We may not have the course you’re looking for. If you enquire or give us a call on + 1-866 272 8822 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Every click, login, and online transaction carries a hidden risk in today’s digital world. Understanding What is Cyber Security is essential as cyber threats continue to evolve, becoming more sophisticated and difficult to detect across industries.
In this blog, we break down what is Cyber Security, its core types, and the best practices organisations use to protect systems, networks, and data. You will also gain insights into how effective security strategies help prevent breaches, reduce risks, and ensure long-term digital resilience.
Table of Contents
1) What is Cyber Security?
2) Why is Cyber Security Important?
3) Essential Security Concepts
4) Common Cyber Security Threats
5) The Different Types of Cybersecurity
6) Advantages of Cyber Security
7) Cyber Security Best Practices
8) Top 10 Cyber Security Tools
9) Conclusion
What is Cyber Security?
Cyber Security is all about protecting devices, networks, and services from threats like hackers, spammers, and cybercriminals. While some parts of Cyber Security work to stop attacks before they happen, most professionals focus on keeping things safe from harm, whether it’s computers, phones, networks, or data.
Why is Cyber Security Important?
In today’s interconnected world, cyber security is essential for protecting individuals and organisations from digital threats. At a personal level, cyberattacks can lead to identity theft, financial loss, and the compromise of sensitive data such as personal files and credentials.
On a larger scale, critical infrastructure like healthcare systems, financial institutions, and energy networks rely heavily on strong cyber security measures. Protecting these systems ensures the smooth functioning of society and prevents widespread disruption.
Cyber security is also strengthened by continuous research and threat analysis, which help identify new vulnerabilities and emerging attack methods. This ongoing effort plays a vital role in making digital environments safer and more resilient for everyone.
Essential Security Concepts
1) Authentication confirms the identity of users trying to access a system, often using multiple factors such as passwords, security keys, or biometrics like fingerprints.
2) Authorisation controls what resources verified users are allowed to access, similar to assigning different access levels within an organisation
3) Confidentiality ensures sensitive information is kept private by restricting access only to those who require it, often through encryption and strict access controls.
4) Integrity guarantees that data remains accurate and unaltered throughout its entire lifecycle, preventing any unauthorised changes.
Availability ensures that authorised users can access systems and information whenever needed, while safeguarding against interruptions caused by cyber threats.
Common Cyber Security Threats
Common Cyber Security threats are risks that can harm systems, networks, and data, leading to data breaches and financial loss. Recognising these threats is key to protecting against them. These are the common Cyber Security risks:
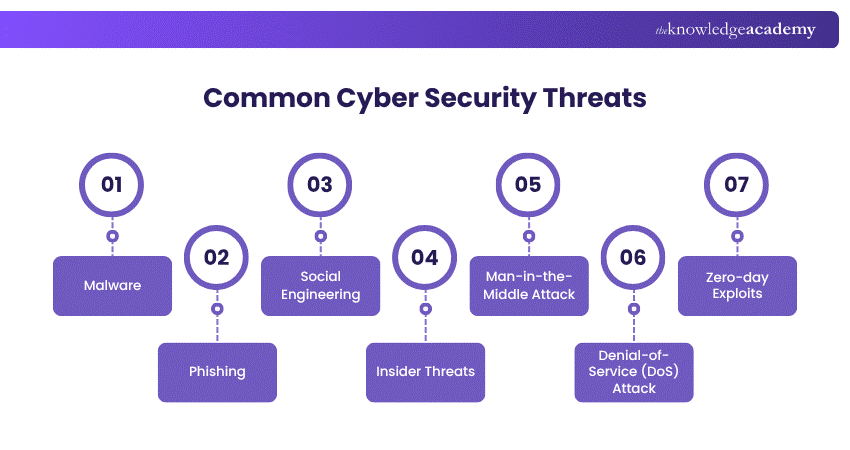
1) Malware
Malware is malicious software designed to disrupt, damage, or gain unauthorised access to systems. It’s one of the most common cyber threats, often spread through suspicious emails or downloads. Cybercriminals use malware for financial gain, espionage, or disruption. Understanding and defending against malware is a core Cyber Security Skill that supports the Three Pillars of Cyber Security, i.e. confidentiality, integrity, and availability.
2) Phishing
Phishing is a cyber-attack where criminals send fraudulent emails that seem to originate from reputable sources. Similar to phishing, Pharming aims to deceive individuals into disclosing sensitive personal information.
3) Social Engineering
Social Engineering is a deceptive tactic where attackers exploit human behaviour to gain unauthorised access to systems or data. Instead of hacking software, they manipulate people to reveal passwords, click malicious links, or share sensitive information. It’s a powerful method because it preys on trust, urgency, and emotion, making awareness and training key defences.
4) Insider Threats
Insider threats come from within an organisation and can be intentional or accidental. They involve employees, contractors, or partners who misuse their access to compromise data or systems. Whether it’s a disgruntled staff member leaking information or someone unknowingly clicking a harmful link, insider threats are difficult to detect and can cause significant damage if not properly monitored and managed.
5) Man-in-the-Middle Attack
Man-in-the-Middle Attack is a cyber-attack where an attacker intercepts the communication between two parties (such as a user and a website). By eavesdropping on the data exchange, the attacker can steal sensitive information or alter the communication.
6) Denial-of-Service (DoS) Attack
A Denial-of-Service (DoS) Attack is a cyber-attack that overwhelms a computer system, network, or server with excessive traffic, making it unusable. Cybercriminals flood the target with requests, disrupting normal Cyber Security Operations and preventing legitimate users from accessing services.
7) Zero-day Exploits
Zero-day exploits are attacks that target software vulnerabilities unknown to the vendor or public. Because there’s no patch or fix available at the time of the attack, they pose a serious risk and are often used in high-stakes cyber espionage or advanced persistent threats. These exploits can remain undetected for long periods, giving attackers a dangerous head start.
Gain a strong foundation in securing systems and networks with our Introduction to System and Network Security Course – Join today!
The Different Types of Cybersecurity
Cybersecurity includes multiple specialised areas that work together to protect systems, networks, and data from evolving threats. Each type focuses on securing a specific aspect of digital infrastructure. These are the key types of cybersecurity:
1) AI Security
AI security focuses on protecting artificial intelligence systems from threats such as data manipulation and malicious inputs. It also leverages AI technologies to enhance threat detection and response capabilities.
2) Critical Infrastructure Security
This type protects essential systems like healthcare, energy, and financial services that are critical to societal functioning. Strong security here prevents large-scale disruptions and national risks.
3) Network Security
Network security safeguards systems from unauthorised access and cyberattacks across networks. It ensures secure data transmission and continuous monitoring of network activity.
4) Endpoint Security
Endpoint security protects devices such as laptops, mobiles, and servers that connect to networks. It helps prevent threats from entering systems through vulnerable endpoints.
5) Application Security
Application security focuses on identifying and fixing vulnerabilities in software applications. It ensures secure development practices and protects against exploitation.
6) Cloud Security
Cloud security protects data and applications stored in cloud environments. It involves shared responsibility between service providers and users to maintain secure access and storage.
7) Information Security
Information security ensures the protection of sensitive data from unauthorised access or misuse. It maintains data confidentiality, integrity, and availability.
8) Identity Security
Identity security manages and protects user identities and access controls. It ensures that only authorised users can access systems and critical resources.
Advantages of Cyber Security
Businesses and individuals (such as MSSPs) can safeguard themselves and others from the entire range of Cyber Security dangers listed below by installing security solutions and experiencing the Benefits of Cyber Security.
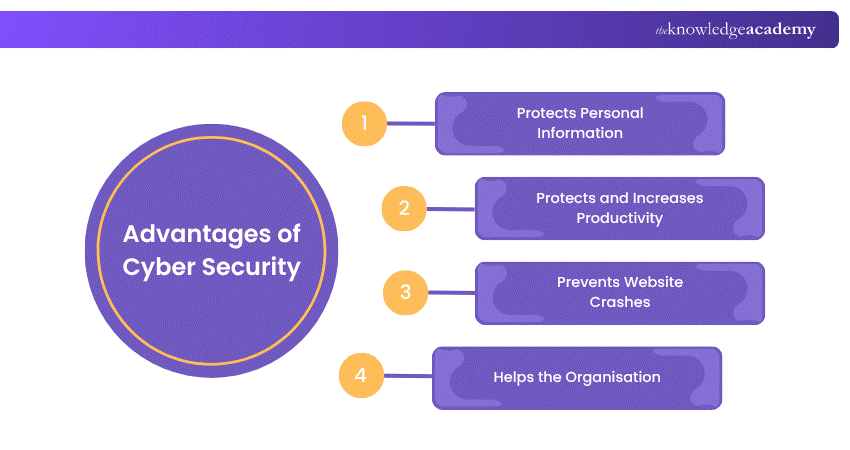
1) Protects personal information by preventing viruses from stealing or exploiting data from employees or customers.
2) Maintains and boosts productivity by stopping viruses from disrupting computers and networks.
3) Prevents website crashes, avoiding lost transactions and damage to systems for small businesses.
Supports the organisation with tools and strategies to defend effectively against cyberattacks and criminals.
Learn to identify, assess, and mitigate cyber risks with confidence with our Cyber Security Risk Management Course- Sign in now!
Cyber Security Best Practices
In an age where digital threats are growing faster than ever, following strong Cyber Security practices is no longer optional, it is essential. Whether you're an individual browsing online or a business managing sensitive data, taking the right precautions can make all the difference in protecting your digital world.
1) Use Strong, Unique Passwords
A strong password is like the lock on your front door; if it’s weak, you’re inviting trouble. While focusing on external threats is crucial, don’t overlook Insider Threats in Cyber Security, which can exploit poor password hygiene. Use long, complex passwords that include a mix of letters, numbers, and symbols. Avoid using the same password across multiple accounts. Better yet, consider a reputable password manager to keep everything secure and easy to manage.
2) Enable Multi-Factor Authentication (MFA)
Even the strongest passwords can be cracked. That’s where MFA comes in. By adding an extra layer of verification, like a one-time code sent to your phone, you make it much harder for intruders to break in. Think of it as a second lock on your digital door.
3) Keep Software Up to Date
Software updates are more than just feature upgrades; they often fix security flaws that attackers can exploit. Regularly updating your operating system, apps, and antivirus software ensures you’re not left vulnerable to known threats.
Top 10 Cyber Security Tools
Cyber Security tools are important for protecting systems and data from cyber crime. These tools help find weak spots, spot bad activities, and respond to security problems. By using the exact tools, companies can make their security stronger and keep their digital information safe.
1) CrowdStrike Falcon: A cloud tool that uses AI to find and stop threats quickly. It protects devices, gives threat information, and helps fix security problems.
2) Palo Alto Networks Next-generation Firewall: Protects networks by checking traffic for bad content and blocking threats right away.
3) Splunk: A tool that watches data in real time and sends alerts to help spot and fix security issues.
4) Norton 360: A full security package with antivirus, VPN, firewall, and protection against identity theft for individuals and small businesses.
5) Darktrace: Uses AI to find strange activity and possible threats, and automatically stops them.
6) Check Point Software: Protects networks, devices, and mobile phones with strong security and helps manage threats.
7) Fortinet FortiGate: A firewall that checks data, stops threats, and keeps networks safe.
8) McAfee Total Protection: Provides antivirus, web security, and identity protection for home and business users.
9) IBM QRadar: Collects and checks data to give updates on security problems and helps decide which issues to fix first.
10) Bitdefender GravityZone: Protects businesses from malware, manages firewalls, and checks for system weaknesses.
Develop the skills to detect, manage, and recover from cyber incidents efficiently with our Incident Response Training- Join now!
Conclusion
Understanding What is Cyber Security is essential for protecting digital systems, data, and networks in today’s connected world. It plays a critical role in preventing cyber threats and ensuring business continuity. By implementing the right types and best practices, organisations can strengthen their security posture. Ultimately, effective cyber security safeguards both individuals and organisations from evolving digital risks.
Build essential knowledge to recognise and prevent cyber threats effectively with our Cyber Security Awareness Course- Sign in today!
Frequently Asked Questions
What Career Opportunities are Available in Cyber Security?

Types of Cyber Security include Network Security, Application Security, Information Security, Cloud Security, Endpoint Protection, Operational Security, and Disaster Recovery. Each type safeguards different components of digital systems from cyber threats.
What is the Difference Between Cyber Security & Information Security?

Cyber Security protects systems, networks, and data from digital attacks, while information security is broader, covering the protection of all information assets, whether digital or physical, from unauthorised access, use, or damage.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Training, including Cyber Security Awareness Course, Digital Forensics Training, and Social Engineering Training. These courses cater to different skill levels, providing comprehensive insights into Cyber Security Incident Report.
Our IT Security & Data Protection Blogs cover a range of topics related to Cyber Security, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your IT Security & Data Protection skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Certified Cyber Security Professional (CCS-PRO)
Certified Cyber Security Professional (CCS-PRO)
Fri 26th Jun 2026
Fri 4th Sep 2026
Fri 23rd Oct 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


