We may not have the course you’re looking for. If you enquire or give us a call on 01344203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Have you ever wished you could anticipate a hacker’s next move before they strike? That’s exactly what the Cyber Kill Chain helps you do. Developed as a framework to understand the stages of a cyberattack, it breaks down how intrusions unfold from initial scouting to data theft.
In this blog, we’ll simplify what is a Cyber Kill Chain and explain each stage with practical insights. Whether you’re a student, IT beginner, or professional aiming to stay one step ahead of cyber threats this knowledge can strengthen your cybersecurity awareness.
Table of Contents
1) What Is the Cyber Kill Chain Framework?
2) The Phases of Cyber Kill Chain
3) Benefits of The Cyber Kill Chain Model
4) Implementing the Cyber Kill Chain
5) Cyber Kill Chain Challenges
6) How to Disrupt the Cyber Kill Chain Process?
7) Conclusion
What Is the Cyber Kill Chain Framework?
Cyber Kill Chain explains how a hacker collects information secretly, then sends some malware and slowly enters and damages the system. This model is inspired from military strategy to help organisations form a defence to safeguard data and systems by knowing every hacking step.
If you know these stages in advance, you can easily stop the attack from completely taking over your system and data. That's why Cyber Kill Chain is very useful. It makes you smarter, helps you understand the hackers' plans in advance, and keeps your digital world safe.
The Phases of Cyber Kill Chain
The stages involved in the Cyber Kill Chain explain step-by-step how attackers plan to enter a target system. Understanding these stages can help security experts strengthen their defence. These stages are something like this:
1) Reconnaissance
The beginning stage is Reconnaissance, where the attacker collects the data and enters the user system. Using passive scanning, social engineering and open-source intelligence the attacker makes his entry. Understanding how Cyber Kill Chain functions helps in eliminating the attack in the initial stage.
2) Weaponisation
In the Weaponisation phase the attackers use the data collected from the initial stage to convert it into a weapon tool to attack the vulnerabilities of the organisations or the weakness of the user. The tools can be advanced malware, viruses or phishing emails. These tools become the essential factor of next phase.
3) Delivery
Once the malware is ready the next phase is action, the delivery of the malware. One of the usual traps is phishing email where employees are tricked into sharing their ID and passwords. Hackers also enter through shared wireless connection that is not very secure or a vulnerability in software or equipment which was noted during reconnaissance.
4) Exploitation
During the exploitation phase, the attacker takes advantage of a vulnerability to execute malicious code on the target system. This could involve exploiting software bugs, weak configurations, unpatched systems, or social engineering to trigger malware execution. Once the vulnerability is exploited, the attacker gains a foothold that allows further actions, such as installing tools, escalating privileges, or moving deeper into the network. Effective patch management and hardened configurations help reduce the risk at this stage.
5) Installation
This stage occurs when an attacker successfully installs malware, backdoors, or malicious tools on the compromised system. The goal is to establish persistence and ensure continued access without detection. Attackers may disable security controls or modify system settings to remain hidden. Once installed, the malware prepares the system for command and control communication.
6) Command and Control
Once cyberattack have acquired control over a large number of systems, they establish a control center that enables them to have remote control. At this phase they employ obfuscation in order to conceal their tracks and prevent detection. The denial-of-service attacks are also used by them to keep the security minds off track.
7) Actions on Objectives
In this stage, the attacker achieves his main goal. This goal can be anything, such as stealing important files, accessing sensitive information, slowing down or shutting down a service, or taking complete control of the system. This phase is the final move of the attack where the attacker's plan works. If the organisation is unable to stop the attacker till this point, it can have a major impact on its data, users, and systems.
Gain knowledge of Cyber Security concepts and skills with Certified Cyber Security Professional (CCS-PRO) Course – Join now!
Benefits of The Cyber Kill Chain Model
The Cyber Kill Chain model is a valuable framework for security teams as it breaks a cyber attack into clear, manageable stages. This structured view helps teams detect suspicious activity early, respond faster, and disrupt attacks before serious damage occurs. Knowing the way attackers work, organisations can make the defences more robust and enhance the overall response to the threats. Key benefits of the Cyber Kill Chain model include:
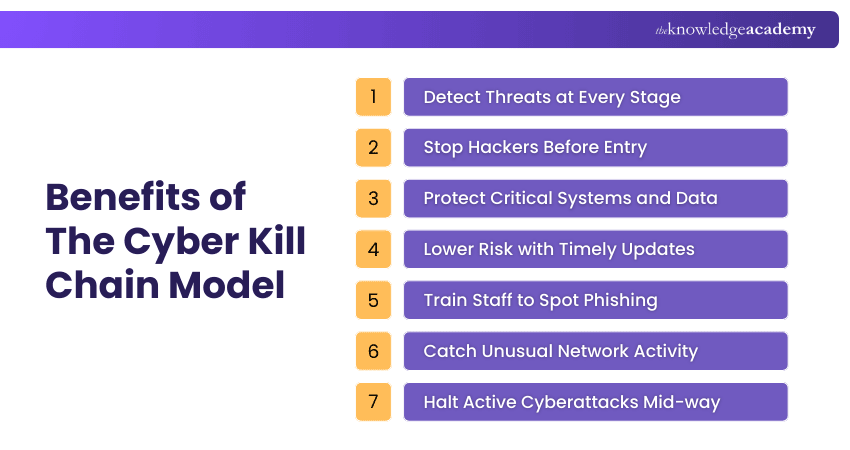
1) Helps detect cyber threats at every level of attack
2) Allows attackers to be prevented prior to gaining access to the systems
3) Secures important data, systems and user accounts
4) Minimises threat by drawing attention to old software and infrastructure
5) Enhances phishing and fraudulent email awareness among employees
6) Identifies the abnormal internal network activity at the early stage
Presents the chance to break attacks when they are being performed Equip your team with essential knowledge – Sign up now for our Cyber Security Awareness Training - Join now!
Implementing the Cyber Kill Chain
The Cyber Kill Chain implementation is the process of combining people, processes, and security technologies to detect and interrupt the attacks throughout the stages. The following controls assist organisations in implementing the model successfully within their security operations.
1) Threat intelligence
Threat intelligence enables the security teams to learn about attacker tactics, methods, and behaviour. By analysing real-time and historical threat data, organisations can identify early attack indicators and respond before threats escalate.
2) Identity and Access Management
Identity and access management controls who can access systems and data. Strong authentication and access policies help stop attackers from misusing stolen credentials and progressing through later attack stages.
3) Security Information and Event Management
SIEM tools gather and associate logs throughout the environment. This central visibility can be used to identify suspicious patterns and identify attack activity at various stages of the kill chain.
4) Endpoint Detection and Response
Endpoint detection and response constantly scan devices in search of abnormal behaviour. It allows quick investigation and containment in case the endpoints are revealing indicators of compromise or mischief.
5) Extended Detection and Response
Extended detection and response bring together data from endpoints, networks, and cloud environments. This combination view enhances the detection of precision and assists security staff to react quicker to intricate and multi-stage assaults.
6) Managed Detection and Response
Managed detection and response offer 24/7 surveillance by security professionals. It assists organisations in detecting threats, investigating incidents, and acting when the in-house resources are insufficient.
Cyber Kill Chain Challenges
The Cyber Kill Chain model is quite helpful, but there are some limitations in complex attacks. Relying on this model alone is not enough to protect against all types of cyber threats. Below are some common challenges:
1) Focused on Malware
This model was mostly designed to detect malware. This model can fail if an attacker gains access to the system without using malware, just by using stolen credentials or phishing.
2) Ideal for Perimeter Security
Earlier, this model worked when there was only a network perimeter. Today, due to cloud systems, remote devices and multiple access points, it has become difficult to apply defence everywhere.
3) Not Equipped for Insider Threats
If employees or authorised logs misuse the system, then the Cyber Kill Chain cannot detect them. User behaviour monitoring is necessary to catch such threats.
4) Too Linear
The model is designed for step-by-step attacks, but not every hacker attacks like this. Sometimes, attackers attack by combining all the steps together, which goes beyond the scope of this model.
How to Disrupt the Cyber Kill Chain Process?
1) Identify and block reconnaissance activity: Threat intelligence and attack surface management can be used to minimise the exposure of systems and the discovery that attackers may have in your environment.
2) Patch vulnerabilities and manage exposures: Software, systems and configurations should be updated frequently to avoid attackers using known vulnerabilities at an early stage of attack.
3) Stop malicious delivery methods: Use email, web and attachment filters to prevent phishing attacks and malware in transit before delivery to users.
4) Prevent exploitation and installation: Install endpoint protection and behaviour monitoring tools to prevent the execution and installation of malicious code on the devices.
5) Disrupt command and control communication: Track and block any suspect network traffic so that attackers cannot remotely control the compromised systems.
6) Apply layered security controls: Engage several different defensive technologies to identify abnormal behaviour at an earlier stage and to disrupt attacks at various stages of the kill chain.
7) Strengthen security awareness training: Educate employees to be aware of phishing and social engineering attacks that are frequent causes of cyber-attacks.
Conclusion
Cyber Kill Chain is a model that helps you understand every step of a hacker. If you identify these stages on time, you can stop the attack before it happens. Staying secure is important in today's world, and this model can become an important part of that journey. With just the right tools and knowledge, you can make your system strong.
Build a foundation for a secure digital future – Sign up now for our course on Introduction to System and Network Security.
Frequently Asked Questions
What is the Difference Between Mitre ATT&CK and Cyber Kill Chain?

MITRE ATT&CK is a comprehensive framework that maps attacker tactics and techniques in detail, showing how adversaries operate across different environments. In contrast, the Cyber Kill Chain outlines the sequential stages of a cyber attack, helping teams understand how attacks progress from reconnaissance to execution.
What are Some Cyber Kill Chain Tools and Technologies?

Some commonly used Cyber Kill Chain tools and technologies include SIEM solutions, threat intelligence platforms, EDR tools, and firewalls. These technologies support different attack stages by helping organisations detect suspicious activity, analyse threats, and respond quickly to security incidents.
What are the Other Resources and Offers provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Courses, including the Certified Cyber Security Professional Training, Cyber Security Awareness Course and Cyber Security Risk Management Course. These courses cater to different skill levels, providing comprehensive insights into Cyber Security Jobs.
Our IT Security & Data Protection Blogs explore a wide range of topics, from understanding What is Cyber Security and What is Cyber Security Attack. Featuring insights on the Cyber Kill Chain, best practices, and expert guidance, these blogs are ideal for anyone looking to strengthen their cyber knowledge. The Knowledge Academy also offers a variety of courses to support your journey in mastering Cyber Security.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Certified Cyber Security Professional (CCS-PRO)
Certified Cyber Security Professional (CCS-PRO)
Fri 24th Jul 2026
Fri 9th Oct 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


