We may not have the course you’re looking for. If you enquire or give us a call on + 1-866 272 8822 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Are you aspiring to kickstart your career with CISM certification but don’t know where to start? Don't worry—we're here to help! The Certified Information Security Manager (CISM) certification is a globally recognised credential for professionals looking to become Information Security Managers, among other prestigious roles in the domain. If we analyse the data, the ISACA report says that CISM-certified professionals enjoy a 42% higher pay hike after their certification. Join us in this captivating blog, where we explore and cover step-by-step and expert tips on how to become CISM Certified through this prestigious certification and upgrade your professional credibility.
Table of Contents
1) What is CISM
2) What is the Steps to Become CISM Certified?
3) CISM Requirements
4) Benefits of CISM Certification
5) How to Maintain Your CISM Certification?
6) Conclusion
What is CISM?
The CISM is a globally recognised certification offered by the ISACA for professionals looking to advance their careers as Certified Information Security Managers. The prestigious certification not only enhances your career prospects but also helps you attain lucrative packages in the industry.
Moreover, with the rise of cybersecurity concerns, the CISM-certified professionals became among the most-sought after career choices today.
What Are the Steps to Become CISM Certified?
Becoming CISM Certified involves several steps. By incorporating these steps, you can demonstrate your expertise in Information Security Management and become Certified in CISM:
Pass the exam
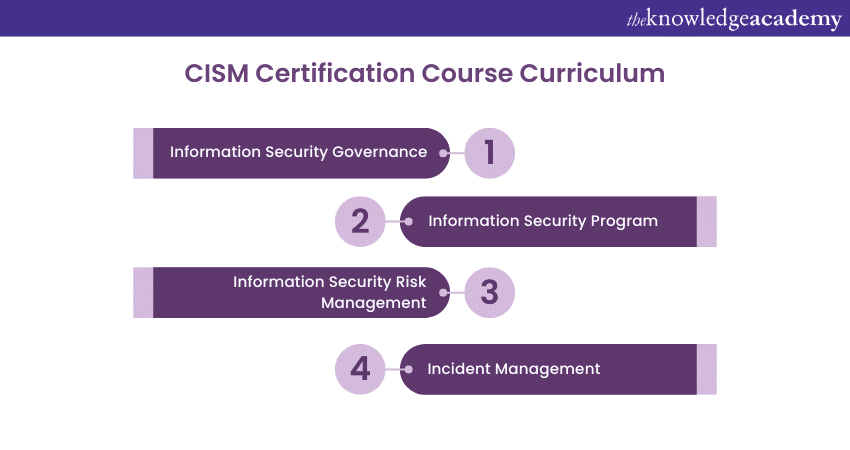
Passing the exam is one of the fundamental requirements for acquiring the CISM Certification. The CISM exam includes four key domains which include:
a) Information Security Governance
b) Information Risk Management
c) Information Security Program
d) Incident Management
2) Involve in the CPE Program
Continuing Professional Education (CPE) refers to continuous professional development required to remain certified and relevant to the field. It is a process that helps promote ongoing professional growth and development among CISM-certified professionals. It helps in expanding the skillset of CISM holders. CPE aligns with the CISM job practice domains, increasing a professional’s relevance in the field of Information Security Management. The benefits of CPE include:
a) Enhances competence of CISM Certified individuals
b) Provides opportunities for networking and collaboration
c) Ensures the validity of the certification
d) Reinforcement of ethical conduct
e) Professional growth and development
f) Improves relevance in the industry
In addition, annual maintenance costs and a minimum of 120 CPE hours earned within the last three years are required. To meet ISACA requirements, you must complete at least 20 hours each.
Reinforcement of Ethical Conduct
To get a CISM Certification, it is essential to comply with the professional ethics code, which will help in shaping your personal and professional conduct. These include:
a) To encourage and facilitate the adoption of suitable standards and procedures for effective governance and management of enterprise information systems and technologies. This includes promoting compliance with audit, control, security, and risk management practices.
b) To Execute their responsibilities with impartiality, thoroughness, and professionalism, adhering to established professional standards.
c) To get a CISM Certification, it is essential to comply with the professional ethics code, which will help in shaping your personal and professional conduct. These include:
d) To Safeguard the privacy and confidentiality of information acquired during their work unless legal authorities mandate disclosure. They must refrain from exploiting such information for personal gain or sharing it with other unauthorised parties.
e) To Sustain and enhance their competence in their respective fields, engaging only in activities for which they possess the necessary skills, knowledge, and proficiency.
f) To Communicate the outcomes of their work to relevant parties, ensuring full disclosure of all significant facts that may impact the accuracy of the reported results.
g) To support stakeholders' ongoing professional education, empowering them to comprehend the governance and management of enterprise information systems and technologies. This encompasses fostering an understanding of audit, control, security, and risk management aspects.
Master Information Security Governance with our comprehensive CISM Certified Information Security Manager Training!
Work Experience
CISM Certification requires expertise in information security management, governance, risk management, program development, and incident management.
Some qualifications, such as up to two years of experience, can be replaced with certain professional certificates or relevant educational credentials. Among those, CISM Certification requires more than just having the necessary job experience. To keep your Certification intact, you must also pass the CISM test, adhere to the Code of Professional Ethics, and fulfil the CPE requirements. Evaluating if CISM Certification is Worth it depends on your career aspirations and industry requirements.
Submit CISM Application to ISACA
The conclusive phase involves the submission of a Certified Information Security Manager (CISM) Certification application. This step becomes possible only after passing the CISM exam and gaining the necessary professional work experience.
CISM Requirements
It is globally recognised and focuses on managing and governing enterprise information security programs with a managerial approach to risk management, governance, and incident response. Below are described some of the requirements of CISM.
1) Offered by ISACA: Designed for professionals aiming to advance in information security management.
2) Global Recognition: CISM credential is known for its comprehensive focus on managing and governing enterprise information security programs.
3) Managerial Approach: Emphasises risk management, governance, and incident response.
4) Certification Requirements:
a) Pass the CISM exam covering four key domains: Information Security Governance, Information Risk Management, Information Security Program Development and Management, and Information Security Incident Management.
b) Minimum of five years of work experience in information security management.
c) At least three years of experience in at least three of the four CISM domains.
d) Experience substitutions or waivers, possibly with other certifications or a degree in information security.
5) Exam Details:
a) Evaluate the ability to apply security principles and manage security programs.
b) Offered globally at various testing centres throughout the year.
c) Exam costs range from £439 to £581, depending on ISACA membership status.
6) Maintenance:
a) Continuous professional education.
b) Adherence to the ISACA Code of Professional Ethics.
c) Compliance with CISM continuing education requirements.
Benefits of CISM Certification
As you are now aware of the topic of How to Become CISM Certified, it is time to explore some of its crucial benefits. These benefits are described as follows:

1) Integration Into an Exclusive Community: A CISM Certification places you in a prestigious group of top-tier information security professionals. This affiliation acknowledges your expertise and provides valuable networking opportunities within this elite circle.
2) Demonstration of Commitment: Obtaining the CISM certification demonstrates your commitment to a career in information security. After candidates have attempted the exam and earned the CISM Certification, they must still maintain it by staying updated with the latest security practices and regularly reviewing a CISM Cheat Sheet to ensure continued compliance and expertise.
3) Expanded Career Opportunities: Earning a CISM certification forms a key role in broadening your job opportunities. Employers typically value this credential higher and actively seek certified professionals to enhance their information security teams. This recognition opens a wider range of potential career paths, making the Information Security Manager as a most sought-after candidate in the job market.
4) Enhanced Earning Potential: You could boost your earning potential and look into new career prospects with a CISM certification. Employers frequently pay greater salaries to individuals who possess this esteemed certificate because they recognise the competence and worth of these qualified experts.
5) Global Recognition: The globally recognized CISM certification improves your marketability and provides you with more mobility in the rapidly growing information security sector. Furthermore, it is flexible and a valuable tool for your successful career, allowing you to seek opportunities in many sectors and geographical areas.
Keen on establishing a career in CISM?, refer to our blog on CISM Interview Questions.
Job Potential
A Certified Information Security Manager (CISM) credential offers up a world of options in the information security profession and greatly increases one's work prospects. Professionals with the CISM certification can succeed in the following fields:
a) Information Security Manager: They oversee and manage the information security program of an organisation, ensuring the optimum sensitive data protection and regulation compliance.
b) Risk Management Specialist: They are responsible to Identify, assess, and mitigate risks to an organisation’s information assets; therefore, form a key role in developing strategies to manage and reduce potential threats.
c) Security Consultant: They provide expert advice and solutions to organisations on improving their information security posture and address specific security challenges.
d) IT Auditor: They conduct audits to evaluate the effectiveness of an organisation’s information security controls and ensure compliance with industry standards and regulations.
e) Chief Information Security Officer (CISO): They primarily lead the information security strategy and operations at an executive level, aligning security initiatives with business goals.
f) Compliance Manager: They ensure that the organisation adheres to relevant laws, regulations, and industry standards relevant to information security.
g) Incident Response Manager: They coordinate and manage the security incident responses, minimise impact and prevent future occurrences.
Salary Outlook
Certified Information Security Manager (CISM) professionals can expect a salary range which are dependent upon several factors such as experience, industry, location, and organisational size. Below we have given the salary structure for two prominent roles based on the experience and skillset.
a) Entry-Level CISM Certified Individuals: They can earn anywhere between £40,000 and £60,000 annually.
b) Mid-Level Professionals: These professionals could command salaries in the range of £60,000 to £80,000 per year.
Ready to become CISM certified? Grab the CISM Certified Information Security Manager Study Guide today!
How to Maintain Your CISM Certification?
Continued and increased dedication to professional growth and observance of ISACA guidelines are necessary to keep your CISM certification current. Below listed are some of the steps to maintain your CISM Certification:
1) Earn and Report CPE Credits: In order to keep your CISM certification active, you must earn and report Continuing Professional Education (CPE) credits. Specifically, you need to accumulate a minimum of 120 CPE hours every three years, with at least 20 hours earned each year. You can obtain these credits through various activities such as attending relevant conferences, participating in webinars, taking additional courses, or engaging in other professional development opportunities related to information security management.
2) Adhere to the ISACA Code of Professional Ethics: Certified professionals must adhere to the ISACA Code of Professional Ethics and the CISM Continuing Education Policy. This includes demonstrating ongoing competency in the CISM domains and adhering to ethical practices in the information security field. Maintaining ethical standards is essential, as it impacts the credibility and integrity of the certification. By doing so, professionals ensure they align with the values and principles set by ISACA, as outlined in the CISM PDF.
3) Pay the Annual Maintenance Fee: Another important aspect of maintaining your CISM certification is paying the annual maintenance fee. This fee supports the administration of the certification program and ensures that your certification status remains current. The fee varies based on your membership status with ISACA; members generally pay a reduced rate compared to non-members.
Get ahead in your CISM journey with our recommended CISM Books!
Conclusion
We hope this blog has enumerated a detailed understanding of How to Become CISM Certified or how to acquire the CISM certification. Earning the CISM or CRISC certification can be a turning point for your career. It opens a diverse array of opportunities for exciting IT management roles that are highly sought after by businesses. This achievement enhances your professional reputation. It opens the door to greater benefits, bonuses, and pay. It also deepens your understanding of security systems management, providing you a competitive edge in the field.
Advance in Information Security Management with our expert-led CISM Training!
Frequently Asked Questions
What Competitive Advantages Do Professionals Gain by Obtaining CISM Certification?

The certification recognises professionals' expertise in risk management, governance, and strategic alignment of security with business objectives. Because of their diverse skill set, CISM holders frequently hold leadership positions, improve job prospects, and command higher salaries.
What Strategies or Advice Can Facilitate a Smoother Journey for Individuals Aiming to Become CISM Certified?

Aspiring individuals should prioritise structured study plans to enhance the path towards CISM certification, leveraging reputable resources. Additionally, they should avail practical experience in information security roles and stay abreast of industry trends and updates.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various CISM Courses, including the CISM Certified Information Security Manager, and BCS CISMP (Certificate in Information Security Management Principles) These courses cater to different skill levels, providing comprehensive insights into 25+ Chief Information Security Officer Interview Questions & Answers.
Our IT Security & Data Protection Blogs covers a range of topics related to CISA Training, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Data Protection skills, The Knowledge Academy's diverse courses and informative blogs have you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 CISM Certified Information Security Manager
CISM Certified Information Security Manager
Mon 22nd Jun 2026
Mon 19th Oct 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


