 To help and support our clients we are providing a limited number of 250 daily discount codes. Hurry, first come, first served!
To help and support our clients we are providing a limited number of 250 daily discount codes. Hurry, first come, first served!
Ethical Hacking Training FAQs
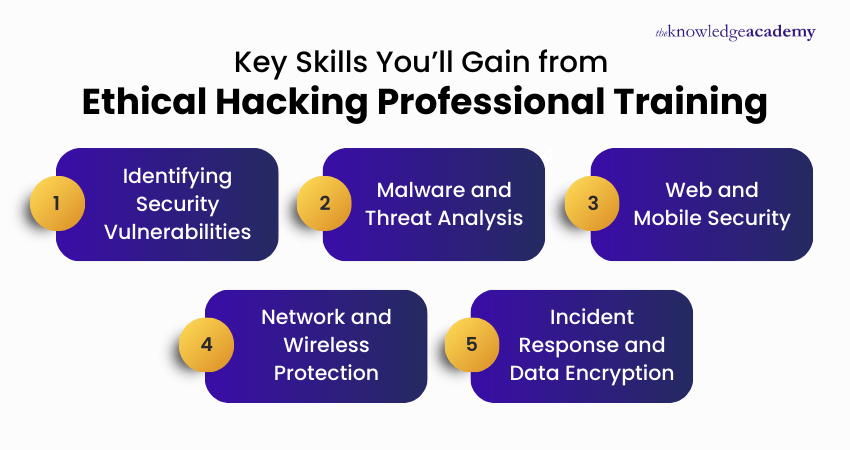
An Ethical Hacking Training Course teaches how to legally identify and fix vulnerabilities in systems and networks. It equips delegates with techniques to strengthen cybersecurity through penetration testing, vulnerability assessments, and ethical hacking practices.
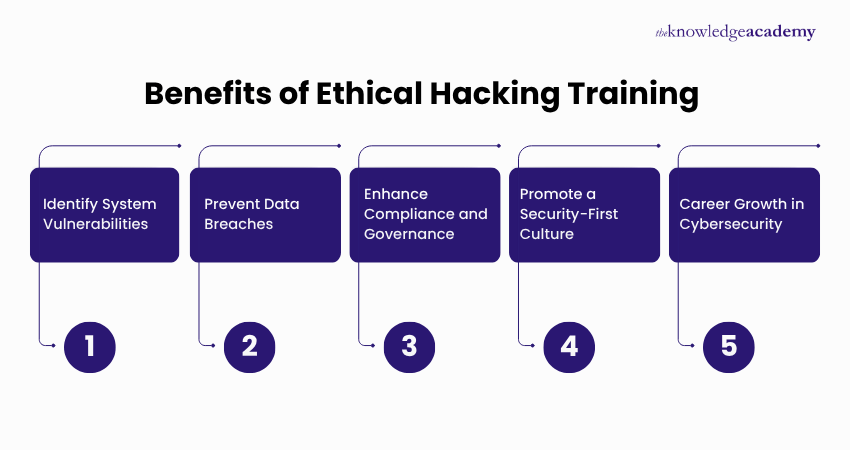
Learning Ethical Hacking helps you protect systems from malicious attacks, opens doors to cybersecurity roles, and equips you with in-demand skills to detect and fix vulnerabilities before real threats occur.
This Ethical Hacking Training benefits IT Professionals, System Administrators, Network Engineers, and Aspiring Cybersecurity Experts. It’s also suitable for anyone responsible for securing digital infrastructure. At The Knowledge Academy, one of the trusted training providers, we support learners across various professional backgrounds.
The duration of these Ethical Hacking Courses varies. Please visit our course pages for specific information.
Yes, The Knowledge Academy offers 24/7 support via phone & email before attending, during, and after the course. Our customer support team is available to assist and promptly resolve any issues you may encounter.
There are no formal prerequisites for Ethical Hacking Training. However, a basic understanding of networking and cybersecurity concepts can be helpful for better comprehension.
Cybersecurity professionals, ethical hackers, IT administrators, and penetration testers should attend. The Ethical Hacking Training is also ideal for those looking to transition into offensive security roles.
No prior programming knowledge is required for this Ethical Hacking Training. However, a basic understanding of scripting or languages like Python can be helpful in advanced Ethical Hacking scenarios.
Languages like Python, Bash, and JavaScript are useful for writing scripts, automating tasks, and understanding vulnerabilities in Ethical Hacking activities.
Yes, beginners can start learning Ethical Hacking with basic computer knowledge and a willingness to learn. At The Knowledge Academy, one of the best training providers, we structure courses to support learners from non-technical backgrounds.
These Ethical Hacking Training Courses train professionals to proactively find and fix vulnerabilities, strengthening an organisation’s defences and preventing potential security breaches.
They simulate real-world cyber-attacks to expose weak points in systems, allowing professionals to implement robust countermeasures and improve system resilience.
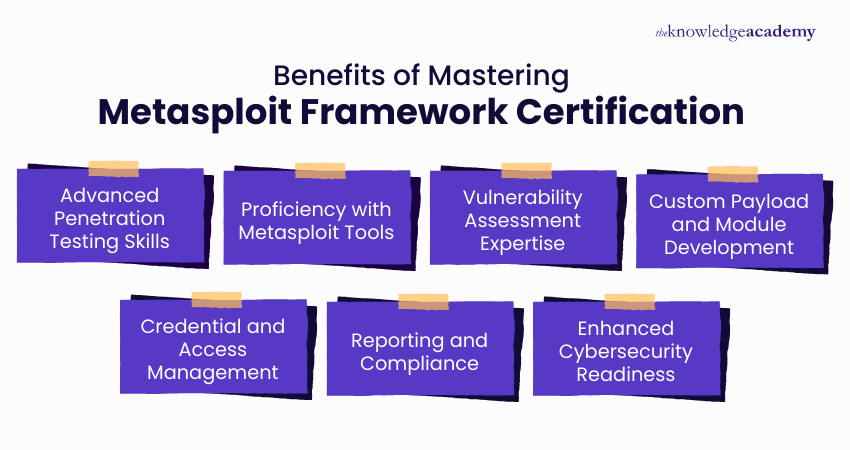
Ethical Hacking focuses on offensive security techniques like penetration testing, while general Cybersecurity Courses cover broader defence strategies, compliance, and risk management.
You can register by visiting The Knowledge Academy website, selecting your preferred course and schedule, and completing the registration through the secure checkout process.
Yes, demand is expected to grow significantly due to rising cyber threats and the need for proactive security measures. At The Knowledge Academy, one of the global training providers, we help learners build skills aligned with future cybersecurity demands.
Career options include Penetration Tester, Security Analyst, Vulnerability Assessor, Red Team Specialist, and Cybersecurity Consultant. At The Knowledge Academy, one of the top training providers, we prepare learners for these in-demand roles.
Yes, industries like finance, healthcare, government, defence, e-commerce, and tech consistently seek ethical hackers to protect sensitive data and infrastructure.
Our Ethical Hacking Training Courses combine real-world labs, expert instruction, and up-to-date content. At The Knowledge Academy, one of the trusted training providers, we ensure practical, hands-on learning aligned with industry standards.
The Knowledge Academy stands out as a prestigious training provider known for its extensive course offerings, expert instructors, adaptable learning formats, and industry recognition. It's a dependable option for those seeking this certification.
Please see our Ethical Hacking Training available in Philippines
The Knowledge Academy is one of the Leading global training provider for Ethical Hacking Training.
The training fees for Ethical Hacking Training in Philippines starts from $3995

Why we're the go to training provider for you

Best price in the industry
You won't find better value in the marketplace. If you do find a lower price, we will beat it.

Trusted & Approved
Recognised by leading certification bodies, we deliver training you can trust.

Many delivery methods
Flexible delivery methods are available depending on your learning style.
High quality resources
Resources are included for a comprehensive learning experience.




"Really good course and well organised. Trainer was great with a sense of humour - his experience allowed a free flowing course, structured to help you gain as much information & relevant experience whilst helping prepare you for the exam"
Joshua Davies, Thames Water



Looking for more information on Ethical Hacking Training
 Top 20 Ethical Hacker Interview Questions and Answers
Top 20 Ethical Hacker Interview Questions and Answers Ethical Hacker Roles and Responsibilities: A Complete Career Guide
Ethical Hacker Roles and Responsibilities: A Complete Career Guide Types of Ethical Hacking in Cyber Security: All You Need to Know
Types of Ethical Hacking in Cyber Security: All You Need to Know 10+ Ethical Hacking Tools
10+ Ethical Hacking Tools Top 10 Skills of Ethical Hacker
Top 10 Skills of Ethical Hacker Difference Between Hacking and Ethical Hacking: A Brief Overview
Difference Between Hacking and Ethical Hacking: A Brief Overview What is a Trojan Horse? Types, Detection & Prevention
What is a Trojan Horse? Types, Detection & Prevention Ethical Hacking vs Penetration Testing: What’s the Difference?
Ethical Hacking vs Penetration Testing: What’s the Difference?













 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


