We may not have the course you’re looking for. If you enquire or give us a call on 01344203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Have you ever noticed a strange charge on your bank statement or received a message about an account you never opened? That sudden wave of confusion and worry might be your first encounter with something serious: identity theft. In today’s digital world, understanding What is Identity Theft is essential for keeping your personal and financial information safe.
Think of your identity as your digital fingerprint, something unique and valuable that defines who you are. When criminals get hold of it, they can use it to steal money, open fake accounts, or even impersonate you. Learning What is Identity Theft is the first step towards protecting yourself.
Table of Contents
1) What Is Identity Theft?
2) Types of Identity Theft
3) How Identity Theft Happens?
4) How to Protect Yourself from Identity Theft?
5) What Do You Do If Someone Has Stolen Your Identity?
6) Examples of Identity Theft
7) Conclusion
What Is Identity Theft?
Identity Theft occurs when someone steals your personal information, such as credit card details, bank account numbers, or ID documents, to commit fraud. This can lead to unauthorised purchases, the creation of false accounts, and even significant financial losses.
Some of the longer-term consequences include damage to your credit score, ongoing financial difficulties, and inaccurate financial records. To stay protected, regularly monitor your bank accounts and credit reports, stay alert for data breaches, freeze your credit if needed, and report any activity that appears suspicious.
Types of Identity Theft
Identity Theft can take many forms, depending on how a criminal uses your personal information to commit financial fraud or other crimes. Below are some of the most common types of Identity Theft that can put your finances, credit, and reputation at risk.

1) Tax Identity Theft
In Tax Identity Theft, scammers steal your personal and financial information, including your Social Security number, to fill false tax returns in your name and access refunds. This type of theft often goes undetected until the legitimate taxpayer submits their return and it is rejected.
2) Financial Identity Theft
Financial Identity Theft is the most common form, where criminals gain access to your bank or credit card information and use it without permission. They may make unauthorised purchases, open new accounts, or apply for loans using your identity, leaving you with financial and credit problems.
3) Child Identity Theft
With a child, personal information that goes unnoticed for years is used by the thieves to apply under his or her name, credit, loans, or jobs. This type of theft can go unnoticed until the child becomes an adult.
4) Medical Identity Theft
In this type of theft, an offender uses another person’s identity to obtain medical services, prescription drugs, or to file fraudulent insurance claims. This not only affects the victim’s financial records but can also result in incorrect medical information being added to their personal health history.
5) Social Security Identity Theft
In this case, a criminal steals your Social Security number and uses it to open credit accounts, claim benefits, or commit other types of fraud. Victims may face issues such as benefit denials, unexpected debt, and complications in tax or financial documentation.
6) Synthetic Identity Theft
Synthetic Identity Theft is a more sophisticated form of crime, where fraudsters combine real and fabricated personal information to create an entirely new identity. These false identities are then used to open fraudulent credit accounts, obtain loans, or make expensive purchases.
7) Criminal Identity Theft
Criminal Identity Theft occurs when an offender provides stolen personal details of another individual during an arrest or legal encounter. This can lead to false criminal records being created under the victim’s name, which are often difficult to trace or remove without significant legal intervention.
Learn how to identify phishing, scams, and insider threats before they cause damage with our Cyber Security Awareness Course – Join now!
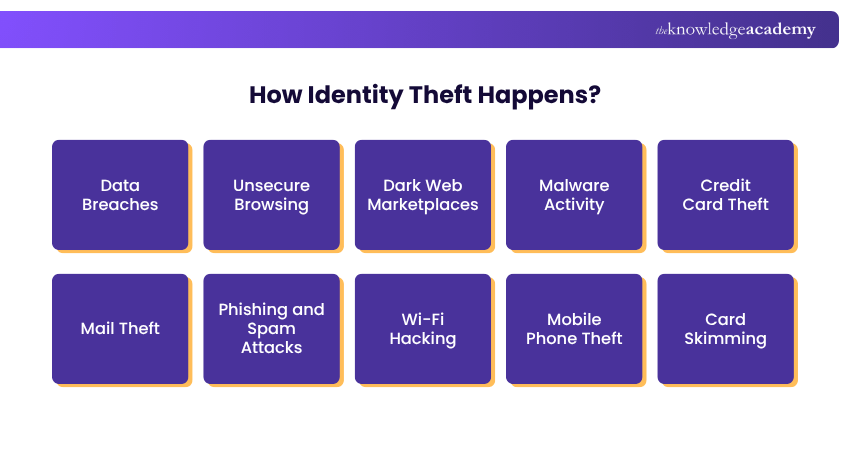
How Identity Theft Happens?
Identity Theft can occur through various tactics that target your personal information, often resulting in stolen credit card numbers, compromised accounts, or fraudulent financial activity. Here are the most common methods
1) Data Breaches
Hackers gain unauthorised access to company databases that store sensitive information such as credit card details, Social Security numbers, and full identity profiles. Victims often discover their personal data has been sold or used to create fake accounts long after the breach occurs.
2) Unsecure Browsing
Your personal details can fall into the hands of cybercriminals when you visit unsecure or fraudulent websites. Information entered on these pages can be intercepted or stolen through malicious forms. Avoid entering credit card or financial details on sites that are not verified or encrypted.
3) Dark Web Marketplaces
Once stolen, personal and financial data are often sold anonymously on dark web marketplaces. Thieves use this information to make illegal purchases or resell it to others for profit. Once listed online, it becomes nearly impossible to track or control where your information goes.
4) Malware Activity
Malware programs can infect your device to track activity or record keystrokes, capturing sensitive data such as passwords, credit card details, and online account credentials. These malicious programs often enter through phishing emails, unsafe downloads, or infected links.
5) Credit Card Theft
With access to your stolen credit card details, thieves can make unauthorised purchases or sell the information to others. Even brief possession of your physical card can lead to substantial losses. Always report lost or stolen cards immediately to your bank or provider.
6) Mail Theft
A traditional yet effective form of Identity Theft occurs when criminals steal physical mail or rummage through discarded documents. Items such as bank statements, credit card offers, and tax forms are prime targets. Always shred paperwork containing personal or financial information before disposing of it.
7) Phishing and Spam Attacks
Fake emails or text messages can trick you into revealing personal or financial information. These messages often direct you to counterfeit websites or ask you to fill out fraudulent forms. Once scammers gain access to your details, they can open new accounts or steal money from existing ones.
8) Wi-Fi Hacking
Hackers can intercept the information you send over public Wi-Fi networks. This may include login credentials, passwords, or credit card details. Always use secure connections and avoid sharing personal information when connected to open or public Wi-Fi.
9) Mobile Phone Theft
Mobile phones often store sensitive data such as saved passwords, account access, and authentication codes. If your phone is stolen and unlocked, a thief can access emails, messages, and even two-factor or Multi-Factor Authentication for codes, giving them complete access to your accounts.
10) Card Skimming
Card skimming involves the use of hidden devices placed on ATMs or payment terminals to capture your card details during a transaction. In some cases, small cameras are also installed to record your PIN or password as you enter it. Always inspect machines before use and cover the keypad when entering your PIN.
11) Child ID Theft
Criminals can use a child’s National Insurance number or personal information to open credit accounts or rent properties. This type of theft often remains undetected for years, causing serious damage to the child’s future credit history. Parents should regularly check or freeze their children’s credit files to help prevent misuse.
12) Tax ID Theft
In tax Identity Theft, criminals use your personal information to file fraudulent tax returns and claim refunds in your name. Victims often discover the theft only when their legitimate return is rejected. This can delay refunds and expose further financial vulnerabilities.
Gain skills to manage cyber risks and ensure business continuity and resilience with our Cyber Security Risk Management Course – Join now!
How to Protect Yourself from Identity Theft?
While no method offers complete protection, these steps can help safeguard your personal, financial, and credit information from Identity Theft:

1) Safeguard Your Devices
Use strong passwords or biometric authentication to secure your phone and computer. Regularly install software updates to patch security vulnerabilities, and avoid leaving your devices unlocked or unattended, especially in public or crowded areas.
2) Use a Password Manager
A password manager helps you create and store strong, unique passwords for all your online accounts. Avoid using the same password across multiple platforms, particularly for banking or financial services. This tool allows you to manage login credentials easily without compromising security.
3) Protect Personal Documents
Always choose e-statements to limit Mail theft exposure. Before disposing of any document with personal information, shred them. Remove mail every day and lock sensitive forms and notices.
4) Watch Out for Phishing Scams
Be cautious of emails or text messages that request your account details or credit card information. Always verify the sender, hover over links to check their legitimacy, and use antivirus software to scan suspicious attachments or websites before clicking.
5) Don't Share Information Over the Phone
Scammers can identify as legitimate businesses to solicit financial information. Always verify unknown callers and never give out sensitive information hastily.
6) Check Your Credit Reports Regularly
Review your credit reports frequently for unusual activity or unauthorised accounts. Each major credit bureau is required to provide at least one free report per year. Monitoring your credit helps detect Identity Theft early and prevents greater financial damage.
7) Be Vigilant When Online
Use a VPN when connecting to public Wi-Fi to keep your data secure. Avoid entering personal or financial information on websites that do not use HTTPS encryption. Research unfamiliar websites before making purchases or sharing information.
8) Consider Identity Theft Protection Services
Reputable companies such as Experian offer identity protection services that monitor your credit activity, scan the dark web, and alert you to suspicious behaviour. They also provide insurance and recovery support if you become a victim of Identity Theft.
Understand how to protect networks, servers, and systems against cyber-attacks with our Introduction To System And Network Security Course – Join now!
What Do You Do If Someone Has Stolen Your Identity?
If you suspect Identity Theft, act fast to limit financial damage and secure your personal information.

1) Contact Your Bank and Card Issuers: Report fraud and freeze your accounts as soon as possible.
2) Check Your Credit Reports: Seek unfamiliar accounts or credit activity.
3) File an FTC Identity Theft Report: Submit a report of recovery actions and formal reporting.
4) Report to Local Police: Make a legal document to enhance your case.
5) Freeze Your Credit or Add a Fraud Alert: Cancel new credit lines and warn lenders about theft.
6) Secure Your Child’s Identity: Freeze and check their credit file.
Train employees to spot phishing, impersonation, and other human-based cyber threats with our Social Engineering Training Course – Join now!
Examples of Identity Theft
Several warning signs may indicate that your personal information has been misused. Common examples include the following:
a) Unfamiliar charges on your credit card or bank account for purchases you did not make
b) Calls from debt collectors about loans or accounts you never opened
c) Loan or credit applications being denied despite a strong financial record
d) Bounced cheques or overdrafts without any recent transactions
e) Legal issues, such as an arrest warrant issued in your name
f) Healthcare bills or insurance claim statements for services you never received
g) Utility services being disconnected despite timely payments
h) Difficulty signing into online accounts or receiving unexpected password reset emails
i) Unauthorised hard inquiries appearing on your credit report
j) Receiving new credit cards that you never applied for
Conclusion
While no one is completely immune, understanding identity theft is vital in today’s digital world. Protecting your personal data, monitoring accounts, and using tools like password managers, VPNs, and fraud alerts can greatly reduce your risk. If your identity is ever compromised, act quickly to limit damage and regain control of your financial security. Vigilance remains your strongest defence.
Train to identify, exploit, and fix security gaps using ethical hacking techniques with our Ethical Hacking Professional Course – Join now!
Frequently Asked Questions
How Can I Tell If My Identity Has Been Stolen?

You may notice unexplained activity in your credit card or bank accounts, such as unfamiliar charges or new accounts opened in your name. Other signs include being denied credit, receiving bills for services you didn’t use, or hearing from debt collectors about loans you never took out.
What Are the Early Warning Signs of Identity Theft?

Early indicators include strange credit report entries, hard inquiries you didn’t authorise, and missing mail related to financial accounts. You may also have trouble logging into your online accounts, receiving new credit cards unexpectedly, or seeing errors in your personal information on official documents.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000 online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 19 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Courses including the Social Engineering Training, Cyber Security Awareness Course, and Cyber Security Risk Management Course. These courses cater to different skill levels, providing comprehensive insights into Social Engineering in Cyber Security.
Our IT Security & Data Protection Blogs cover a range of topics related to Cyber Security Training, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your IT Security & Data Protection skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.
Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Social Engineering Training
Social Engineering Training
Fri 29th May 2026
Fri 24th Jul 2026
Fri 6th Nov 2026







 Top Rated Course
Top Rated Course



 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


