We may not have the course you’re looking for. If you enquire or give us a call on +1 6474932992 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

It's no news that our lives are increasingly woven into the digital realm. This is precisely the reason Cyber Attacks have become the unseen storms capable of disrupting everything, from personal moments to global operations. Understanding Cyber Attack is the first step toward staying protected.
From deceptive phishing emails to sophisticated ransomware campaigns, cyber threats are growing more advanced and widespread. This blog explores What is a Cyber Attack, its alarming trends, the steps to detect and mitigate it and more. So read on and step up your cyber warrior game!
Table of Contents
1) What is a Cyber Attack?
2) Types of Cyber Attacks
3) Emerging Cyber Attack Trends & Future Threats
4) How Can a Cyber Attack Be Prevented?
5) Detecting Cyber Attacks
6) Mitigating Cyber Attacks
7) Conclusion
What is a Cyber Attack?
A Cyber Attack refers to an attempt to gain unauthorised access to computers or networks, often to disrupt operations or steal sensitive data. It's often the first step attackers take before carrying out larger incidents, such as data breaches affecting individuals or organisations.
The primary objective of a Cyber Attack may be to shut down systems, disrupt services or gain access to valuable information as it spreads through connected networks. Cybercriminals commonly use techniques such as denial-of-service attacks, malware, phishing and ransomware to carry out these intrusions.
Types of Cyber Attacks
Now let’s explore the most prevalent types of Cyber Attacks to watch out for:
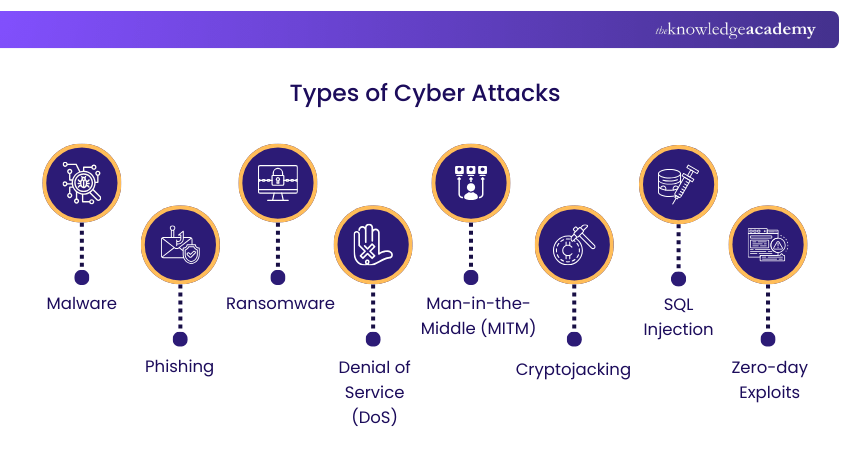
1) Malware
Malware refers to malicious software that disrupts computers, servers or networks. Common types of malware include worms, viruses and Trojans, all of which can replicate and spread within systems. Once inside a network, malware can allow attackers to access sensitive data, damage devices, disrupt operations or even gain control of systems.
2) Phishing
Phishing is a Cyber Attack technique that deceives individuals into revealing sensitive information. Attackers typically send emails that appear to come from trusted sources and include harmful attachments. These links often lead users to fake websites that prompt them to enter login details or financial information. While some phishing campaigns target large groups, others are carefully designed to target specific individuals or organisations.
3) Ransomware
This type of malware attack is driven by financial motives. In this attack, victims receive messages with malicious attachments, which, when opened, can encrypt files, systems or entire networks. The attacker then demands a ransom payment with the promise of restoring access to the encrypted data. Beyond the ransom itself, ransomware can cause significant financial losses through operational downtime. Ransomware’s prevalence can be further gauged by the fact that the global ransomware protection market size is projected to reach £74 billion by 2033.
4) Denial of Service (DoS)
This type of Cyber Attack aims to make online services unavailable by overwhelming systems with excessive traffic or requests. This flood of activity forces websites or servers to slow down or even shut down completely. A more advanced variation is a Distributed Denial-of-Service (DDoS) attack, where attackers use multiple compromised devices to generate the traffic and intensify the disruption.
5) Man-in-the-Middle (MITM)
This type of attack occurs when a malicious actor secretly intercepts communication between a user and an online service. For example, an attacker may set up a fake public Wi-Fi network that appears legitimate. When the users connect, the attacker can capture sensitive information such as login credentials or personal data transmitted during the session.
6) Cryptojacking
Cryptojacking involves secretly using another person’s computer, mobile device or server to mine Cryptocurrency. Attackers may install malware or run malicious scripts through web browsers to gain access to the device’s computing power. These attacks are designed to remain hidden, often only noticeable through reduced system performance or unusually active cooling fans.
7) SQL Injection
This Cyber Attack method exploits vulnerabilities in web applications that interact with databases using Structured Query Language (SQL). By inserting malicious queries into input fields, attackers can access sensitive information like usernames and passwords. In severe cases, they may modify or delete data, transfer funds or gain deeper access to internal systems.
8) Zero-Day Exploits
These attacks target previously unknown vulnerabilities in a software code that Developers have not yet identified or patched. Once attackers discover such weaknesses, they can exploit them to infiltrate systems before organisations become aware of the issue. These attacks allow Hackers to steal data, collect credentials and expand their access within networks while remaining undetected for extended periods.
9) DNS Tunneling
This is a Cyber Attack technique that abuses the Domain Name System (DNS), which normally translates domain names into IP addresses. Since DNS traffic is rarely monitored for data transfer, attackers exploit it to send malicious data. By creating a domain hosted on their own server and infecting a target system, attackers can establish a hidden communication channel to steal information or carry out further malicious activities.
10) Password Attacks
Password attacks involve attempts by Hackers to obtain a user’s password to gain unauthorised access to systems or accounts. Since passwords are widely used as a primary authentication method, they are a common target for cyber criminals. Attackers may discover passwords written on paper or sticky notes, or stored insecurely near a workstation, or obtain them through insiders who provide access intentionally or unintentionally.
Spot the patterns and stop the fraud. Become the Analyst every system needs with our Fraud Analytics Training - Sign up now!
Emerging Cyber Attack Trends & Future Threats
Cyber threats evolve as attackers exploit advanced technologies and modern infrastructure. Although these threats are still developing, they already need close monitoring from Security Operations Centres (SOCs) and Cyber Security teams. Here are some of the alarming trends to watch out for:
1) AI-driven Attacks
Artificial Intelligence (AI), especially generative AI, has created new opportunities for Cyber Attackers. Criminals can use large language models (LLMs) to design highly convincing phishing messages, generate deepfake audio and video and automate large-scale reconnaissance activities. More advanced techniques, such as prompt injection and AI jailbreaks, can also be used to bypass built-in safety controls.
2) Cloud and Container Exploits
As organisations increasingly move their workloads to public and hybrid Cloud environments, the potential attack surface grows. Exposed Application Programming Interfaces (APIs) and vulnerabilities in container orchestration platforms like Kubernetes can provide attackers with entry points. A single configuration error can allow threat actors to move across multiple workloads.
3) Data Tampering
Data integrity attacks are about corrupting data while it is stored, transmitted or processed. By manipulating datasets, attackers can cause systems to make misleading decisions. This may involve modifying real-time data streams or altering records in sectors such as finance and healthcare. A particularly concerning method is data poisoning, where attackers inject malicious data into machine learning training datasets.
4) Quantum-era Risks
Advancements in quantum computing pose possible challenges to current public-key encryption systems. Cyber Attackers are already adopting “harvest now, decrypt later” strategies, in which the encrypted data is collected today with the expectation that future quantum technologies will enable its decryption. To address this emerging risk, organisations must monitor the developments in Post-quantum Cryptography (PQC).
Embrace the human side of Cyber Security with our Social Engineering Training. Sign up now and outsmart the manipulators!
How Can a Cyber Attack Be Prevented?
Proper prevention begins with identifying an organisation’s most valuable assets and understanding the potential attack surface around them. By pinpointing these vulnerabilities, organisations can reduce the chances of unauthorised access. Here are some common preventive measures:
1) Identity and Access Management (IAM): IAM makes sure that only authorised individuals can have access to critical systems. This is enforced through least-privilege access, multi-factor authentication and strong password policies. Many organisations also require remote users to connect through secure channels like Virtual Private Networks (VPNs).
2) Data Security and Data Loss Prevention (DLP): These measures protect sensitive information by encrypting data, monitoring how it is stored and used, and maintaining regular backups to minimise the damage caused by potential breaches.
3) Network Controls: Organisations deploy multiple layers of firewalls and intrusion prevention systems (IPS) to detect and block malicious traffic entering or leaving the network. This also helps prevent malware from communicating with Command-and-Control (C2) servers.
4) Continuous Vulnerability Management: Regular system updates, security patches, and penetration testing help identify and fix weaknesses before the attackers can exploit them.
5) Attack Surface Management (ASM): ASM involves identifying, tracking and securing exposed assets across on-premises systems, Cloud environments and Internet of Things (IoT) devices before attackers discover them.
6) Security Awareness Training: Educating employees helps them recognise phishing emails, Social Engineering attempts and other common methods attackers use to gain entry into organisational systems.
Detecting Cyber Attacks
Since no security defence is completely foolproof, organisations must maintain continuous visibility across their networks and information systems to detect potential threats quickly. Here are some ways to detect Cyber Security Attacks:
1) Security Information and Event Management (SIEM): SIEM systems collect and analyse alerts from multiple security tools to identify suspicious activity. This includes intrusion detection systems and endpoint detection and response (EDR) platforms.
2) Threat Intelligence: Threat intelligence boosts security alerts by providing information about known attackers, tactics and Indicators of Compromise (IOCs). This helps security teams respond more efficiently.
3) Advanced Analytics and AI: Modern detection tools use Machine Learning and advanced analytics to point out unusual behaviour patterns. This helps them detect potential cyber incidents that might otherwise go unnoticed.
4) Proactive Threat Hunting: Cyber Security Analysts actively search for hidden threats, such as Advanced Persistent Threats (APTs), that automated security tools may fail to detect.
Register for a course on Introduction To System And Network Security and acquire the skill set to protect systems and networks with ease!
Mitigating Cyber Attacks
When an attack is identified, a coordinated and well-structured response helps reduce damage and restore operations quickly. Here are some mitigation steps you can take:
1) Incident Response Planning: A documented and regularly tested response plan enables organisations to contain security incidents, eliminate threats, restore systems and perform Root Cause Analysis (RCA) to prevent similar attacks in the future.
2) Security Orchestration, Automation and Response (SOAR): SOAR platforms integrate multiple security tools and automate routine processes. It helps security teams focus on more complex investigations and Threat Analysis.
3) Extended Detection and Response (XDR): XDR platforms combine security data from endpoints, networks, emails, application and Cloud environments to deliver a unified view of threats and accelerate remediation efforts.
4) Post-incident Review: After resolving an incident, organisations conduct reviews to identify lessons learned, strengthen security controls and update preventive and detection strategies based on new threat intelligence.
Conclusion
Cyber Attacks are no longer distant threats; they are a menacing reality. By understanding What is a Cyber Attack, how these attacks occur and recognising their various forms, individuals and organisations can take smarter steps to stay protected. Strong security practices and awareness are the keys to defending valuable data and maintaining trust in an increasingly connected world.
Become a malware Detective and outsmart the unseen threats before they strike. Sign up for our Malware Analysis Training now!
Frequently Asked Questions
What Do Cyber Attacks Target?

Cyber Attacks typically target digital assets such as sensitive data, financial information, intellectual property and critical systems within organisations. Attackers may also focus on networks, databases, cloud environments and connected devices to gain unauthorised access or disrupt operations.
How do Cyber Attacks Occur?

Cyber Attacks occur when attackers exploit vulnerabilities in systems, networks, software or human behaviour to gain unauthorised access. They may use techniques such as phishing emails, malware infections, weak passwords or unpatched software vulnerabilities to enter a system.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Training, including the Certified Cyber Security Professional (CCS-PRO) Course, Cyber Security Awareness Course and the Cyber Security Risk Management Training. These courses cater to different skill levels, providing comprehensive insights into Vulnerability Management.
Our IT Security & Data Protection Blogs cover a range of topics related to Cyber Attacks, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Cyber Security skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Certified Cyber Security Professional (CCS-PRO)
Certified Cyber Security Professional (CCS-PRO)
Fri 26th Jun 2026
Fri 4th Sep 2026
Fri 23rd Oct 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


