 To help and support our clients we are providing a limited number of 250 daily discount codes. Hurry, first come, first served!
To help and support our clients we are providing a limited number of 250 daily discount codes. Hurry, first come, first served!
Cyber Security Training FAQs
Cyber Security refers to the process of safeguarding systems, networks, and data against attacks, unauthorised access, and digital threats. It provides secure information flows within organisations with regard to confidentiality, integrity, and availability.
Prerequisites for Cyber Security Courses vary depending on the specific course and level. Some introductory courses have no formal requirements, while advanced courses may require prior IT or security knowledge. Please refer to the individual course page for accurate, course-specific prerequisite details.
Cyber Security skills are essential due to the growing volume and sophistication of global cyber threats. These skills enable professionals to protect digital assets and access high‑demand, future‑proof career opportunities. Learning with The Knowledge Academy, a top training provider, further enhances credibility and industry readiness.
This training covers key skills such as threat analysis, vulnerability scanning, network defence strategies, incident response, and risk mitigation. The Knowledge Academy (TKA), a trusted Global Courses Provider, also provides exposure to industry‑standard tools and practical cyber security methodologies.
These Cyber Security Courses would suit IT Specialists, Network Administrators, security analysts, and security consultants who wish to gain security awareness. It can be useful to any delegates who would like to build a career or improvise career path in the sphere of cybersecurity.
Yes, Cyber Security Courses are prepared to encourage those who are set to begin learning in systematic learning plans. Security principles are presented in a clearer manner without the need to involve complicated issues.
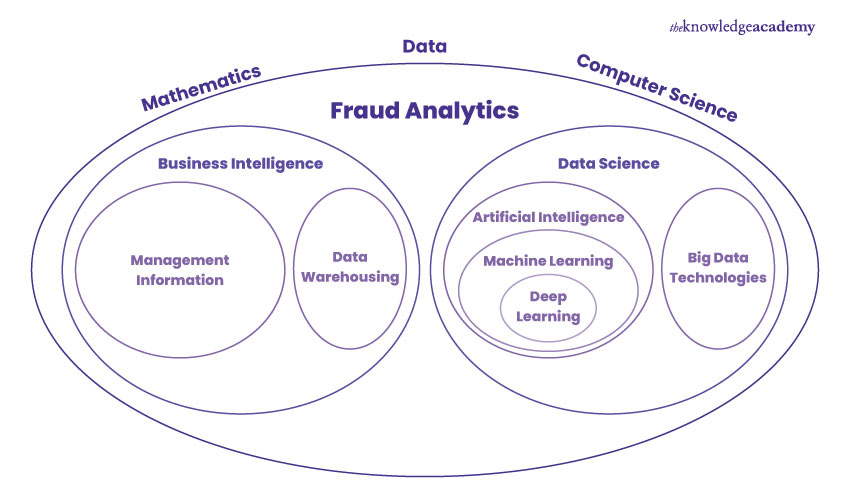
The most effective Cyber Security Courses are the ones that conform to the industry standards and certifications. Our courses include Certified Cyber Security Professional Training, Cyber Security Awareness Course, Digital Forensics Training, and Fraud Analytics Training. There are more options for you that include practical abilities and real-world examples.
Some of the subjects covered in these Cyber Security Certification Courses are network security modules, ethical hacking, cryptography, risk assessment, compliance, cloud security and handling of incidents. It has been designed in a manner that is compliant with the present industry and certification standards.
The Knowledge Academy, a trusted training provider, offers 24/7 support via phone & email before attending, during, and after the course. Our customer support team is available to assist and promptly resolve any issues you may encounter.
Yes, after completing this course, you will receive a certificate of completion to validate your achievement and demonstrate your proficiency in the course material.
After completing Cyber Security Courses from a training provider in Philippines, your earning will be very high since these certifications are very high-in demand in global market. In all the industries, professionals can expect a rise of 30% since they have been certified in Cyber Security Training.
Some of the job opportunities that are in high demand in the Cyber Security field include Cyber Security Analyst, Security engineer, Ethical Hacker, SOC Analyst, and Information Security Manager. These are significant roles played in the government and in the corporate world.
These Cyber Security Courses provided by The Knowledge Academy, a Global Training Provider, would assist you in achieving job-ready and qualification-based skills. It allows progression in the profession, foreign-exposed experience and service in a rapidly expanding field.
The Knowledge Academy stands out as a prestigious training provider known for its extensive course offerings, expert instructors, adaptable learning formats, and industry recognition. It's a dependable option for those seeking this certification.
Please see our Cyber Security Training available in Philippines
The Knowledge Academy is one of the Leading global training provider for Cyber Security Training.
The training fees for Cyber Security Training in Philippines starts from $1995

Why we're the go to training provider for you

Best price in the industry
You won't find better value in the marketplace. If you do find a lower price, we will beat it.

Trusted & Approved
Recognised by leading certification bodies, we deliver training you can trust.

Many delivery methods
Flexible delivery methods are available depending on your learning style.
High quality resources
Resources are included for a comprehensive learning experience.




"Really good course and well organised. Trainer was great with a sense of humour - his experience allowed a free flowing course, structured to help you gain as much information & relevant experience whilst helping prepare you for the exam"
Joshua Davies, Thames Water



Looking for more information on Cyber Security Training
 Top 50 Cyber Security Interview Questions with Answers in 2026
Top 50 Cyber Security Interview Questions with Answers in 2026 Cyber Security Analyst Salary: The Definitive Guide
Cyber Security Analyst Salary: The Definitive Guide Cyber Security Job : Roles & Career Guide
Cyber Security Job : Roles & Career Guide What is a Whaling Attack? Meaning and Prevention
What is a Whaling Attack? Meaning and Prevention What is SIEM? A Beginner's Guide
What is SIEM? A Beginner's Guide What is a Proxy Server? Types, Benefits, and Risks
What is a Proxy Server? Types, Benefits, and Risks What is a SOC Analyst? The Ultimate Guide
What is a SOC Analyst? The Ultimate Guide Types of Cyber Attacks And How to Prevent Against Them
Types of Cyber Attacks And How to Prevent Against Them Importance of Cyber Security: A Complete Overview
Importance of Cyber Security: A Complete Overview















 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


