Who Should Attend this CISM Certified Information Security Manager Course?
The CISM Course focuses on developing a professional’s expertise in managing Information Security systems and practices. This CISM Course can be beneficial for professionals, including:
- Information Security Managers
- Internal Auditors
- Risk Management Specialists
- Compliance Officers
- Security Analysts
- IT Consultants
- Data Protection Officers
Prerequisites of the CISM Certified Information Security Manager Course
There are no formal prerequisites for this CISM Certified Information Security Manager Course. However, a basic understanding of Information Security and experience in job roles related to it can be beneficial for delegates.
CISM Certified Information Security Manager Course Overview
The CISM Training develops the skills required to manage and govern enterprise information security effectively. It covers governance, risk management, security program development, and incident response within a structured framework.
This training enhances professional capability by improving readiness to manage security risks and respond to incidents. Delegates gain practical insight to strengthen organizational resilience, compliance, and protection of critical information assets.
This 4-Day course offered by The Knowledge Academy helps delegates apply CISM principles with confidence in real-world cases. Through practical learning, delegates build the competence to lead security initiatives and support informed decision-making across the organization.
CISM Certified Information Security Manager Course Objectives
- To understand the core principles of Information Security governance
- To learn to develop and manage an Information Security aligned with business objectives
- To master risk management processes to safeguard an organization's assets
- To acquire skills for incident response and recovery
- To gain the ability to establish and maintain Information Security policies and procedures
- To develop the competence to align Information Security with regulatory and compliance requirements
- To learn how to manage and govern Information Security teams effectively
- To prepare for the CISM exam and enhance their career prospects
After completing this CISM Training, delegates will gain strong practical knowledge of information security management principles. The training enhances professional capability, supports career progression, and equips delegates with skills valued across industries managing information security functions.
Skills You’ll Gain from CISM Training
CISM Training equips learners and professionals with the advanced skills required to govern, manage, and strengthen an organization's information security function. Delegates can enhance skills such as
- Information Security Governance: Professionals learn to design, implement, and maintain governance frameworks that align security initiatives with organizational objectives.
- Risk Management: Gain the ability to identify, analyze and prioritise information risks, implement mitigation strategies, and monitor ongoing risk exposure.
- Security Development: Build skills in creating, managing, and measuring a comprehensive information security programme that supports business needs.
- Business Continuity and Disaster Recovery: Learners understand how to create continuity plans, support resilience strategies, and ensure the organization can continue operations after a major security incident.
- Threat and Vulnerability Management: Develop the capability to identify vulnerabilities, evaluate emerging threats, and support the implementation of controls to reduce security risks.
- Policy, Compliance, and Leadership: Professionals gain expertise in establishing security policies, supporting regulatory compliance, and leading security initiatives across teams and departments.
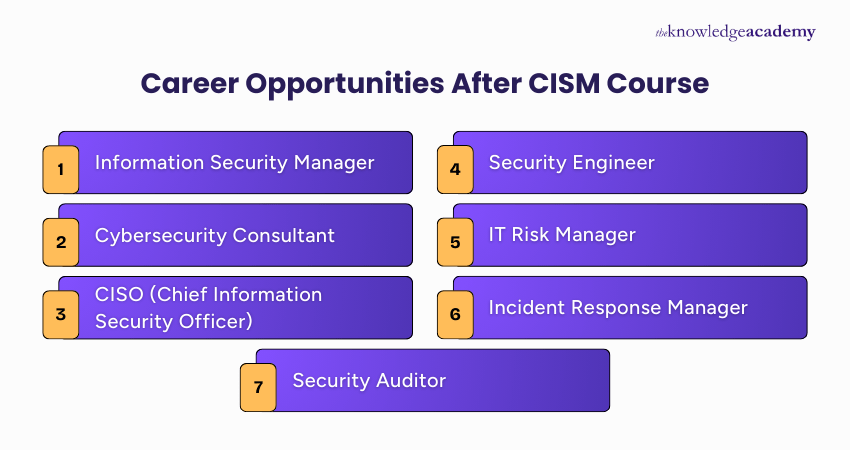
Career Opportunities After CISM Course
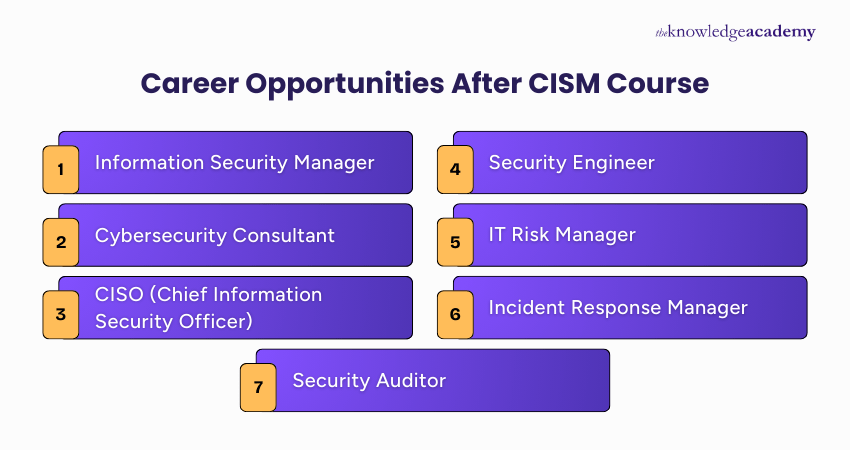
Completing CISM Course enables professionals to move into advanced leadership, governance, and management roles within cybersecurity and information security. Key career paths include:
- Information Security Manager: Oversee security governance, develop security programmes and manage compliance across the organization.
- Cybersecurity Consultant: Evaluate organizational security maturity, identify risks, propose governance-focused enhancements, and help implement best-practice security measures.
- CISO (Chief Information Security Officer): Lead enterprise-wide security strategy, manage security governance, and oversee teams responsible for risk, compliance, and programme development.
- Security Engineer: Implement security controls, resolve vulnerabilities, and ensure technical safeguards support organizational governance and compliance.
- IT Risk Manager: Identify and evaluate organizational risks, develop mitigation measures, and ensure risk management practices support business objectives.
- Incident Response Manager: Coordinate detection, analysis and response to security incidents, ensuring quick recovery and reduced impact.
- Security Auditor: Assess security controls, evaluate compliance, and ensure organizational policies and procedures are effective.























 If you miss out, enquire to get
yourself
on the waiting list for the next day!
If you miss out, enquire to get
yourself
on the waiting list for the next day!


















 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


