We may not have the course you’re looking for. If you enquire or give us a call on +44 1344 203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Have you ever wondered how companies keep their data safe from hackers? The answer often lies in something called Ethical Hacking. But What is Ethical Hacking, and why does it matter? It’s a legal way to test systems for security issues before real hackers find them. In this blog, we will discuss what Ethical Hacking means, how it works, and why it’s so important in a digital world. Let’s get started!
Table of Contents
1) What is Ethical Hacking?
2) Benefits of Ethical Hacking
3) Types of Ethical Hacking
4) Types of Hacking/Hackers
5) Phases of Ethical Hacking
6) Conclusion
What is Ethical Hacking?
Ethical Hacking is the practice of testing a computer system, network, or software to find security problems. It is done by people who have permission to hack and who help protect systems. The main goal is to find and fix weaknesses before bad hackers can use them.
Ethical Hackers work like real hackers but with a good purpose. For example, a company may hire an Ethical Hacker to check if their website can be attacked. The hacker will try to break in, find weak spots, and report them to the company. This helps the company make its systems stronger and safer from cyberattacks.
Benefits of Ethical Hacking
Here are the advantages of Ethical Hacking:
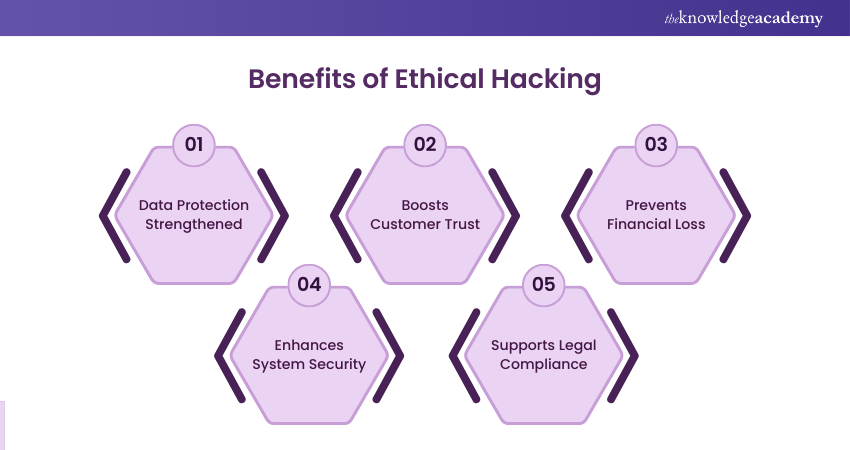
a) Protects important data from cyber criminals
b) Builds trust with customers and users
c) Prevents loss of money and business due to hacks
d) Improves the overall security of a company
e) Trains staff to be more careful and aware
f) Keeps the company safe from legal troubles
g) Prepares the system for future threats and attacks
h) Helps follow industry standards and regulations
i) Increases confidence in using digital systems safely
Types of Ethical Hacking
Some of the common Types of Ethical Hacking include:
1) Web Application Hacking
This type checks websites and online apps for weak areas that hackers could attack. Ethical Hackers test login forms, search boxes, and data entry points. They look for bugs or coding mistakes that can let hackers in. The goal is to keep user data and the website safe.
a) Finds problems in website code
b) Stops hackers from stealing user data
c) Keeps online apps safe and working well
d) Tests user input fields for security gaps
2) System Hacking
This involves testing a computer system to find and fix security issues. Ethical Hackers try to gain access just like real hackers would. They check if passwords, files, or settings can be broken into. This helps protect important data on computers.
a) Protects files and private data
b) Fixes weak points in computer settings
c) Stops illegal access to the system
d) Checks password strength and user permissions
3) Web Server Hacking
This focuses on the main computer (server) that runs websites. Ethical Hackers test the server for errors or security gaps. They make sure the server is not easy to break into. A safe server keeps the whole website secure.
a) Keeps the website running smoothly
b) Stops attackers from changing web content
c) Secures the server from outside attacks
d) Tests server software for known bugs
4) Hacking Wireless Network
This checks Wi-Fi and other wireless connections for security issues. Hackers can break into networks and use them without permission. Ethical Hackers test passwords and settings to make sure only trusted users can connect. It helps prevent data theft through open networks.
a) Secures Wi-Fi from outsiders
b) Protects data sent over the network
c) Prevents misuse of internet access
d) Checks for weak or default passwords
5) Social Engineering
This is when hackers trick people into giving away private information. Ethical Hackers test how easy it is to fool staff with fake emails or calls. They help train employees to spot and avoid such tricks. It’s about protecting the human side of security.
a) Teaches staff to stay alert
b) Prevents sharing of sensitive info
c) Reduces chances of scam-based attacks
d) Test response to phishing and fake messages
Learn to safeguard sensitive information with our Cyber Security Awareness Course – Join today!
Types of Hacking/Hackers
Here are the three main types of hackers based on how they use their skills:
1) White Hat Hacker
White Hat Hackers are also called Ethical Hackers. They use their skills to help companies stay safe from cyber threats. They test systems, find weak spots, and fix them before real hackers can attack. These hackers follow the law and work to protect information.
a) Hired by companies to test security
b) Help fix the website or system issues
c) Work with government or private firms
d) Use legal tools and methods
2) Black Hat Hacker
They break into systems without permission. They often steal, damage, or sell private information. These hackers break laws and cause serious harm to people or businesses. Their goal is usually to make money or cause trouble.
a) Steal bank or card details
b) Spread viruses or malware
c) Sell stolen data on the dark web
d) Often wanted by law enforcement
3) Gray Hat Hacker
They are a mix of white and black hat hackers. They may break into systems without asking, but they don’t always do it to cause harm. Sometimes, they tell the company about the issue, but they don’t have permission to check it. Their actions can be both helpful and risky.
a) Find issues in systems and report them
b) Not always hired, but may help
c) Can still break the rules or laws
d) Sometimes seek recognition or rewards
Learn to strengthen security with our Ethical Hacking Professional Course – Join today!
Phases of Ethical Hacking
Here are the phases of Ethical Hacking that assist the process from start to finish:

Pre-engagement Phase
This is the first step before any hacking work starts. In this phase, the goals and rules of the testing are discussed. The client and the Ethical Hacker agree on what systems can be tested and what methods can be used. This helps avoid legal problems and misunderstandings.
a) Defines what systems will be tested
b) Sets clear rules and limits
c) Helps avoid legal trouble
d) Builds trust between the hacker and the company
Reconnaissance
This phase is all about gathering information. Hackers try to learn as much as they can about the target system. This includes IP addresses, emails, employee details, and more. The goal is to collect data without touching the system directly.
Popular Tools Used
Here are the tools often used in this step:
a) Nmap
b) Maltego
c) Recon-ng
d) Google Dorks
Commonly Used Techniques
Here are some techniques used during reconnaissance:
a) Google search and open-source info
b) Social media lookup
c) WHOIS lookups
d) DNS footprinting
Vulnerability Assessment
This phase checks the system for weaknesses. Ethical Hackers use scanning tools to find security holes. The aim is to see what parts of the system could be attacked. It helps in making the system stronger.
Popular Tools Used
Here are some tools used to find weaknesses:
a) Nessus
b) OpenVAS
c) Nikto
d) Burp Suite
Commonly Used Techniques
Here are some common methods used:
a) Port scanning
b) Banner grabbing
c) Software version check
d) Misconfiguration checks
Exploitation
Now the hacker tries to use the weaknesses found earlier. They try to break into the system or take control. This helps to see how much damage a real hacker could do. It also shows how fast the company can detect the attack.
Popular Tools Used
Here are tools used to exploit weaknesses:
a) Metasploit
b)SQLmap
c) Hydra
d) BeEF
Commonly Used Techniques
Here are some methods used for attacks:
a) SQL Injection
b) Brute-force attacks
c) Cross-site scripting (XSS)
d) Buffer overflow
Post-exploitation
This phase checks what a hacker can do after getting access. The hacker might try to steal data, create new users, or move deeper into the system. It helps companies understand the full risk of a breach.
Popular Tools Used
Here are the tools used after access is gained:
a) Mimikatz
b) Netcat
c) Empire
d) PowerSploit
Commonly Used Techniques
Here are some techniques used post-exploitation:
a) Privilege escalation
b) Password dumping
c) Lateral movement
d) Data exfiltration
Reporting
This is the final step. The Ethical Hacker writes a report on everything found. It includes all the problems, how they were found, and how to fix them. This report helps the company improve its security.
Popular Tools Used
Here are some tools used for reporting:
a) Dradis
b) Serpico
c) MagicTree
d) Microsoft Word
Commonly Used Techniques
Here are some ways reports are created:
a) Clear and simple summaries
b) Step-by-step attack logs
c) Screenshots of findings
d) Fix recommendations
Conclusion
We hope you now understand What is Ethical Hacking and why it is important for keeping systems safe. Ethical Hackers help companies find and fix security problems before real hackers can cause harm. In addition, preparing for Ethical Hacker Interview Questions can help you understand the critical role they play in protecting data and improving security. By following the right steps, Ethical Hacking helps build safer networks and systems. It is a smart way to stay safe in today’s digital world.
Learn vulnerability assessment with our Mastering Metasploit Framework Course – Join today!
Frequently Asked Questions
What is the Purpose of Ethical Hacking?

The aim of Ethical Hacking is to find and fix security problems before bad hackers can use them. It helps protect data, systems, and networks from attacks. Ethical Hackers help companies stay safe and secure by testing for weak points.
Which Language is Used for Hacking?

Many hackers use languages like Python, JavaScript, and C to write tools and scripts. Python is popular because it’s easy to learn and works well for many tasks. Other languages like C++ or Java are also used for more complex attacks or software.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Ethical Hacking Courses, including the Ethical Hacking Professional Course and Mastering Metasploit Framework Course. These courses cater to different skill levels, providing comprehensive insights into Social Engineering Attacks.
Our IT Security & Data Protection Blogs cover a range of topics related to Ethical Hacking, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Ethical Hacking skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Ethical Hacking Professional
Ethical Hacking Professional
Thu 24th Sep 2026
Thu 3rd Dec 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


