We may not have the course you’re looking for. If you enquire or give us a call on +358 942454206 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.
Have you ever thought that securing and creating a robust network is enough for your organisation? If it is yes, then you are wrong in your ideology. Protecting your network is important, and so is protecting your devices that are used in your businesses or organisation.
What if you have a secure network, but your data was breached by accessing one of your systems? Sounds terrible, right? To empower and educate you, this blog highlights the key points of What is Endpoint Security and its functions and benefits. Let’s dive into it!
Table of Contents
1) What is Endpoint Security?
2) How does Endpoint Security Work?
3) Endpoint Security Components
4) Core Functions of Endpoint Security
5) Benefits of Endpoint Security
6) Endpoint Protection vs Antivirus: Key Differences
7) Conclusion
What is Endpoint Security?
Endpoint Security is also referred to as endpoint protection. From the term, you might understand that it is related to the security and protection of something called endpoint. It is the process of protecting your endpoints or end-user devices like laptops, computers, mobile phones, and tablets from malicious, suspicious and cyber threats and attacks.
These endpoints are often targeted as entry points because they provide access to sensitive company data and internal systems. The traditional version had antivirus software. However, the upgraded version has incorporated tools like firewalls, intrusion prevention, application control, and threat intelligence, all working together to detect, prevent, and respond to cyber-attacks across all endpoint devices.
How does Endpoint Security Work?
As the central goal is to protect data from any suspicious attacks, Endpoint Security offers robust protection for the data and workflows of the devices that are connected to your network. Here is how the Endpoint Security works:
1) Installing Client Software: As the initial step, client software will be installed on each endpoint, and they will communicate constantly with the central management console.
2) Monitoring and Data Collection: The software continuously scans activity on the device, looking for unusual behaviour or known threat signatures.
3) Threat Detection: When potential risks are identified, the system flags them for review or automatically initiates a response.
4) Policy Enforcement: Security policies can be applied to ensure restricted access to certain websites or block unauthorised software access.
5) Threat Response: The software can isolate affected devices, remove malicious files, or alert administrators to take further action.
Endpoint Security Components
Endpoint Security will have several components to provide a rigid security solution and layered protection. Those components include the following:

1) Firewall: It monitors incoming and outgoing traffic over a network as well as managing access controls.
2) Antivirus and Antimalware Software: These are the foundations and first line of defence in detecting threats like viruses and trojans.
3) Intrusion Prevention System (IPS): It helps to detect and immediately block suspicious network attacks in real time.
4) Endpoint Detection and Response (EDR): It offers advanced detection, continuous monitoring, and identifying complex and potential threats.
5) Endpoint Encryption: It manages your data to be encrypted, thereby deciding who can get access to which data. It prevents data theft by making it unreadable.
6) Patch Management: Updating your software and operating system on a regular basis will upgrade your security and lessen Vulnerabilities in cyber-Security.
Core Functions of Endpoint Security
So far, you have been provided with the components of Endpoint Security and how it works. Let's explore the list of the core functions of Endpoint Security.
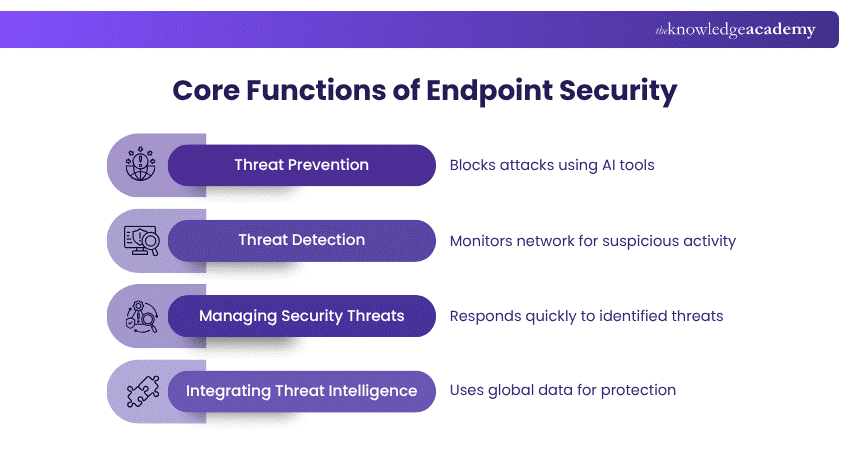
1) Threat Prevention
Have you come across this proverb, “Prevention is better than cure?” Then, you might understand the importance of the act of prevention before anything goes wrong. The same is applicable to your network. Proactively block the attacks before your network gets attacked. For that, Endpoint Security uses Next-generation Antivirus (NGAV) techniques, which incorporate AI and Machine Learning to find possible threats.
2) Threat Detection
What if you are relaxed that you have installed preventive software and some strong cyberattack happened with your network? Who will let you know that? For that purpose, you need to have detection software like EDR to have real-time monitoring of what is happening within your network. It detects anomalies, file changes, and unusual user behaviour that may indicate an active attack.
Aware of the cyber-threats effectively by signing up for our Cyber Security Awareness Course immediately!
3) Managing Security Threats
When a malicious attack has been identified, immediate action for rectification is taken. This might include removing the system from the network or isolating the malware. Sometimes the attacks will be of a highly sophisticated range. For such threats, security professionals are required to check and rectify them. This is often called managed threat hunting, since it involves referring to similar past incidents to effectively handle the situation.
4) Integrating Threat Intelligence
One of the methods to prevent threats is being aware of what is in trend with security breaches. To stay up-to-date, Endpoint Security grabs real-time updates on global threats. With this integration, it easily recognises the latest malware strains, phishing tactics, and exploit methods. This nature aids the security system with proactive threat detection and steps to act upon it.
Benefits of Endpoint Security
Endpoint Security is crucial for all kinds of organisations, irrespective of their size and network. Here are the benefits that come with establishing it:
1) Endpoint Protection
1) Protects endpoints from malware, unauthorised access, and network-based threats
2) Ensures data integrity and device performance to secure the data
2) Advanced Threat Defence
1) Utilises AI, machine learning, and behavioural analysis to detect complex threats
2) Quick detection enhances the remediation process and data protection
3) Securing remote working
1) Offers consistent security across all endpoints, even outside the office network
2) Aids in safe and secured hybrid and remote work environments
4) Enhancing Identity Protection
1) Safeguards login credentials and personal data of the employees
2) Implements multi-factor authentication, and credential vaults to increase security
Enhance protecting your data through Data Privacy Awareness Course - Register immediately!
Endpoint Protection vs Antivirus: Key Differences
Before exploring the difference between Endpoint protection and antivirus, let’s know what an antivirus is:
What is Antivirus?
An antivirus is software that is installed on Endpoint devices like laptops, computers, network servers and mobile devices. The primary function of antivirus software is to detect, eliminate and prevent any threats or malware from attacking your devices.
Usually, you will prepare a list of possible threats and let the antivirus software learn those patterns. After that, it will detect and check if there are any similar patterns noticed on your devices. The problem is you need to keep updating the evolving threats since it could not detect new patterns of malicious threats and attacks.
Endpoint Protection vs Antivirus:
Here are the differences between endpoint protection and antivirus:

Conclusion
With Endpoint Security, protect not only your network, but all the devices that are linked to it. It will be a hassle if you don’t protect your individual systems since a breach can happen with any minute loop. With this blog on What is Endpoint Security, its benefits and functions, its inevitable significance is also highlighted. Start implementing this strategy to make malicious attackers lose their jobs!
Boost your ability to design robust security architectures by signing up for our ISSAP Training & Certification today!
Frequently Asked Questions
What does Endpoint Security Protect Against?

Endpoint security protects against a wide range of threats like malware, ransomware, phishing attacks, data breaches, and unauthorised access.
What are the Three Main Steps of Endpoint Security?

The three main steps of Endpoint Security are prevention, detection, and response. Prevention controls potential threats. Detection monitors suspicious activities. The response involves the actions you take to address the threats.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various CISSP Training, including CISSP Certification, ISSAP Certification and Chief Information Security Officer Training. These courses cater to different skill levels, providing comprehensive insights into What is Antivirus Software.
Our IT Security & Data Protection Blogs cover a range of topics related to Endpoint Security, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Security and Data Protection skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 CISSP Training
CISSP Training
Mon 8th Jun 2026
Mon 13th Jul 2026
Mon 10th Aug 2026
Mon 7th Sep 2026
Mon 12th Oct 2026
Mon 9th Nov 2026
Mon 14th Dec 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


