage for the organisation.
Protecting against it requires strong access controls, secure storage systems and regular monitoring of data activity.
Ransomware
Ransomware is a cyberattack where criminals encrypt or block access to systems and demand payment to restore them. It can halt operations, disrupt services, and expose personal data, often leading to financial loss and reputational damage. Modern attacks increasingly target backups and cloud platforms, making recovery harder.
Reducing ransomware risk requires regular offline backups, timely software updates, and strong email security. Staff training is equally important, as most attacks begin with phishing emails or malicious links that appear legitimate.
Password Guessing
Password guessing occurs when attackers exploit weak, reused, or predictable passwords to access accounts. Once inside, they can steal data, change settings, or impersonate users, often without being detected for long periods. Automated tools now make these attacks faster and more effective.
Organisations can limit this risk by enforcing strong password rules, enabling multi-factor authentication, and monitoring failed login attempts. Educating employees about password hygiene and avoiding reuse across systems is essential.
Keylogging
Keylogging involves malicious software that secretly records everything typed on a device, including passwords, card details, and private messages. These tools often arrive through infected downloads, fake software updates, or email attachments disguised as legitimate files.
Preventing keylogging relies on updated antivirus software, restricted installation permissions, and secure system configurations. Employees should be trained to avoid unknown downloads and to report unusual device behaviour immediately.
Phishing
Phishing is one of the most common social engineering attacks, where criminals send convincing emails, messages, or links that appear to come from trusted sources. The aim is to trick users into sharing passwords, financial details, or other sensitive information, often without realising anything is wrong.
These attacks are increasingly personalised and may reference real names, roles, or recent activity. Preventing phishing relies on regular staff awareness training, clear reporting processes, and robust email security tools that filter suspicious content before it reaches users.
Malware or Virus
Malware or viruses are malicious programs designed to damage, disrupt, or gain unauthorised access to vital systems. They can spread through infected files, downloads, or links, and once inside a system, they may steal data or compromise operations. Protecting against malware requires strong firewalls, frequent updates, and reliable antivirus tools.
Distributed Denial of Service (DDoS)
Distributed Denial of Service (DDoS) attacks are meant to overwhelm a website or system by flooding it with excessive traffic, making it slow, unstable or completely unavailable. While it does not always involve data theft, it disrupts services and can cause financial losses.
Mitigation includes using traffic filtering tools, load balancing, and having a clear incident response plan.
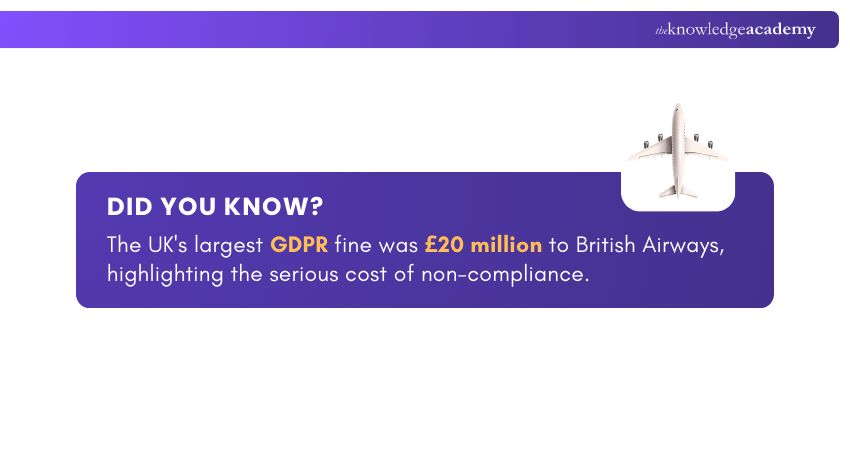
Penalty for a Data Breach
Under the UK GDPR and the Data Protection Act 2018, the Information Commissioner’s Office (ICO) can impose two levels of fines, depending on severity:
a) Standard maximum fine: Up to £8.7 million or 2% of an organisation’s worldwide annual turnover from the previous financial year (whichever amount is higher).
b) Higher maximum fine: Up to £17.5 million, or 4% of the organisation's worldwide annual turnover (whichever is higher). This applies to more serious GDPR Data Breaches.
Each of these tiers applies under the following scenarios:
a) Standard maximum fines typically apply when there are violations of administrative requirements. This includes failure to comply with controller/processor obligations (Chapter IV), or rules regarding the processing of children's data under Article 8 or exemptions under Article 11.
b) Higher maximum fines apply to more significant breaches involving fundamental principles and rights. This includes breaches of data processing principles, consent requirements, data subject rights, or international data transfers.
What are GDPR Violations?
GDPR violations refer to breaches of the European Union’s GDPR, which governs how organisations collect, process, store, and transfer personal data of individuals within the EU. Common GDPR violations include:
a) Non-compliance with data processing principle
b) Insufficient fulfillment of data subject rights
c) Lack of legal basis for data processing
d) Failure to cooperate with supervisory authorities
e) Insufficient technical and organisational security measures
Data protection isn’t just a regulation; it’s a mindset. Learn how to cultivate it in our Certified EU General Data Protection Regulation (EU GDPR) Foundation Course now!
What are the 4 actions of a data breach?
When a Data Breach occurs, GDPR expects organisations to act quickly and methodically. The first step is to identify what has happened by understanding how the incident occurred, what data is affected, and who may be impacted. This is followed by containment, where systems are secured, access is restricted, and immediate measures are taken to prevent further data loss.
Next, organisations must assess the level of risk to individuals by considering the nature of the data and the potential harm. If the breach poses a significant risk, it must be reported to the ICO within 72 hours, and affected individuals should be informed without delay. These actions ensure transparency, limit damage, and uphold accountability.
Conclusion
A GDPR Data Breach can cause many serious problems. So, it is essential to understand its definition, its method of occurrence, and its various existing types. The Data Security assessment should be conducted by companies to decrease their potential breach risks. The organization needs to implement top safety measures while building staff competence in appropriate personal data management. Companies achieve compliance through ongoing proactive measures which also enhance customer trust.
Awareness is the first step to compliance. Sign up for our comprehensive GDPR Awareness Training and take the lead in safeguarding privacy!
Frequently Asked Questions
Can a GDPR Breach be Avoided Through Employee Training?

Yes, employee training can help stop many GDPR Data Breaches. When staff know how to handle personal data safely. They are less likely to make mistakes like sending details to the wrong person or opening unsafe links. Regular training also keeps them aware of the rules and how to follow data protection steps.
Can a GDPR Breach be Remedied, or are There Long-term Consequences?

Some GDPR Data Breaches can be fixed if the company acts fast. They must report the breach, tell the people affected and improve their security. However, some breaches can cause long-term problems like losing customer trust, getting fined or affecting the company’s name.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various GDPR Training, including the GDPR Awareness Training and Data Privacy Awareness Course, and the Certified EU General Data Protection Regulation (EU GDPR) Foundation and Practitioner. These courses cater to different skill levels, providing comprehensive insights into Data Breach.
Our IT Security & Data Protection Blogs cover a range of topics related to GDPR Training, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your IT Security & Data Protection skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

Richard Harris is a highly experienced full-stack developer with deep expertise in both frontend and backend technologies. Over his 12-year career, he has built scalable web applications for startups, enterprises and government organisations. Richard’s writing combines technical depth with clear explanations, ideal for developers looking to grow in modern frameworks and tools.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Certified Data Protection Officer (CDPO)
Certified Data Protection Officer (CDPO)
Fri 3rd Jul 2026
Fri 31st Jul 2026
Fri 2nd Oct 2026
Fri 30th Oct 2026
Fri 20th Nov 2026
Fri 4th Dec 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


