We may not have the course you’re looking for. If you enquire or give us a call on +60 1800812339 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

People utilise a search engine day-to-day without even understanding its full capabilities. Using specific search and syntax techniques, you can find information that exists but is not readily visible. This process is known as Google Dorking. What is Google Dorking exactly? It is a process that uncovers information that could be sensitive or simply overlooked. It is important to know how it works and when it becomes a security risk to use it safely. Let's begin!
Table of Contents
1) What is Google Hacking/Dorking?
2) How Does Google Dorking Work?
3) Google Dorking Techniques
4) Examples of Google Dorking
5) The Dangers of Google Dorking
6) How to Prevent Google Dorking?
7) Complete List of Known Working Search Operators
8) How Cybercriminals Exploit Google Dorking?
9) Conclusion
What is Google Hacking/Dorking?
Google Dorking, also known as Google Hacking, is a legal technique that uses advanced search operators to uncover information not easily found through standard queries. It takes advantage of Google’s powerful search algorithms to locate specific text, files, or data that often remain hidden from regular users.
Think of Google as a giant library. Most people search its shelves for obvious titles, but with the right tools (advanced search techniques), you can uncover what lies behind locked drawers and in the margins. Google Dorking works like a magnifying glass, helping you reveal valuable details that typical searches overlook.
How Does Google Dorking Work?
Google Dorking works by using advanced search operators such as filetype: inurl: and in the title: to refine queries and zero in on specific information hidden within indexed web pages. These operators instruct Google’s algorithm to search for particular file types, keywords in URLs or titles, and other targeted content that standard searches would likely miss.
Because Google continuously crawls and indexes publicly accessible web content, anything that isn’t properly secured, like configuration files, credentials or private documents, can be revealed using these techniques. Although often used by security professionals to audit systems, Google Dorking must be guided by cyber security principles and remains legal so long as it only accesses public information.
Enhance your cyber defence capabilities with the comprehensive Certified Cyber Security Professional (CCS-Pro) course.
Google Dorking Techniques
If you want to dive deeper into search results and uncover information hidden from regular browsing, mastering a few specific Google Dorking techniques can make a significant difference. Here are some key methods:
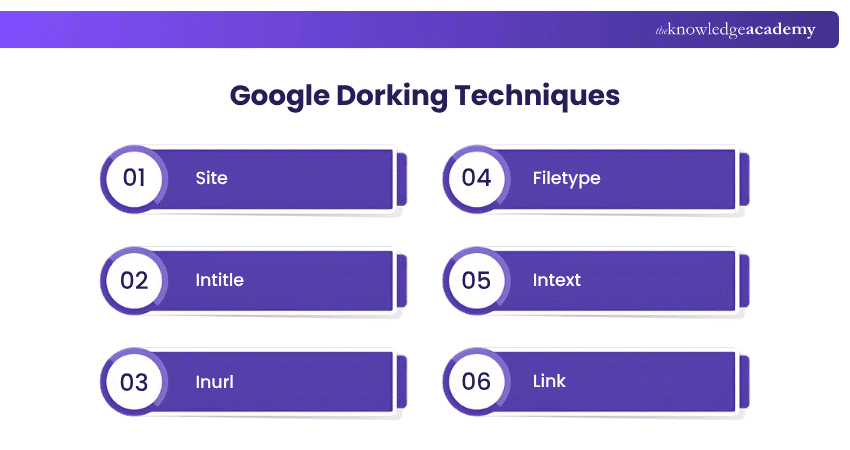
a) Site: This technique restricts your search to a specific website or domain. For example, using site:example.com will display results exclusively from "example.com."
b) Intitle: The "intitle:" command searches for specific keywords within the title of web pages. For instance, intitle:"login" can help locate pages with "login" in their titles, often leading to login portals.
c) Inurl: The "inurl:" command searches for keywords within URLs. For example, inurl:admin might reveal admin pages.
d) Filetype: This command searches for specific file types, such as PDFs or Excel sheets. For example, filetype:pdf confidential can uncover potentially sensitive PDF documents.
e) Intext: The "intext:" command searches for specific words within the content of web pages. For instance, intext:"password" could expose pages containing visible passwords.
f) Link: The "link:" command is used to find web pages that link to a specific URL. For example, link:example.com displays pages that include links pointing to example.com.
By mastering these Google Dorking techniques, you can reveal data that regular searches might overlook, giving you a deeper understanding of what's accessible online.
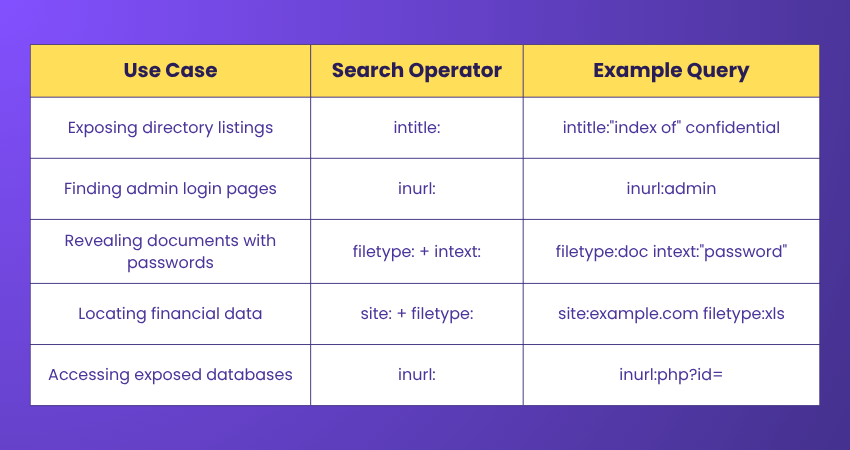
Examples of Google Dorking
Understanding Google Dorking becomes clearer with practical examples that demonstrate its effectiveness in uncovering hidden data. Here are some examples:
Protect your business – Start Cyber Security Risk Management Training today!
The Dangers of Google Dorking
While this technique can be useful, it also presents serious risks if misused. Sensitive data, such as passwords or private documents, may be exposed and easily found through targeted searches using a Google Dork.
It can also reveal security flaws, violate privacy, and lead to legal issues. In some cases, it may even be used for corporate spying, putting business information at risk.Master digital investigation techniques – Register in Digital Forensics Training now!
How to Prevent Google Dorking?
Given the risks associated with Google Dorking, organisations must adopt effective measures to protect their data and prevent unintended exposure. To safeguard against the dangers of this consider the following key steps:
a) Secure Sensitive Files: Ensure that confidential files are not stored in public directories, and implement strong access controls to restrict who can view or download these files.
b) Robots.txt Configuration: Use a robots.txt file to prevent search engines from indexing sensitive sections of your website, reducing the chances of them being exposed through Google Dorking.
c) Use Proper Permissions: Set strict permissions on files and directories to ensure that only authorised users can access them, minimising the risk of unauthorised access.
d) Regularly Audit Your Website: Conduct routine audits to identify and remove any exposed files or vulnerable pages that may have been indexed by search engines.
e) Avoid Storing Sensitive Data in URLs: Ensure that sensitive information is not included in URLs, as it can be easily discovered using Google Dorking techniques.
Enhance your expertise in Computer Forensics with the Computer Forensics Training- Join today!
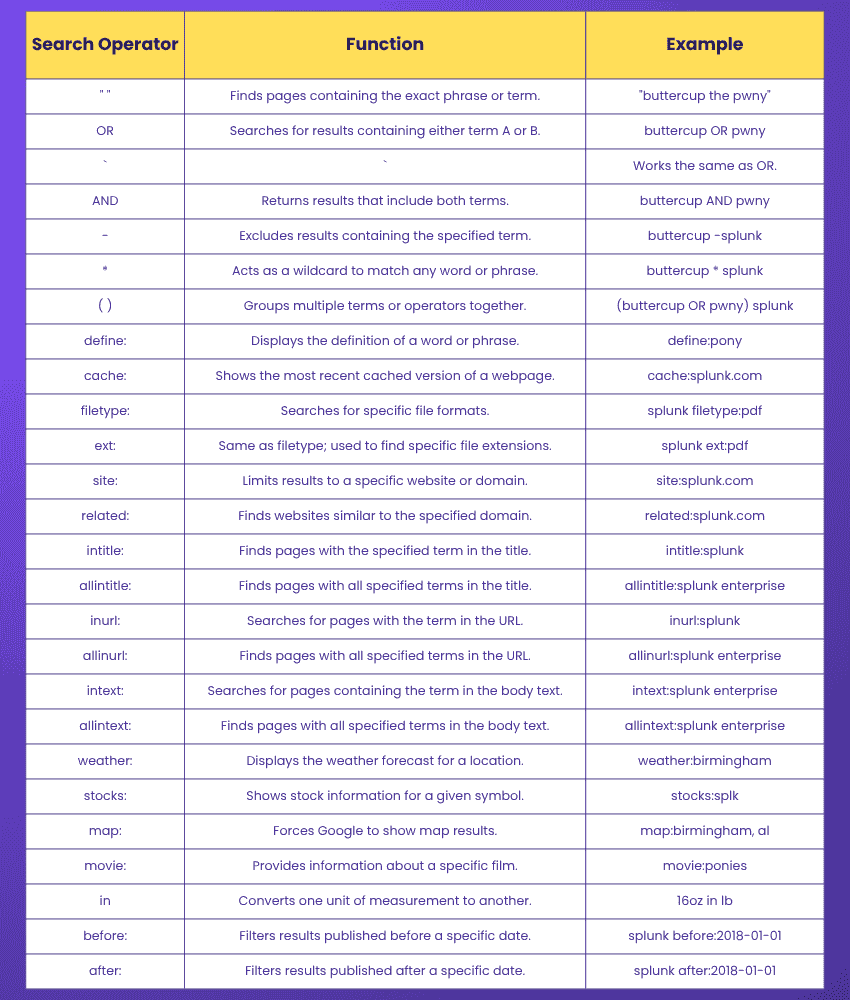
Complete List of Known Working Search Operators
Below is a comprehensive list of currently supported Google Search Operators, many of which are useful for advanced search techniques like Google Dorking.
How Cybercriminals Exploit Google Dorking?
Cybercriminals use it to identify vulnerable login pages, such as admin panels, by scanning indexed sites, enabling brute-force attacks. They also uncover exposed databases and confidential files containing sensitive user information.
By locating these unsecured pages and files, attackers can harvest credentials, financial records, and internal documents, which are then exploited for identity theft, fraud, or unauthorised system access.
Conclusion
Google Dorking offers powerful search capabilities that can uncover hidden or overlooked information online. While it has legitimate uses in cybersecurity and research, it must be applied responsibly to avoid ethical and legal issues. Understanding its risks is key to using it safely and effectively.Build fraud detection and analytics skills with our comprehensive Fraud Analytics Course, start learning today!
Frequently Asked Questions
Is Google Dorking Illegal?

Google Dorking is not illegal in itself; it simply entails making use of advanced search operators to access information that is publicly available, which has been indexed by Google. However, to use the obtained data for nefarious purposes or to access a private system without authorisation is illegal and could result in prosecution.
Can Google Dorking be Used for Ethical Hacking?

Yes, ethical hackers use this to identify exposed data and weak points in systems. When used responsibly, it supports vulnerability assessment without breaching laws or accessing unauthorised content.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 19 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Training, including the Cyber Security Awareness Training, Cyber Security Risk Management Resources, and Fraud Analytics Training Course. These courses cater to different skill levels, providing comprehensive insights into Zero Trust Security.
Our IT Security & Data Protection Blogs cover a range of topics related to Google Dorking, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your IT Security & Data Protection skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

The Knowledge Academy is a world-leading provider of professional training courses, offering globally recognised qualifications across a wide range of subjects. With expert trainers, up-to-date course material, and flexible learning options, we aim to empower professionals and organisations to achieve their goals through continuous learning.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Cyber Security Awareness
Cyber Security Awareness
Fri 26th Jun 2026
Fri 4th Sep 2026
Fri 23rd Oct 2026





 Top Rated Course
Top Rated Course








 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


