We may not have the course you’re looking for. If you enquire or give us a call on + 1-866 272 8822 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.
Imagine storing all your valuables in a vault but forgetting to lock it. That’s what it feels like when organisations manage data without a proper security system in place. With cyber threats growing smarter every day, businesses need more than good intentions, they need a solid framework to stay protected. That’s where the ISO 27001 Framework comes in. It’s the international gold standard for building a secure information environment.
In this blog, we’ll explore what the ISO 27001 Framework is, why it matters, and how it can help your organisation prevent data breaches, stay compliant, and earn customer trust. Ready to take the guesswork out of Cyber Security? Let’s unlock the secrets of ISO 27001 together.
Table of Contents
1) What is the ISO 27001 Framework?
2) Understanding Information Security Management System (ISMS)
3) Why is ISO 27001 Important?
4) How Does ISO/IEC 27001 Ensure Data Protection?
5) 14 Domains of ISO 27001 Framework
6) ISO/IEC 27001 Compliance Checklist
7) Who Needs ISO 27001?
8) What are the Pillars of ISO 27001?
9) Conclusion
What is the ISO 27001 Framework?
The ISO 27001 Framework is an internationally recognised standard for establishing and maintaining an effective Information Security Management System (ISMS). It offers a systematic approach to safeguarding sensitive company data, ensuring its security, confidentiality, and availability.
This framework enables organisations to identify security risks, implement necessary controls, and continuously monitor and enhance their information security practices. Suitable for businesses of all sizes and industries, it helps build customer trust, comply with regulatory requirements, and mitigate the risk of data breaches.
Understanding Information Security Management System (ISMS)
An Information Security Management System (ISMS) consists of the ISO 27001 Access Control Policy framework, which ensures that an organisation’s vital data and digital systems remain secure by implementing effective security controls and risk management strategies. An ISMS accomplishes this by outlining security procedures, policies, and controls designed to protect data and keep it accessible only to qualified individuals. Utilising an ISO 27001 Information Security Guide can help organisations implement these measures effectively and ensure compliance with industry standards.
An ISMS outlines the technical procedures and tools necessary to protect digital assets, including strategies to keep employees informed about how they can contribute to the organization's security, as detailed in the ISO 27001 Standard PDF.
ISO 27001 Controls
The ISO 27001:2022 standard includes 93 controls, grouped into 4 themes: organisational, people, physical, and technological controls. These address various aspects such as access control, encryption, physical security, and incident management. These controls serve as practical measures that organisations can adopt to safeguard their information.
Each control targets a specific risk or requirement and can be customised to fit the organisation's size, industry, and risk profile. Listed in Annex A of the ISO/IEC 27001:2022 standard, these controls are integral to any effective ISMS.
Why is ISO 27001 Important?
ISO 27001 is important as it offers a proven and internationally recognised method for managing information security risks. It aids businesses in protecting sensitive data, ensuring compliance, and fostering trust with clients, partners, and stakeholders.
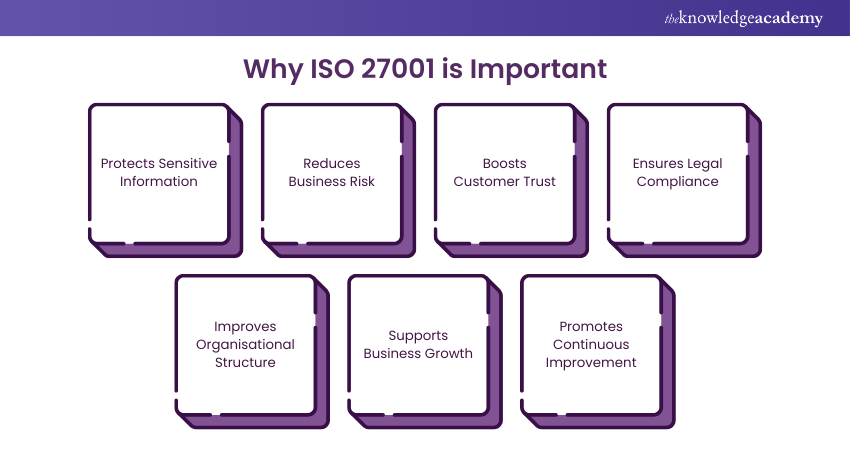
Key Reasons Why ISO 27001 is Important:
a) Protects Sensitive Information: Safeguards data from breaches, leaks, and unauthorised access.
b) Reduces Business Risk: Identifies and mitigates security threats before they escalate.
c) Boosts Customer Trust: Demonstrates a commitment to data security, enhancing credibility with clients.
d) Ensures Legal Compliance: Helps meet regulatory and legal requirements, such as GDPR.
e) Improves Organisational Structure: Promotes better internal processes, accountability, and clear security roles.
f) Supports Business Growth: Opens new business opportunities where ISO 27001 certification is a prerequisite.
g) Promotes Continuous Improvement: Encourages regular monitoring and enhancement of security practices.
Professional who are involved in internal audits in ISMS can benefit from ISO 27001 Internal Auditor Training now – Sign up now!
How Does ISO/IEC 27001 Ensure Data Protection?
ISO 27001 ensures enterprise-level information security by offering companies a set of internationally acclaimed standards that align with each organisation's distinctive structure and function. These guidelines:
1) Establish effective Risk Management procedures for assigning data protection duties across an organisation.
2) Establish specific security objectives so the company can continuously monitor its data protection.
3) Incorporates regular risk analysis assessments to ensure that any changes to the organisation's systems will continue to support its information security.
Secure your organisation's data with ISO 27001 Training. Sign up now to master compliance and Information Security!
14 Domains of the ISO 27001 Framework
The ISO 27001 Statement of Applicability framework consists of 14 domains, each containing a number of controls that specify the requirements for implementing and maintaining an ISMS. The 14 domains are:
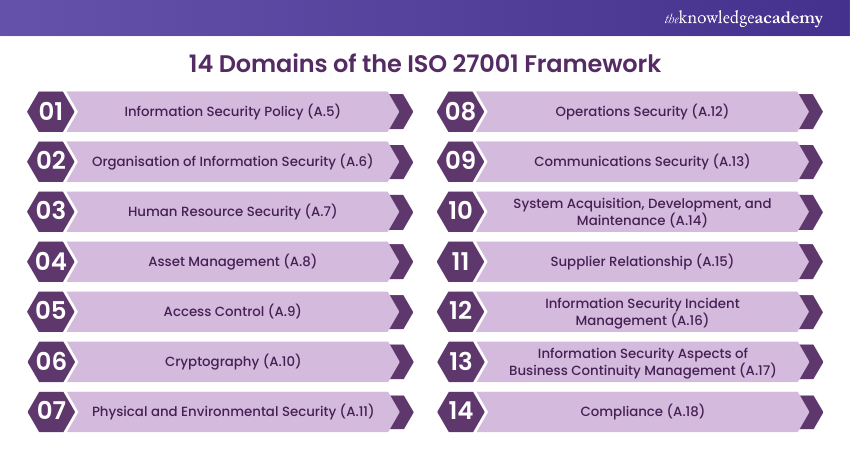
1) Information Security Policy (A.5)
This domain serves as the foundation of ISMS, outlining how an organisation should handle Information Security Policies.
2) Organisation of Information Security (A.6)
This domain defines the organisational structure of Information Security, including the roles and responsibilities of individuals and employees.
3) Human Resource Security (A.7)
This domain covers the security aspect of human resources, including information assets under the control of an individual or employee.
4) Asset Management (A.8)
This domain covers the identification, classification, and control of assets used in Information Security.
5) Access Control (A.9)
The Controls in this domain limit or control access to information assets, including both logical and physical access controls.
6) Cryptography (A.10)
This domain describes the proper use of encryption to protect the confidentiality and integrity of confidential information.
7) Physical and Environmental Security (A.11)
This domain is concerned with the security of physical assets, equipment, and facilities to protect against both human and natural interventions. The implementation of effective ISO 27001 Physical and Environmental Security measures is crucial for safeguarding sensitive information and ensuring the overall integrity of the organization's information security management system.
8) Operations Security (A.12)
This domain describes how the organisation’s operating system, software, and Information Technology (IT) systems should be protected.
9) Communications Security (A.13)
The Controls in this domain are for protecting the Information Security risks related to communication networks, including infrastructure and services.

10) System Acquisition, Development, and Maintenance (A.14)
The Controls in this domain ensure that Information Security is maintained during the upgrading or purchasing of Information Systems.
11) Supplier Relationship (A.15)
This domain explains how third-party security performance should be monitored and ensures that suppliers or partners follow appropriate Information Security Controls.
12) Information Security Incident Management (A.16)
The controls in this domain are related to the management of security incidents.
13) Information Security Aspects of Business Continuity Management (A.17)
This domain describes the measures that must be taken to ensure that business operations are unaffected in the event of any Information Security incidents.
14) Compliance (A.18)
This domain details the framework to prevent legal, statutory, regulatory, and contractual breaches.
Are you looking to lead audits of an ISMS that complies with ISO 27001 standards? Our ISO 27001 Lead Auditor can help you - Sign up now!
ISO/IEC 27001 Compliance Checklist
The ISO/IEC 27001 Compliance Checklist is a practical framework designed to help organisations implement and maintain an effective Information Security Management System. It outlines the essential steps needed to meet ISO 27001 requirements and achieve certification, ensuring your data and systems remain secure.
1) Specify the Scope of Your ISMS
Defining the scope of your ISMS is the first step. This involves identifying the assets, departments, processes, and systems that will be protected under the ISMS. A clear scope ensures focused efforts and avoids unnecessary complexity.
2) Clearly Outline the Risk Assessment Process
Create a structured approach to identifying and evaluating information security risks. This involves determining the likelihood and impact of potential threats to your data. The results will guide the selection of appropriate security controls.
3) Make Sure Executives Set the Tone
Top-level management must actively support and lead the ISMS. Their involvement helps prioritise security, ensures sufficient resources, and reinforces a culture of accountability throughout the organisation.
4) Design an Information Security Policy (ISP)
Develop a comprehensive security policy that outlines your organisation’s approach to information protection. The ISP should reflect your security goals, define responsibilities, and serve as a framework for all related processes.
5) Write Out Your Statement of Applicability (SoA)
The SoA lists which of the ISO 27001 controls are applicable to your organisation and explains why. It also includes reasons for excluding any controls and links them to your risk assessment and treatment plan.
6) Create Your Risk Management Strategy
Based on your risk assessment, outline how identified risks will be treated. This includes selecting controls, assigning responsibilities, and setting timelines. Regular updates to this strategy are key to the ongoing effectiveness of your ISMS.
Who Needs ISO 27001?
ISO 27001 is ideal for any organisation that handles sensitive information, including IT companies, financial institutions, healthcare providers, and government bodies. It helps protect data, meet legal requirements, and build trust with clients and stakeholders.
What are the Pillars of ISO 27001?
The pillars of ISO 27001 are Confidentiality, Integrity, and Availability - often referred to as the CIA triad. These principles ensure that data is protected from unauthorised access, remains accurate, and is accessible when needed.
Conclusion
The ISO 27001 Framework offers a reliable, structured approach to protecting sensitive information. It helps organisations manage risks, meet legal obligations, and build trust with clients and partners. Whether you're a small business or a large enterprise, ISO 27001 strengthens your security posture and promotes a lasting culture of information security and continuous improvement. Think of it as your digital armour in an age where data is the new gold.
Want to learn the basics of the ISO 27001 Framework? ISO 27001 Foundation Course can help you nail the basics of ISO 27001.
Frequently Asked Questions
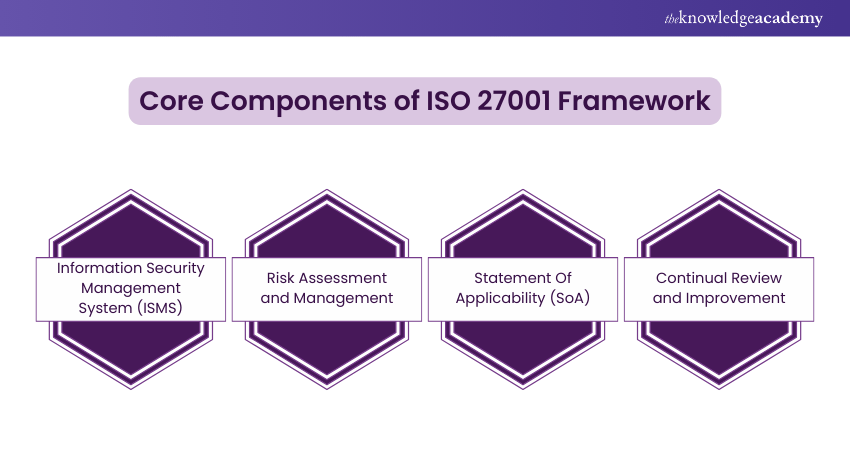
What are the Key Components of the ISO 27001 Framework?

The key components of the ISO 27001 Framework include risk assessment, security policies, access control, incident management, asset management, and continuous improvement, all supported by leadership commitment and regular audits to ensure ongoing compliance and effectiveness.
How Does ISO 27001 Framework Contribute to Risk Management?

The ISO 27001 Framework significantly elevates risk management through:
a) Risk assessment and treatment
b) Continuous monitoring and review
c) Improved risk awareness
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various ISO 27001 Courses, including the ISO 27001 Foundation Course and the ISO 27001 Internal Auditor Course. These courses cater to different skill levels, providing comprehensive insights into what is ISO.
Our ISO & Compliance Blogs cover a range of topics related to ISO standards, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your knowledge of ISO, The Knowledge Academy's diverse courses and informative blogs have got you covered.

Hailey Davis is an ISO compliance expert with over 10 years of experience in audit, quality management systems (QMS), and regulatory compliance. She has worked with various industries, including manufacturing, healthcare, and technology, ensuring organisations achieve and maintain ISO certifications. Hailey’s content provides practical, actionable insights on navigating compliance challenges and improving business processes.
View Detail
Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 ISO 27001 Foundation
ISO 27001 Foundation
Mon 13th Jul 2026
Mon 26th Oct 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


