We may not have the course you’re looking for. If you enquire or give us a call on 01344203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

In today's digital world, where Personal Data is gathered and stored on an unprecedented scale, ensuring individuals' privacy has never been more critical. This is where the General Data Protection Regulation (GDPR), the EU's legal framework, comes in to enforce strict rules and guidelines for organisations to protect sensitive data. At the heart of GDPR compliance lies the GDPR Risk Assessment. It is a vital component of the broader GDPR Audit process.
The risk assessment process involves systematic identification, analysis, and evaluation of risks and vulnerabilities in Data Protection. According to Statista, one of the most significant fines for violating GDPR (due to insufficient legal grounds for processing data) reached nearly £4.3 million. With the rising frequency of data breaches and privacy concerns, GDPR grows increasingly essential for organisations seeking to safeguard personal information. This blog outlines the steps to conduct an effective GDPR Risk Assessment. Read on and ensure strengthened Data Security for your organisation.
Table of Contents
1) What is GDPR Risk Assessment?
2) Why are Risk Assessments by GDPR Essential?
3) GDPR Risk Assessment Methodologies
4) A Step-by-step Guide to Conduct GDPR Risk Assessments
5) Tools and Resources for Risk Assessments by GDPR
6) Conclusion
What is GDPR Risk Assessment?
A GDPR Risk Assessment is a process of identifying, analysing and evaluating the potential threats and vulnerabilities that may affect the Personal Data of individuals in the European Union. A GDPR Risk Assessment helps organisations comply with the GDPR regulations, which aim to protect the privacy and security of Personal Data. It also helps organisations to implement appropriate measures to reduce the risks and to demonstrate their accountability and transparency.
It is also required to process personal data, which might put an individual's rights at high risk. It includes some specific types of data processing avenues, such as using new technologies, tracking people's location or behaviour, monitoring public places, processing sensitive personal data, or making automated decisions. This requirement also aligns with GDPR after Brexit changes, especially for UK-based entities dealing with EU data.
Why are Risk Assessments by GDPR Essential?
Risk Assessments by GDPR are significant in the context of Data Protection. These evaluations are crucial in helping organisations identify and mitigate potential risks to the Personal Data they process. Organisations can proactively address vulnerabilities, ensure compliance, and strengthen their overall Data Security posture by conducting a thorough evaluation. Here are some key reasons why Risk Assessments by GDPR are essential:

a) Compliance with GDPR: Organisations must adhere to the strict requirements of the GDPR to protect personal data and uphold individuals' rights. Regular risk assessments are essential in achieving compliance, as they help organisations identify and mitigate potential risks. By addressing these risks, organisations demonstrate their commitment to data protection and reduce the likelihood of non-compliance.
b) Mitigating Data Breach Threats: GDPR risk assessments enable organisations to identify vulnerabilities in their data processing activities, enhancing their understanding of what constitutes a GDPR breach. By proactively addressing these vulnerabilities, organisations can implement appropriate security measures to reduce the likelihood of data breaches.
c) Enhancing Data Security: Through comprehensive evaluations, organisations gain a deeper understanding of their data processing activities and the associated risks. This insight allows them to implement tailored, robust security measures that enhance data security, protect against unauthorised access, and minimise the risk of data breaches.
d) Efficient Resource Allocation: Conducting risk evaluations helps organisations allocate resources effectively by identifying and prioritising risks. This targeted approach ensures that resources are directed towards areas requiring immediate attention, leading to more efficient utilisation.
e) Continual Improvement: GDPR risk analyses are an ongoing process. Regular evaluations enable organisations to monitor and assess the effectiveness of their data protection measures, identifying areas for improvement. By continually adapting to emerging threats and regulatory changes, organisations can ensure their data protection practices remain current and effective.
Looking for enhanced Data Security for your organisation? Sign up for our Certified Data Protection Officer (CDPO) Course now!
GDPR Risk Assessment Methodologies
A consistent and clear set of rules for conducting and interpreting the Risk Assessment is essential for any information security Risk Assessment methodology. This ensures that the risks are evaluated in a uniform way, which helps to prioritise them effectively.
A GDPR Risk Assessment can be done by following standardised methodologies that include:
1) Baseline Security Criteria: The basic level of defences to protect against risks.
2) Risk Scale: A common way of measuring risk.
3) Risk Appetite:It refers to the amount of risk an organisation is willing to overlook.
4) Scenario- or Asset-based Risk Management: The strategies to minimise the impact of certain incidents or that can affect certain parts of the organisation.
A Step-by-step Guide to Conduct GDPR Risk Assessments
By following a structured approach, organisations can effectively assess their data processing activities, identify potential vulnerabilities, and implement appropriate measures to mitigate threats. Here are the key steps involved in conducting a GDPR Risk evaluation:
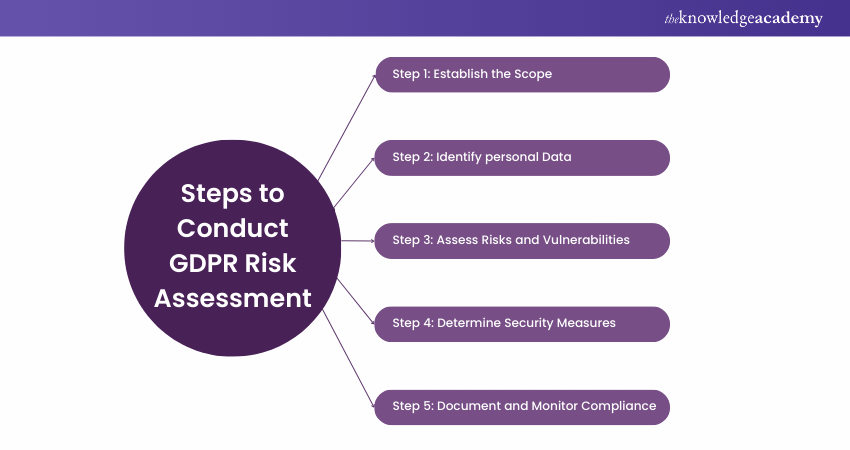
Step 1: Establish the Scope
The first step involves defining the GDPR Scope of the risk evaluation. You must determine the specific data processing activities, processes, and systems that will be included in the analysis. Then, you must consider the types of Personal Data being processed, their purpose, and any third parties involved in the data processing chain.
Step 2: Identify Personal Data
The second step is to identify and document the Personal Data being processed by the organisation. This includes understanding the categories of Personal Data, its source, and the recipients to whom it is disclosed. Consider structured and unstructured data stored in physical and digital formats.
Step 3: Assess Risks and Vulnerabilities
The third step evaluates the potential risks and vulnerabilities associated with data processing. Identify threats such as unauthorised access, data breaches, loss, or corruption. You must consider the impact and likelihood of each threat, considering factors such as the sensitivity and volume of the data.
Step 4: Determine Security Measures
Based on the identified threats, determine the appropriate security measures to mitigate them. This may include taking technical steps such as encryption, access controls, data anonymisation and organisational measures such as policies, training, and awareness programs. Consider the "Privacy by Design and Default" principle when selecting and implementing security measures.
Step 5: Document and Monitor Compliance
The final step involves documenting the risk evaluation outcomes, including the identified threats, vulnerabilities, and the corresponding security measures. Develop a risk register or similar document to record and track the evaluation findings. It is essential to establish monitoring mechanisms to ensure ongoing compliance with the identified security measures and to detect and address any new threats or vulnerabilities that may arise.
Gain in-depth knowledge and practical skills to navigate the complexities of GDPR compliance with our Certified EU GDPR Practitioner Course now!
Tools and Resources for Risk Assessments by GDPR
GDPR Requirements like risk evaluations and data processing are conducted frequently. To facilitate this process, organisations can leverage various tools and resources that assist in the efficient and effective execution of evaluations. Let's look at a few key tools and resources that can be utilised:
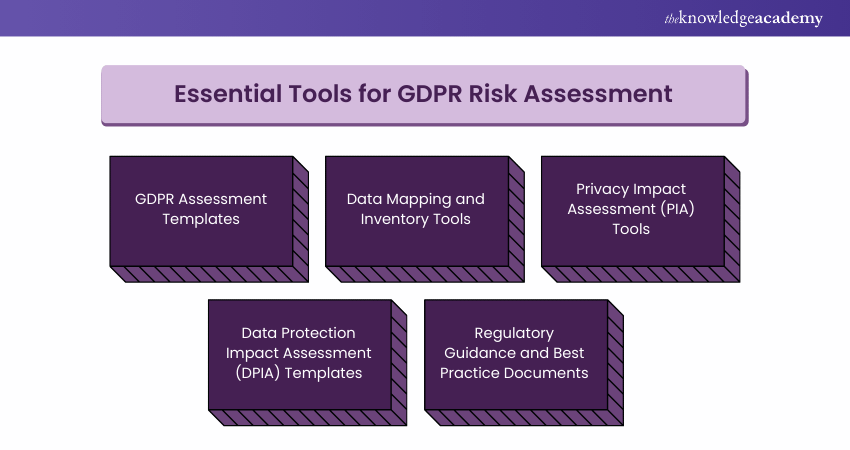
a) GDPR Assessment Templates: These templates provide a structured framework for conducting risk evaluations.
b) Data Mapping and Inventory Tools: Data mapping and inventory tools help organisations understand the flow of Personal Data within their systems and processes.
c) Privacy Impact Assessment (PIA) Tools: PIA tools aid in evaluating the impact of data processing activities on individuals' privacy rights and identifying associated threats.
d) Data Protection Impact Assessment (DPIA) Templates: DPIA templates assist organisations in conducting evaluations specifically focused on high-threat data processing activities.
e) Regulatory Guidance and Best Practice Documents: Regulatory authorities and industry associations provide guidance and best practice documents related to GDPR compliance and potential threat evaluations. Utilising a GDPR Best Practices Implementation Guide can further enhance understanding and implementation of effective compliance strategies.
Stay informed about GDPR—download the GDPR Cheat Sheet today!
Conclusion
In our increasingly data-driven world, GDPR Risk Assessment is essential for strengthening data protection. By identifying and mitigating risks, organisations can comply with GDPR regulations, safeguard personal data, and build trust with customers and employees. GDPR Audit can further support these efforts by offering practical guidance tailored to your data governance strategies. We hope this blog guides you in the same direction for your organisation.
Increase Data Privacy awareness within your organisation by registering for our Data Privacy Awareness Course now!
Frequently Asked Questions
What Tools Can Assist With GDPR Risk Assessments?

Tools like OneTrust, Varonis, and TrustArc provide automated risk assessment frameworks, compliance tracking, and data privacy management. These platforms help businesses identify and manage potential risks, ensuring GDPR compliance by offering tools for data mapping, policy creation, and breach monitoring.
Can Small Businesses Benefit From a GDPR Risk Assessment?

Yes, small businesses can greatly benefit from GDPR Risk Assessments. These assessments help identify data privacy risks, ensure compliance, and avoid costly penalties. Implementing proper risk management can enhance trust with customers, protect sensitive data, and streamline business operations.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000 online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 19 major categories, we go the extra mile by providing a plethora of free educational Online Resources like News updates, Blogs, videos, webinars, and interview questions. Tailoring learning experiences further, professionals can maximise value with customisable Course Bundles of TKA.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various GDPR Courses, including the Certified Data Protection Officer (CDPO) Course and the EU General Data Protection Regulation Awareness Course. These courses cater to different skill levels, providing comprehensive insights into Data Protection.
Our Data Protection Blogs cover a range of topics related to GDPR, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your understanding of GDPR, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Certified Data Protection Officer (CDPO)
Certified Data Protection Officer (CDPO)
Fri 3rd Jul 2026
Fri 31st Jul 2026
Fri 2nd Oct 2026
Fri 30th Oct 2026
Fri 20th Nov 2026
Fri 4th Dec 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


