We may not have the course you’re looking for. If you enquire or give us a call on 01344203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.
Cyber threats are evolving at an unprecedented pace, and Ransomware has emerged as one of the most disruptive forms of attack. From small businesses to global enterprises, organisations across sectors are being targeted, often facing operational shutdowns, financial losses, and reputational damage.
Understanding What is Ransomware is no longer optional for IT teams and business leaders. This blog explores how ransomware works, the major types of attacks, notable real-world examples, and the essential prevention strategies required to strengthen organisational Cyber Security.
Table of Contents
1) What is a Ransomware Attack?
2) How Does Ransomware Work?
3) Types of Ransomware
4) Stages of a Ransomware Attack
5) Popular Ransomware Variants
6) How to Prevent Ransomware Attacks?
7) Real-world Ransomware Examples
8) Conclusion
What is a Ransomware Attack?
Ransomware is a type of malicious software (malware) that prevents users from accessing their systems or data, typically by encrypting files, until a ransom payment is made to the attacker. Such attacks are also prone to organisations that handle sensitive information like personal data, financial data, and intellectual property, among others.
As such, Ransomware can be considered one of the most widespread cyber threats in the present day, which was first introduced in the 1980s. Ransomware attacks have become more manageable to carry out and difficult to track due to technological progress, further digitalisation, remote working, and the emergence of cryptocurrency.
How Does Ransomware Work?
A ransomware attack is a methodical process, made in such a way that particular systems are penetrated, critical data is encrypted, and the victims are compelled to pay a ransom. Knowledge of each of the stages assists organisations to identify threats at the first moment and become more responsive:
1) Infection: Ransomware gets into the systems via email spam, guest downloads, hacked sites, or automated transmissions of the network, which is usually camouflaged as legitimate files.
2) Payload and Encryption: It encrypts files on-site with strong encryption and can block any recovery routes to negate recovery.
3) Ransom Demand: A message is sent that is a demand and can be made through untraceable means, and if not paid on time, there will be a threat of a higher ransom.
4) Decryption: Once a payment has been made, the attackers can give out a decryption key, but not always access to data.
Learn to detect and remove malware using real-world analysis. Join our Malware Analysis Training today!
Types of Ransomware
Ransomware has become one of the most common cyber threats, and attackers can launch it with little effort. Here are some common types:
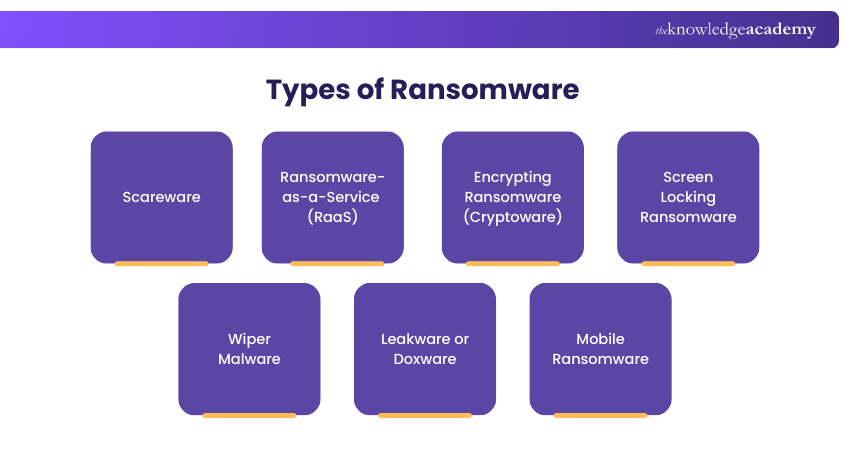
1) Scareware
Scareware is harmful software that tries to frighten or trick people. It may say your computer has a fake virus or another problem. The goal is to make you buy software you don’t need. To avoid scareware, only trust warnings from well-known and trusted antivirus companies.
2) Ransomware-as-a-Service (RaaS)
Ransomware-as-a-Service (RaaS) is a business model used by cybercriminals where developers create ransomware and sell or rent it to others. This allows people with little technical knowledge to launch attacks easily. The RaaS operators take a share of the ransom paid, while the attacker keeps the rest.
3) Encrypting Ransomware (Cryptoware)
This Ransomware locks your files using special codes. It then shows a message telling you how much to pay to get them back. Like screen lockers, you can use a backup to restore your computer instead of paying.
4) Screen Locking Ransomware
This type locks your computer screen so you can’t use it. You may see a message asking you to pay money to unlock it. Sometimes it pretends to be from the police or another authority. Experts say you should not pay. Instead, wipe your system and restore it from a recent backup.
5) Wiper Malware
Wipers, also called destructive Ransomware, threaten to delete your data if you don’t pay. Sometimes, they erase the data even if you do pay. This kind of Ransomware is often used by governments or activist hackers, not regular cybercriminals.
6) Leakware or Doxware
A type of ransomware, more specifically a type of data theft ransomware, that extorts sensitive information and threatens to leak it online. Recent versions tend to use data theft together with encryption in order to put more pressure on the victims. This is a two-sided risk and, therefore, Leakware can be very harmful to organisations dealing with classified information.
7) Mobile Ransomware
Mobile ransomware attacks smartphones and tablets, and usually distributes via virus apps or downloads in a broken state. Screen-locking techniques are adopted by most mobile attacks instead of encryption because it is easy to retrieve the data in cloud backups.
Stages of a Ransomware Attack
Since now you know What is Ransomware and its types, Ransomware attack usually happens in these steps:
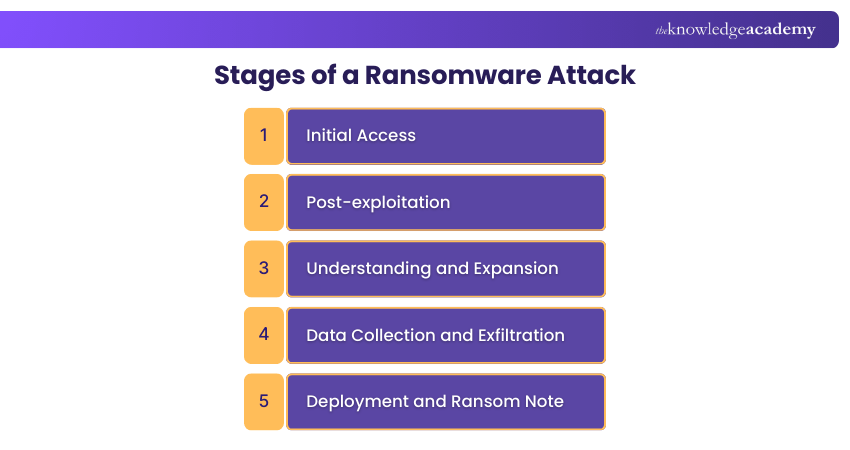
1) Initial Access: Attackers have access to the initial step via phishing messages, vulnerabilities, or weakened remote access protocols, including the RDP.
2) Post-exploitation: As the next move, malicious software or remote-access protections are installed in order to provide authority in the system.
3) Understanding and Expansion: Hackers scan and scale the network until they obtain access to additional systems and domains.
4) Data Collection and Exfiltration: Valuable data, including credentials, sensitive information, etc., is identified and stolen to be extorted.
5) Deployment and Ransom Note: The files are encrypted, or the devices are locked down, backup services are turned off, and a ransom note is issued with payment instructions.
Gain hands-on experience developing cyber risk strategies and response plans. Join our Cyber Security Risk Management Training now!
Popular Ransomware Variants
Ransomware continues to evolve, with numerous variants emerging that use diverse tactics and targets to extort victims. The following are some well-known Ransomware strains that have made significant impacts on organisations worldwide:
1) Black Basta
Ransomware as a service is known as Black Basta, which targets businesses through exploited vulnerabilities in the system. It usually encrypts the data and steals sensitive information, and then asks for money.
2) Royal
Royal ransomware is characterised by its forceful double-extortion strategy, which encrypts files and threatens to publish stolen information. It attacks across the board and has grown to impact Windows as well as Linux machines.
3) Play (PlayCrypt)
Play or PlayCrypt is a file-encryption programme that adds a suffix to files, which is. Play. It combines data theft and encryption in order to compel victims to hand over the ransom.
4) Dharma/Phobos
Dharma and its successor Phobos were mostly distributed with the help of damaged remote desktop sessions and phishing. Such variants are still prevalent because they are simple and effective in the encryption of the networked systems.
Gain in-depth knowledge of Cyber Security concepts and skills. Join our Certified Cyber Security Professional (CCS-PRO) Training now!
How to Prevent Ransomware Attacks?
The prevention of ransomware involves a set of active security steps, awareness efforts, and solid practices of systems within a company. These measures will minimise the risk of attack and enhance defence strength. The strategies are:
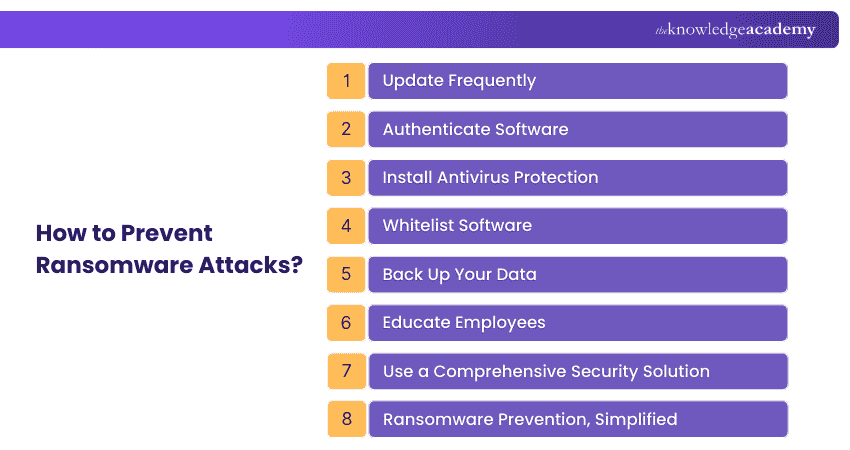
1) Update Frequently
Scan all software, operating systems, and security tools with the latest patches and fixes. Periodic updating seals the vulnerabilities through which ransomware developers usually find their way.
2) Authenticate Software
Download applications only from a reliable source and check the integrity of the software. Multi-factor authentication provides an additional access control measure that can be used to prevent unauthorised access.
3) Install Antivirus Protection
Install the trustworthy antivirus and anti-malware software to identify and stop the ransomware before it runs. The use of email filtering and advanced firewalls also helps to lessen the threat of malicious attachments making it to the consumers.
4) Whitelist Software
Implement application whitelisting in order to execute approved programmes only. This will block the execution of untrusted or unknown software, which will lead to a ransomware attack.
5) Back Up Your Data
Periodically transfer important data to offline places. Although backups will not prevent ransomware, this is so that you will be able to restore the systems without paying a ransom.
6) Educate Employees
Educate and train personnel on phishing attacks, links, and unsafe downloads. Human error is a primary entry point of ransomware that awareness helps to minimise.
7) Use a Comprehensive Security Solution
Integrate web filtering, firewalls, endpoint protection, and email security in a layered defence. It is a more effective mitigation of ransomware and detection using this multi-layered approach.
8) Ransomware Prevention, Simplified
Ransomware prevention does not necessarily need to be complicated; a combination of updated systems, quality authentication, frequent backups, employee training, and quality security protection tools will form a strong fence against the new-age ransomware.
Real-world ransomware examples
The real-life examples of ransomware are the following:
1) LockBit
Founded in 2019, LockBit is a ransomware-as-a-service provider that allows affiliates to attack the financial services, healthcare, and manufacturing industries. It is characterised by the ability to spread across compromised networks and quickly encrypt systems, causing mass disruption to operations.
2) Hive
As active in 2021-2023, Hive focused on government facilities and critical infrastructure, especially healthcare facilities. This group employed the methods of double extortion, encrypting and exfiltrating data and asking to be paid ransom. In 2022, it was hit by the Federal Bureau of Investigation, which did not allow sending more than $130 million in ransom.
Conclusion
Ransomware continues to evolve in scale and sophistication, posing serious operational and financial risks to organisations worldwide. Understanding What is Ransomware, how it spreads, and the damage it can cause is critical for informed decision-making. By recognising common attack patterns and implementing strong prevention measures, businesses can significantly reduce exposure. Proactive cyber security is no longer optional; it is a strategic necessity.
Learn how to detect and defend against modern cyber threats with our Cyber Security Training – Join now!
Frequently Asked Questions
How do Ransomware Attacks Use Psychological Tactics to Pressure Victims?

Ransomware attacks use fear and time pressure to manipulate victims, often through threatening messages, countdown timers, and warnings of data exposure or permanent loss. These tactics are designed to create panic and force rushed payment decisions.
Why is Ransomware Becoming More Common in Modern Enterprise Environments?

Ransomware is increasing in enterprise environments because organisational data has become highly valuable. Attackers now use double-extortion tactics, operate as organised criminal groups, and target enterprises at scale for maximum financial gain.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Training, including the Cyber Security Awareness Training, Cyber Security Risk Management Training, and the Malware Analysis Training. These courses cater to different skill levels, providing comprehensive insights into What is Spyware.
Our IT Security & Data Protection Blogs cover a range of topics related to Ransomware, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your IT Security & Data Protection skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Cyber Security Awareness
Cyber Security Awareness
Fri 21st Aug 2026
Fri 20th Nov 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


