We may not have the course you’re looking for. If you enquire or give us a call on + 1-866 272 8822 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Imagine your business faces a cyber threat, and you’re not sure what to do. That’s where the ISO 27005 Risk Assessment Process can help. It gives you a simple way to find, understand, and deal with security risks before they become big problems. Whether you're a small company or a large one, this process helps protect your important data and keeps your systems safe. It’s like having a smart plan in place to stay one step ahead of trouble. In this blog, we will discuss the key components of ISO 27005 and how to implement the process effectively. Let’s get started.
Table of Contents
1) Understanding ISO 27005
2) Key Components of ISO 27005 Risk Assessment Process
3) Implementing ISO 27005 Risk Assessment
4) What is the Risk Assessment Process ISO 27005?
5) Conclusion
Understanding ISO 27005
ISO 27005 is a standard that gives guidance on how to manage risks related to Information Security. It supports the main ISO 27001 standard by helping organisations identify, assess, and handle risks that could affect their data. This standard is useful for any business that wants to keep its information safe.
ISO 27005 helps businesses understand where their risks are and what steps they can take to reduce them. For example, a company may find that staff using weak passwords is a risk. Using ISO 27005, they can assess how serious this risk is and decide to set stronger password rules and staff training. This makes the system more secure and avoids problems like data leaks.
Key Components of ISO 27005 Risk Assessment Process
The critical components of the ISO 27005 Risk Assessment Process form the foundation for a systematic and comprehensive approach to managing Information Security Risks. These components work together to identify, analyse, evaluate, and treat risks effectively:
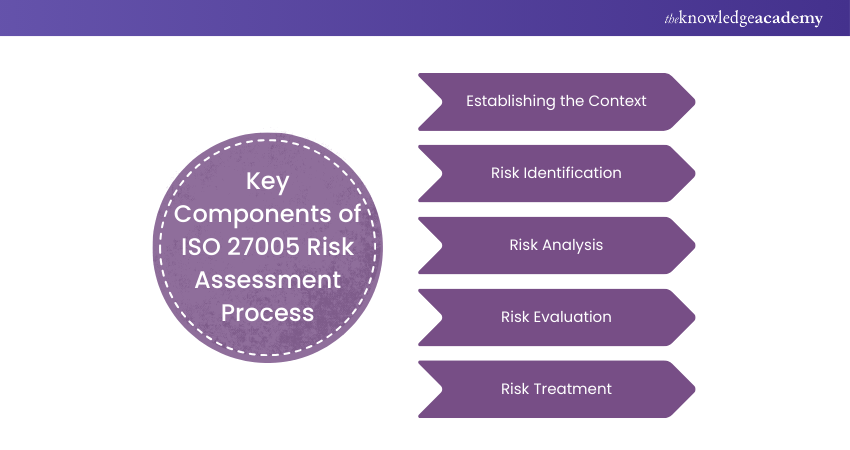
a) Establishing the Context:This initial step sets the stage for the Risk Assessment Process. Organisations define the scope, objectives, and context of the assessment. It involves specifying the Risk Assessment methodology, criteria for risk acceptance, and the overall framework for Risk Management.
b) Risk Identification: Here, organisations identify assets, threats, and vulnerabilities within their scope. Threats encompass potential sources of harm, while vulnerabilities are weaknesses that those threats may exploit. Comprehensive identification is crucial to understanding the landscape of potential risks.
c) Risk Analysis: Once identified, risks undergo examination to determine their potential impact and likelihood. Impact refers to the harm that could result from a risk materialising, while likelihood assesses the probability of it happening. This analysis helps prioritise risks and focus resources on the most critical areas.
d) Risk Evaluation: In this step, organisations combine the risk analysis results to evaluate the overall level of risk. Typically, this is done by assigning risk scores or ratings. The evaluation assists in making informed decisions about which risks need immediate attention and which can be managed over time.
e) Risk Treatment:Finally, organisations develop risk treatment plans. These plans outline strategies to mitigate, transfer, or accept risks. Mitigation measures aim to reduce the risk's impact or likelihood, while risk transfer involves mechanisms like insurance. Acceptance acknowledges that some risks may be within acceptable tolerances or that the cost of mitigation outweighs the potential harm.
Learn the benefits of risk assessment with our ISO 27005 Lead Implementer Course – Join today!
Implementing ISO 27005 Risk Assessment&
Here are the main steps to follow when implementing ISO 27005 risk assessment:

Define the Scope
This step sets the limits of what the risk assessment will cover. It includes deciding which parts of the business, systems, or data will be checked. A clear scope helps avoid confusion and keeps the work focused. It’s the first step to making a useful risk plan.
a) Sets clear focus for risk assessment
b) Helps teams know what areas to review
c) Avoids wasting time on unrelated parts
Identify Assets
In this step, the team makes a list of important things to protect, like data, software, hardware, or people. These are called assets. Knowing what is valuable helps decide what needs more protection. This step is important to stop loss or damage.
a) Finds important things to protect
b) Helps decide what risks matter most
c) Makes it easier to plan protection
Identify Threats and Vulnerabilities
Here, the team looks at what could go wrong (threats) and what weak spots exist (vulnerabilities). A threat could be a hacker, and a vulnerability could be weak passwords. This helps to understand how the business could be harmed.
a) Finds possible dangers to the business
b) Spots weak points that need fixing
c) Helps plan how to stop attacks
Assess Risks
Now, the team checks how likely each risk is and how bad the damage could be. Risks are ranked based on how serious they are. This helps decide which ones need action first. It’s a way to focus on the biggest problems.
a) Measures how risky each threat is
b) Helps pick which problems to fix first
c) Saves time by focusing on major issues
Develop Risk Treatment Plans
This step is about choosing what to do about each risk. You can reduce, avoid, share, or accept the risk. The team picks the best way to handle each one. It turns ideas into real actions.
a) Decides how to manage each risk
b) Creates plans to lower or avoid danger
c) Makes sure action is taken, not just talk
Monitor and Review
Risks can change, so it’s important to keep checking. The team looks at what’s working and what needs to be updated. Reviews help keep the risk plan useful and strong. It’s a cycle that keeps going.
a) Keeps security plans updated
b) Finds new risks early
c) Improves the risk plan over time
Learn to lead audit teams with our ISO 27005 Lead Auditor Training – Join today!
What is the Risk Assessment Process ISO 27005?
The ISO 27005 Risk Assessment Process is a way to find and manage risks that could harm your business data. It starts by identifying important assets, possible threats, and weak areas. Then, each risk is checked to see how likely it is to happen and how bad the effect would be. This helps businesses take the right steps to stay safe and protect their information.
Develop practical auditing skills for effective risk management with our ISO 27005 Internal Auditor Course – Sign up now!
Conclusion
The ISO 27005 Risk Assessment Process is more than just following rules — it is a smart way to protect your information. It helps organisations find risks early, understand them, and take action before they cause problems. In today’s world of growing cyber threats, ISO 27005 gives you the strength to stay prepared and respond quickly. Using this process as part of your security plan helps keep your data safe and builds trust with your team and customers.
Learn strategies to improve security measures with ourISO 27005 Foundation Course – Join today!
Frequently Asked Questions
What is ISO 27001 Risk Assessment?

ISO 27001 Risk Assessment is the process of finding and checking risks that could harm a company’s information. It helps to understand what needs protection and what could go wrong. This process allows the business to take steps to reduce or control those risks.
What are the 5 C's of Risk Assessment?

Here are the 5 C’s:
a) Context
b) Causes
c) Consequences
d) Controls
e) Communication
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various ISO 27005 Courses, including ISO 27005 Foundation Course, ISO 27005 Lead Auditor Course and ISO 27005 Lead Implementer Course. These courses cater to different skill levels, providing comprehensive insights into Risk Retention and Risk Acceptance in ISO 27005.
Our IT Security and Data Protection Blogs cover a range of topics related to ISO 27005, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your IT Security and Data Protection skills, The Knowledge Academy's diverse courses and informative blogs have you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.






 Top Rated Course
Top Rated Course






 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


