We may not have the course you’re looking for. If you enquire or give us a call on 800969236 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Choosing the right security framework can directly impact your organisation’s compliance, credibility, and risk management strategy. Understanding ISO 27001 vs SOC 2 is essential for businesses aiming to protect sensitive data while meeting industry and regulatory expectations.
In this blog, we break down ISO 27001 vs SOC 2, highlighting their key differences, benefits, and similarities. You will gain clarity on which framework aligns best with your organisation’s goals, security requirements, and customer expectations.
Table of Contents
1) What is ISO 27001?
2) What is SOC 2?
3) Key Differences Between ISO 27001 vs SOC 2
4) Key Similarities Between ISO 27001 vs SOC 2
5) Which One Is Right for You Between ISO 27001 vs SOC 2?
6) How to Become ISO 27001 Compliant?
7) How to Become SOC 2 Compliant?
8) Conclusion
What is ISO 27001?
ISO 27001 is an internationally recognised standard created by the International Organisation for Standardisation to assist organisations in documenting, establishing, and maintaining an Information Security Management System (ISMS). It offers a well-designed framework for sensitive data management, including such practises as risk assessment, access control, and incident management.
Organisations adopt ISO 27001 to demonstrate their commitment to protecting customer and business information. Certification requires an independent third-party audit to verify that the organisation meets all compliance requirements and follows best practices in information security management.
What is SOC 2?
The SOC 2 is a regulatory framework by the American Institute of Certified Public Accountants (AICPA) to determine the manner in which organisations handle and safeguard customer information. It prioritises some of its major criteria that include security, availability, processing integrity, confidentiality, and privacy.
In order to be SOC 2 compliant, organisations should have adequate controls and be audited by an independent assessor. There is the outcome of a comprehensive report that identifies the efficiency of such controls and the ability of the organisation to protect data.
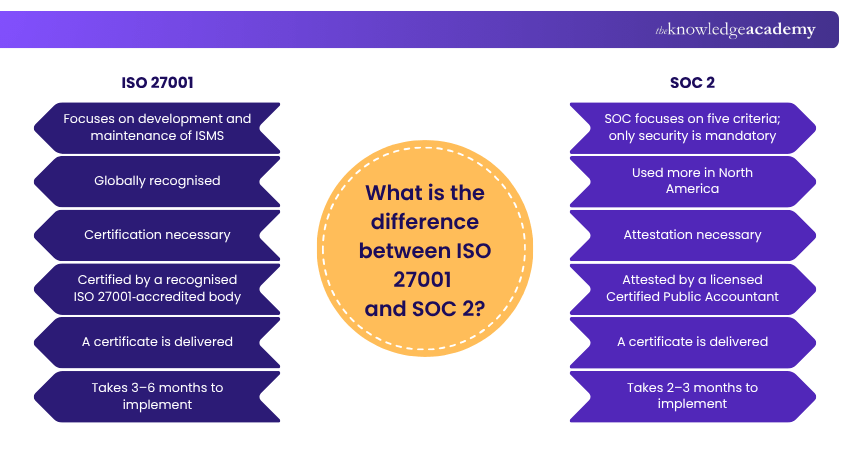
Key Differences Between ISO 27001 vs SOC 2
There is a plethora of differences between ISO 27001 and SOC 2. These differences are described in the below sections:
1) Scope
The primary difference between ISO 27001 and SOC 2 lies in their scope. Both frameworks include security control procedures along with their processes, policies, and technologies to protect sensitive data. Based on the recent studies, they share 96% of the same security protocols; however, their implementation approaches differ.
ISO 27001 focuses primarily on maintaining and developing an Information Security Management System (ISMS), to provide a structured approach to managing information security. Moreover, to complies with ISO 27001, organisations must implement security controls, conduct risk assessments, and review their effectiveness regularly. On the other hand, SO offer more flexibility. It consists of five trust service criteria: availability, processing integrity, security, privacy, and confidentiality. Of all these five criteria, only security is important. Organisations have the option to implement internal controls related to other principles.
2) Market Applicability
The market applicability should play a crucial role in your decision to choose between ISO 27001 and SOC 2. While both frameworks have global recognition, ISO 27001 vs ISO 27002 highlights that SOC 2 is more associated with North America. Conversely, ISO 27001 is a global standard and is more prevalent outside North America.
3) Certification vs Attestation
One of the key differences between the standards is that SOC reports are not generally considered certifications. Since SOC examination services are conducted under the AICPA attestation standards, they are classified as attestation reports. Attestation reports offer an independent auditor's opinion on an organisation's control environment, while a recognised body grants certifications. For SOC 2, the attestation focuses on an organisation's internal controls to meet vital criteria such as security, availability, processing integrity, confidentiality, and privacy. Conversely, an organisation receives certification if its ISMS conforms to the ISO 27001 global standard.
4) Certification/Attestation Process
To achieve certification or attestation under either framework, an external audit is required. However, the process differs in terms of who conducts the audit. For ISO 27001, an accredited certification body must attest to it. On the other hand, for SOC 2 attestation, it can only be performed by a licensed Certified Public Accountant (CPA).
5) External Deliverables
Another notable difference between the two standards is the type and content of external deliverables. The final external deliverable for SOC 2 is a verification report, which includes a service organisation audit result, a statement of the service organisation's management, and a detailed policy description. This description of the organisation details five key components of the system under review: infrastructure, software, people, processes, and data. In addition, the report will include appropriate organisation-level policies and fiduciary service metrics, associated controls, and test results from the auditor's testing.
On the other hand, the external deliverable for ISO 27001 is a one or two-page document that contains relevant information pertaining to the engagement. These include certified organisation’s ISMS scope, in-scope locations, standard certified against, date issued, and date of expiration. Reports are issued at the conclusion of each stage (stage 1, stage 2, surveillance audits, and recertification reviews). However, these reports are primarily for internal use and are not intended as external deliverables, unlike SOC 2 reports.
6) Project Timeline
Once the external audit is completed, both ISO 27001 and SOC 2 certifications can be obtained. The certification process is similar for both frameworks, consisting of three stages. The first stage involves a gap analysis to identify areas of improvement and for the organisation to define its ISO 27001 physical security objectives. The second stage requires the organisation to identify and implement appropriate security controls based on its needs. This step also involves the documentation of practices and the establishment of a method to review and improve processes. The final stage is an internal audit to identify and rectify any issues.
After completing all three stages, an organisation can contact a certification body to arrange for an ISO 27001 or SOC 2 audit. Although the certification process is similar for both frameworks, the time required for implementation varies. The duration typically depends on the work needed to meet the standards. Conducting an ISO 27001 Gap Analysis can help determine the specific actions required for compliance. Implementing SOC 2 usually takes two to three months, whereas ISO 27001 can take three to six months.
Develop expert auditing skills to assess and manage information security systems effectively with our ISO 27001 Lead Auditor- Join now!
Key Similarities Between ISO 27001 vs SOC 2
When comparing ISO 27001 vs SOC 2, both frameworks share several common objectives focused on strengthening data security and building trust. These are the key similarities between ISO 27001 vs SOC 2:
1) Both of them are independent measures that the security controls of an organisation have been designed and implemented well.
2) They both assist organisations in fulfilling regulatory and industry-related standards like GDPR, HIPAA, PCI DSS, and NIST specifications
3) They both help organisations gain a competitive edge as well as credibility through showing good security practises.
4) The two need constant compliance, periodic audits, and improvement to ensure they remain effective.
Which One Is Right for You Between ISO 27001 vs SOC 2?
This section of the blog will describe the different scenarios and needs for which you should choose either ISO 27001 SOC 2 or a combination of both.
When to Choose ISO 27001?
Choosing between ISO 27001 and SOC 2 depends on your compliance needs and requirements. You will be better suited to opt for ISO 27001 if you are looking to fulfil the following needs:
a) Global Compliance Needs: Attaining certification in a single or both standards gives traders and clients reassurance concerning your agency's protection posture. Because the two frameworks have lots in common, becoming certified in a single lets you get towards pleasurable requirements for the opposite. Getting SOC 2 certified might assist an organisation in realising numerous ISO 27001 benefits even though neither framework is required.
b) Comprehensive Information Security Management: ISO 27001 addresses data safety holistically, addressing people, tactics, and generation. Employ this stage to create an integrated management gadget that includes continuous development, criminal compliance, and hazard management.
c) Third-Party Assurance: ISO 27001 certification demonstrates your commitment to facts security to customers, companions, and regulators. If your stakeholders require tangible proof of your security features, ISO 27001 Certification can offer the warranty they want.
When to Choose SOC 2?
The selection between ISO 27001 and SOC 2 depends broadly to your compliance desires and requirements. Choose SOC 2 if it satisfies the following necessities:
a) Industry-Specific Requirements: SOC 2 is critical for generation and cloud computing organisations. If your commercial enterprise handles sensitive purchaser facts, consisting of in Software as a Service (SaaS) or records hosting, SOC 2 compliance ensures you meet industry-particular standards.
b) Trust and Transparency: SOC 2 focuses majorly on controls related to security, availability, processing integrity, confidentiality, and consumer records privacy. This approach offers your clients the much-wanted warranty to beautify agreement and transparency between you and your clients.
c) US Market Focus: SOC 2 is regularly the preferred choice for corporations operating mostly within the United States, where stringent statistics safety standards are essential.
Don't leave anything to chance! Check out our ISO 27001 Interview Questions & Answers and make sure you're fully prepared.
Do You Need Both ISO 27001 and SOC 2?
You might be higher desirable to opt for a aggregate of ISO 27001 and SOC 2 if you are seeking to fulfil the following wishes:
a) Diverse Client Base: If your business caters to a various purchaser base with various compliance requirements, obtaining both ISO 27001 and SOC 2 certifications might be vital. This twin certification method showcases your dedication to assembly both worldwide and industry-unique requirements, thereby accommodating the numerous desires of your customers.
b) Enhanced Security Posture: Integrating ISO 27001's complete framework with SOC 2's centred cognizance on patron records creates a sturdy safety posture. This twin technique not only adheres to generalised safety standards but also meets the specific demands of your industry, accordingly, offering more desirable protection against capability threats.
Build a strong understanding of information security principles and standards with our ISO 27001 Foundation Course- Sign in now!
How to Become ISO 27001 Compliant?
Becoming ISO 27001 compliant requires a structured approach to managing information security. Start by defining security policies, objectives, and conducting a risk assessment to identify vulnerabilities.
Implement appropriate controls, train employees on security practices, and regularly monitor and review processes. Conduct internal audits and obtain certification through an authorised auditor, ensuring continuous improvement over time.
How to Become SOC 2 Compliant?
Achieving SOC 2 compliance involves implementing strong controls to protect customer data. Begin with an internal assessment to identify gaps, followed by establishing security policies aligned with SOC 2 requirements.
Ensure employee awareness, monitor systems, and document all processes. Engage an independent auditor to assess controls, address any gaps, and maintain compliance through continuous monitoring and improvement.
Learn to conduct internal audits and ensure compliance with ISO 27001 requirements with our ISO 27001 Internal Auditor Course- Join today!
Conclusion
Understanding ISO 27001 vs SOC 2 helps organisations choose the right framework to strengthen their information security and compliance strategy. Both offer valuable approaches to protecting sensitive data and building stakeholder trust. The right choice depends on business needs, industry focus, and geographic requirements. Implementing either ensures stronger security and long-term organisational resilience.
Gain the skills to plan, implement, and manage an effective ISMS with our ISO 27001 Lead Implementer Course- Sign in today!
Frequently Asked Questions
What is the Overlap Between ISO 27001 and SOC 2?

The overlap between ISO 27001 and SOC 2 lies in their focus on protecting sensitive data through strong security controls, risk management, and continuous monitoring. Both frameworks require regular audits, support regulatory compliance, and help organisations demonstrate trust and accountability in managing information security.
Is SOC 2 Certification Mandatory?

SOC 2 certification isn’t mandatory but is highly recommended. It’s a valuable way to demonstrate your commitment to data security and build client trust. While not required by law, many businesses choose SOC 2 to fulfil industry expectations and gain a competitive edge.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various ISO 27001 Training Courses, including the ISO 27001 Foundation, ISO 27001 Lead Auditor, and ISO 27001 Internal Auditor Training. These courses cater to different skill levels, providing comprehensive insights into the ISO 27001 Gap Analysis.
Our ISO & Compliance Blogs cover a range of topics related to information security and regulatory standards, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your compliance and certification skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

Hailey Davis is an ISO compliance expert with over 10 years of experience in audit, quality management systems (QMS), and regulatory compliance. She has worked with various industries, including manufacturing, healthcare, and technology, ensuring organisations achieve and maintain ISO certifications. Hailey’s content provides practical, actionable insights on navigating compliance challenges and improving business processes.
View Detail
Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 ISO 27001 Foundation
ISO 27001 Foundation
Mon 1st Jun 2026
Mon 6th Jul 2026
Mon 3rd Aug 2026
Mon 7th Sep 2026
Mon 5th Oct 2026
Mon 2nd Nov 2026
Mon 7th Dec 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


