We may not have the course you’re looking for. If you enquire or give us a call on +31 208081674 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Data security has become essential because our world depends on digital information and uninterrupted online access. Organisations need to establish security measures that protect confidential data while demonstrating compliance with acknowledged security frameworks.
Businesses need to know about ISO 27001 Compliance because it helps them protect their systems while managing risks and building trust with their stakeholders. In this blog, we will explore what it involves and why it matters for modern organisations.
Table of Contents
1) What is ISO 27001 Compliance?
2) Why is ISO 27001 Compliance Required?
3) What are the Three Main Principles of ISO 27001?
4) ISO 27001 Compliance Standards
5) Clause of ISO 27001
6) ISO 27001 Compliance Checklist
7) ISO 27001 Implementation Process
8) Benefits of ISO 27001 Compliance
9) What are the ISO 27001 Audit Controls?
10) How Much Does ISO 27001 Implementation Cost?
11) Who Needs ISO 27001 Compliance?
12) Conclusion
What is ISO 27001 Compliance?
ISO 27001 Compliance refers to adhering to the international standard for Information Security Management Systems. It delivers a systematic approach to managing sensitive company information, ensuring its confidentiality, integrity, and availability.
Organisations achieving ISO 27001 Certification demonstrate their commitment to protecting data through risk management, security controls, and continuous improvement practices. Compliance helps build stakeholder trust and can enhance a business’s reputation, as it shows a proactive stance towards safeguarding information against potential threats and breaches.
Why is ISO 27001 Compliance Required?
Following ISO/IEC 27001 can strengthen your security and build trust with stakeholders by proving your commitment to data protection. While not mandatory, it’s highly valuable for any organisation looking to ensure strong security practices. Consider the following:
1) Business Growth and Continuity
a) Managing an organisation is demanding and leaves little room for unexpected security incidents.
b) Security breaches can spread quickly and have a domino effect, making multiple systems vulnerable.
c) Compliance with ISO 27001 helps detect vulnerabilities, analyse risks and apply corrective measures for smooth operations.
d) It requires ongoing evaluation of threats so teams can prevent the issues before they cause any harm.
ISO 27001 mandates the planning, implementation and maintenance of security processes to protect against disasters.
2) Better Reputation
a) Data is a crucial asset, and businesses prefer partners who prioritise security.
b) Demonstrating strong security measures increases their confidence in your business.
c) The ISO 27001 Certification sets you apart from competitors who lack proven security standards.
d) Many companies prefer working with ISO 27001-certified partners for data protection assurance
3) Coordinated Controls
a) ISO 27001 helps you unify various security controls that may otherwise be implemented separately.
b) It helps you detect, block, mitigate and respond to security risks in a structured way.
c) Unlike traditional controls, an ISMS protects both digital and physical assets, including paper documents.
d) ISO 27001 requires a full suite of security measures to safeguard data in any format.
e) It provides a centralised approach to managing and improving security across an organisation.
Gain expertise in auditing, ensure top-notch data security, and advance your career with our ISO 27001 Lead Auditor Course - Join today!
What are the Three Main Principles of ISO 27001?
The three key principles of ISO 27001 are confidentiality, integrity, and availability of data.
1) Confidentiality: Data must be kept private, and only authorised individuals must be allowed to access it.
2) Integrity: Data must not be altered, tampered with, or damaged.
3) Availability: Only authorised people must be able to access data.
ISO 27001 Compliance Standards
As mentioned above, the primary goal of the ISO 27001 standard is to guide organisations towards creating, implementing and enforcing an ISMS. However, to achieve ISO 27001 Compliance, an organisation must document the steps to develop the ISMS. The main documentation includes:
1) Defined Scope of the ISMS
2) Information Security Risk Assessment Process and Plan
3) Information Security Policy
4) Information Security Objectives
5) Evidence for Competence of People Working in Information Security
6) ISMS Internal Audit Programme and Results of Audits Conducted
7) Outcomes of Information Security Risk Assessment and Treatment
8) Proof of Nonconformities Identified and Corrective Action Results
9) Evidence of Leadership Reviews of the ISMS
Clause of ISO 27001
ISO 27001 Clauses 4 to 10 outline the core ISMS requirements, covering organisational context, leadership commitment, planning, support, operation, performance evaluation, and continual improvement. These policies embed information security into everyday business operations.
Clause 4: Context of the Organisation
This clause requires understanding internal and external factors, stakeholder expectations, and defining the ISMS scope. It ensures security efforts are shaped around real business needs rather than assumptions.
Clause 5: Leadership
Leadership must show commitment, set a clear direction for information security, and assign defined responsibilities. Without active involvement from top management, an ISMS struggles to gain organisational traction.
Clause 6: Planning
This clause focuses on assessing risks, defining treatments, and setting measurable security objectives. It ensures organisations plan proactively instead of reacting to security issues.
Clause 7: Support
Organisations need to provide resources while they need to develop staff skills and create awareness programs, and they need to keep documents safe. The ISMS requires this system to function properly according to its fundamental needs.
Clause 8: Operation
The clause describes two activities which include executing risk treatment plans and running security processes. The system makes sure that security controls get implemented correctly while it supervises all outsourced work activities.
Clause 9: Performance Evaluation
Organisations need to execute monitoring activities together with auditing work and conducting reviews to assess their ISMS system performance. The evaluations assist in finding existing weaknesses while they guarantee that decisions are based on solid proof.
Clause 10: Improvement
The clause demands organisations to fix problems while they need to resolve all non-conformities and proceed with their ISMS system improvements. The system needs to maintain its security practices through all risk changes.
ISO 27001 Compliance Checklist
What’s the key to achieving compliance? There are no shortcuts, but following the ISO 27001 Compliance checklist below can guide you through the process.
a) Take a Holistic Approach: Apply information security practices across all areas of the business to ensure transparency and consistent protection.
b) Perform Regular Audits and Risk Assessments: Carry out audits, gap analysis, and risk assessments to identify weaknesses and close gaps in your ISMS.
c) Maintain Proper Documentation: Keep records of policies, procedures, and security activities so they can be presented to auditors when required.
d) Develop and Review Security Policies: Establish policies that clearly define scope and monitor them regularly to support continual improvement.
e) Engage Senior Management and Stakeholders: Involve leadership and key stakeholders to provide support, accountability, and resources for effective compliance.
Sign up for our course on ISO 27001 Internal Auditor Course and learn how to perform Internal Audits and secure ISMS – Join now!
ISO 27001 Implementation Process
Here are the steps involved in the ISO 27001 implementation process:
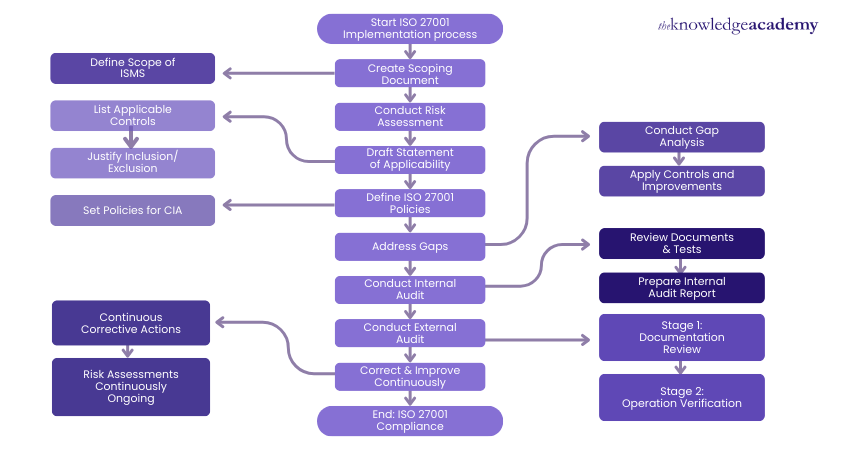
1) Start ISO 27001 Implementation Process
Initiate the Journey: Assemble a project team responsible for the implementation, define roles, and communicate the objectives of obtaining ISO 27001 certification to all relevant stakeholders.
2) Define the Scope of ISMS
Identify Boundaries: Determine which areas of the organisation (e.g., departments, locations, assets) will be included in the Information Security Management System (ISMS) based on business requirements and risk considerations.
3) Create Scoping Document
Document the Scope: Outline the ISMS boundaries, including the types of information and systems covered, as well as applicable legal, regulatory, and contractual obligations that must be adhered to.
4) List Applicable Controls
Identify Relevant Controls: Refer to the controls outlined in Annex A of ISO 27001 and select those that apply to your organisation based on identified risks and operational needs.
5) Justify Inclusion/Exclusion
Provide Rationale: Clearly document the reasons for including or excluding specific controls in the Statement of Applicability. This helps ensure transparency and accountability.
6) Set Policies for Confidentiality, Integrity, and Availability (CIA)
Define Security Policies: Establish clear policies that address how the organisation will ensure the confidentiality, integrity, and availability of its information assets.
7) Conduct Risk Assessment
Evaluate Risks: Identify assets, threats, and vulnerabilities systematically. Analyse the potential impact and likelihood of each risk to prioritise your approach to risk management.
8) Draft Statement of Applicability
Prepare a Foundational Document: This statement should outline which controls are implemented, their current status, and justify their application, serving as a key document for the certification process.
9) Conduct Gap Analysis
Assess Current Practices: Compare existing information security practices against ISO 27001 requirements. Identify gaps in compliance that need to be addressed.
10) Address Gaps
Develop Action Plans: For every identified gap, create an action plan detailing what measures need to be taken, who is responsible, and the timeline for completion.
11) Conduct Internal Audit
Review ISMS Effectiveness: Perform an internal audit to evaluate how well the ISMS is functioning. Identify areas for improvement and document the audit findings and recommendations.
12) Conduct External Audit
Certification Process: Remember to engage an accredited certification body to perform an external audit. They will review your ISMS against ISO 27001 standards to determine readiness for certification.
13) Correct & Improve Continuously
Implement Improvements: Use findings from internal and external audits, along with ongoing assessments, to make necessary improvements to the ISMS.
14) Risk Assessments Continuously Ongoing
Maintain Vigilance: Regularly reassess risks and update your ISMS as necessary. This ensures that the system continues to be effective in managing evolving threats.
15) End: ISO 27001 Compliance
Achieve Certification: Following successful external audits and resolution of any non-conformities, the organisation will be certified to ISO 27001, reflecting its dedication to maintaining high information security standards.
Benefits of ISO 27001 Compliance
ISO 27001 Compliance enhances the general security posture of an organisation because it offers an organised method of information protection. It assists in protecting sensitive information, decreasing the vulnerability to cyber-attacks, and enhancing the capability of detecting and controlling risks in a better way.
It also enhances the trust and business credibility of clients and portrays a strong commitment towards data protection. It can be operational resilience (clear documentation, repeatable processes, and recognised certification can be used and even become a competitive edge when collaborating with clients or partners.
What are the ISO 27001 Audit Controls?
ISO 27001 outlines a set of audit controls that must be included in a compliant ISMS. These include the following:
1) Information Security Policies: This control outlines how security policies must be documented and reviewed as part of the ISMS.
2) Organisation of Information Security: Role responsibilities are important to an ISMS. This control breaks down the security responsibilities across an organisation, ensuring a clear responsibility for each task.
3) Human Resource Security: This control handles how employees are trained on Cyber Security when starting and ending roles within an organisation, including onboarding, offboarding, and changing positions.
4) Asset Management: Data security is one of the primary concerns of ISO 27001. This control focuses on managing security of and access to assets that impact data security, including hardware, software, and databases.
5) Access Control: This control outlines how an organisation manages access to data to protect against unauthorised access to sensitive or valuable data.
6) Cryptography: Encryption is one of the most powerful tools for data protection. Companies should implement Data Encryption whenever possible using strong cryptographic algorithms.
7) Physical & Environmental Security: Encryption is one of the most potent tools for data protection. Companies must implement Data Encryption whenever possible through strong cryptographic algorithms.
8) Compliance: As a component of ISO 27001 Compliance, the organisation should demonstrate full compliance with other mandatory regulations that the organisation is subject to.
9) Operations Security: This control focuses on how the organisation processes and manages data. The organisation should have visibility into and control over data flows within its IT environment.
10) Communications Security: Organisational communication systems (email, videoconferencing, etc.) must encrypt data in transit and have strong access controls.
11) System Acquisition, Development and Maintenance: This control ensures that new systems introduced into an organisation’s environment don't endanger enterprise security and that existing systems are maintained securely.
12) Supplier Relationships: Third-party relationships spark the potential for supply chain attacks. An ISMS must include controls for tracking relationships and managing third-party risk.
13) Information Security Incident Management: The company must have processes to detect and manage security incidents.
14) Information Security Aspects of Business Continuity Management: Besides security incidents, the company must be prepared to manage other events (such as power outages, fires, etc.) that could negatively impact security.
How Much Does ISO 27001 Implementation Cost?
The cost of implementing ISO 27001 Compliance can vary depending on your organisation's size, industry, and current security posture. It also depends on how you choose to become ISO compliant. For instance, hiring an external consultant to perform an ISO 27001 Gap Analysis will be more expensive than using compliance automation software.
Take the first step towards securing your organisation's information with our comprehensive ISO 27001 Foundation Course – Register now!
Conclusion
Achieving ISO 27001 Compliance may seem like a big task, but it ultimately strengthens your organisation and boosts confidence in your security practices. With the right approach, it becomes a smart, empowering step toward a safer future. Stay committed, stay curious, and enjoy the peace of mind that comes with doing security right.
Advance your career with our ISO 27001 Lead Auditor Course. Gain expertise in auditing and ensure top-notch data security. Join today!
Frequently Asked Questions
What is the Difference Between ISO 27001 Compliance and ISO 27001 Certification?

ISO 27001 Compliance means following the standard internally, while ISO 27001 certification is an accredited external audit that formally confirms your ISMS meets all ISO 27001 requirements.
What are the Pros and Cons of ISO 27001?

Here are the pros and cons:
Pros:
a) Enhances data security
b) Builds customer trust
c) Improves compliance
Cons:
a) Can be costly
b) Time-consuming
c) Requires ongoing effort to maintain compliance
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 19 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various ISO 27001 Courses, including the ISO 27001 Lead Auditor Course, ISO 27001 Foundation Course, and ISO 27001 Internal Auditor Course. These courses cater to different skill levels, providing comprehensive insights into ISO 27001 Roles and Responsibilities.
Our IT Security & Data Protection Blogs cover a range of topics related to ISO 27001 Compliance, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your technical skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

Hailey Davis is an ISO compliance expert with over 10 years of experience in audit, quality management systems (QMS), and regulatory compliance. She has worked with various industries, including manufacturing, healthcare, and technology, ensuring organisations achieve and maintain ISO certifications. Hailey’s content provides practical, actionable insights on navigating compliance challenges and improving business processes.
View Detail
Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 ISO 27001 Foundation
ISO 27001 Foundation
Mon 13th Apr 2026
Mon 11th May 2026
Mon 1st Jun 2026
Mon 6th Jul 2026
Mon 3rd Aug 2026
Mon 7th Sep 2026
Mon 5th Oct 2026
Mon 2nd Nov 2026
Mon 7th Dec 2026







 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


