We may not have the course you’re looking for. If you enquire or give us a call on + 1-866 272 8822 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Whether you’re an IT pro safeguarding your company’s digital fortress or a curious business owner, understanding the Types of Attacks in Cyber Security is crucial. These attacks come in all shapes and sizes, from the familiar to the obscure.
Imagine them as a rogue’s gallery of digital mischief-makers, each with its own modus operandi and motivations. In this blog, we’ll unravel the mysteries behind Types of Cyber Attacks, revealing their tactics and potential impact. So, grab your virtual magnifying glass, and let’s explore!
Table of Contents
1) What is a Cyber Attack?
2) Common Types of Cyber Attacks
a) Malware
b) Ransomware
c) Trojan
d) Phishing
e) Spoofing
3) How to Protect Against Cyber Attacks?
4) Conclusion
What is a Cyber Attack?
A Cyber Attack is the intentional action of cybercriminals or malicious agents to find unauthorised entry to computer systems, networks, or digital devices. The aim is often to steal, corrupt, damage, or reveal confidential data.
Cyber Attacks may be focused on individuals, business or government organisations. Some of the types of valuable assets that attackers tend to target include confidential information, customer data, financial records, intellectual property, and so on. Such attacks are usually performed with the help of such techniques as malware, phishing, ransomware, and other malicious tools that exploit security vulnerabilities in systems.
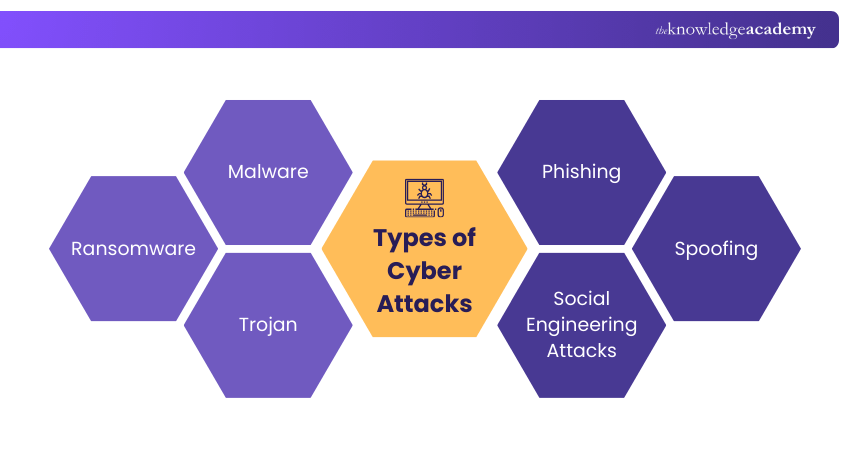
Common Types of Cyber Attacks
When attempting to hack into a network, a hacker never tries reinventing the wheel. Instead, attackers employ tried-and-tested approaches that they know are highly effective. Here is the list of different types of attacks in Cyber Security.
1) Malware
Malware, short for malicious software, is designed to damage systems, disrupt operations, or steal sensitive data from computers, networks, or servers. Malware is another type of cybercriminal activity that is usually used to access and break into digital systems without authorisation.
One common example is Trojan malware, which disguises itself as legitimate software to trick users into installing it. After activation, it runs in the background without any security controls and lets attackers obtain data or gain control of the impacted system.
2) Ransomware
Ransomware is a type of malware that blocks access to a system or encrypts files until a ransom is paid, usually in cryptocurrency. The victims are requested to pay a decryption key to recover access to their data.
These attacks may be directed against any individual or any organisation and may usually affect key systems. The payment of the ransom is not guaranteed to restore the encrypted information by the attacker even after payment.
3) Trojan
A Trojan is a malicious code that poses as a genuine program/file to deceive users into downloading it. It is commonly transmitted via email attachments, downloads, or counterfeit applications.
When installed, the Trojan may execute hidden processes, steal data, or leave a backdoor through which attackers can access the system unauthorisedly.
Build a foundation for a secure digital future – Sign up now for our Introduction to System and Network Security Course.
4) Phishing
Phishing refers to a form of Cyber Attack where hackers masquerade as trusted organisations through impersonation of banks, government agencies, or popular companies so as to mislead users. They normally attach fake emails, message, or links which they use to lure the victims into providing personal information.
Phishing is meant to steal user logins, financial or personal information by sending them to rogue websites or attachments. The attacks can also be done via phone calls (voice phishing) or text messages (SMS phishing) which has made them a very popular and efficient tool of cybercriminals.
5) Spoofing
Spoofing represents a kind of cyberattack, where the offenders impersonate someone they are trusted to be in order to ensure the confidence of a victim. This can be done by pretending and impersonating an authentic site, email address, IP address, or even phone number in order to make the communication sound authentic.
Spoofing aims at deceiving users to engage with malicious systems that can result in stolen information, malware, or unauthorised network access. Some of the common types are email spoofing, domain spoofing, and IP spoofing.
6) Social Engineering Attacks
Social engineering attacks are computer attacks which exploit human behaviour to find unauthorised access to systems or other sensitive information. Rather than exploiting technical flaws, attackers manipulate people into disclosing passwords or financial information or other confidential information.
These attacks are based on psychological strategies like trust, urgency, or curiosity to swindle victims. The most common ones are phishing, baiting, pretexting, and tailgating, in which attackers convince users to perform actions that undermine security.
7) Denial-of-service Attack
A Denial-of-service (DoS) attack happens when the attackers saturate a system, network, or server with unnecessary traffic, which leaves the system unable to respond to legitimate requests. This overload makes the intended system to slow down or cease to perform well.
In contrast to most cyberattacks related to stealing data, DoS attacks are concerned with interfering with services and rendering the systems unavailable to their users. These are frequently employed to disrupt organisations or government systems and result in financial or operational harm.
8) SQL Injection
SQL Injection is a type of cyber attack whereby the attackers put malicious SQL statements in the input boxes of a web application. This enables them to view, edit, or delete information saved in the database of the application.
The attack will exploit any vulnerabilities in database-driven applications and may expose sensitive information like the user credentials or financial data to the attacker. SQL Injection is more dependent on server-side database systems in contrast to the XSS attacks, which are user-focused.
9) Man-in-the-middle Attack
A Man-in-the-middle (MitM) attack is a type of cybercrime in which a criminal compromises the communication between two parties that assume they are communicating directly with each other. The attacker places himself between the sender and the receiver without their knowledge.
It enables the attacker to spy, steal, or alter the data being exchanged on the fly. MitM attacks help hackers gain access to sensitive information like logins, financial information, or personal data.
10) DNS Spoofing
DNS spoofing is a computer attack that aims at tampering with the Domain Name System to make users access a fake site rather than a genuine one. This fraud allows the victims to assume that they are entering into a reputable site.
After being redirected, the user can proceed to fill in personal information without realising like passwords or bank details. This data can then be stolen by the attackers or malware and other malicious information can be propagated using the bogus site.
11) Drive-by attacks
Drive-by attack is a type of attack that involves attackers inserting malicious code on the attacked or unsecure websites. Once the user accesses the site, the malware will be automatically downloaded or installed on the device of the user without the user needing to do anything.
These attacks use the weaknesses of browsers or old software. Drive-by infections may be mitigated by keeping systems up to date and employing security applications like web filtering.
12) Password Attack
A password attack is a computer hack where hackers are trying to access or break user passwords to gain unauthorised access to systems or accounts. Since most organisations use passwords as a form of authentication, they are frequently targeted by cybercriminals.
The methods that may be employed by attackers include brute-force attacks, dictionary attacks, network interception, or social engineering to steal passwords. Hackers can easily guess the login credentials and compromise accounts using weak or easily guessable passwords.
13) Insider Threat
An insider threat happens when a person in an organisation, like the employees, contractors, or ex-employees, abuses their approved access to systems or data. Insiders are in a situation to create high levels of security threats because they have previous access to the network and are familiar with the internal processes.
These attacks can be both intentional, like stealing sensitive information and accidental, due to negligence or bad security practices. Organisational insider risks can be mitigated by using a high level of access controls, monitoring, and frequent cybersecurity awareness training.
Learn the fundamentals of Cyber Security Awareness. Sign up for our Cyber Security Awareness Course now!
How to Protect Against Cyber Attacks?
Protecting against cyber attacks begins with awareness and strong cybersecurity practices. Individuals and organisations must identify possible threats and proactively ensure protection of systems, networks, and sensitive data. Varying security policies, employee training, and keeping systems current can go a long way in decreasing the risk of cyber incidents and enhancing cyber resilience in general.
Following are the ways to prevent:
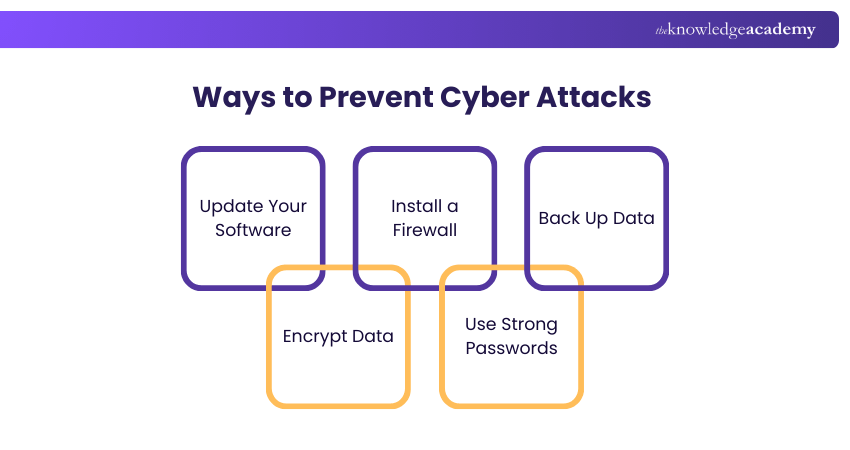
1) Update Your Software
Keeping software up to date ensures resilience against attacks. Updates fix flaws and vulnerabilities. Investing in a patch management system can help maintain current software versions.
2) Install a Firewall
Firewalls control network traffic, preventing attacks like backdoors and denial of service. They block suspicious activity deemed harmful to your computer.
3) Back Up Data
Regularly back up data to a secure location, such as cloud storage or a physical device. This ensures you can recover lost data in case of an attack.
4) Encrypt Data
Encrypting data ensures it's only accessible with a decryption key. This makes it difficult for attackers to access information, as they would need to guess the correct key through brute force.
5) Use Strong Passwords
Use unique, strong passwords for different accounts and systems. Combine special characters, upper and lowercase letters, and numbers. Regularly update passwords to enhance security and avoid reuse.
Conclusion
Armed with knowledge, you’re now a digital Sherlock Holmes, ready to foil the nefarious plots of cyber villains. Remember, Cyber Attacks are like puzzle pieces—each one fits a different scenario. We’ve explored over Types of Cyber Attacks, from phishing to ransomware, and even the elusive zero-day exploits. Alongside external risks, it’s essential to recognise Insider Threats in Cyber Security, which can be just as damaging if overlooked. But fear not! You’re not alone in this virtual maze. Implement robust defences, stay vigilant, and keep your firewalls fortified. And just like that, you’ll be the hero your network deserves!
Secure your digital assets with a comprehensive Cyber Security Risk Management Course. Sign up today!
Frequently Asked Questions
What happens during a Cyber Attack?

During a Cyber Attack, attackers infiltrate a computer system or network to steal, alter, or destroy data, disrupt operations, or gain unauthorised access. This can involve malware, phishing, or exploiting system vulnerabilities.
What Causes Cyber Attacks?

Cyber Attacks are caused by motives such as financial gain, espionage, political agendas, or personal grievances. They exploit system vulnerabilities, user negligence, or social engineering tactics to gain unauthorised access to data and systems.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Training, including the Certified Cyber Security Professional Training, Cyber Security Awareness Course, and Cyber Security Risk Management Course. These courses cater to different skill levels, providing comprehensive insights into Password Attacks.
Our IT Security & Data Protection Blogs cover a range of topics related to Cyber Security, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Cyber Security skills, The Knowledge Academy's diverse courses and informative blogs have you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Certified Cyber Security Professional (CCS-PRO)
Certified Cyber Security Professional (CCS-PRO)
Fri 26th Jun 2026
Fri 4th Sep 2026
Fri 23rd Oct 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


