We may not have the course you’re looking for. If you enquire or give us a call on +44 1344 203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Imagine never updating your smartphone, apps freeze, bugs pile up, and hackers slip in. Soon, the device you rely on becomes slow and unsafe. Vulnerability Management is the “update all” button for organisations, keeping systems patched, secure, and ready to perform.
In this blog, we’ll cover everything you need to know about Vulnerability Management, including what it is, why it’s important, how it works, and its lifecycle. We’ll also explore its key components, automation, the risks of inadequate management, and the advantages of a strong approach.
Table of Contents
1) What is Vulnerability Management?
2) Why is Vulnerability Management Important?
3) How Vulnerability Management Works?
4) The Vulnerability Management Lifecycle
5) Components of Vulnerability Management
6) Vulnerability Management Automation
7) Risks of Inadequate Vulnerability Management
8) Advantages of a Strong Vulnerability Management
9) Conclusion
What is Vulnerability Management?
Vulnerability Management is the process of finding, checking, fixing, and reporting security problems in your systems. These problems can be things like old software that needs updates or cloud settings that are not safe.
It is a regular cycle of scanning for issues, checking how risky they are, fixing them, and keeping watch all the time. By adding Vulnerability Management to their security plan, organisations can lower risks, follow rules, and keep the trust of customers and partners while reducing the potential for attacks.
Why is Vulnerability Management Important?
Every organisation today relies heavily on technology. From emails and websites to financial systems and customer data, everything is digital. With this dependence comes risk. Hackers are always looking for easy targets.
If you do not manage vulnerabilities, attackers can use them to:
Break into your systems.
Steal important information.
Damage your company’s reputation.
Stop your services, leading to money loss.
A good Vulnerability Management system lowers these risks. It protects sensitive data, helps meet compliance rules, and builds trust with customers and partners.
How Vulnerability Management Works?
Vulnerability Management works by scanning systems for weaknesses, assessing their risk level, addressing the most critical issues, and monitoring for new threats. This proactive approach helps prevent security breaches before they happen.
Let’s look at each step in more detail:
Asset Discovery: Find all devices, apps, and systems
Asset Prioritisation: Pick which ones matter most
Risk Assessment: Check how big the problem is
Reporting: Write down what you found
Remediation: Fix the problems
Monitoring: Keep checking for new problems
Learn cloud security best practices and controls to enhance organisational safety. Join our ISO 27017 Training now!
The Vulnerability Management Lifecycle
The Vulnerability Management lifecycle consists of six main phases. Organisations looking to build or enhance their security programme can follow these structured steps:
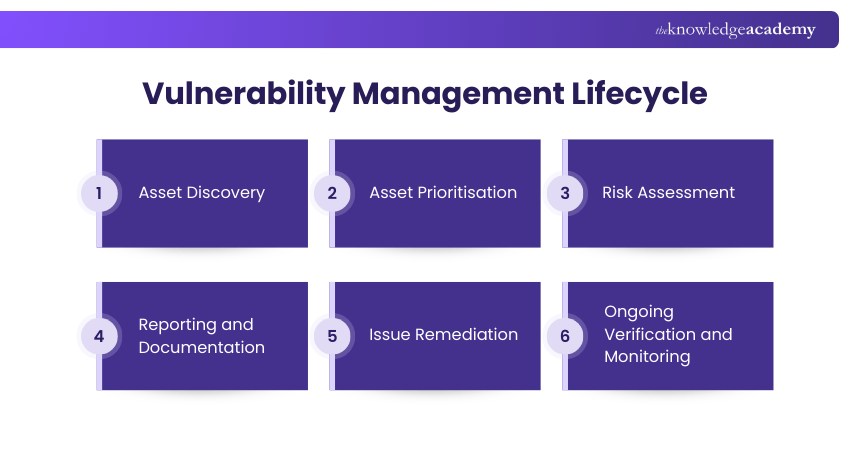
Phase 1: Asset Discovery
Create a complete inventory of all assets within your network. Utilise regular automated scans to detect weaknesses and establish a security baseline. This helps you stay proactive against emerging threats.
Phase 2: Asset Prioritisation
Assign a value to each asset based on its importance to business operations. This helps you focus on protecting the most critical systems and allocate resources more effectively.
Phase 3: Risk Assessment
Assess your assets to understand the risks linked to each one. This step helps you decide which vulnerabilities should be fixed first, based on criticality, threat level, and potential impact.
Phase 4: Reporting and Documentation
Record your findings clearly. Report on which vulnerabilities exist, explain the level of risk, and document the security plan you will follow to address them.
Phase 5: Issue Remediation
Fix the vulnerabilities, starting with the ones that bring the highest risk to your business. This could include applying patches, updates, or other changes.
Phase 6: Ongoing Verification and Monitoring
Finally, perform regular audits and checks to confirm that vulnerabilities have been fixed. Continuous monitoring ensures new threats are caught quickly.
Learn best practices for password security, safe browsing, and data protection. Join our Cyber Security Awareness Course now!
Components of Vulnerability Management
Effective Vulnerability Management has many connected parts that work together to keep an organisation safe. These are the most important components of Vulnerability Management:
1) Asset Visibility and Context
Know what you are protecting. Keep a clear list of all devices, apps, and systems, how they are set up, and how they connect. This helps you spot gaps and understand the impact of problems.
2) Scanning and Analysing Vulnerabilities
Do regular scans on your systems, cloud, office, or mixed. Scans show weak points and give you data to check risks and defend against threats.
3) Risk-based Prioritisation
Not all problems are the same. Some are small, some are very dangerous. Rank them by how serious they are and fix the most harmful ones first.
4) Effective Remediation Plans
Have clear steps to fix issues. This can include patches, updates, or changing settings. Sometimes extra controls are added to reduce risks without stopping work.
5) Continuous Monitoring and Feedback Mechanisms
New threats appear all the time. Keep checking for them. Use feedback to improve your methods and stay ready.
6) Integrated Automation Capabilities
Automation makes the job faster. Tools can scan, rank, and fix issues automatically, and even connect to team workflows for easy tracking.
7) Support for Policy and Regulatory Compliance
Strong Vulnerability Management also helps follow industry and legal rules, keeping your business safe from fines or penalties.
8) Threat Intelligence
Stay updated on new attack methods. Threat intelligence tools give real-time knowledge so you can fix weaknesses before hackers try to use their potential entry points.
Acquire skills in deploying firewalls to control network traffic effectively. Join our Introduction to System and Network Security Training now!
Vulnerability Management Automation
A Vulnerability Management (VM) system can make the job easier by using automation. It helps find, check, and fix security problems across all systems. These tools use scanners and agents to list devices, spot weaknesses, and show how risky they are.
1) Advanced Vulnerability Testing
VM automation can work with other security methods like penetration testing and Breach-and-Attack Simulation (BAS). Penetration testing acts like a fake hacker attack to see how real the risk is. BAS tools test defences often and automatically, showing weak points and checking if protections are strong enough.
2) Cross-functional Team Collaboration
Automation also supports collaboration between teams. Red teams simulate attacks, blue teams defend systems, and purple teams coordinate both. Automated data enables these teams to share insights, align their efforts, and improve defences more effectively.
3) Managing Exposure Proactively
Automated VM should be part of a bigger plan. By linking with attack surface management (ASM) tools, it can watch all company systems, even hidden or new ones in the cloud. This makes sure scans always cover the right assets.
Risks of Inadequate Vulnerability Management
If Vulnerability Management is weak or missing, the risks are high:

Data Loss: Hackers can steal important information if problems are not fixed
Fines: Companies may have to pay money if they don’t follow the rules
Missed Threats: Too many small alerts can hide the big, dangerous ones
No Clear View: Without proper checks, companies may miss their weak points
Advantages of a Strong Vulnerability Management
Strong Vulnerability Management offers many benefits:
Stronger Safety: Problems are fixed before hackers can use them
Easy Work: Security fits smoothly into daily tasks
Clear View: You can see all weaknesses across systems in real time
Team Support: Both IT and developers get tools to protect systems
Rule Compliance: Helps the company follow laws and industry rules
Conclusion
Vulnerability Management is more than just fixing system flaws; it is an ongoing shield against cyber risks. By identifying weaknesses early, prioritising fixes, and monitoring continuously, organisations can stay resilient and secure. Strong practices not only protect sensitive data but also build customer trust and ensure compliance. With the right approach, managing vulnerabilities becomes a vital part of long-term business safety and success.
Learn to secure critical data and assets through effective security measures. Join our Certified Cyber Security Professional (CCS-PRO) Training now!
Frequently Asked Questions
What are the Four Main Types of Security Vulnerabilities?

The four main types of Security Vulnerabilities are:
1) Network Vulnerabilities: Weaknesses in networks, like open ports
2) Operating System Vulnerabilities: Bugs or flaws in OS software
3) Application Vulnerabilities: Problems in apps or websites
4) Human Vulnerabilities: Mistakes by people, such as weak passwords
What are the 6 P's of Security?

The 6 P’s of security are a simple way to remember key points:
1) Patches: Always update systems
2) Passwords: Use strong and unique ones
3) Policies: Follow clear security rules
4) People: Train staff in safety
5) Processes: Have proper security steps in place
6) Physical Security: Protect buildings and devices
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various ISO 27017 Training, including the ISO 27017 Information Security Controls for Cloud Services. This course caters to different skill levels, providing comprehensive insights into Information Security Risk Management.
Our IT Security & Data Protection Blogs cover a range of topics related to Vulnerability Management, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your IT Security & Data Protection skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 ISO 27017 Information Security Controls for Cloud Services
ISO 27017 Information Security Controls for Cloud Services
Thu 13th Aug 2026
Thu 26th Nov 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


