We may not have the course you’re looking for. If you enquire or give us a call on +91-181-5047001 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

With cyber-attacks becoming more sophisticated; it’s crucial to stay one step ahead. According to a survey by the World Economic Forum, 81% of leaders feel more exposed or similarly exposed to cybercrime compared to last year. Are you equipped with the right Cyber Security Tools to protect your organisation from these ever-evolving threats?
Cyber Security Tools are vital for identifying vulnerabilities, preventing breaches, and ensuring compliance with industry standards. In this blog, we will explore the top tools that every organisation must know. These tools provide advanced threat detection, robust encryption, and comprehensive security solutions to safeguard your digital assets. Let’s delve into these tools and enhance our defence against cyber threats.
Table of Contents
1) What are Cyber Security Tools?
2) Top 10 Cyber Security Tools
3. Need for Cyber Security Tools
4. Types of Cybersecurity Tools and Why You Need Them
5. Benefits of Cyber Security Tools
6. Conclusion
What are Cyber Security Tools?
Cyber Security Tools help businesses identify, assess, and mitigate IT Security risks. The main objective of such tools is to secure the data, network, and systems. Organisations use these tools to maintain their privacy on the internet and safeguard their systems and data. Understanding the Importance of Cyber Security is essential, as IT security tools not only defend a firm's network, intellectual property, and systems from cyberattacks but also provide protection against cybercrimes like identity theft and password trafficking.
Top 10 Cyber Security Tools
Cyber Security solutions help to identify vulnerabilities, prevent attacks, and ensure compliance with security standards. Below are the top 10 such Cyber Security solutions that every organisation should consider implementing:

1) Kali Linux
Kali Linux is a widely used open-source cyber security platform, known for its extensive range of tools that support vulnerability assessment and network security testing. As highlighted by Lumifi Cyber, it includes hundreds of built-in tools, supports multiple environments, and is widely adopted for penetration testing and security auditing.
Its flexibility, open-source integration, and strong community support make Kali Linux suitable for professionals at different skill levels, while regular updates ensure it stays relevant for real-world cyber security challenges.Kickstart your forensic journey with Computer Forensics Foundation Training - Register today!
2) Wireshark
Wireshark is an open source, free network protocol analyser that allows security experts to examine network traffic in real time or when the packet has been captured. It assists in detecting abnormal activity by dissecting packets and formats of packets into an interpretable form.
Wireshark is popular to analyse network issues and study security breaches due to its ability to decode a wide range of protocols and provide visualisation of the flow of traffic.
3) Metasploit Framework
Metasploit Framework is an open-source penetration testing framework that is used to find and exploit vulnerabilities in systems and applications. It gives a modular architecture, allowing users to create exploits along with payloads to determine security risk adequately.
It is used by security experts to authenticate vulnerability discoveries and generate tailor-made security tests, which cover a wide range of target platforms and exploit modules.
4) KeePass
KeePass is an open-source password management application that is free and stores credentials in a strictly encrypted database, which may be accessed with a single master key. It helps to encrypt such high standards as AES-256, ChaCha20, and Twofish to secure the login information and notes.
KeePass is used by organisations and individuals to minimise password reuse, enhance access control through centralised management of complex and unique passwords.
5) Nikto
Nikto is an open-source webserver scanner which examines servers to investigate thousands of known security vulnerabilities, older versions, and improper configurations. It offers a fast method of determining vulnerabilities that can be used by attackers.
Nikto is a popular tool among security auditors despite its command-line interface which needs technical expertise, because it has a wide range of vulnerability coverage.
6) Nmap
Nmap (Network Mapper) is a free open-source utility that can be used to scan networks and hosts to identify services, open ports and possible vulnerabilities. It charts networks and assists in identifying unsecured or suspicious activity that needs to be investigated.
Security experts will Nmap as an initial assessment tool to learn more about the network topology to set up prior to more thorough auditing or penetration.
7) OpenVAS
OpenVAS is an open-source scanner tool that identifies security vulnerabilities in servers, services, and network-based systems. It performs simple and complex tests to bring out areas that require correction.
The tool helps in authenticated and unauthenticated checks which enable organisations to test internal and external security posture.
8) OSSEC
OSSEC is an open-source host based intrusion detection system which monitors and analyses real-time log data. It identifies threats by inspection of file integrity, registry changes, authentication logs and suspicious activities on cross-platform platforms.
Our security teams use OSSEC to have a centralised log monitoring, better incident detection and automatic alert in abnormal behaviour.
9) Security Onion
Security Onion is an open-source and free Linux distribution used to monitor security at the enterprise level, threat-hunt and log management. It incorporates the usage of Snort, Suricata, Zeek, and Elasticsearch as a complete analytical package.
Security Onion is used by organisations to gather, analyse and investigate security events and logs of systems to protect the networks with multi-layered detection.
10) VeraCrypt
VeraCrypt is a free open-source disk encryption software that provides an encrypted and secure disk volume on the storage medium to safeguard delicate information. It is compatible with robust encryption algorithms and is able to encrypt drives or partitions.
VeraCrypt is frequently used by users to protect the confidential files in laptops, desktops or removable media against unauthorised access.Transform your investigation skills with Digital Forensics Training - Join today!
Need for Cyber Security Tools
Malware, ransomware, phishing attacks, data breaches, are all types of cybersecurity threats that are on the increase and may have a devastating impact on individuals and organisations. This necessitates the need to employ efficient Cyber Security Tools that shield systems, networks and sensitive information against attack.
Good security tools assist in identifying and addressing vulnerabilities before they can be exploited as well as facilitate adherence to legal and regulatory policies, which contributes to maintenance of trust and elimination of financial damage.
Types of Cybersecurity Tools
Following are some of the key tools organisations use to protect systems, detect threats, and strengthen their overall security posture:
1) Network security monitoring tools: Trace network activity in order to prevent threats in real-time.
2) Vulnerability scanners: Get to know possible areas of weakness and point them out so that they are addressed at an early stage. Firewalls: Use firewalls to block malicious traffic and prevent unauthorised access to your networks.
3) Encryption tools: Protect and encrypt data in transit and at rest to make them inaccessible to the sensitive information should they be intercepted.
4) Antivirus software: Precludes and eliminates viruses, worms and the likes before they attach to devices.
5) Intrusion detection/prevention systems (IDS/IPS): Identify and block suspicious network and system activities.
6) Hacking tools: Recreate actual incursions to test and refine the effectiveness of your security defences.
Benefits of Cyber Security Tools
In recent years, Cyber Security has become essential for organisations to protect data and build secure IT systems. As cyber threats continue to evolve, strong Cyber Security practices help prevent attacks, reduce risks, and maintain business stability and competitiveness.
Cyber Security MCQs with Answers also support learning by strengthening understanding of key concepts and real-world security challenges. The following are some of the benefits of Cyber Security Tools.
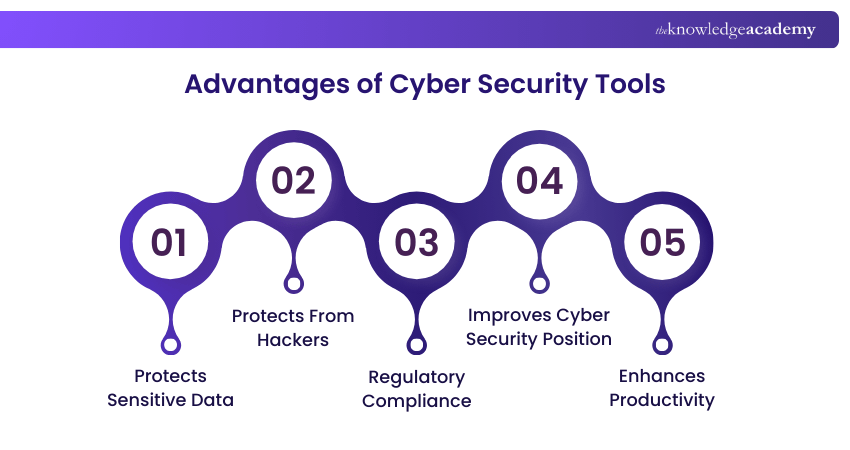
1) IT Security Tools encrypt data, adding another protection layer against cyber-attacks, and preventing significant damage from data leaks to the public or competitors.
2) These tools provide an added level of security, making it difficult for hackers and cybercriminals to breach systems and access data.
3) IT Security Tools help companies comply with laws and regulations like GDPR, avoiding severe penalties and maintaining a positive company image.
4) These tools enhance overall Cyber Security, offering comprehensive digital protection, quick response to threats, and tracking activities to prepare for cyber-attacks.
5) By preventing cyber-attacks and minimising downtime, IT Security Tools help maintain workflows and operations, leading to better performance and goal achievement.
Build a resilient defence against cyber-attacks with our Cyber Security Awareness Training – secure your place now!
Conclusion
In an era of constant digital threats, understanding the advantages and disadvantages of cybersecurity while equipping your organisation with the right Cyber Security Tools is essential. By leveraging these top 10 tools, you can strengthen your defenses, safeguard sensitive data, and stay ahead of cybercriminals. Enhance your Cyber Security strategy to maximise its benefits while addressing potential challenges, ensuring that your digital assets remain secure.
Elevate your expertise with the Certified Cyber Security Professional (CCS-PRO) Course – join now and become a Cyber Security Leader!
Frequently Asked Questions
What is the Difference Between Open-Source and Commercial Cybersecurity Tools?

Open-source tools are free, transparent, and can be customised, but usually rely on community support. Commercial tools are paid solutions that offer vendor support, regular updates, and advanced features, with less flexibility to modify the code.
Are Open-Source Cybersecurity Tools Effective?

Yes. Open-source tools can be effective when properly configured and maintained, as they help detect threats, protect systems, and improve security posture. SentinelOne highlights that choosing the right tools and using them correctly is key to defending against modern cyber threats.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Courses, including the Cyber Security Awareness Training, Cyber Security Risk Management Course, and Computer Forensics Foundation Training. These courses cater to different skill levels, providing comprehensive insights into Cyber Security Resume.
Our IT Security & Data Protection Blogs cover a range of topics related to Cyber Security Tools, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your IT Security and Data Protection skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Certified Cyber Security Professional (CCS-PRO)
Certified Cyber Security Professional (CCS-PRO)
Fri 24th Jul 2026
Fri 9th Oct 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


