We may not have the course you’re looking for. If you enquire or give us a call on +31 208081674 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Every time you browse a website, your browser quietly runs scripts that make pages interactive and dynamic. But what if those scripts are malicious? This is where Cross-Site Scripting (XSS) can become a serious Cyber Security issue. XSS attacks allow Hackers to inject harmful code into trusted websites, putting user data, sessions and privacy at risk.
Understanding how these attacks work is essential for Developers and users alike. In this blog, we break down what is Cross-site Scripting, explore its different types, and reveal real‑world examples that show how easily vulnerabilities can be exploited. So read on!
Table of Contents
1) What is Cross-site Scripting (XSS)?
2) How Does Cross-site Scripting Work?
3) Types of Cross-site Scripting Attacks?
4) How to Prevent Cross-site Scripting?
5) How To Find XSS Vulnerabilities?
6) How Attackers Exploit XSS to Cause Damage?
7) What is the Impact of XSS?
8) Example of a Cross-site Scripting Attack
9) Conclusion
What is Cross-site Scripting (XSS)?
Cross-site Scripting (XSS) is a kind of cyberattack in which the attacker injects a malicious code into a legitimate website. When the user visits the affected page, the harmful code runs in their browser. This code is typically embedded in URLs or placed in areas that allow user-generated content. In technical terms, XSS is a client-side code injection attack that targets users interacting with the compromised webpage. Its prevalence can be gauged by the fact that by mid-2025, the Microsoft Security Response Center (MSRC) had addressed more than 970 Cross-site Scripting (XSS) incidents reported since January 2024.
How Does Cross-site Scripting Work?
Cross-site Scripting works by taking advantage of security weaknesses in a website that allows malicious code to be returned to users when they visit a page. When this happens, harmful JavaScript runs inside the user’s browser, allowing the attacker to interfere with the user’s interaction with the website.
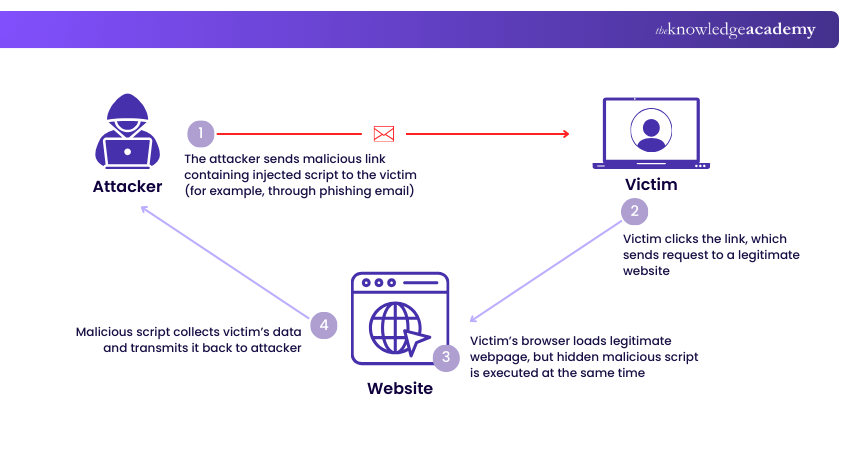
Although XSS can involve different scripting languages and technologies such as VBScript, ActiveX, Adobe Flash, or CSS, it most commonly targets JavaScript, which is widely used in web browsing environments. An XSS attack generally occurs in two stages:
1) The first stage involves injecting malicious code, known as a payload, into a webpage. This becomes possible when a website allows user-generated input, such as comments, forms, or search fields, without properly filtering it.
2) The second stage occurs when a victim visits the compromised page containing the malicious payload. Attackers often use Social Engineering or phishing techniques to trick the users into clicking a link or visiting an infected webpage.
Turn networking fundamentals into real-world IT expertise with our CompTIA Network+ Training - Sign up now!
Types of Cross-site Scripting Attacks
The three primary categories of XSS attacks are persistent, reflected and DOM-based XSS. Let's explore them in detail:
1) Persistent XSS
Persistent, also known as stored XSS, occurs when untrusted user input is saved directly on a server. Attackers exploit the vulnerable websites or applications to inject malicious code that becomes stored in the system. When other users later visit the affected page, the stored code automatically runs in their browsers.
2) Reflected XSS
Reflected, or non-persistent XSS, happens when an unverified user input is immediately returned by a web application and displayed in the user’s browser. Attackers usually trick victims into clicking a specially crafted malicious link that sends harmful data to the target website.
3) DOM-based XSS
DOM-based XSS differs from other types because the vulnerability exists in the user’s browser rather than on the server. The malicious script is neither stored nor sent to the server. Instead, it exploits weaknesses in client-side JavaScript that fail to validate or sanitise input properly.
How to Prevent Cross-site Scripting?
The following best practices help reduce application security vulnerabilities that may lead to Cross-site Scripting attacks:
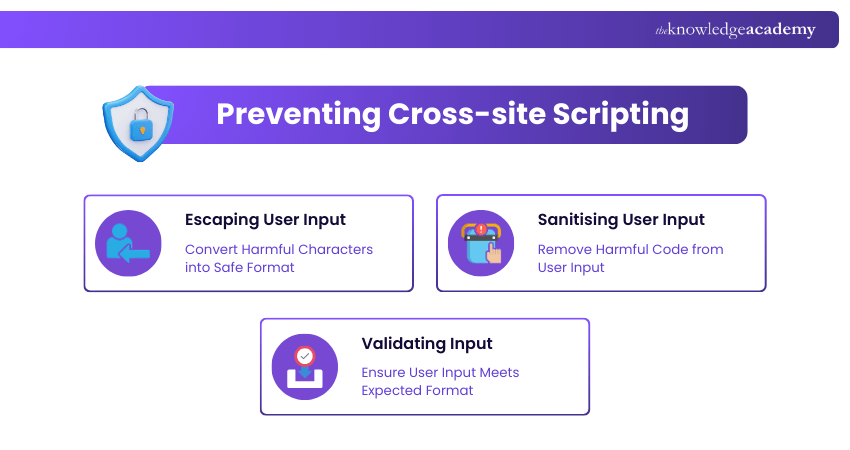
1) Escaping User Input
Escaping user input involves processing the data received by an application before displaying it to users. This ensures that the special characters in the input are not interpreted as executable code by the browser. Instead, these characters are converted into safe formats, preventing them from triggering malicious scripts.
2) Sanitising User Input
Sanitising input removes or modifies potentially harmful characters from user-submitted data. This process converts the unsafe input into a secure format so it cannot be executed as code. It's particularly useful for websites that allow users to include HTML or formatted content.
3) Validating Input
Input validation ensures that only appropriate and expected data is accepted by an application. By restricting certain characters or formats in input fields, websites can prevent malicious scripts from being submitted through forms. This helps protect the website, its database and its users from potential XSS attacks.
Take your IT skills to the Cloud and beyond with our CompTIA Cloud+ Certification - Register now!
How to Find XSS Vulnerabilities?
Finding XSS vulnerabilities can be challenging because they often depend on the specific type of attack, the way user input is handled and the programming framework or scripting language used. However, many of these vulnerabilities can be identified using web vulnerability scanning tools.
XSS weaknesses may also appear when Developers update the code or integrate new libraries, modules or software components. For this reason, organisations must regularly scan their web applications to detect unusual behaviour or security gaps before they can be exploited.
Guard your data with ease far from the prying eyes of Hackers. Learn how in our Cyber Security Awareness Training – Register now!
How Attackers Exploit XSS to Cause Damage?
Cross-site Scripting attacks often target JavaScript because it can access sensitive information within a user’s browser. For example, JavaScript can read browser cookies, which may contain login details or session data. JavaScript can also send HTTP requests, allowing stolen information to be transmitted to the attacker’s server.
Additionally, client-side scripts may access certain browser APIs that reveal data such as geolocation or other sensitive information. A typical XSS attack usually follows these steps:
1) A victim visits a webpage containing malicious code, which secretly copies the user’s cookies.
2) The script prompts an HTTP request to the attacker’s server with the stolen cookies included.
3) The attacker then uses those cookies to impersonate the victim on the website, potentially carrying out Social Engineering attacks or accessing sensitive information such as personal or financial data.
What is the Impact of XSS?
The impact depends on the type of website or application targeted, the data involved and the level of access of the affected user. These factors typically determine the severity:
1) If sensitive information such as banking details or healthcare records is exposed, the consequences can be significant.
2) The attack becomes more critical when the compromised user has higher access privileges within the application.
3) When users provide sensitive personal or identifiable information, the potential damage from the attack can be substantial.
Example of a Cross-site Scripting Attack
A common example of Cross-site Scripting occurs on websites that allow user comments without properly validating the input. In such cases, an attacker may post a comment containing executable code placed within tags.
These tags instruct the browser to treat the content between them as JavaScript. When other users visit the page and the comment loads, the browser executes the malicious code, making those new users the victims of the attack.
Conclusion
Cross‑site scripting may be invisible to the untrained eye, but its impact is anything but subtle. By understanding XSS, its types, and real‑world examples, you can gain the tools to spot and stop these sneaky attacks. With awareness and strong security practices, you can outsmart malicious scripts and keep our digital experiences safer and more resilient.
Build a future-ready tech career with the power of CompTIA. Sign up for our CompTIA Certifications now!
Frequently Asked Questions
What is the Difference Between XSS and SQL Injection?

The key distinction lies in the target of these attacks. XSS targets users by injecting malicious scripts that run in their browsers, often stealing cookies or session data. Meanwhile, SQL injection targets a website’s database by inserting malicious SQL queries to modify or delete stored data.
What's the Best Mitigation for XSS?

The most effective way to prevent XSS is to properly validate, sanitise, and escape all user input before displaying it on a webpage. Using secure coding practices, implementing content security policies and regularly testing applications for vulnerabilities can significantly reduce the risk of Cross-site Scripting attacks.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various CompTIA Certification Training, including the CompTIA Cloud+ Certification, CompTIA Network+ Training and the CompTIA Security+ Certification. These courses cater to different skill levels, providing comprehensive insights into CompTIA Project+.
Our IT Infrastructure & Networking Blogs cover a range of topics related to Cross-site Scripting, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your IT Security skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

Lily Turner is a data science professional with over 10 years of experience in artificial intelligence, machine learning, and big data analytics. Her work bridges academic research and industry innovation, with a focus on solving real-world problems using data-driven approaches. Lily’s content empowers aspiring data scientists to build practical, scalable models using the latest tools and techniques.
View Detail
Upcoming IT Infrastructure & Networking Resources Batches & Dates
Date
 CompTIA PenTest+ Certification
CompTIA PenTest+ Certification
Mon 10th Aug 2026
Mon 12th Oct 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


