We may not have the course you’re looking for. If you enquire or give us a call on +1 7204454674 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Cyber Security Risk Management is a managed and active process that assists organisations in identifying, assessing and ranking risks impacting their digital assets and operations to take informed actions to mitigate vulnerabilities in systems and networks. It is a structural element of information security, commonly called IT or Electronic Information Security, and it helps businesses to deploy specific measures against cyberattacks and information breach.
The key to this approach is the possibility to evaluate what threats might be realistic, what impact they might have, and implement necessary mitigation strategies to protect critical infrastructure in the future. As cyber threats continue to escalate, the Check Point Software 2026 Cyber Security Report found that organisations experienced an average of nearly 2,000 cyberattacks per week in 2025, representing a 70% increase compared to 2023 — underscoring the urgent need for robust Cyber Security Risk Management practices.
Table of Contents
1) What is Cyber Security Risk Management?
2) Why is Cyber Security Risk Management Important?
3) Process for Managing Cyber Security Risks
4) Frameworks and Standards for Managing Cyber Security Risks
5) Critical Capabilities for Managing Risk
6) What Are the Consequences of Not Managing Cyber Security Risks?
7) Best Practices for Managing Cyber Security Risks
8) What Will You Gain from Undertaking the Cyber Security Risk Management Process?
9) Conclusion
What is Cyber Security Risk Management?
Cyber Security Risk Management is a systematic method that will enable organisations to realise the possible threats to their systems, networks and data. Through proper security tools and monitoring systems, businesses are able to detect vulnerabilities at its initial stage and take effective measures to mitigate the risk of cyber attacks. This enhances the capacity of the organisation to defend its online space.
To limit both the risk and the effects of cyberattacks, cyber risk management is necessary. It is a continuous process which is concerned with identifying, assessing, prioritising and dealing with security risks. Through consistent analysis of threats and weaknesses, organisations can focus on the worst risks and implement appropriate controls to control them accordingly.
A developed cyber security risk management framework facilitates the overall business performance as well, as it protects sensitive information, ensures a stable operation and preserves the reputation of the organisation. It gives management a clear direction on security practices, compliance requirements which can enable the company to evade regulatory fines, financial losses and reputational losses.
Why is Cyber Security Risk Management Important?
Cyber security risk management assists organisations to safeguard their delicate information and computer systems against breaches and other malicious occurrences. By determining vulnerable spots and determining how to handle them, companies are able to minimise attack harm and prevent loss of customer and partner trust.
It also assists in adherence to legislation and industry standards helping organisations establish controls and processes that help minimise financial, operational and reputational damage. This action will build a stronger security system that can adjust to current threats.
Process for managing Cyber Security Risks
The following are the key stages involved in managing cyber security risks effectively within an organisation:
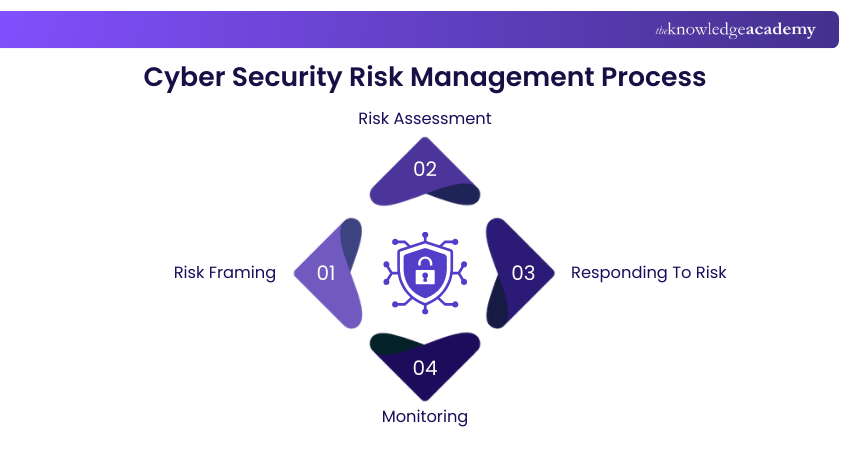
1) Risk Framing
Risk framing creates a context through which cyber risks are managed. During this phase, the organisation establishes its risk tolerance, business goals, regulatory requirements and general security interests. This assists leadership to establish clear directives on the amount of risk to be tolerated and to be able to align cyber security initiatives with business objectives.
2) Risk Assessment
Risk assessment is a method of identifying the possible threats and vulnerabilities that may impact the systems, data and operations. These risks are then analysed to establish the probability of occurrence and the impact that they may have. This assessment gives decision-makers the data required to determine which risks are the most threatening to the organisation.
3) Responding To Risk
The risk is evaluated after which the organisation decides on the response. This can be by mitigating the risk by security measures, transferring it (such as through insurance), avoiding it, or taking it (where the risk is in tolerance limits). The aim is to implement appropriate measures to reduce the possible harm to a reasonable degree.
4) Monitoring
Cyber risks are constantly evolving as they create new threats and vulnerabilities. Risk management strategies are kept up to date through continuous monitoring. Periodic reviews and updates to controls and continuous monitoring allow organisations to identify emerging risks as soon as possible and align their response plans with them.
Strengthen threat detection, incident response, network security, and risk management with our Certified Cyber Security Professional (CCS-PRO) Training – Sign Up Now!
Frameworks and Standards for Managing Cyber Security Risks
Below are some widely recognised frameworks and standards that help organisations structure their approach to managing cybersecurity risks, providing common practices and guidance:
1) ISO/IEC 27001
The ISO/IEC 27001 is a global standard in information security management. It provides specifications of setting, implementing, upholding, and advancing an Information Security Management System (ISMS). The standard includes risk assessment and treatment processes that require organisations to identify security risks, evaluate them consistently, and apply appropriate controls to protect the confidentiality, integrity and availability of information.
2) NIST Cybersecurity Framework Version 2.0
NIST Cybersecurity Framework (CSF) Version 2.0 is a set of guidelines and deliverables that organisations can adopt to control and mitigate cyber threats. It describes essential cybersecurity capabilities Govern, Identify, Protect, Detect, Respond and Recover enables organisations in various industries to align their business priorities and risk tolerance with cybersecurity operations. The model is not rigid and can be moulded to different degrees of cybersecurity maturity.
3) NIST Risk Management Framework
NIST Risk Management Framework (RMF) is a process that incorporates the security, privacy and supply chain risk management within the system development life cycle. It provides organisations with a roadmap, including risk management preparation, system categorisation, and choice and implementation of controls, evaluation of their efficiency, system operation authorisation, and continuous monitoring, to make certain that cyber and privacy risks are addressed in a uniform and risk-oriented way.
Critical Capabilities for Managing Risk
The main capabilities that are needed to handle risk within the organisation are as follows. These capabilities support structured assessment, clear ownership, and consistent monitoring of risks.
1) Collaboration and Communication Tools
Good collaboration and communication tools will facilitate teamwork in identifying, assessing, and responding to risks. They enable stakeholders to communicate updates, record discussions and ensure transparency through the entire risk management process. This eliminates confusion and ensures that everyone understands their responsibilities.
2) Risk Management Frameworks
Frameworks of risk management offer a rational method of risk identification and assessment. They provide clear guidance on assessment criteria, risk scoring, and mitigation planning. Application of recognised frameworks also facilitates consistency, consistency in regulation and better governance throughout the organisation.
3) Analytics
Analytics assists organisations to know the trends, patterns, and possible impact of risk. Data analysis helps teams to focus on the high-risk areas and hence make evidence-based decisions instead of assumptions. This strengthens proactive risk management and improves overall resilience.
4) Single Data Repository
One data repository is the central location of all information concerning risks. It stores assessments, evidence, documentation, and remediation records in one secure location. This enhances accessibility, elimination of duplication and proper reporting within departments.
5) Issues Management Tools
Issues management tools assist in monitoring remediation activities associated with the risks identified. They enable organisations to delegate duties, track progress, and keep a check on outstanding tasks. This holds accountability and maintains risk responses on time.
6) Versatile Reporting
The ability to report in a versatile manner allows organisations to reveal risk information to various stakeholders in a straightforward manner. The reports serve the operational teams with detailed reports and the senior leaders with high level summaries to make strategic decisions. The flexible reporting provides access to risk insight which is relevant and actable.
What Are the Consequences of Not Managing Cyber Security Risks?
The lack of effective cyber security management may subject an organisation to severe and far-reaching damage that impacts finances, operations, reputation and legal status.
1) Financial Loss: Security incidents and breaches without an adequate cyber risk management approach can result in substantial recovery costs, legal expenses, and regulatory penalties. Attacks can also cost organisations revenue that occurs due to downtime.
2) Operational Disruption: Cyber-attacks and unmanaged vulnerabilities can interrupt normal business activities. The work is slowed due to system outages or limited access, and teams cannot continue with critical operations until the problem has been fixed.
3) Damage to Reputation and Trust: A breach or security failure sabotages trust in customers, partners and stakeholders. The loss of trust might be difficult to regain and could impact on the long-term relationships and brand reputation.
4) Regulatory And Legal Consequences: There are numerous laws and standards that demand provable risk management. Unidentified risks and inadequate control of risks may result in regulatory fines and heightened attention of regulators.
5) Data Loss and Exposure: Data can be lost or disclosed to untrusted individuals, leading to additional legal consequences and affecting people whose data is affected.
Efficient management of cyber risks assists organisations in projecting potential threats, prioritising response, and lowering the probability and consequences of such adverse effects.
Understand how to safeguard against Cyberattacks with Cyber Security Risk Management course – Sign Up!
Best Practices for Managing Cyber Security Risks
Risks and threats online have grown considerably over the last few years. The best practices highlighted below can assist organisations in handling and minimising cyber security risks:
1) Understand The IT Environment and Assets: Leadership should be able to know all IT assets, such as servers, systems, hardware, and software. By understanding what they possess and its utilisation, organisations make effective decisions to secure networks, data and infrastructure.
2) Develop A Strong Cyber Security Risk Management Strategy: Organisations are expected to develop and maintain a well-organised cyber security policy following comprehensive risk-assessments. This involves establishing the risk tolerance levels and instilling clear security practices into the training process and the daily operation of employees.
3) Embed Cyber Security into Organisational Culture: The company should incorporate cyber security into its values and daily behaviour. Once employees see their part in the information protection, secure practices become the standard practice and boost the resilience in general.
4) Implement Strict Security Protocols: Effective security controls and monitoring help in identifying and fighting possible cyber threats. An IT team that monitors and has well-established procedures helps in responding promptly and protecting important systems.
Boost your cybersecurity career with our expert-led Malware Analysis Course – Register Now!
What Will You Gain from Undertaking the Cyber Security Risk Management Process?
1) The role of IT Security Risk Management is vital. It forms the basis on which the company can focus on protecting its data, networks, and IT infrastructures. A robust IT Security strategy can help improve the organisation's security posture and identify the necessary improvements further to strengthen the security of the data and such systems. The following points show some of the main benefits of managing Cyber Security Risks.Timely Identification and Mitigation of Risks - One of the critical benefits of the IT Security Risk Management process is that it helps in the timely identification and mitigation of Cyber Security Risks. The IT team should be able to recognise the threats on time to manage the cyber risks effectively. To safeguard against cyber threats, proactiveness is very important. The company has to identify the threat and implement its solutions before the risk becomes an issue. A firm can achieve this proactiveness with properly developed Cyber Risk Management plans.
2) Reducing the Vulnerabilities - Another way the IT Security Risk Management processes can help an organisation is by reducing vulnerabilities. Fixing the systems after an attack has taken place is very difficult. This exposes the company to market forces and negatively impacts its image and performance. With such processes, the company can reduce its vulnerabilities by eliminating weak areas and identifying potential threats before they cause any damage.
3) Ensuring Compliance - Laws and regulations, including Cyber Security Laws and the General Data Protection Regulation (GDPR) of the European Union (EU), have established various policies that guide companies in managing their data and IT infrastructure. Compliance with such regulations is essential; otherwise, the government and agencies may impose severe penalties on the company. Additionally, IT Security Risk Management plans play a crucial role in ensuring that the company adheres to the regulations set by the government.
Conclusion
Cyber Security has become an essential part of business operations. It enhances the company's security position and provides a way to prevent cyberattacks on its data and networks. The role of IT Security has evolved as organisations use several methods and approaches to secure data and systems. We hope that this blog helps you understand the processes used by companies to manage their Cyber Security better and reduce the overall risks and threats. As you prepare for roles in this area, studying Risk Management Interview Questions will give you the tools to better understand how risk management intersects with cybersecurity practices.
Secure your data! Download the Cyber Security ISO 27001 PDF Guide for complete protection.
Frequently Asked Questions
What Are the Key Components of Cyber Security Risk Management?

Key components include identifying and assessing risks, establishing controls and mitigation plans, and monitoring risk over time to ensure ongoing protection and improvement. These steps help organisations understand their threat landscape, decide how to reduce threats, and track how well risk responses are working.
What Are Some Common Cyber Security Risks That Organisations Face?

Common cyber security risks include malware and ransomware attacks, phishing and social engineering, and unauthorised access or data breaches. These threats exploit system vulnerabilities and human error, potentially causing financial loss, disruption, and reputational damage.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Courses, including Cyber Security Awareness, Fraud Analytics Training, and Malware Analysis Training. These courses cater to different skill levels, providing comprehensive insights into Replay Attack.
Our IT Security & Data Protection Blogs cover a range of topics related to Cyber Security, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Risk Management skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Certified Cyber Security Professional (CCS-PRO)
Certified Cyber Security Professional (CCS-PRO)
Fri 26th Jun 2026
Fri 4th Sep 2026
Fri 23rd Oct 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


