We may not have the course you’re looking for. If you enquire or give us a call on 01344203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.
Every time you log in to an app, store files online, or share data across systems, there is a security framework quietly working in the background. As systems grow complex, gaps can appear if security is not planned properly. That is where Cloud Security Architecture becomes important, helping organisations protect sensitive data while keeping services fast and flexible.
Whether you are new to cyber security or managing modern cloud systems, this blog will enable you to design and implement a strong architecture. In this blog, you will learn about Cloud Security Architecture, its key phases, components, and more!
Table of Contents
1) What is Cyber Security Architecture?
2) The 3 Phases of Cyber Security Architecture
3) Key Components of Cyber Security Architecture
4) Designing a Robust Cyber Security Architecture
5) Challenges and Best Practice
6) Conclusion
What is Cyber Security Architecture?
Cyber Security Architecture is a structured framework that organisations design to protect their IT systems, digital assets, and sensitive data from cyber threats. It defines how security tools, technologies, and controls are arranged across networks, applications, and data to prevent attacks and reduce risk.
Cyber Security Architecture brings together policies, principles, models, and industry standards to create a layered approach to defence. Each security layer is designed to address different kinds of threats, ensuring that if one control fails, others remain in place to provide protection from cyber threats.
The 3 Phases of Cyber Security Architecture
Let’s look at the three phases of Cyber Security Architecture in detail below:
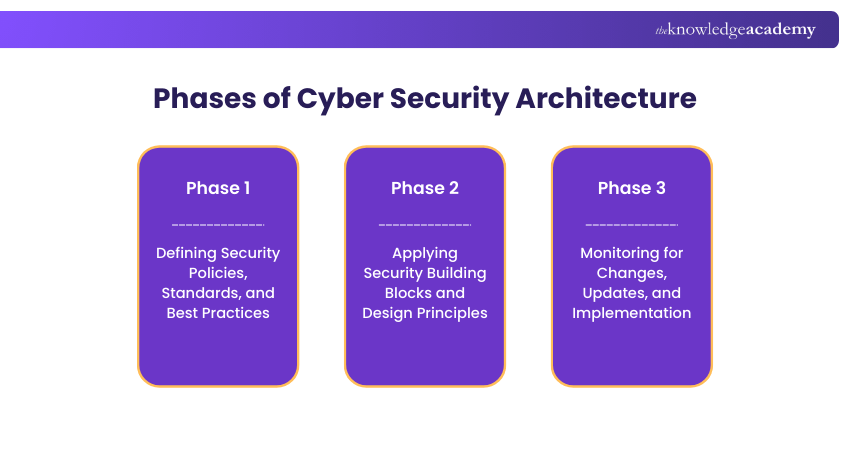
Phase 1: Developing an Organisation’s Policies, Standards, and Best Practices According to Cyber Security Architecture Frameworks
In this phase, focus on defining how security should work across the organisation. Security architects create policies, standards, and best practices based on recognised cybersecurity frameworks. These frameworks explain what must be safeguarded but leave room for organisations to decide how strong the controls should be.
Some common frameworks include ISO 27001 and the Open Web Application Security Project (OWASP). After implementation, organisations can pursue certification to prove their security maturity. Also, regular staff training is essential to maintain compliance and protect the trust of customers.
Phase 2: Using the Building Blocks of Security and Applying Design Concepts
Once policies and standards are set, development teams begin applying them during system design and development. Here follows the principle of security, where security controls are built into software from the start with each component designed to handle specific security needs.
For example, rules for authentication and access control are defined by security architects and implemented by developers. These secure building blocks are reused across systems, reducing risk and improving consistency.
Phase 3: Monitoring for Changes, Updates, and Implementation
The final phase focuses on continuous monitoring, review, and improvement. Security architects regularly assess systems to ensure policies and standards are being followed correctly. They track exceptions, review incidents, and identify gaps that may introduce vulnerabilities.
As technologies and threats evolve, standards and controls must be updated to stay effective. This oversight ensures that earlier phases remain aligned with real-world risks, helping organisations maintain compliance, resilience, and long-term security.
Learn to identify threats proactively with Cyber Security Awareness Training now!
Key Components of Cyber Security Architecture
To build a resilient Cyber Security Architecture, organisations need multiple security components working together. Let’s look at the key components below.
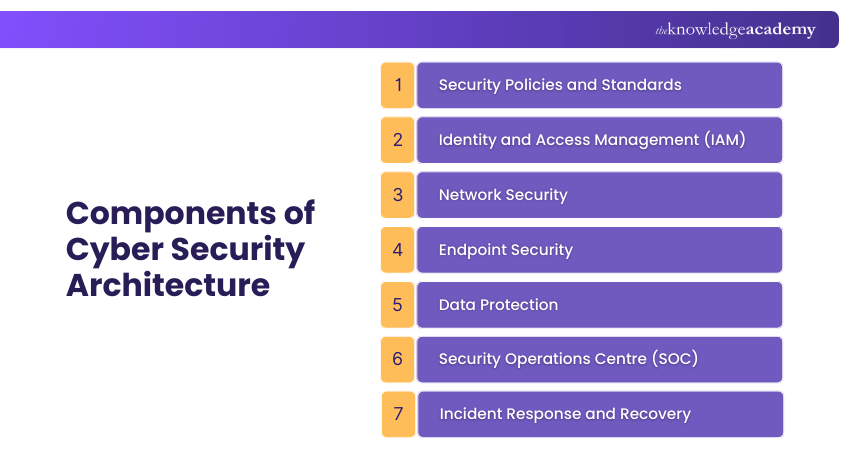
1) Security Policies and Standards
Security Policies and Standards build the foundation of cybersecurity architecture. They define rules for system access, data handling, password management, and incident response. These policies are aligned with recognised frameworks such as ISO/IEC 27001.
2) Identity and Access Management (IAM)
Identity and Access Management ensures that only authorised users can access systems. It follows the principle of least privilege to reduce misuse and insider threats. IAM includes controls such as multi-factor authentication, single sign-on, and privileged access management to detect unusual user behaviour.
3) Network Security
Network security protects an organisation’s infrastructure from unauthorised access and cyberattacks. It controls traffic flow and blocks threats before they reach critical systems. Common measures include firewalls, intrusion detection and prevention systems, and network segmentation to isolate sensitive assets.
4) Endpoint Security
Endpoint Security protects devices such as laptops, mobile phones, servers, and Internet of Things (IoT) devices. As remote work increases, endpoints have become common attack targets. Thus, modern endpoint solutions provide malware protection, automated threat detection, and endpoint detection to reduce risk.
5) Data Protection
Data Protection protects sensitive information throughout its lifecycle. It ensures data remains secure when it is stored, shared, or transmitted. Techniques such as encryption, data loss prevention, and integrity monitoring help prevent data leaks and unauthorised access.
6) Security Operations Centre (SOC)
A Security Operations Centre is a core team responsible for monitoring, detecting, and responding to security incidents. It operates continuously to identify threats proactively. SOC teams use various tools to analyse alerts, investigate incidents, and support faster response.
7) Incident Response and Recovery
Incident Response and Recovery minimise damage during and after a security incident. It includes clear response procedures, disaster recovery planning, and business continuity strategies. An effective response ensures systems are restored quickly with minimal reputational impact.
Learn risk assessment and decision-making for safer organisations with Cyber Security Risk Management Course now!
Designing a Robust Cyber Security Architecture
Designing a robust Cyber Security Architecture requires a structured approach that balances security requirements with business priorities. A strong architecture not only protects critical assets but also supports operational efficiency and long-term growth. Let’s explore the key steps involved in building an effective framework.
1) Risk Assessment and Management
Risk Assessment helps organisations to understand which assets are most valuable and vulnerable. It identifies potential threats and their impact, allowing teams to prioritise security efforts. Focusing on high-risk areas helps organisations allocate resources effectively.
2) Threat Modeling
Threat Modeling examines how attackers target systems and exploits weaknesses. It helps security teams identify attack paths, such as threat actors, and deliver possible outcomes. This insight allows organisations to design targeted controls that prevent high-impact attacks.
3) Secure Design Principles
Secure Design Principles ensure security is built into systems from the start. Practices, such as least privilege, limit user access to only what is necessary to reduce misuse. Also, fail-safe defaults protect systems by blocking access when security criteria are not met.
4) Integration with Business Goals
Integrating cybersecurity with business goals ensures security support. When aligned, security controls improve efficiency, trust, and continuity. This approach helps organisations protect assets while enabling seamless workflows and positive user experiences.
Challenges and Best Practices
Developing a Cyber Security Architecture comes with its own set of challenges. Applying the right practices helps organisations to create an effective one. Let’s look at them below.
1) Address Security Gaps: Security gaps result from outdated systems or misconfigurations. Regular risk assessments, vulnerability scans, and penetration testing help identify weak points early, leading to improved controls for risk reduction.
2) Balance Security and Usability: Overly complex controls can disrupt productivity. Using user-friendly solutions, such as single sign-on, helps maintain security without slowing down work.
3) Keep up with Emerging Threats: Cyber threats are constantly changing, making it essential to stay informed. Regularly updating threat models ensures defences remain effective against new and evolving risks.
4) Conduct Regular Audits and Compliance: Audits help organisations verify that security controls meet regulatory and internal requirements. They also highlight improvement areas and regular reviews maintain trust and accountability.
5) Train and Increase Employee Awareness: Human error is one of the biggest risk factors. Continuous training helps employees recognise threats, such as phishing, to strengthen the organisation’s defence.
Conclusion
Cyber Security Architecture is a core part of building trust and resilience in a digital world. From defining policies and designing secure systems to monitoring threats and training people, every layer is crucial for protecting organisations against cyber threats. A strong architecture helps organisations to protect data, support business continuity, and adapt confidently to threats.
Build effective cyber defence skills with Cyber Security Training – Join now!
Frequently Asked Questions
What are the Layers of Cyber Security Architecture?

The layers of Cyber Security Architecture include:
1) Mission-critical Assets
2) Data Security
3) Application Security
4) Endpoint Security
5) Network Security
6) Perimeter Security
7) Human Layer
What are Some Common Cyber Security Architectures?

Some common Cyber Security Architectures include:
1) Zero Trust Architecture
2) Defence in Depth
3) Secure Access Service Edge
4) Cybersecurity Mesh Architecture
5) Perimeter Security Architecture
6) Cloud Security Architecture
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Courses, including the Certified Cyber Security Professional (CCS-PRO) Course, Cyber Security Awareness Training, and Introduction to System and Network Security Course. These courses cater to different skill levels, providing comprehensive insights into What is Cyberbullying.
Our IT Security & Data Protection Blogs cover a range of topics related to Cyber Security, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Cyber Security and Defence skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Certified Cyber Security Professional (CCS-PRO)
Certified Cyber Security Professional (CCS-PRO)
Fri 24th Jul 2026
Fri 9th Oct 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


