We may not have the course you’re looking for. If you enquire or give us a call on 01344203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.
Every time you log into an app or website, there is a silent guard making sure only the right people get in. That guard is authentication. But not all guards work in the same way. Two of the most widely used methods are Session Authentication and Token Authentication. One keeps the user’s details safe on the server, while the other gives the user a token to carry with every request.
This blog explores how Session vs Token Authentication differ, the strengths each brings, and when to use them. By the end, you will have a clear view of which option aligns with your application’s needs. Let’s get started!
Table of Contents
1) What is Session Authentication?
a) How Does Session-based Authentication Work?
b) Advantages of Session Authentication
c) Disadvantages of Session Authentication
2) What is Token Authentication?
3) Differences Between Session vs Token Authentication
4) Conclusion
What is Session Authentication?
Session Authentication is a method where the server creates and stores a record of a user’s activity after they log in. This record usually contains details like a unique session ID, login time, and expiry information. The session ID is then sent to the user’s browser as a cookie. Each time the user makes a request, the cookie is returned to the server, allowing it to recognise the session and validate the user’s actions.
How Does Session-based Authentication Work?
Here’s how session-based authentication works:
1) User request is sent to the server containing their credentials and the data they want to access.
2) The server verifies the credentials, creates a session, stores relevant details in a database, and sends back a sessionId.
3) This sessionId is saved in the user's browser cookies.
4) On subsequent requests, the browser automatically includes the cookie in the HTTP header.
5) The server checks the sessionId, and if it's valid, it authenticates the user and delivers the requested data.
Here’s an example of session-based authentication request:

Advantages of Session Authentication
Here are the key benefits of Session Authentication:
1) Simplicity and Ease of Use: Session Authentication is easy to implement, especially in traditional web applications. Browsers natively support cookies, so there’s no need for complex token handling on the client side.
2) Centralised Session Management: All session data is stored on the server, allowing you to manage, revoke or expire sessions centrally. This gives more control over user access and activity.
3) Small Client-side Footprint: Cookies typically store only a session ID, keeping the client-side data minimal. This reduces exposure and storage demands on the user’s browser.
4) Secure by Default (if Configured Properly): With the HTTP-only and Secure cookie flags, session cookies can be protected from JavaScript access and man-in-the-middle attacks, thereby adding an extra layer of security.
5) Compatible with Traditional Web Architectures: Session Authentication works seamlessly with multi-page applications and server-rendered sites, where the server handles each request.
Disadvantages of Session Authentication
Here are some key drawbacks of Session Authentication that you should keep in mind:
1) Scalability Issues: Since session data is stored on the server, managing many users can strain server memory and hinder scalability. This contrasts with Token Authentication, which handles scaling more efficiently.
2) Challenges with Multiple Domains: Cookies are typically associated with a specific domain or subdomain. This makes it difficult to use them when sending API requests across multiple domains.
3) Security Concerns: Cookies are more prone to Cross-site Request Forgery (CSRF) attacks. It’s essential to implement proper security measures on the server to mitigate this risk.
4) Less Suitable for Modern Architectures: As applications increasingly decouple their front-end and back-end, traditional Session Authentication becomes less ideal.
What is Token Authentication?
Token Authentication is a method where the server issues a digitally signed token to a user after successful login. This token contains encoded information, such as the user’s identity and expiry time, and is stored on the client side (often in local storage). For every new request, the client sends the token, and the server verifies its signature before granting access.
How Does Token-based Authentication Work?
Here’s how token-based authentication works:
1) The client sends a request to the server along with their login credentials.
2) If the credentials are found valid, the server creates a secure, signed token.
3) This token is returned to the client and stored locally (for example, in local storage).
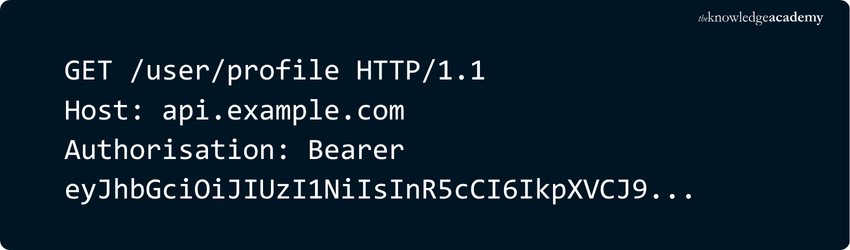
4) For future requests, the client includes the token in the HTTP header.
5) The Server verifies the token. If it is valid, access is granted and a response is sent.
6) The token is discarded or invalidated when the user logs out.
Here’s an example of a token-based authentication request:
Advantages of Token Authentication
Token Authentication takes care of many of the limitations of cookie-based methods and adds greater flexibility and performance benefits. Let's explore some of them:
1) Mobile-friendly: Unlike cookies, tokens integrate smoothly with iOS, Android and IoT environments where cookie storage isn't available. This makes tokens ideal for modern app ecosystems.
2) Faster and More Efficient: With cookie-based sessions, the server must perform a database lookup on every request. Tokens can be quickly decoded without querying a database. They can also carry user roles and permissions which reduces the need for additional server-side checks.
3) Highly Scalable and Stateless: Token authentication is stateless, meaning the server doesn't store the token. Every necessary information is self-contained within the token. This makes it much easier to scale your application.
4) Cross-domain Compatibility: While cookies are restricted to a single domain or subdomain, tokens can be used across multiple domains. This is especially helpful in single-page applications or Microservice architectures that make calls to various APIs across different domains.
Become a Microsoft identity pro and fortify your enterprise. Sign up for our Microsoft Identity and Access Administrator SC300 Course now!
Disadvantages of Token Authentication
Here are some drawbacks of Token Authentication you must consider:
1) Tokens can be Stolen: Tokens are typically stored in the browser which JavaScript can access. This makes them easier for hackers to steal using XSS attacks. Also, if stolen, the server can’t easily block them because it doesn’t track token sessions.
2) Tokens are Larger in Size: JWT tokens carry additional data such as user roles and permissions. This makes them larger than simple session IDs. This increases the size of every request, which can slow down the process.
3) Harder to log out or Expire: Since tokens don’t rely on server-side sessions, logging out doesn’t instantly make a token useless. It stays active until it expires.
4) More Work to Set Up: With cookies, the browser handles sending them automatically. Tokens need to be added manually to each request which adds more work for Developers, especially in big apps with many API calls.
5) Difficult Across Devices: Managing tokens across different devices (like phone and laptop) is tricky. You need extra tools or code to track and block tokens for each device if needed.
Ready to scale your Developer skills and build scalable apps? Sign up for our App & Web Development Training now!
Differences Between Session vs Token Authentication
Here are the key distinctions between Session Authentication vs Token Authentication:

Conclusion
Understanding the difference between Session vs Token Authentication is vital for creating secure and efficient applications. Session-based methods suit traditional web apps, while token-based authentication provides scalability, flexibility, and cross-domain support for modern systems. By recognising their strengths and limitations, you can choose the method that aligns with your project’s needs, ensuring both robust security and a smooth user experience.
Master the art of User Experience and craft designs that delights. Register for our comprehensive UX Design Course now!
Frequently Asked Questions
Is Session ID the Same as Token?

No, a Session ID and a Token are not the same. A Session ID is server-generated and stored on the server, while a Token (like a JWT) is client-stored, carries encoded user data and enables stateless authentication.
What is Better Than Token Authentication?

No, a Session ID and a Token are not the same. A Session ID is server-generated and stored on the server, while a Token (like a JWT) is client-stored, carries encoded user data and enables stateless authentication.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000 online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 19 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various App & Web Development Courses, including the Node.JS Course, UI UX Design Course and the UX Design Training. These courses cater to different skill levels, providing comprehensive insights into What is JSON.
Our Programming & DevOps Blogs cover a range of topics related to Session and Token Authentication, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your authentication knowledge, The Knowledge Academy's diverse courses and informative blogs have got you covered.

Richard Harris is a highly experienced full-stack developer with deep expertise in both frontend and backend technologies. Over his 12-year career, he has built scalable web applications for startups, enterprises and government organisations. Richard’s writing combines technical depth with clear explanations, ideal for developers looking to grow in modern frameworks and tools.

Upcoming Programming & DevOps Resources Batches & Dates
Date
 Node.JS Course
Node.JS Course





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


