We may not have the course you’re looking for. If you enquire or give us a call on 01344203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Ever wondered who makes sure your files reach the right device on your Local Area Network (LAN)? In a world full of machines and technology, it can be tricky to figure out which device is using a specific Internet Protocol (IP) address. That’s where the Address Resolution Protocol (ARP) comes in!
Address Resolution Protocol is a technique used to find the MAC address of reliable IP addresses of devices. Without ARP, your system wouldn't know how to deliver data packets to the right place on a local network. Let’s explore what ARP is, how it works, why it matters, and the common types!
Table of Contents
1) What is Address Resolution Protocol (ARP)?
2) How Does Address Resolution Protocol Work?
3.) The Purpose of ARP
4) What are the Types of ARP?
5) What is ARP Spoofing/ARP Poisoning Attack?
6) Dangers of ARP Spoofing
7) Advantages of Using ARP
8) Disadvantages of Using ARP
9) Best Practices for ARP Attack Prevention
10) Conclusion
What is Address Resolution Protocol (ARP)?
Address Resolution Protocol (ARP) is a networking protocol that converts logical IP Addresses from the Network Layer into physical Media Access Control (MAC) addresses at the Data Link Layer within a Local Area Network (LAN). This translation allows devices on the same network to communicate directly by identifying the correct hardware address linked to a known IP address.
ARP works by sending broadcast requests to locate the target device and then storing the discovered IP-to-MAC mapping in a cache for faster future communication. By acting as a bridge between IP-based networking and Ethernet communication, ARP plays a vital role in delivering data accurately between devices on the same network segment.
How Does Address Resolution Protocol Work?
ARP enables devices on a local network to find the correct MAC address linked to an IP address. This process ensures data is delivered to the right device quickly and accurately.

ARP works through the following steps:
1) A host wants to communicate with another device and knows its IP address but does not know the MAC address.
2) The host first checks its ARP cache to see if the IP-to-MAC mapping already exists.
3) If no entry is found, the host sends an ARP request broadcast across the local network asking who owns the target IP address.
4) The device with the matching IP address responds by sending back its MAC address.
5) The host saves this IP-to-MAC mapping in its ARP cache for future use.
Once the MAC address is identified, data packets are sent directly to the correct device through the network, ensuring smooth and efficient communication within the LAN.
The Purpose of ARP
In the early days of computer networking, IP addresses and MAC addresses operated at different layers of the OSI model. IP addresses were used at the Network layer to route data between networks, while MAC addresses functioned at the Data Link layer to deliver data within the same network segment.
To bridge this gap, ARP was introduced to map IP addresses to their corresponding MAC addresses. This allows devices on the same local network to identify each other correctly and communicate smoothly across layers, making reliable data exchange within a network possible.
What are the Types of ARP?
ARP extends beyond its basic IP-to-MAC lookup. Here are several types that you might encounter:
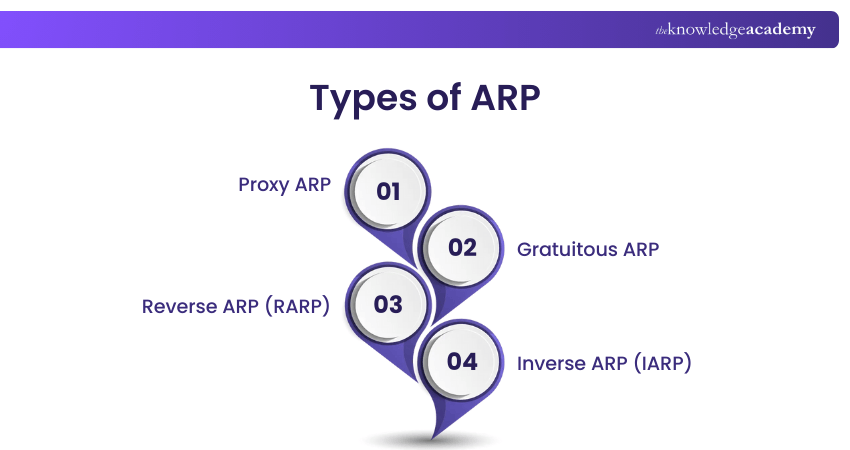
1) Proxy ARP
Proxy ARP occurs when a router responds to an ARP request on behalf of another device, usually on a different subnet. This enables communication across network segments but may cause security or traffic issues if misused.
2) Gratuitous ARP
Gratuitous ARP is an unsolicited ARP message sent by a device to announce its own IP and MAC address to the network. It helps update ARP tables, detect IP address conflicts, and inform other devices about changes in hardware addresses.
3) Reverse ARP (RARP)
Reverse ARP (RARP) enables a device to discover its own IP address when it only knows its MAC address. This method was mainly used by diskless systems in the past and is now considered obsolete, having been replaced by Dynamic Host Configuration Protocol (DHCP).
4) Inverse ARP (IARP)
Inverse ARP (IARP) is used in networks such as Frame Relay and ATM to identify the IP address linked to a known virtual circuit or hardware address. It supports dynamic address discovery in specialised networking environments.
Step into the future of networking by registering for our IPv6 Basics Course now!
What is ARP Spoofing/ARP Poisoning Attack?
ARP spoofing, also called ARP poisoning or ARP poison routing, is a type of cyberattack where a Hacker sends fake ARP messages to trick devices on a LAN. These messages trick devices into linking the MAC address of attackers with a trusted device’s IP address, like a server. This allows the attacker to access and perform the actions they require.
Once the attacker successfully positions themselves between communicating devices, they can intercept, modify, or block data without being detected. This type of attack is often used as a stepping stone for more serious threats such as data theft, session hijacking, or denial of service attacks. Because ARP operates without authentication, ARP spoofing can be difficult to detect unless proper network security controls are in place.
Dangers of ARP Spoofing
It can often lead to redirected traffic, stolen sessions, or take down entire systems. The other kinds of cyberattacks include the following:
1) Man-in-the-Middle (MITM) Attacks
In this attack, a Hacker secretly places themselves between two devices that are talking to each other, like your computer and a website. The Hacker tricks them into thinking they are talking directly, but everything goes through the Hacker first.
This lets them read or change messages without you knowing. It is often used to steal passwords, credit card numbers, or login details, especially when fake websites are involved.
2) Denial-of-Service Attacks
Here, in the Denial-of-Service (DoS) attacks, the Hackers send a lot of fake ARP messages to confuse devices on a LAN. These devices will fail to send data properly, which can crash systems or make websites and services stop working.
As a result, these can make the systems crash or become unresponsive. It even prevents legitimate users from accessing network services.
3) Session Hijacking
Session hijacking happens when a Hacker steals a user's session identity or the special code that tells a website you’re logged in. By using ARP spoofing, they can grab this code during login and take over your session.
They are capable of pretending to like you, viewing private info, sending messages, or making transactions just like you would without needing your password again.
Advantages of Using ARP
Address Resolution Protocol (ARP) ensures smooth communication within local networks by automatically mapping IP addresses to MAC addresses. This improves efficiency and simplifies network operations in the following ways:
1) Enables Local Communication: Allows devices to communicate by resolving IP addresses into MAC addresses within a network.
2) Automatic Address Resolution: Removes the need for manual IP to MAC configuration through dynamic discovery.
3) Improves Network Efficiency: Stores mappings in an ARP cache to reduce repeated broadcasts and network traffic.
4) Simplifies Troubleshooting: Helps identify connectivity issues by displaying IP to MAC address relationships.
5) Supports Network Growth: Makes it easy to add or remove devices without reconfiguring the network.
6) Enhances Security Monitoring: Helps detect unusual ARP activity, such as spoofing attempts.
7) Supports Advanced Networking: Enables features like Proxy ARP and Gratuitous ARP for flexible network communication.
Would you like to defend against real-world threats? Sign up for our Cisco IOS Network Security Training today!
Disadvantages of Using ARP
Although Address Resolution Protocol (ARP) is widely used in local networks, it has certain limitations. Its simple design and limited security can impact performance and safety in the following ways:
1) Security Risks: ARP is vulnerable to attacks such as ARP spoofing, where malicious devices can impersonate others and intercept network traffic.
2) Network Congestion: The use of broadcast requests can increase traffic on the network, particularly in large or busy environments.
3) Weak Security Features: ARP lacks strong authentication methods, making it difficult to verify device identities and prevent unauthorised access.
Best Practices for ARP Attack Prevention
ARP attacks, such as ARP spoofing, can disrupt network operations and expose sensitive data. Here are the key practices organisations can follow to secure local network communication.
1) Use Static ARP in Sensitive Zones: Configure fixed IP to MAC mappings for critical systems to prevent spoofed ARP responses.
2) Enable Dynamic ARP Inspection: Validate ARP packets against trusted DHCP or static data to block forged mappings and DoS attempts.
3) Apply Port Security: Limit the number of MAC addresses per switch port to reduce device impersonation risks.
4) Implement Network Segmentation: Divide networks into smaller segments to limit the spread and impact of ARP based attacks.
5) Monitor ARP Traffic: Regularly track ARP activity to detect unusual behaviour and respond to threats early.
6) Use Encryption and VPNs: Protect data in transit with secure tunnels and encryption to minimise the impact of interception attacks.
7) Control Network Access: Restrict physical and wireless access using authentication methods to prevent unauthorised connections.
Conclusion
Address Resolution Protocol is a core part of how local networks operate, ensuring smooth communication between devices. As one of the essential Network Protocols, ARP helps organisations improve performance, reduce attack risks, and maintain reliable, efficient network communication through proper understanding and security practices.
Gain the Skills to Design Robust Enterprise Networks with Designing Cisco Enterprise Networks (ENSLD) Training – Register Now!
Frequently Asked Questions
What are the Key Components of the ARP Protocol Structure?

The ARP protocol structure uses defined packet fields to map IP addresses to MAC addresses within a local network. These include hardware and protocol types, address length fields, an opcode for request or reply, and sender and target IP and MAC details that enable accurate device identification and communication.
Is the ARP Protocol Still Relevant?

Yes, the ARP protocol is still highly relevant, particularly in IPv4 networks. It serves as the essential link between logical IP addresses and physical MAC addresses, enabling local communication. Although IPv6 uses the Neighbor Discovery Protocol instead, ARP continues to support most existing network infrastructures today.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 19 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cisco Training, including the CCNP Training (Cisco Certified Network Professional), CCNP Security Training, and the CCNP Wireless Training. These courses cater to different skill levels, providing comprehensive insights into What is Ethernet.
Our IT Infrastructure & Networking Blogs cover a range of topics related to Address Resolution Protocol, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your IT Infrastructure & Networking skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.
Upcoming IT Infrastructure & Networking Resources Batches & Dates
Date
 CCNP Training (Cisco Certified Network Professional)
CCNP Training (Cisco Certified Network Professional)
Mon 22nd Jun 2026
Mon 26th Oct 2026





 Top Rated Course
Top Rated Course



 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


