We may not have the course you’re looking for. If you enquire or give us a call on +60 1800812339 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Text messages feel quick and personal, which is exactly why cybercriminals use them. Blending SMS with phishing, this scam slips into your text messages pretending to be someone you trust, like your bank, a delivery service, or even your workplace. With just one tap on a malicious link, your personal data can fall into the wrong hands.
These scams often appear urgent or legitimate, making them easy to fall for. In this blog, you’ll explore What is Smishing, the common types and real-world examples, and practical tips to help you recognise and prevent these attacks. So read on and fend off these attacks with ease!
Table of Contents
1) What is Smishing?
2) How Does Smishing Work?
3) Types of Smishing Attacks
4) How to Detect Smishing Scams?
5) How to Prevent Smishing Attacks?
6) Smishing vs Phishing vs Vishing
7) Examples of Smishing Scams
8) Conclusion
What is Smishing?
Smishing in Cyber Security is a type of cyberattack carried out through SMS or text messages. The term combines “SMS” and “phishing.” In a smishing attack, criminals send misleading messages to trick people into revealing personal or financial details, clicking harmful links or downloading malicious apps. Similar to email phishing, these messages often appear to come from trusted organisations and use tactics like urgency or curiosity to pressure recipients into taking action.
How Does Smishing Work?
Most smishing attacks operate in a similar way to email phishing. Attackers combine technical methods with psychological tactics to trick victims. The general process usually involves the following steps:
1) Target Selection: Cybercriminals identify their targets. This may involve sending messages to large lists of phone numbers or focusing on specific individuals using data from previous breaches or information sold online.
2) Message Creation: The attacker crafts a convincing text message designed to trigger emotions such as urgency, fear, or curiosity. These messages usually include a clear call to action, such as clicking a link or contacting a number.
3) Message Distribution: The fraudulent messages are sent using SMS gateways, spoofing tools, or compromised devices to reach the intended recipients.
4) Victim Interaction: Once the message is received, the victim may be encouraged to click a link, reply with personal details, or call the provided number.
5) Data Theft or Malware Installation: If the victim responds, they may be directed to a fake website that collects sensitive information, or they may unknowingly download harmful software onto their device. In some cases, attackers may extract information directly through phone conversations.
6) Misuse of Stolen Information: The collected data can then be used for unauthorised financial activity, identity theft, resale on illegal markets, or further cyberattacks.
7) Avoiding Detection: To remain unnoticed, attackers often change phone numbers, alter their methods, and use tools that hide their identity and location.
Uncover the secrets hidden in every byte. Sign up for our Computer Forensics Foundation Training and follow the digital footprints like a pro!
Types of Smishing Attacks
Smishing attacks have become the new form of Phishing that extracts vital information from the targets by tricking them. Even though these attacks use similar methods, their presentation differs significantly. Some of the common types of such attacks are:
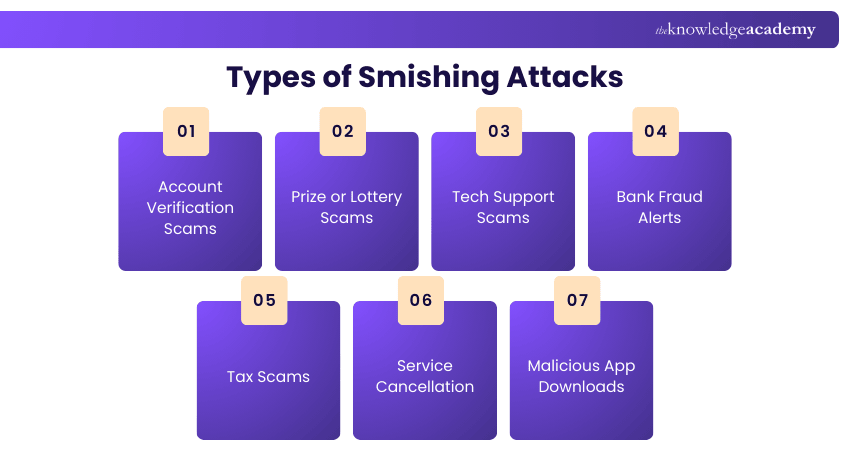
1) Account Verification Scams
In this scam, victims receive a message claiming to be from a trusted organisation like a bank or delivery service. The message warns about suspicious activity or asks the user to verify their account. When the link is clicked, it leads to a fake login page that captures the victim’s credentials.
2) Prize or Lottery Scams
Attackers inform victims that they have won a prize, a lottery or a sweepstake. To claim the reward, they are asked to provide personal information, pay a fee or click a link. The real objective is to steal money or sensitive data.
3) Tech Support Scams
A message warns the recipient about an issue with their device or account and asks them to contact a support number. When the victim calls, they may be charged fees or coerced into granting remote access, which can result in data theft.
4) Bank Fraud Alerts
These messages appear to come from a bank and warn about suspicious transactions. The victim is asked to click a link or call a number to verify activity, both of which are controlled by the attacker.
5) Tax Scams
During tax season, fraudsters send messages pretending to be from tax authorities. They may promise refunds or threaten penalties for unpaid taxes to pressure victims into sharing personal or financial information.
6) Service Cancellation
The victim receives a message claiming that a subscription or service is about to be cancelled due to a payment problem. They are urged to click a link to resolve the issue, which typically leads to a fraudulent website.
7) Malicious App Downloads
Some smishing messages promote useful or entertaining mobile apps. When the link is clicked, it installs malicious software that can compromise the user’s device and data.
See what others miss and detect fraud with data‑driven precision with our Fraud Analytics Training - Sign up now!
How to Detect Smishing Scams?
Smishing messages become harmful only when a user interacts with them. Recognising suspicious signs can help you avoid becoming a victim. Here's how you can detect them:
1) Banks and financial institutions never request passwords, PINs, or transfer information via text message. Never share sensitive financial information via SMS.
2) Messages promising quick money, prizes, or rewards after entering personal details are often scams. Discount or coupon offers are also commonly used tactics.
3) Be cautious of messages from unfamiliar phone numbers and avoid responding to them.
4) Storing sensitive banking details on your phone can make them vulnerable if malware is installed.
5) Short or unusual sender IDs with only a few digits may indicate the message was sent from an email gateway, which is often associated with spam.
6) Many telecom providers allow users to report suspicious messages so they can investigate and help protect others.
How to Prevent Smishing Attacks?
Since smishing attacks are widespread, their prevention requires a mix of technology, organisational practices and individual awareness. Let’s explore each in detail:
1) Technological Measures
Technological solutions play an essential role in preventing smishing attacks. Many smartphones and mobile carriers provide SMS filtering features that can automatically catch and block suspicious messages.
Using Multi-Factor Authentication (MFA) also strengthens security, as it adds an extra verification step even if attackers obtain login credentials. In addition, mobile anti-phishing tools and security applications can identify malicious links in text messages and warn users before they access unsafe websites.
2) Organisational Measures
Organisations can reduce the risk of smishing by implementing strong awareness and security practices. Regular Cyber Security training helps employees recognise suspicious messages and respond appropriately. Clear reporting channels allow staff to flag potential smishing attempts, enabling the organisation to alert others and respond quickly.
Some companies also run simulated smishing exercises to test awareness and identify training gaps. Keeping devices, applications, and security tools up to date further protects systems from newly discovered threats.
3) Individual Safety Practices
Individuals can also take simple steps to protect themselves from smishing attacks. Avoid clicking on unverified links or downloading attachments from unexpected messages. If a text claims to come from a company or organisation, verify it via official contact details instead of using the contact information provided in the message.
Using device security features such as biometric locks and regular updates can help safeguard personal data. Staying informed about common smishing tactics, avoiding sharing sensitive information via text, and confirming the legitimacy of communications can significantly reduce the risk of falling victim to these scams.
Great Cyber Security starts with great risk decisions. Start your journey into security excellence with our Cyber Security Risk Management Training - Sign up now!
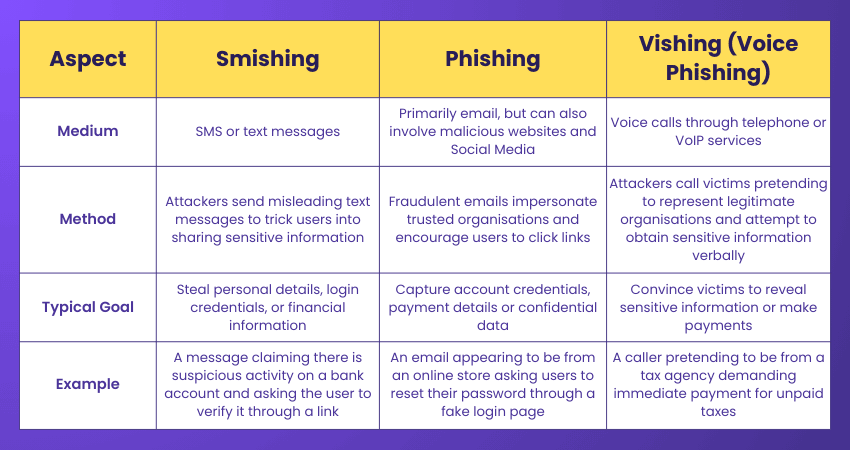
Phishing vs Vishing vs Smishing
Here are the main distinctions between Phishing, Vishing and Smishing:
Examples of Smishing Scams
As mentioned above, Smishing attacks appear in many forms, but their primary objective is always the same: to obtain sensitive personal or financial information. Let’s look at some common examples of smishing scams:
1) Bank Impersonation Texts
In these scams, attackers send text messages pretending to be from a bank. The message may warn about suspicious activity or request account verification. Victims may end up sharing personal details, such as their Social Security number, or even lose significant amounts of money.
2) Fake Prize or Gift Texts
Also known as sweepstakes scams, these messages claim that the recipient has won a prize or gift. The message usually includes a link to claim the reward, but victims are often asked to pay a small fee or provide financial details, which can lead to fraudulent charges.
3) Delivery Notification Scams
Fraudsters send messages that seem to come from delivery companies, claiming there is an issue with a package or shipment. When recipients click the provided link to track or confirm the delivery, they are directed to a fake page that requests payment or sensitive information.
4) Phony Job Offer Scams
Job seekers may receive text messages about attractive job opportunities. These unsolicited offers are often scams where the sender claims they need personal or banking information for background checks or payment setup. But the truth is, their goal is to steal money or personal data.
Conclusion
Smishing may arrive as a simple text, but its impact can be anything but small. With a proper understanding of What is Smishing, recognising the signs, understanding the common tactics and staying alert, you can stop these scams before they start. With smart habits and the right precautions, your phone becomes a safer space where messages stay meaningful and cybercriminals stay locked out.
Outsmart the Hackers and upgrade your career with our Certified Cyber Security Professional (CCS-PRO) Course - Sign up now!
Frequently Asked Questions
What Happens if You Click on a Smishing Text?

Clicking on a smishing link may direct you to a fraudulent website that’s designed to steal personal and financial information. In some cases, it can also trigger the download of malicious software onto your device. This malware may allow attackers to access your data or perform unauthorised transactions.
How do I Stop Smishing Text Messages?

You can reduce smishing messages by blocking suspicious numbers, enabling spam filters on your phone, and avoiding sharing your number on untrusted websites. It’s also helpful to report scam messages to your mobile carrier and delete them without clicking any links or responding.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Courses, including the Certified Cyber Security Professional (CCS-PRO) Course, Cyber Security Risk Management and the Computer Forensics Foundation Training. These courses cater to different skill levels, providing comprehensive insights into Replay Attack.
Our IT Security & Data Protection Blogs cover a range of topics related to Smishing, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Cyber Security skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Certified Cyber Security Professional (CCS-PRO)
Certified Cyber Security Professional (CCS-PRO)
Fri 5th Jun 2026
Fri 28th Aug 2026
Fri 25th Sep 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


