We may not have the course you’re looking for. If you enquire or give us a call on +47 80010068 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.
Picture this: You write a secret letter, but you transform it into a mysterious code only your friend can decipher before sending it. That’s encryption! Now, with the correct key, your friend translates it back into plain text—welcome to decryption! Essentially, these two processes work together like digital guardians, keeping sensitive data safe from prying eyes and hackers.
From securing online transactions to protecting private messages, Cryptography Techniques like encryption and decryption continue to shape our digital world. But how exactly do these two processes differ? Look no further! This blog explores the Difference Between Encryption and Decryption in detail along with their applications and real-life examples. So read on and understand their importance in fortifying digital information.
Table of Contents
1) What is Encryption?
2) What is Decryption?
3) Difference between Encryption and Decryption
4) Real-life Examples of Encryption and Decryption
5) Applications of Encryption and Decryption
6) Types of Keys
7) Conclusion
What is Encryption?
Encryption is the process of converting information (plaintext) into a form that cannot be accessed or read without the appropriate key (ciphertext). It's a fundamental part of Cyber Security because it ensures the confidentiality of data by making it inaccessible to unauthorised parties. Encryption algorithms employ mathematical formulas to scramble the data and makes it secure during transmission or storage.
What is Decryption?
Decryption is the process of turning the unreadable data that was scrambled through encryption back into its original form. It makes the information clear and understandable, like readable text or images. This can be done manually or automatically, often using keys or passwords.
Difference between Encryption and Decryption
Here are the key differences between the encryption and decryption processes:

Real-life Examples of Encryption and Decryption
Here are some real-life examples of encryption and decryption:
1) Messaging Apps Security: End-to-end encryption is used by many messaging apps to keep the messages private. Using a pre-shared key or password makes sure that only the sender and recipient can read them.
2) Secure Data Transfer: The data sent between a website’s server and the user’s browser is protected by encryption. This keeps sensitive information such as passwords, credit card details and personal data safe from unauthorised access.
3) VPN Protection: The internet traffic is encrypted by VPN services, preventing hackers from looking into your online activity. This is especially beneficial on public Wi-Fi networks.
4) File and Disk Protection: Encryption is used to secure the files on your computer or hard drive from unauthorised access. Tools like BitLocker (Windows) and FileVault (Mac) require a password to unlock encrypted files and make them readable.
Gain in-depth knowledge on network security controls and protocols in our comprehensive Certified Network Defender Certification - Register now!
Applications of Encryption and Decryption
Encryption and decryption find widespread usage as exemplified by these applications:
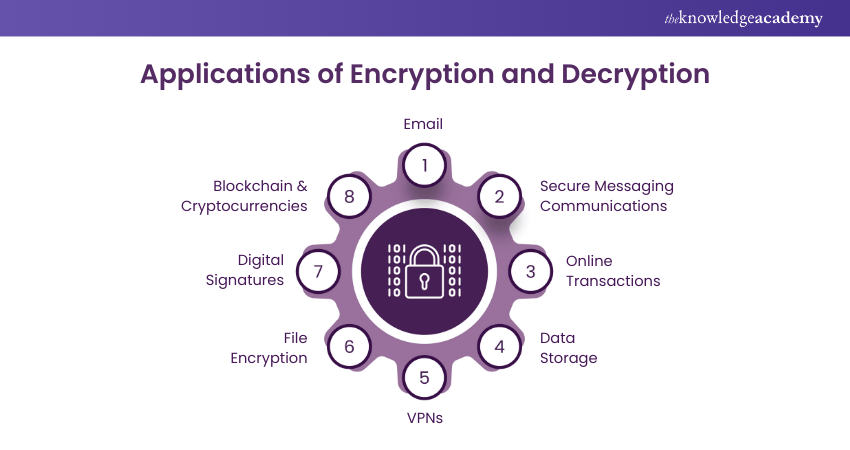
1) Email: Email encryption protects email content from outside an email conversation that wants to obtain participant information.
2) Online Transactions: During online transactions, websites use encryption (HTTPS) to protect sensitive information like credit card details and personal data.
3) Data Storage: The encryption process protects the data stored on devices such as smartphones, laptops, and Cloud storage services. This ensures that the data remains secure even if the device is lost or stolen.
4) Virtual Private Networks (VPNs): VPNs utilise encryption to build a secure connection over the internet. It protects data transmitted between the user's device and the VPN server.
5) Secure Communications: Encryption is used by messaging apps (like WhatsApp and Signal) to make sure that only the intended recipients can read the messages.
6) File Encryption: Tools like BitLocker and VeraCrypt protect sensitive information from unauthorised access by encrypting files and folders on a computer.
7) Digital Signatures: Encryption is widely used in digital signatures to verify the integrity of digital software and documents.
8) Blockchain and Cryptocurrencies: Encryption and decryption ensures the security and integrity of transactions in blockchain technology and Cryptocurrencies like Bitcoin and Ethereum.
Master cutting-edge cryptographic techniques in our Certified Encryption Specialist Certification - Sign up now!
Types of Keys
In Cryptography, various types of keys are utilised to secure communication and data. Here's an overview of the primary key types:
Symmetric Key
a) It uses the same cryptographic key for encryption and decryption.
b) Its efficient and fast nature makes it ideal for encrypting large volumes of data.
c) The primary challenge is securing the key among all involved parties.
d) Anyone with access to this key can decrypt the data.
Asymmetric Key
a) It's also known as public-key Cryptography.
b) It uses two keys: one public key for encryption and a private key for decryption.
c) The public key is available for everyone, while the private key is kept secret.
d) It improves security by avoiding the need to share the private key.
e) It's ideal for secure communication over untrusted networks.
Public Key
a) It's a part of asymmetric encryption, openly shared with others.
b) It's used to encrypt messages meant for the key pair's owner.
c) Only the corresponding private key can decipher these messages.
d) It makes sure sensitive information remains confidential during transmission
Private Key
a) This is the secret counterpart to the public key in asymmetric encryption.
b) It's used to decrypt messages that were encrypted with the corresponding public key.
c) Keeping the private key secure is vital for maintaining data protection.
d) Exposure to private keys can compromise encrypted data.
Pre-Shared Key
a) This is a secret key shared between parties before being used for encryption.
b) It's commonly used in symmetric encryption, where the same key is needed for encryption and decryption.
c) The security level depends on how well the key is protected during distribution and storage.
d) If the key is leaked, the encrypted data becomes vulnerable.
Acquire practical skills for preventing and managing cyber threat in our Certified Cyber Security Technician Certification - Sign up now!
Conclusion
Encryption and decryption work together to protect digital data, providing secure communication and safeguarding sensitive information. While encryption jumbles data into an unreadable format, decryption restores it for authorised access. Understanding the Difference Between Encryption and Decryption helps strengthen Cyber Security, making digital interactions safer in an era where data protection is essential.
Learn how to implement robust security policies and protocols in our EC – Council Certification Training - Sign up now!
Frequently Asked Questions
Can Encrypted Data be Decrypted Without a Key?

No, encrypted data cannot be decrypted without the right key. Since encryption algorithms are designed to transform data into an unreadable format, the decryption key is essential to reverse this process.
What are the Most Common Types of Encryptions Used Today?

The most common types of encryptions used today include:
a) Transport Layer Security/Secure Sockets Layer (TLS/SSL).
b) Advanced Encryption Standard (AES).
c) Rivest-Shamir-Adleman (RSA).
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various EC – Council Certification Courses, including the Certified Ethical Hacker Course and the Certified Encryption Specialist Certification. These courses cater to different skill levels, providing comprehensive insights into What is Hacking.
Our IT Security & Data Protection Blogs cover a range of topics related to encryption and decryption, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your IT Security skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Certified Encryption Specialist Certification
Certified Encryption Specialist Certification
Mon 3rd Aug 2026
Mon 12th Oct 2026
Mon 21st Dec 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


