 To help and support our clients we are providing a limited number of 250 daily discount codes. Hurry, first come, first served!
To help and support our clients we are providing a limited number of 250 daily discount codes. Hurry, first come, first served!
IT Support and Solution Training FAQs
The prerequisites for IT Support and Solution Courses depend on the specific course and target audience. At The Knowledge Academy, one of the trusted training providers, we offer courses suitable for both beginners and experienced professionals.
In IT support, individuals learn to troubleshoot hardware and software issues, including diagnosing problems, resolving technical issues, and aiding with operating systems.
While degrees in computer science or related fields are beneficial, many roles prioritise certifications and practical skills. At The Knowledge Academy, one of the top training providers, we offer courses that help learners build job-ready IT support skills.
The course covers troubleshooting, network management, hardware and software installation, system maintenance, cybersecurity, customer service skills, and IT solutions for common technical issues.
The duration of the IT Support and Solution Courses varies depending on the course you select. Please visit the course page you wish to pursue to know the exact details of the duration.
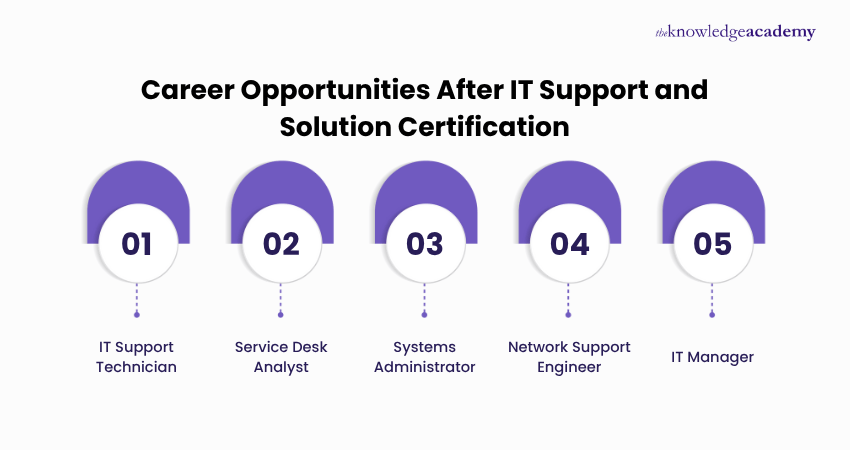
You can pursue roles such as IT Support Specialist, Helpdesk Technician, Technical Support Analyst, Systems Administrator, or IT Solutions Consultant. At The Knowledge Academy, one of the best training providers, we help learners prepare for real-world IT roles.
You can start a career in IT Support by acquiring foundational knowledge, obtaining relevant education or certifications, gaining practical experience, and showcasing customer service skills in your resume for entry-level roles.
Yes, tech support is an excellent starting point, offering hands-on experience and exposure to various technologies. At The Knowledge Academy, one of the trusted training providers, we support learners in building a strong foundation for IT careers.
An IT support person troubleshoots hardware and software issues, assists with technology-related problems, and provides technical support to end-users, ensuring the smooth functioning of IT systems.
Yes, our IT Support and Solution Training include assessments to test your understanding and application of IT support and solutions concepts.
Courses are regularly updated with input from industry experts and incorporate current technologies and real-world case studies. At The Knowledge Academy, one of the global training providers, we ensure our content aligns with evolving IT industry trends.
The Knowledge Academy stands out as a prestigious training provider known for its extensive course offerings, expert instructors, adaptable learning formats, and industry recognition. It's a dependable option for those seeking IT Support and Solution Training.
Please see our IT Support and Solution Training available in Philippines
The Knowledge Academy is one of the Leading global training provider for IT Support and Solution Training.
The training fees for IT Support and Solution Training in Philippines starts from $3995

Why we're the go to training provider for you

Best price in the industry
You won't find better value in the marketplace. If you do find a lower price, we will beat it.

Trusted & Approved
Recognised by leading certification bodies, we deliver training you can trust.

Many delivery methods
Flexible delivery methods are available depending on your learning style.
High quality resources
Resources are included for a comprehensive learning experience.




"Really good course and well organised. Trainer was great with a sense of humour - his experience allowed a free flowing course, structured to help you gain as much information & relevant experience whilst helping prepare you for the exam"
Joshua Davies, Thames Water



Looking for more information on IT Support and Solution Training
 25+ IT Support Interview Questions And Answers
25+ IT Support Interview Questions And Answers IT Support job description: A Complete Guide
IT Support job description: A Complete Guide What is a VPN and How Does It Work? A Comprehensive Guide
What is a VPN and How Does It Work? A Comprehensive Guide What Is Nginx? A Beginner's Guide
What Is Nginx? A Beginner's Guide What is Cloudflare? Everything You Need to Know
What is Cloudflare? Everything You Need to Know Network Protocols: Key Concepts and Types Explained
Network Protocols: Key Concepts and Types Explained Types of Networks: Explained in Detail
Types of Networks: Explained in Detail What is Network Topology: An Essential Guide to Networking
What is Network Topology: An Essential Guide to Networking













 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


