We may not have the course you’re looking for. If you enquire or give us a call on +44 1344 203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

You start your workday as usual. You open your laptop, check your emails, and begin your tasks. But somewhere behind the scenes, a Hacker is quietly climbing the digital ladder, gaining admin access, and unlocking sensitive files without your knowledge. This is the silent danger of Privilege Escalation, where one small security gap can give attackers full control of your system.
In this blog, we go into Privilege Escalation: what it is, why it is dangerous, and how it works. You will learn the main types, common weak points attackers use, and clear ways to detect and stop these attacks. We also share real examples that show how one small mistake can cause a large cyber disaster.
Table of Contents
1) What is Privilege Escalation?
2) Why is Preventing Privilege Escalation Attacks Important?
3) How do Privilege Escalation Attacks Work?
4) Types of Privilege Escalation Attacks
5) Privilege Escalation Attack Vectors
6) How to Prevent Privilege Escalation Attacks?
7) How to Detect Privilege Escalation Attacks?
8) Examples of Privilege Escalation Attacks
9) Conclusion
What is Privilege Escalation?
A Privilege Escalation attack happens when a Hacker gets more access in a computer system than they should have. They do this by using mistakes made by people or problems in software and websites.
Once they get inside, they can move through the system to reach important files or data. This means someone who had little access can suddenly control much more. The damage can be small, like reading someone’s email, or very big, like locking up data with a virus. If no one notices the attack, it can stay hidden and cause serious problems later.
Why is Preventing Privilege Escalation Attacks Important?
For Hackers, Privilege Escalation is often a stepping stone to achieving larger goals. It allows them to infiltrate systems more deeply, maintain access for longer periods, and cause greater damage. What begins as a minor malware infection can quickly escalate into a severe data breach once higher-level privileges are obtained.
This elevated access enables attackers to:
a) Move laterally into other connected systems
b) Install additional malicious software
c) Modify or disable security settings
d) Access restricted apps or data
e) In severe cases, take full control of a system or network
When security teams suspect Privilege Escalation, immediate investigation is crucial. Warning signs may include unusual login patterns, the presence of malware on critical systems, or unexpected network activity.
How do Privilege Escalation Attacks Work?
A Privilege Escalation attack usually happens in several small steps:
a) Initial Access: The attacker first finds a way into the system, often through phishing, weak passwords, or software bugs.
b) Information Gathering: They look around the system to understand how it works and what accounts exist.
c) Finding Weak Points: The attacker searches for loopholes such as misconfigurations, unpatched software, or stored passwords.
d) Exploiting the Weakness: They use tools or scripts to gain more privileges.
e) Maintaining Access: Once they get higher access, they often create new accounts or install backdoors to stay inside the system.
Gain hands-on experience with real-world ethical hacking scenarios. Join our Ethical Hacking Essentials Certification now!
Types of Privilege Escalation Attacks
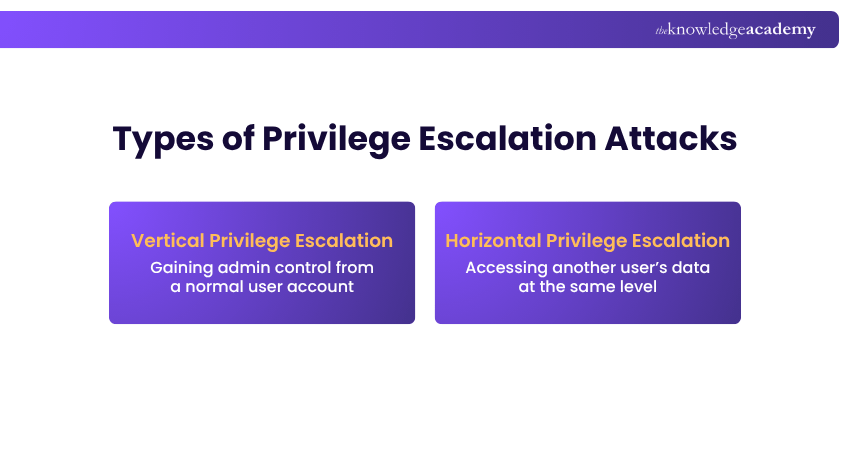
There are two types of Privilege Escalation attacks, vertical and horizontal. Both involve Hackers trying to gain access to data or areas they are not authorised to enter, but they do so in different ways.
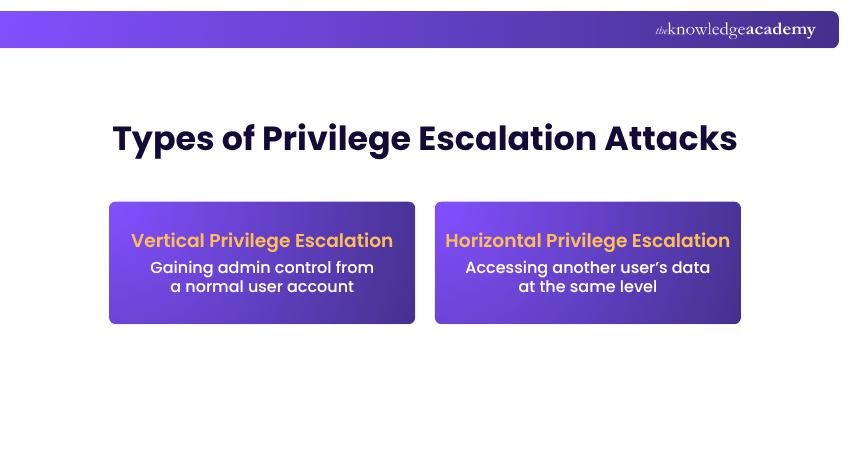
1) Vertical Privilege Escalation
In this type of attack, the hacker moves from an ordinary user account to an administrator or root-level account. This elevated access grants them full control over the system, allowing them to change configurations, install programs, add or remove users, and delete critical files.
2) Horizontal Privilege Escalation
In a horizontal Privilege Escalation, attackers use stolen logins to access another user’s data at the same level. Unlike vertical escalation, which seeks higher control, this targets peer accounts. Strong security, safe logins, and activity monitoring help prevent such attacks.
Privilege Escalation Technique
A Privilege Escalation technique is a method attackers use to gain higher access in a system. They find a weakness and then use it to move from low-level access to more powerful rights.
Common techniques include:
a) Exploiting Software Bugs: Using flaws in programs or operating systems
b) Password Cracking: Guessing or stealing admin passwords
c) DLL Injection: Placing malicious files into trusted system folders
d) Kernel Exploits: Attacking the core of the operating system
e) Abusing Weak Permissions: Changing files or processes that are not properly protected
Privilege Escalation Attack Vectors
Privilege Escalation does not occur by a single method. Attackers use different paths, known as attack vectors, to gain higher access. Here are the most common ones:
1) Malware
Malware is malicious software that can help attackers take control of systems. Once installed, malware can create backdoors, steal credentials, and exploit system weaknesses to obtain elevated privileges.
For example, some malware automatically runs with admin rights after infecting a system, giving attackers instant control.
2) Social Engineering
Social Engineering attacks mislead people into giving away information or performing risky actions.
For example, an employee may be fooled into downloading a “security update” that is a malicious file. Once run, the file gives Hackers higher access rights.
3) Credential Exploitation
Attackers use stolen or weak passwords to move from a regular account to higher access. They hunt for saved admin passwords, tokens, or shared credentials. Methods include password reuse, brute force, and memory scraping.
For example, an attacker finds an employee’s password on a breach site, tries it on the company portal, gains a user account, then finds saved admin credentials and expands access.
4) Vulnerabilities and Exploits
A vulnerability is a flaw in software or system design. Attackers exploit these flaws to run commands or gain admin rights.
For example, an unpatched operating system may allow Hackers to run special code that gives them control. Keeping your software updated is one of the best ways to close such gaps.
5) Misconfigurations
Poorly configured systems make unauthorised access easier. Weak security settings, open network ports, or excessive administrative permissions can all be exploited.
For example, if a folder that contains sensitive files is open to “Everyone,” a Hacker can easily read or change those files.
Understand strategies for enterprise wireless and cloud network security. Join our Certified Network Defender Certification now!
How to Prevent Privilege Escalation Attacks?
The best way to stop Privilege Escalation is to reduce the chances of it happening in the first place. Below are some simple but effective steps:
a) Follow the Principle of Least Privilege (PoLP)
Give users only the access they truly need for their jobs. Do not give admin rights unless required.
b) Use Multi-factor Authentication (MFA)
Even if a Hacker gets a password, MFA can stop them from logging in without the second step of verification.
c) Keep Systems Updated
Always install software and security updates. Many attacks happen because systems are not patched.
d) Strong Password Policies
Use long, complex passwords and change them regularly. Avoid reusing passwords across accounts.
e) Limit Use of Admin Accounts
Do not use admin accounts for everyday tasks like browsing or emailing. Separate admin and user activities.
f) Disable Unused Accounts
Remove or disable accounts that are no longer needed. Old accounts are often easy targets for attackers.
g) Train Employees
Most attacks start with human error. Regular training helps staff understand phishing, scams, and secure behaviour.
How to Detect Privilege Escalation Attacks?
Even with strong preventive measures, it’s crucial to detect suspicious activity early. Identifying warning signs promptly can stop attackers before they gain full control. Here are some effective ways to detect Privilege Escalation attacks:
1) Audit System Logs
Regularly reviewing system logs helps uncover unusual activities such as repeated failed logins, unfamiliar commands, or unexpected privilege changes. Frequent log audits make it easier to trace who accessed what and when, providing an early warning of potential breaches.
2) Anomaly Detection Tools
Anomaly detection tools monitor network behaviour and flag deviations from normal patterns. For instance, a sudden change in user roles or unusual access hours could indicate an attempt to gain elevated privileges. These tools provide early alerts that help security teams act quickly.
3) User and Entity Behaviour Analytics (UEBA)
UEBA tools study normal user activity and alert you when something looks different, such as unusual login times or access patterns. They can highlight insider threats or attackers using stolen accounts.
4) Password Monitoring
Enable alerts for unauthorised password changes or resets. These can indicate that an attacker is attempting to maintain access after gaining higher privileges. Monitoring also ensures users follow strong password policies, reducing the risk of compromise.
5) Intrusion Detection Systems (IDS)
IDS tools continuously scan for patterns of known attacks, such as buffer overflows or SQL injections. They help identify unauthorised access attempts before significant damage occurs. When paired with real-time alerts, IDS allows security teams to respond swiftly and safeguard critical systems.
Acquire the needed skills for implementing cloud security. Join our Certified Cloud Security Engineer Certification now!
Examples of Privilege Escalation Attacks
Privilege Escalation attacks have happened to many big organisations. Here are a few real-world Privilege Escalation attack examples:

a) Exploiting Software Bugs
Hackers use mistakes in software or operating systems to get more control. For example, a small error in a program might let a normal user run admin commands and control the whole system.
b) Misconfigured Permissions
Sometimes files or folders have the wrong access settings. Attackers can use this to open, change, or delete data that should be protected.
c) Stolen Credentials
If people share or reuse passwords, Hackers can steal them through fake emails or data leaks. Once inside, they look for admin passwords or other accounts to gain higher access.
d) Malware Infections
Some malware is made to increase user access automatically. Once it’s installed, it can turn off security tools, create admin accounts, or hide harmful files.
e) Unpatched Systems
When systems don’t have the latest updates, Hackers can use old security flaws to get more access. Updating software often helps stop these attacks.
f) Social Engineering Attacks
Hackers trick users into giving away their logins or downloading fake updates. Once inside, they use those accounts to quietly reach higher access levels.
Conclusion
Understanding Privilege Escalation is key to keeping systems secure. Even small gaps, like weak passwords or missed updates, can give Hackers powerful control. Regular monitoring, timely patching, and user awareness are simple yet effective ways to stop such attacks. Staying alert helps protect data and keep networks safe from hidden threats.
Acquire familiarity with encryption technologies and practice. Join our EC – Council Certification now!
Frequently Asked Questions
How Do I Know If I Have Elevated Privileges?

You can check by seeing what actions your account can perform. If you can install software, change settings, or manage other accounts, you likely have elevated privileges. Normal users usually cannot do these things.
What is the Difference Between Privileged and Elevated Access?

Privileged access means having high-level permissions, such as system admin rights. Elevated access means temporarily raising your permission to perform a special task. For example, an IT employee may use elevated access to install software, but they return to normal access afterwards.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000 online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.;
Alongside our diverse Online Course Catalogue, encompassing 19 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and;Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various EC – Council Certification, including the Certified Ethical Hacker (CEH) Certification, Ethical Hacking Essentials Certification, and the Ethical Hacking Core Skills Certification. These courses cater to different skill levels, providing comprehensive insights into Hacking.
Our IT Security & Data Protection Blogs cover a range of topics related to Privilege Escalation, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your IT Security & Data Protection skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Certified Ethical Hacker (CEH) Certification
Certified Ethical Hacker (CEH) Certification
Mon 8th Jun 2026
Mon 17th Aug 2026
Mon 19th Oct 2026
Mon 23rd Nov 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


