We may not have the course you’re looking for. If you enquire or give us a call on +34 932716793 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

While the digital landscape brings us all closer than ever through lightning-fast connectivity, the darker side of such interconnectivity rears its ugly head in the form of cyber threats. The scary thing is that these threats evolve quickly and grow smarter. That's why it’s important that making resilience, not just defence, is the new digital imperative. This is where the Cyber Resilience Framework comes in.
A Cyber Resilience Framework goes beyond prevention. It helps organisations prepare for, respond to and recover from cyber incidents. This blog explores this topic in detail, highlighting its key components, benefits, challenges and more. So read on and turn disruption into an opportunity to help your organisation grow smarter, faster and more secure!
Table of Contents
1) Understand Cyber Resilience
2) What are Cyber Resilience Frameworks?
3) Why You Need a Cyber Resilience Plan?
4) Key Components of a Cyber Resilience Framework
5) Examples of Cyber Resilience Frameworks
6) Steps to Implement a Cyber Resilence Framework
7) Implement a Cyber Resilience Framework
8) Benefits of a Cyber Resilience Framework
9) Improving the Cyber Resilience Framework
10) Cyber Resilience Frameworks and Regulatory Compliance
11) Cyber Resilience Best Practices
12) Challenges in Achieving Cyber Resilience
13) Future of Cyber Resilience
14) What are the Three Rs of Cyber Resilience?
15) Is COBIT a Cyber Security Framework?
16) Conclusion
Understand Cyber Resilience
Cyber Resilience is now a key part of modern Cyber Security. Instead of just trying to stop cyberattacks, it accepts that attacks may still happen. The goal is to help organisations stay strong, respond quickly, and recover well after an attack. It uses different strategies, tools, and plans to reduce damage and keep operations running, even when problems occur. Cyber Resilience focuses on bouncing back rather than only blocking threats.
Cyber Security and Cyber Resilience may sound similar, but they mean different things. Cyber Security focuses on stopping attacks before they happen using tools like firewalls and encryption. Cyber Resilience, however, goes further. It accepts that some attacks may still happen and helps the organisation recover quickly, reduce damage, and keep things running with minimal disruption
What are Cyber Resilience Frameworks?
Cyber Resilience Frameworks give clear guidance and best practices to help organisations improve their ability to prevent, handle, and recover from cyber threats. They don’t give strict rules or promote specific tools but offer useful advice to build strong, flexible defences. These frameworks focus on areas like managing risks, responding to attacks, keeping the business running, and recovering after problems.
These frameworks guide organisations to build stronger systems that help stop cyberattacks and recover quickly if one happens. These frameworks can be adjusted to match each organisation’s needs and goals. Customising them makes sure the protection fits real risks. When these practices are added to the security plan, they help keep assets safe, maintain customer trust, and support long-term stability.
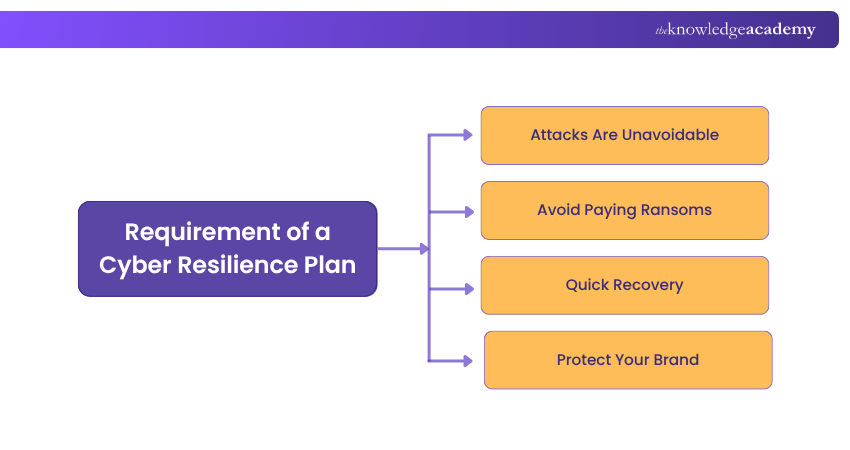
Why You Need a Cyber Resilience Plan?
Cyber resilience plans are no longer optional; they’re essential. With cyberattacks on the rise, it's clear that strong security alone isn’t enough. Here’s why every business must have a cyber resilience plan:
Key Components of a Cyber Resilience Framework
The Cyber Resilience Framework, designed to weather the storm of cyber incidents, comprises a strategic amalgamation of critical components that fortify an organisation's ability to respond to and recover from cyberattacks. Let's explore these pivotal components in detail:
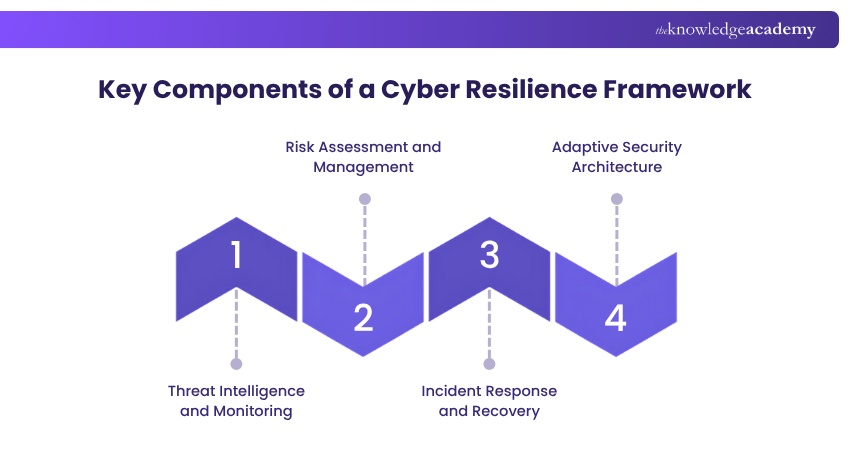
Threat Intelligence and Monitoring
Proactive identification of potential threats is at the core of Cyber Resilience. It constantly monitors network activities and digital environments to detect anomalies, vulnerabilities, and signs of compromise. Threat intelligence leverages data from various sources to predict and counter emerging threats, enabling organisations to take pre-emptive actions.
Risk Assessment and Management
Understanding an organisation's digital vulnerabilities and potential risks is paramount for effective Cyber Resilience. Comprehensive risk assessments evaluate the organisation's assets, openness, and the potential impact of cyber incidents. This information aids in prioritising resources and efforts toward safeguarding critical assets.
Incident Response and Recovery
An integral aspect of Cyber Resilience is the development of comprehensive incident response and recovery plans.
1) Developing a Response Plan: A well-defined response plan outlines roles, responsibilities, communication protocols, and containment strategies that minimise the damage of a cyber incident.
2) Business Continuity Measures: It ensures critical functions can continue even during an incident, minimising disruption to operations and customer service.
Adaptive security architecture
To Improve Cyber Resilience, organisations must architect their digital infrastructure with adaptability. Adaptive security architecture focuses on creating multiple layers of defence that can adjust to emerging threats and attacks.
Examples of Cyber Resilience Frameworks
NIST Cyber Security Framework
Developed by the National Institute of Standards and Technology (NIST), this framework offers a flexible, risk-based approach to managing and mitigating cyber risks. It emphasises five core functions: Identify, Protect, Detect, Respond, and Recover.
ISO 27001
Part of the ISO 27000 series, ISO 27001 focuses on establishing an organisation’s Information Security Management System (ISMS). It provides a systematic approach for managing information security risks, including cyber threats.
Cyber Resilience Review (CRR)
Created by the Department of Homeland Security (DHS), the CRR is a no-cost, voluntary assessment that evaluates an organisation’s operational resilience and Cyber Security practices. It helps organisations identify and prioritise areas needing improvement.
Cyber Security Maturity Model Certification (CMMC)
The Cyber Security Maturity Model Certification (CMMC) is a program created by the Department of Defense (DoD) to strengthen Cyber Security across the Defense Industrial Base (DIB) and safeguard sensitive data.
Steps to Implement a Cyber Resilence Framework
Here are five key steps to building a powerful cyber resilience framework:

1) Conduct a Comprehensive Risk Assessment: Start by looking at all your digital systems and finding where you might be vulnerable. Consider these points:
a) Make a list of your important systems, data, and third-party tools.
b) Check for weak spots like outdated software or exposed passwords.
c) Use trusted security standards like NIST or ISO 27001 to help guide you.
2) Implement Robust Security Controls: Once you know your risks, put protections in place. Consider these points:
a) Use tools to hide and manage sensitive data like passwords and API keys.
b) Monitor your network to catch threats quickly.
c) Make sure your software and hardware are set up securely.
d) Use data protection tools to keep important information safe.
e) Protect all your company's devices with real-time security tools.
3) Develop Detection and Response Capabilities: Have tools and plans in place so you can act fast during an attack. Consider these points:
a) Use automated tools that connect and manage your security systems.
b) Actively look for threats, not just wait for alerts.
c) Make clear plans for how to respond if something goes wrong.
d) Monitor your systems regularly to catch unusual behaviour early.
4) Minimise Disruption and Maximise Recovery: Prepare for what to do if an attack happens. Consider these points:
a) Create a business continuity plan, so essential work can continue
b) Back up your data and set up systems to recover it quickly
c) Practise recovery steps with drills to make sure your team is ready
5) Foster a Culture of Continuous Improvement: Cyber threats change, so your plans should too. Consider these points:
a) After an attack, review what happened and how to do better next time.
b) Use feedback to improve your security.
c) Train your staff regularly on how to stay safe online.
Build resilient defence strategies with our Certified Cyber Security Professional Training - Sign up now!
Implement a Cyber Resilience Framework
Organisations increasingly recognise the need to shift from a reactive cybersecurity stance to a proactive and resilient approach. Implementing a robust Cyber Resilience Framework is the cornerstone of this strategic shift, empowering organisations to not only withstand cyberattacks but also respond swiftly and recover effectively.
Benefits of a Cyber Resilience Framework
Implementing a Cyber Resilience Framework offers numerous benefits to organisations across various industries, including:
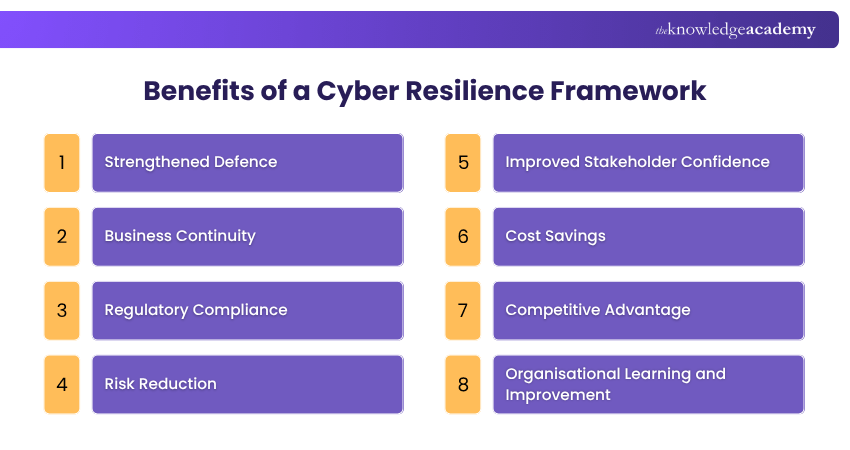
a) Strengthened Defence: A Cyber Resilience Framework enhances your organisation’s ability to identify and respond to cyber threats, reducing the likelihood of successful attacks.
b) Business Continuity: By incorporating business continuity planning into it, a Cyber Resilience Framework ensures minimal disruption to operations during and after a cyberattack.
c) Regulatory Compliance: Many industries, including finance, manufacturing and pharmaceuticals are subject to strict regulatory requirements. A Cyber Resilience Framework helps meet these obligations and spotlight the commitment to Cyber Security.
d) Risk Reduction: A Cyber Resilience Framework enables organisations to proactively address potential risks by identifying and prioritising vulnerabilities and threats. This proactive approach helps implement preventive measures to mitigate the likelihood of successful attacks.
e) Improved Stakeholder Confidence: Showcasing a robust Cyber Resilience Framework instils confidence in stakeholders, including customers, partners and investors. It showcases your organisation’s commitment to defending sensitive information, which cultivates trust and credibility in the marketplace.
f) Cost Savings: Being invested in Cyber Resilience can result in significant cost savings in the long run. Organisations can avoid financial losses associated with disrupted operations, data breaches, and regulatory penalties by minimising the effect of cyber incidents and reducing downtime.
g) Competitive Advantage: A well-established Cyber Resilience Framework provides a competitive edge in the marketplace. It demonstrates your organisation’s commitment to Cyber Security, giving you a much-needed advantage over competitors and positioning you as a reliable partner.
h) Organisational Learning and Improvement: Implementing a Cyber Resilience Framework involves continuously monitoring, evaluating, and improving Cyber Security measures. This process facilitates organisational learning, enabling you to adapt and strengthen defences based on evolving threats and industry best practices.
Improving the Cyber Resilience Framework
Cyber Resilience Frameworks provide managers with a reliable, standardised, and systematic approach to mitigating cyber risks, regardless of the complexity of the environment. These frameworks need continual improvement, and the following five activities are essential for enhancing a Cyber Resilience Framework.
1) Identification of a Top Management Coordinator
Assigning a senior manager responsible for Cyber Resilience ensures that there is a champion for Cyber Resilience at the C-suite level. This senior manager will educate board members and secure their support for investment in incident response automation tools and the development of a comprehensive Cyber Resilience Framework.
2) Nurturing a Culture of Cyber Resilience
Leaving Cyber Resilience solely to the security team is a common mistake. If only a few people has a grasp on the systems and how to protect them, the security posture weakens as the company grows. All employees should adopt a Cyber Resilience mindset, knowing how to identify and detect malware and phishing threats and understanding the consequences of data breaches.
Leaders must promote teamwork, open communication, and knowledge sharing across teams. Through ongoing education and peer learning, an enterprise can instil a security-focused culture that serves as a strong foundation for the Cyber Resilience Framework.
3) Creating Formal Cyber Security Policies
A strong risk management policy is a vital component of a Cyber Resilience Framework. Documenting proven security processes as official guidelines provides employees with a reliable set of protocols to follow, strengthening the organisation’s security posture.
4) Making Cyber Resilience a Priority at Board Meetings
Incident response strategies and Cyber Resilience Frameworks are dynamic, evolving assets. They require regular review and updates. Security issues should not be confined to a single department.
Enterprise leaders must regularly consult with key stakeholders on security policies, ensuring the organisation maintains a high level of Cyber Resilience and is prepared to respond to and manage threats.
5) Offering Career Paths for Security Professionals
Top security professionals seek continuous learning and career growth opportunities. Without clear pathways for advancement, they may leave for other opportunities. By investing in ongoing training and career development, organisations can cultivate a loyal, highly skilled workforce of security professionals, ensuring long-term engagement and expertise within the company.
Strengthen your defence-ready IT skillset with our Introduction to System and Network Security Training- Join now!
Cyber Resilience Frameworks and Regulatory Compliance
Cyber resilience Frameworks are essential for achieving regulatory compliance across various industries. These frameworks provide structured guidelines and best practices to improve an organisation's ability to prevent, withstand, and recover from cyber threats. Consider these points:
1) Cyber Resilience Frameworks provide clear security guidelines that support compliance with laws like GDPR, HIPAA, and industry-specific regulations.
2) These frameworks help businesses manage risks, respond to incidents, and recover operations, which are core requirements for many regulatory standards.
3) Adopting a framework shows regulators that an organisation takes Cyber Security seriously and is prepared for potential threats.
4) Regular assessments and updates built into frameworks ensure businesses stay aligned with changing legal and regulatory expectations.
5) Strong cyber resilience prevents legal penalties and builds trust amongst investors, customers and other key stakeholders.
Cyber Resilience Best Practices
Achieving Cyber Resilience requires balancing people, processes, and technology. Organisations often mistakenly rely too heavily on technology, neglecting the importance of skilled people and well-designed processes. Ensuring Cyber Resilience involves integrating all three components effectively.
a) People: Often the weakest link in the context of Cyber Security, every employee must understand their roles and responsibilities. Organisations should provide role-specific Cyber Security training, ensure top management supports and reviews Cyber Resilience initiatives, educate board members on relevant Cyber Security terms, and establish specialist groups to monitor risks.
b) Processes: Strong governance and processes are crucial. Best practices include maintaining regulatory compliance, validating data controls, agile policy adjustments, using scenario-based strategies for preparedness, and devising effective communication plans. Comprehensive documentation, centralised asset management, continuous monitoring, and deploying various controls are essential measures.
c) Technology: As a key enabler, organisations should invest in response and recovery capabilities, update technologies based on industry standards, adopt automation, create air-gapped copies of critical assets, and leverage advanced technologies like deception to enhance Cyber Resilience.
Own the risk before it owns you! Sign up for our Cyber Security Risk Management Course now!
Challenges in Achieving Cyber Resilience
Achieving cyber resilience is vital for helping organisations recover from cyberattacks. However, some common challenges can make this difficult. Here are a few key obstacles and how they affect cyber resilience:
1) Lack of Awareness: Some organisations don’t fully understand the importance of cyber resilience, so they don’t prepare properly for possible threats.
2) Complex IT Systems: Today’s IT setups can be very complicated, which makes it hard to spot weak areas and apply strong security.
3) Limited Resources: Not having enough money or staff can make building and maintaining a strong cyber resilience plan tough.
4) Changing Threats: Cyber threats keep evolving, so businesses must regularly update their defences to stay protected.
5) Risks from Third Parties: Working with outside vendors can bring new risks if those partners don’t follow good security practices.

Future of Cyber Resilience
The future of cyber resilience will rely heavily on the combined power of new technologies like Generative AI and the digital skills of Generation Z (Gen Z). Consider these points:
1) Using AI in Cyber Security: Generative AI can quickly detect threats, respond automatically, and predict future risks. It helps organisations stay ahead of cyberattacks more effectively.
2) Gen Z Leading the Way: Gen Z has grown up with technology. Their strong tech skills and comfort with AI make them ideal for building and running future-ready Cyber Security systems.
3) Human-AI Teamwork: Cyber Security will be shaped by teams where humans and AI work together. Gen Z brings creativity and quick thinking, while AI handles fast data processing and alerts, strengthening defences.
4) Keeping Up with Changes: Cyber threats are always evolving. That’s why people and AI tools must keep learning and improving over time.
5) Responsible Use of AI: As we use AI more in security, it's essential to make sure it's used fairly and ethically. Being transparent and responsible builds trust and keeps systems safe.
By combining Gen Z’s digital talent with AI tools, organisations can create stronger, smarter, and more adaptable defences against any cyber threats that may spring up in the future.
What are the Three Rs of Cyber Resilience?
The three Rs of cyber resilience include Resist, Recover, and Rebuild. Resist means the prevention of attacks through strong defences. Recover means restoration of operations following an attack as soon as possible. Last but not least, rebuild involves improving defences and learning from incidents so that protection keeps getting better.
Is COBIT a Cyber Security Framework?
COBIT isn’t a Cyber Security framework on its own. Instead, it’s a broad IT governance framework. Unlike NIST or ISO 27001, which focus mainly on Cyber Security, COBIT is designed to help ensure that IT efforts support a company’s overall business objectives.
Conclusion
As the digital world becomes more complicated and perilous, strengthening an organisation’s cyber defences is more important than ever. A Cyber Resilience Framework takes a proactive approach, preventing attacks and helping respond quickly and recover effectively. It encourages a culture of readiness and flexibility so organisations can confidently handle cyber incidents.Smarter threats need smarter defenders!
Learn how to harness the power of AI in our Certified Artificial Intelligence (AI) For Cyber Security Professionals Training - Sign up now!
Frequently Asked Questions
How Does a Cyber Resilience Framework Differ From Traditional Cyber Security Measures?

A Cyber Resilience Framework focuses on the ability to withstand and recover from cyber threats, not just preventing them. It integrates proactive risk management, incident response, and business continuity, unlike traditional Cyber Security measures which primarily focus on threat prevention.
How do You Measure the Effectiveness of a Cyber Resilience Framework?

The effectiveness of a Cyber Resilience Framework is measured by assessing incident response times, recovery speed, business continuity during attacks, regulatory compliance, and the overall reduction in the impact and frequency of cyber incidents.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Training, including the Fraud Analytics Training, Cyber Security Awareness Course, and Digital Forensics Training. These courses cater to different skill levels, providing comprehensive insights into the What is Cyber Resilience.
Our IT Security & Data Protection Blogs cover a range of topics related to Cyber Resilience, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Cyber Security skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 DVMS NISTCSF – Foundation Course
DVMS NISTCSF – Foundation Course
Thu 11th Jun 2026
Thu 20th Aug 2026
Thu 8th Oct 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


