 To help and support our clients we are providing a limited number of 250 daily discount codes. Hurry, first come, first served!
To help and support our clients we are providing a limited number of 250 daily discount codes. Hurry, first come, first served!
Automation & Penetration Testing FAQs
Taking these courses can enhances your cybersecurity skills, enabling individuals to identify vulnerabilities, automate security tasks, improve system defenses, and stay updated with the latest threats, ultimately boosting career prospects and organisational security.
These courses enhance your cybersecurity skills by teaching efficient vulnerability identification, exploitation techniques, and automated security processes, enabling professionals to proactively defend systems, identify weaknesses, and strengthen overall security posture effectively.
There are no formal prerequisites for attending these courses. However, a basic understanding of the Linus Operating System would be beneficial for the delegates.
Automation techniques improve Penetration Testing efficiency by streamlining repetitive tasks, increasing test coverage, reducing human error, and accelerating the detection of vulnerabilities. This allows security professionals to focus on more complex analysis and remediation efforts.
These Automation and Penetration Testing Courses by The Knowledge Academy, a trusted training provider, cover tools such as Selenium, Jenkins, and Ansible for automation, and Metasploit, Burp Suite, Nmap, and Wireshark for Penetration Testing, equipping learners with essential practical skills.
The Automation and Penetration Testing exam, delivered by The Knowledge Academy, one of the top training providers, includes multiple-choice, drag-and-drop, and simulation-based questions, assessing knowledge of automation, Penetration Testing techniques, security concepts, and tools across both practical and theoretical areas.
Manual Penetration Testing involves human testers identifying and exploiting vulnerabilities using their expertise. Automated Penetration Testing uses software tools to scan and identify vulnerabilities quickly. Manual testing is thorough and context-aware, while automated testing is faster but less nuanced.
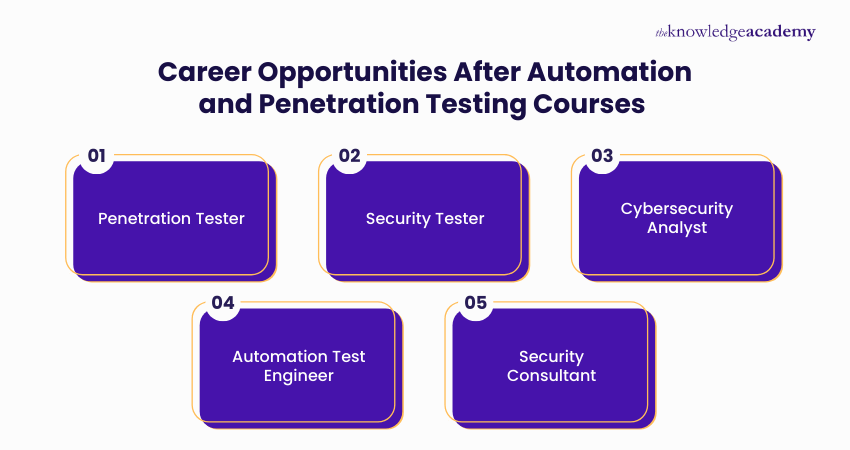
Professionals skilled in Automation and Penetration Testing can pursue careers as Security Analysts, Penetration Testers, Cybersecurity Consultants, Red Team Operators, Automation Engineers, Vulnerability Assessors, and Security Architects, often leading to roles in high-demand industries like finance, tech, and government.
This course typically takes around 5 to 7 weeks to complete, depending on the course structure and intensity, including both theoretical lessons and practical hands-on exercises to master essential skills.
Automation and Penetration Testing Courses by The Knowledge Academy, one of the best training providers, include practical labs, real-world scenarios, and hands-on projects, ensuring learners gain experience through industry-relevant simulations.
Upon completion of these courses by The Knowledge Academy, one of the global training providers, learners receive a Certified Automation Tester certification and a Certified Penetration Testing Professional certification, both recognised credentials that enhance professional credibility.
Please see our Automation & Penetration Testing available in Canada
The Knowledge Academy is one of the Leading global training provider for Automation & Penetration Testing.
The training fees for Automation & Penetration Testing in Canada starts from CAD5595

Why we're the go to training provider for you

Best price in the industry
You won't find better value in the marketplace. If you do find a lower price, we will beat it.

Trusted & Approved
Recognised by leading certification bodies, we deliver training you can trust.

Many delivery methods
Flexible delivery methods are available depending on your learning style.
High quality resources
Resources are included for a comprehensive learning experience.




"Really good course and well organised. Trainer was great with a sense of humour - his experience allowed a free flowing course, structured to help you gain as much information & relevant experience whilst helping prepare you for the exam"
Joshua Davies, Thames Water



Looking for more information on Automation & Penetration Testing
 65 Penetration Testing Interview Questions
65 Penetration Testing Interview Questions Penetration Testing Job Description Guide
Penetration Testing Job Description Guide How To Update Kali Linux? A Complete Breakdown
How To Update Kali Linux? A Complete Breakdown Penetration Testing Tools: A Complete Guide
Penetration Testing Tools: A Complete Guide Web Application Penetration Testing Explained
Web Application Penetration Testing Explained Network Penetration Testing and How It Identifies Risks
Network Penetration Testing and How It Identifies Risks What Is Kali Linux? A Beginner's Guide
What Is Kali Linux? A Beginner's Guide 15 Best Kali Linux Tools: An Overview
15 Best Kali Linux Tools: An Overview













 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


