We may not have the course you’re looking for. If you enquire or give us a call on 01344 203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

In the fast-paced world of Digital Communication, your email inbox is more than just a hub—it's a target for cybercriminals. While Proofpoint has been a popular shield against email threats, it’s not the only player in town. What if there were other dynamic options to elevate your email security game? Look no further; this blog has a curated list of the top 10 Proofpoint Alternatives. Read on and learn how these alternatives offer unique features to keep your emails safe, your data secure, and your organisation productive.
Table of Contents
1) What is Proofpoint?
2) Proofpoint Alternatives
a) DTEX
b) Cyberhaven
c) Symantec DLP
d) Trellix
e) Safetica
f) Forcepoint Insider Threat
g) Securonix
h) Endpoint Protector by CoSoSys
i) Rapid 7
j) Gurucul
k) IBM QRadar
3) Conclusion
What is Proofpoint?
Founded in 2002 and headquartered in the United States, Proofpoint is a popular Cyber Security solution offering DLP software and device control tools. It specialises in endpoint protection and email security, serving various sectors, including telecommunications, healthcare, IT, and education. Its focus is on protecting organisations’ data and people from advanced threats and compliance risks
Proofpoint's key offerings include:
1) Data loss prevention for enterprises
2) Email security
3) Insider threat management
4) Security awareness training
5) Email encryption
6) Web security
7) Cloud app security broker (CASB)
8) Intelligent classification and protection
Proofpoint Alternatives
Despite being a legacy data protection solution known for its insider threat management, Proofpoint is not without its tradeoffs. If you are looking for more Cyber security options, here are some alternatives your security team should consider:
1) DTEX
DTEX Systems is a Cyber Security company specialising in insider risk management. There are multiple exciting features that make DTEX a comprehensive solution for organisations aiming to manage insider risks effectively.
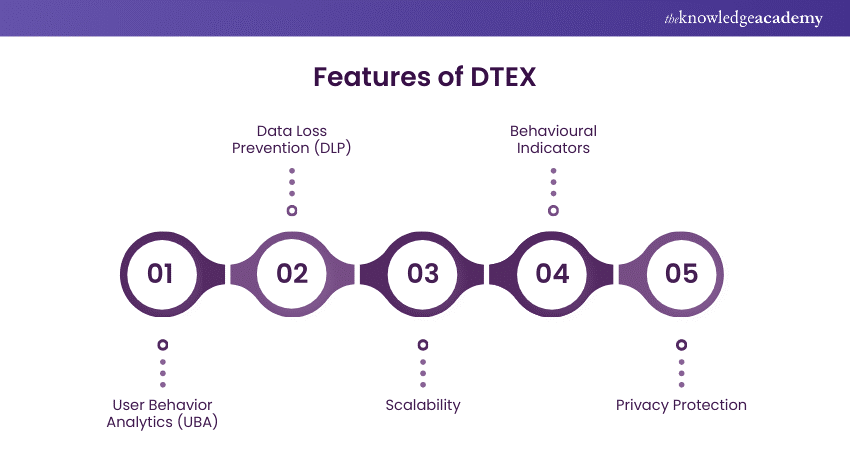
These features include:
a) It leverages ML and AI to detect anomalies and analyse user behaviour that may indicate insider threats.
b) Provides contextual intelligence to enforce risk-adaptive responses, helping prevent data loss without hindering productivity.
c) Monitors user activities to identify suspicious behaviours while maintaining employee privacy through pseudonymisation.
d) Capable of scaling up to 800,000 users in a single implementation.
e) Seamlessly integrates with security tools and platforms, such as Microsoft 365.
f) Ensures employee privacy by tokenising personally identifiable information (PII) and building a forensic audit trail.
2) Cyberhaven
Cyberhaven is a data-aware insider threat detection platform that combines incident response capabilities with endpoint data loss prevention. It leverages intelligence on data ingress and egress on user devices and end-user behaviour to detect genuine threats to critical data more accurately.
Here are some key features of Cyberhaven:
1) Tracking and protecting sensitive data wherever it goes, using data lineage to understand the context and flow of data.
2) Providing robust DLP capabilities, reducing false positives by almost 95% and protecting data across all exfiltration channels.
3) Detecting and stopping risky behaviour by monitoring user actions and providing real-time interventions.
4) Secures data even after it leaves the cloud, ensuring comprehensive protection for modern applications.
5) Easy-to-customise policies, making the platform user-friendly for administrators.
Safeguard your inbox and your organisation from Cyber threats with our Microsoft Proofpoint Training - Sign up now!
3) Symantec DLP
Symantec Data Loss Prevention (DLP) is a comprehensive data security solution designed to prevent sensitive information from leaking outside your organisation, whether accidentally or maliciously. It monitors data across various channels and endpoints, detecting and blocking unauthorised data transfers.

Key features of Symantec DLP include:
a) Monitoring of data across email, web, cloud, endpoints, and storage.
b) Real-time protection preventing data breaches by blocking unauthorised data transfers in real time.
c) Provides a unified interface for policy management, reporting, incident response, and administration.
d) Works seamlessly with other security solutions like Microsoft Information Protection for data classification and encryption
4) Trellix
Formed by the merger of McAfee Enterprise and FireEye in 2022, Trellix is a Cyber Security company providing advanced threat detection and response solutions. Trellix delivers a range of products and services designed to protect organisations from cyber threats, including:
a) Extended Detection and Response (XDR) which integrates multiple security products into a cohesive system to detect and respond to threats across various environments.
b) Endpoint Security Solutions to safeguard devices from malware and other threats.
c) Network Security Tools to safeguard networks, servers, and data centres.
d) Threat Intelligence Insights and analysis to understand and mitigate evolving cyber threats.
Trellix’s approach focuses on creating a sort of living security system that adapts and evolves to counteract sophisticated cyber-attacks.
Struggling to respond to cyber threats effectively? Sign up for our Cyber Security Awareness now!
5) Safetica
Founded in 2007, Safetica has been securing enterprise data with comprehensive Cyber Security solutions focusing on Data Loss Prevention (DLP) and Insider Risk Management (IRM). Its key features and benefits include:
a) Protecting confidential data from being shared with unauthorised parties. It manages data flow within a company to prevent leaks.
b) Detecting insider threats and mitigating risks to sensitive data, including monitoring user behaviour to identify anomalies.
c) Providing detailed insights into user activities, helping to uncover any suspicious behaviour that could indicate a security threat.
d) Helping businesses comply with Data Protection regulations such as PCI-DSS, HIPAA, GDPR, and ISO/IEC 270011.
e) Offering flexible deployment options, including cloud-based hosting for greater scalability and flexibility or on-premise installation for maximum security.
6) Forcepoint Insider Threat
Forcepoint offers a comprehensive suite of solutions to address insider threats. Their Insider Threat Solutions are designed to help organisations understand how users interact with critical data and to stop risky behaviours before they result in data loss.
Here are some key features of Forcepoint’s Insider Threat Solutions:
a) Detailed insights into user behaviour allow organisations to protect intellectual property and detect threats from within.
b) Proactive identification and monitoring of high-risk behaviour to drive better policy enforcement.
c) Early warning system to prevent the exfiltration of intellectual property and regulated data.
d) Reduction of investigation triage time by an average of 70% with user risk scoring and granular visibility
e) Blocking compromised users acting anomalously from accessing critical data.
7) Securonix
Securonix is a well-regarded Cyber Security solution, particularly noted for its security threat management and User and Entity Behaviour Analytics (UEBA) capabilities. The platform enables organisations to understand typical user behaviours and swiftly identify anomalies.
Additional strengths include:
a) Near real-time visibility across system estates
b) Ability to collect data from various log sources
c) Strong automated response mechanisms via Playbooks
d) Advanced analytics using threat models across both micro and macro time frames
Want to learn how to battle the menace of threat actors? Sign up for our Incident Response Training and arm your organisation’s communication channels now!
7) Endpoint Protector by CoSoSys
Endpoint Protector by CoSoSys (now part of Netwrix) is among the best Proofpoint Alternatives due to its comprehensive endpoint and device control features.
Some of its additional features include:
a) Ease of use
b) Customisable settings for 30+ device types
c) Effectiveness in data loss prevention
d) The exceptional support and knowledge of the implementation team
However, users have sometimes reported issues with SSL certificates on the Microsoft Edge browser.
8) Rapid 7
Rapid7’s User Behaviour Analytics (UBA) solution (part of the InsightIDR platform) has received praise for its:
a) User-friendly and intuitive interface
b) Robust reporting
c) Commendable features for user behaviour analytics
d) Ease of configuration and affordability
e) Ability to detect threats such as malware on monitored endpoints
With the well-regarded rules for attack review and the solution being reportedly easy to set up, this Proofpoint alternative is easy to understand for different user skill levels. However, users suggest that the digital forensics part could be expanded and more could be provided on the endpoint detection level.
9) Gurucul
Thanks to its foundation on the Hadoop platform, Gurucul’s User and Entity Behaviour Analytics (UEBA) solution is distinguished by its high flexibility. Let’s explore some features of this architecture:
a) Gurucul’s next-gen SIEM system integrates ML and advanced analytics to provide real-time threat detection and response.
b) The UEBA feature uses big data, ML, and predictive analytics to identify anomalous behaviour that could indicate security threats.
c) Gurucul stands out with its advanced Threat Detection, Investigation, and Response (TDIR) capabilities, which are central to its Cyber Security offerings.
d) Insider Threat Management feature helps detect and mitigate risks from insider threats by providing context-aware data on real-time detections.
e) Gurucul adopts an identity-centric approach to threat detection, providing visibility and insights into risky access behaviour and suspicious activity within identity systems.
f) The Data Optimiser tool reduces the signal-to-noise ratio, helping security teams focus on true threats and reduce investigation time.
g) The Security Orchestration, Automation, and Response (SOAR) platform automates security operations to enhance efficiency and reduce the burden on security analysts.
10) IBM QRadar
The IBM QRadar Suite is a modernised threat detection and response solution designed to increase the security analyst efficiency throughout the entire incident lifecycle. This suite incorporates enterprise-grade automation and AI, significantly boosting analyst productivity and enabling resource-constrained security teams to work more effectively across essential technologies.
Here are some features of IBM Qradar:
a) Collecting and analysing log data from several sources to provide comprehensive visibility into network activities.
b) Providing detailed insights into network traffic, helping to identify suspicious activities and potential breaches.
c) Integrating with vulnerability management tools to assess and prioritise vulnerabilities based on their risk.
d) Offering cloud-native deployment options, allowing for scalable and flexible security management across hybrid cloud environments.
e) Supporting over 900 pre-built integrations with various security tools, enhancing its ability to provide a unified security management platform
Conclusion
In conclusion, Proofpoint is not the only player in the landscape of Cyber Security. The 10 Proofpoint Alternatives explored in this blog provide a range of features tailored to diverse organisational security needs. We hope this blog helps you find the best fit and ensure your email communications remain secure and resilient.
Worried about the risk of digital threats? We are here to guide you with our Cyber Security Risk Management Course – Sign up now!
Frequently Asked Questions
What is The Message Limit for Proofpoint?

For registered users, the message limit is 500 emails over a 10-minute period or 2,500 emails over a 24-hour period. For unregistered accounts, there is a 500-message limit in 60 seconds.
Does Proofpoint do Encryption?

Proofpoint's policy-based DLP engine lets you define and dynamically apply granular encryption policies at the global, group and user levels with LDAP and Active Directory integrations.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 19 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers Microsoft 365 Training, including the Microsoft 365 Messaging MS203 Course and the Microsoft Proofpoint Course. These courses cater to different skill levels, providing comprehensive insights into What is Microsoft Dynamics 365 Business Central.
Our Office Applications cover a range of topics related to Proofpoint, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your office security options, The Knowledge Academy's diverse courses and informative blogs have got you covered.

Richard Harris is a highly experienced full-stack developer with deep expertise in both frontend and backend technologies. Over his 12-year career, he has built scalable web applications for startups, enterprises and government organisations. Richard’s writing combines technical depth with clear explanations, ideal for developers looking to grow in modern frameworks and tools.

Upcoming Office Applications Resources Batches & Dates
Date
 Microsoft Proofpoint Training
Microsoft Proofpoint Training
Fri 17th Jul 2026
Fri 9th Oct 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


