 To help and support our clients we are providing a limited number of 250 daily discount codes. Hurry, first come, first served!
To help and support our clients we are providing a limited number of 250 daily discount codes. Hurry, first come, first served!
CISSP Courses FAQs
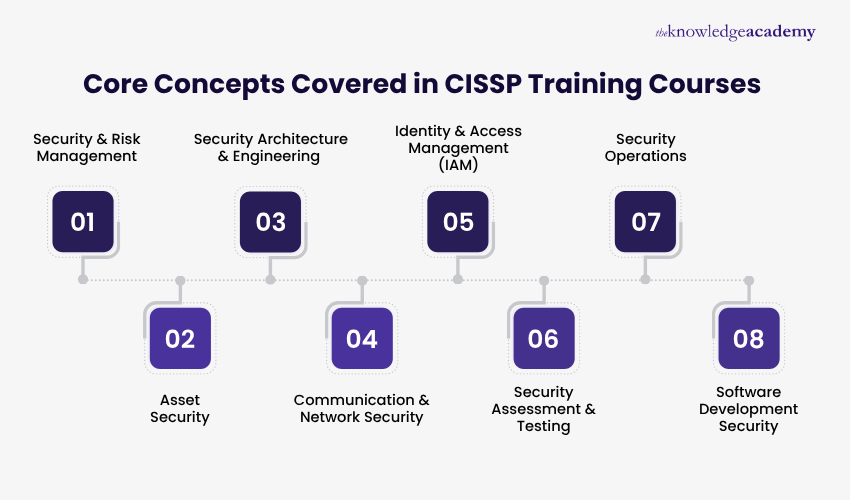
CISSP (Certified Information Systems Security Professional) is a globally recognised standard in Information Security. It defines essential practices across areas such as risk management, asset security, and software development security.
Yes, CISSP Training Courses are highly in demand by professionals worldwide. Organisations increasingly rely on skilled delegates to manage cyber security risks and safeguard critical information systems.
CISSP Courses opens opportunities in senior security roles across industries, including finance, healthcare, government, and technology. It equips delegates to handle complex security challenges effectively.
An understanding of Information Security principles, networking, and risk management is recommended but not compulsory. Familiarity with IT systems and security frameworks will help delegates to maximise course outcomes.
Professionals aiming for leadership roles in cyber security, such as Security Managers, Auditors, Consultants, and IT Engineers, will benefit most.
Yes, the course aligns with a widely recognised information security framework. Completing it demonstrates competence that is respected by employers across more than 180 countries.
Delegates gain knowledge of critical security domains, develop strategic risk management skills, and enhance career readiness for senior information security roles with CISSP Training.
The key requirements for the CISSP Course are foundational experience in IT and security, and a clear understanding of networking, systems, and risk principles. This ensures delegates can fully engage with advanced domain topics.
By providing comprehensive domain knowledge and strategic security skills, the CISSP Training prepare delegates for leadership roles, higher responsibilities, and increased employability in information security.
Industries such as banking, government, healthcare, consulting, cloud services, and global IT rely on advanced security expertise to protect systems, data, and operations.
Our CISSP Training is delivered through instructor-led classroom sessions, live virtual training, and online self-paced learning options. This flexible delivery allows professionals to choose a format that fits their schedule and learning preferences.
Security operations are taught through practical scenarios, risk mitigation techniques, and management strategies. Delegates learn how to monitor, detect, and respond to security incidents effectively.
Security assessment and testing are significant because they help identify vulnerabilities and evaluate the effectiveness of security controls. This training builds the ability to assess risks, validate security measures, and strengthen organisational security posture through structured testing practices.
Identity and access management in this CISSP Training focuses on controlling user privileges, authentication, and authorisation. Delegates gain skills to protect sensitive data and enforce robust security policies.
The Knowledge Academy stands out as a prestigious training provider known for its extensive course offerings, expert instructors, adaptable learning formats, and industry recognition. It's a dependable option for those seeking this training.
Please see our CISSP Courses available in Honduras
The Knowledge Academy is one of the Leading global training provider for CISSP Courses.
The training fees for CISSP Courses in Honduras starts from $4695

Why we're the go to training provider for you

Best price in the industry
You won't find better value in the marketplace. If you do find a lower price, we will beat it.

Trusted & Approved
Recognised by leading certification bodies, we deliver training you can trust.

Many delivery methods
Flexible delivery methods are available depending on your learning style.
High quality resources
Resources are included for a comprehensive learning experience.




"Really good course and well organised. Trainer was great with a sense of humour - his experience allowed a free flowing course, structured to help you gain as much information & relevant experience whilst helping prepare you for the exam"
Joshua Davies, Thames Water



Looking for more information on CISSP Courses
 Top 42+ CISSP Interview Questions with Sample Answers
Top 42+ CISSP Interview Questions with Sample Answers CISSP Salary: Boost Your Cyber Security Career
CISSP Salary: Boost Your Cyber Security Career What is Information Security: Definition, Policy, and Principles
What is Information Security: Definition, Policy, and Principles CISM vs CISSP: Which Security Certification is Best for You in 2026
CISM vs CISSP: Which Security Certification is Best for You in 2026 Prepare for CISSP Exam: Cost & Essential Tips for 2025
Prepare for CISSP Exam: Cost & Essential Tips for 2025
















 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


