We may not have the course you’re looking for. If you enquire or give us a call on 01344203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Keeping quiet isn’t always a bad thing. In fact, in the professional world, it can be a sign of trust, respect, and responsibility. Confidentiality is the silent shield guarding personal, financial, and business details. Whether it’s in schools, hospitals, or corporate offices, protecting sensitive information is the key to trust, ethics, and professionalism.
From guarding client data to protecting internal communications learning What is Confidentiality can be a core principle that every employee and employer should live by. In this blog, we break down why it’s vital, and how to practice it in the workplace with real-world examples. If you handle sensitive data or trust someone else with yours, this is must-read.
Table of Contents
1) What is Confidentiality?
2) Importance of Confidentiality
3) Types of Confidentiality
4) Confidential Information in the Workplace
5) How Do You Maintain Confidentiality in Your Work?
6) Skills of Confidentiality
7) Examples of Confidentiality
8) Conclusion
What is Confidentiality?
Confidentiality is the ethical and legal duty to protect sensitive, private, or personal information from being disclosed to unauthorised individuals. It ensures that data shared in trust, whether in healthcare, education, business, or law is handled with care, respect, and security. It is a fundamental principle that supports professionalism, integrity, and responsible information management across industries.
Key Areas:
1) In Healthcare: confidentiality protects a patient’s medical history and treatment
2) In Business: Involves safeguarding trade secrets, employee data, and strategic plans
3) In Education: Ensures students’ academic and personal records are not shared
Importance of Confidentiality
Confidentiality is vital because it builds trust, supports legal compliance, and protects individuals and organisations from data breaches, identity theft, or reputational damage. Here are some key areas where protecting confidentiality is essential:
Health and Social Care
In healthcare, confidentiality is the backbone of trust. Patients must feel confident sharing private information, knowing it will stay between them and their care providers. A breach can led to legal action, loss of trust, or even patient harm.
Example: A nurse discussing a patient’s condition in a public space violates confidentiality.
Patient-doctor
Doctor-patient confidentiality is legally protected in many countries. Doctors are ethically and legally bound to protect patient details, medical histories, diagnoses, and treatment plans. These are done unless the patient consents or it’s legally required to disclose.
Example: A doctor revealing someone’s medical history without permission could lose their license.
Educational Institutions
Teachers and school staff often handle sensitive information about students, such as academic performance, behavioural issues, or family background. Maintaining confidentiality ensures students' dignity and protects them from stigma or discrimination.
Example: Sharing a student’s learning difficulty with others without need or consent breaches trust.
Types of Confidentiality
Confidentiality comes in various forms depending on the nature of the information being handled. Each type plays a vital role in protecting data and maintaining trust within organisations and professional relationships. Below are the key types of confidentiality:

Organisational Data
These data Involves internal information critical to company operations. Key areas:
1) Business strategies and future
2) Financial statements and forecasts
3) Internal communications and performance reports
4) Prevents data leaks that can harm competitive advantage
5) Maintains company reputation and stakeholder trust
Learn and build bulletproof systems with our Fundamentals of Test Automation today!
Administrative Information
This information refers to daily operational and procedural documents. Key features:
1) Meeting minutes information
2) Staff schedules and duty times
3) Internal memos and policy drafts
4) Supports internal order and decision-making
5) Prevents exposure of sensitive operations or planning
Employee and Staff Information
This sensitive information is managed by HR and includes personal and employment details. Key features:
1) Salaries, bonuses, and appraisals
2) Performance records and disciplinary actions
3) Medical or family-related leaves
4) Ensures employee privacy and dignity
5) Complies with employment laws and data protection regulations
Customer and Client Confidentiality
It covers all personal and transactional data of customers or clients. Key areas:
1) Contact details and identification numbers
2) Purchase history and payment information
3) Personal preferences or feedback
4) Builds consumer trust and loyalty
5) Avoids legal risks under data privacy laws like GDPR
Professional and Business Information
This information Handled by service professionals like lawyers, accountants, consultants. Key areas:
1) Legal documents and contracts
2) Business reports and analysis
3) Client strategies or intellectual property
4) Upholds ethical standards and professional credibility
5) Prevents legal breaches and protects client relationships
Be the bug hunter every company dreams of hiring with our Kali Linux Fundamentals Training.
Confidential Information in the Workplace
Protecting this information is not just about policy compliance. It’s essential for building trust, avoiding legal issues, and maintaining a competitive edge. Two of the most critical areas in workplace confidentiality include:
1) Protecting Personal and Sensitive Data
This involves securing employee and client information to protect confidentiality.
Information Include:
a) Names, addresses, contact numbers
b) Identification numbers like national ID, tax ID
c) Medical records, personal leave details, or emergency contacts
d) Financial information such as salary, bank details, or benefits
How to Protect it:
a) Use password-protected systems and encrypted databases
b) Limit access only to authorised personnel
c) Shred physical documents containing sensitive information
d) Train employees on data handling and privacy practices
Why it Matters:
a) Protects individuals’ privacy rights
b) Ensures compliance with data protection laws like GDPR or HIPAA
c) Reduces the risk of identity theft or internal misuse
2) Safeguarding Company Trade Secrets
These secrets refer to protecting proprietary or confidential business information.
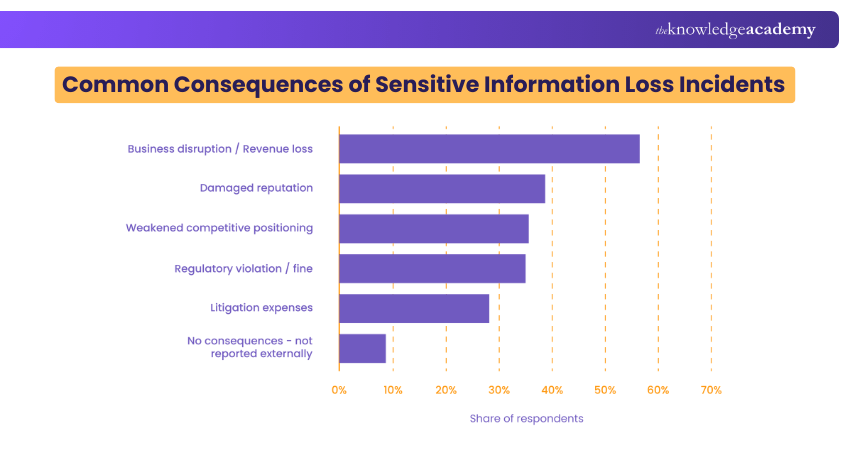
Source: Statista
Type of Information:
a) Product formulas, algorithms, or designs
b) Marketing strategies, business plans, or launch dates
c) Customer lists, pricing structures, or vendor agreements
How to Safeguard Them:
a) Implement Non-disclosure Agreements (NDAs) for employees and contractors
b) Restrict file access using role-based permissions
c) Conduct regular audits of confidential data
d) Monitor digital activities for unauthorised file sharing
Why it Matters:
a) Maintains competitive advantage in the market
b) Prevents corporate espionage or information leaks
c) Protects innovation, revenue streams, and business integrity
Code, crack, conquer with our Cyber Security Awareness. Automate your way into cybersecurity greatness!
How Do You Maintain Confidentiality in Your Work?
Maintaining confidentiality involves consistent practices and awareness. These steps help uphold trust, comply with legal standards, and protect valuable information. Here are the some of the most possible ways:
1) Know What’s Confidential: Understand which data must be protected like employee info, client records, trade secrets and others.
2) Follow Policies and Laws: Adhere to NDAs, company rules, and regulations like GDPR or HIPAA.
3) Limit Access: Share sensitive data only with authorised individuals.
4) Secure Data: Use passwords, encryption, and locked storage for both digital and physical files.
5) Be Discreet: Avoid public or casual discussions of confidential matters.
6) Use Secure Tools: Rely on trusted, encrypted communication platforms.
7) Stay Trained: Regularly update your knowledge through compliance and privacy training.
8) Report Breaches: Notify the appropriate authority immediately if a breach occurs.
Skills of Confidentiality
To handle sensitive information responsibly, professionals must develop and demonstrate specific skills that support confidentiality. These skills ensure information is managed securely, ethically, and effectively in any work environment.
Professionalism
1) It involves upholding ethical standards, respecting privacy, and being trustworthy
2) Professionals should avoid gossip, manage conflicts of interest
3) Handles confidential data with integrity regardless of personal opinions
Example: A manager keeping employee health concerns private, even under pressure.
Discretion
1) The ability to judge what information can be shared and with whom
2) Requires awareness of context and sensitivity
3) Handling private conversations or documents
Example: Not discussing a client’s case in public spaces or casual chats.
Computer Literacy
1) Knowing how to use digital tools safely to store, access, and transmit data
2) Includes using strong passwords, understanding cybersecurity basics
3) This involves navigating software with secure settings
Example: Encrypting emails or documents that contain sensitive information.
Attention to Detail
1) Attention to small mistakes that can lead to big breaches
2) This skill helps ensure no sensitive data is accidentally shared or exposed
3) Involves double-checking recipients, reviewing access permissions
4) It helps the team in verifying file security
Example: Ensuring a confidential file is sent to the right recipient, not copied to the entire team.
Turn keystrokes into cyber shields by learning from Fraud Analytics Training today. Register now!
Examples of Confidentiality
Here are real-world examples that highlight how confidentiality is maintained in different professional contexts:
Finance Data Security
Financial institutions like banks, accounting firms, and investment companies handle extremely sensitive data such as:
1) Bank account details
2) Credit scores
3) Investment portfolios
4) Tax records
Why it Matters:
Any breach can lead to identity theft, fraud, or significant financial loss for clients.
Example:
An accountant ensures a client’s tax return documents are password-protected and shared only through secure channels. Discussing client finances in open office areas or with unauthorised staff is strictly avoided.
HR Confidentiality Practices
Human Resources departments manage:
1) Employee personal details
2) Medical leave records
3) Salary and bonus data
4) Disciplinary actions and internal complaints
Why it Matters:
Mishandling such information can result in lawsuits, employee distrust, and reputational harm to the organisation.
Example:
An HR manager keeps performance reviews and grievance reports confidential, discussing them only with relevant leadership and never over informal conversations or unsecured platforms.
Therapist-client Confidentiality
Therapists, counsellors, and psychologists are legally and ethically bound to maintain complete confidentiality over:
1) Client history
2) Session notes
3) Diagnoses and treatment plans
Why it Matters:
Breaching confidentiality can severely harm a client’s emotional well-being and may lead to legal consequences for the practitioner.
Example:
A therapist does not share session details with family members or colleagues unless the client gives written consent or there’s a legal requirement like risk of harm.
Conclusion
This blog concludes that confidentiality is a fundamental principle that protects personal, professional, and organisational information across various industries. By understanding What is Confidentiality, the types, importance, and practices, individuals and organisations can create safer, more respectful environments. With the right skills like professionalism, discretion, and attention to detail, confidentiality becomes a natural part of everyday work.
Master pen testing with precision! Join our Malware Analysis Training today for better results.
Frequently Asked Questions
What is a Confidentiality Policy?

A confidentiality policy is a set of rules that explain how sensitive information should be handled in a workplace. It tells employees what data must be kept private, how to protect it, and what happens if it's shared without permission. It helps keep trust and legal compliance.
What is a Breach of Confidentiality?

A breach of confidentiality happens when private or sensitive information is shared with someone who shouldn’t have access to it. This can be accidental or intentional and may lead to legal issues, loss of trust, or damage to a person or company’s reputation.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 19 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Automation & Penetration Testing Courses, including the Fundamentals of Test Automation, Tools and Techniques for Penetrating Testing and the Kali Linux Fundamentals. These courses cater to different skill levels, providing comprehensive insights into Multi-Factor Authentication (MFA).
Our IT Security & Data Protection Blogs cover a range of topics related to Security, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Data Protection skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Tools and Techniques for Penetrating Testing
Tools and Techniques for Penetrating Testing
Thu 6th Aug 2026
Thu 29th Oct 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


