We may not have the course you’re looking for. If you enquire or give us a call on 01344 203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.
Imagine trying to assemble a complex puzzle without knowing which pieces are missing it would be frustrating, right? That’s exactly what securing your organisation without a clear assessment feels like. This is where an ISO 27001 Gap Analysis comes in - it acts as your blueprint, helping you spot missing security controls, weak links, and areas needing attention before diving into the certification process.
Understanding its importance helps organisations evaluate how closely their current security practices align with the ISO 27001 standard. In this blog, you will explore what an ISO 27001 Gap Analysis is, its importance, how to get started, and more. Keep reading to learn more about it!
Table of Contents
1) What is an ISO 27001 Gap Analysis?
2) Why is an ISO 27001 Gap Analysis Important?
3) Benefits of an ISO 27001 Gap Analysis
4) How to Perform an ISO 27001 Gap Analysis?
5) Challenges of Implementing ISO 27001 Gap Assessment
6) What is the Difference Between a Gap Analysis and an Internal Audit?
7) How Often is the ISO 27001 Gap Analysis Conducted?
8) Conclusion
What is an ISO 27001 Gap Analysis?
An ISO 27001 Gap Analysis is a process that evaluates how well an organisation's current information security practices align with the ISO/IEC 27001 standard. It identifies missing or weak controls, helping organisations understand what needs improvement before pursuing full ISO 27001 Certification. This step is typically conducted at the beginning of the ISO implementation journey.
The analysis generates a detailed report highlighting areas of non-compliance, partially implemented measures, and existing strengths. It serves as a roadmap for developing an implementation plan by prioritising critical gaps and estimating the resources, timelines, and effort required to achieve compliance.
Key Components of a Gap Analysis
A successful ISO 27001 Gap Analysis involves examining the components to build a strong foundation for an effective Information Security Management System (ISMS). Let's look at the components below:
1) Scope Definition: Clearly define what will be analysed, such as a specific department, information system, or the entire organisation. This ensures the gap analysis remains focused and relevant.
2) Documentation Review: Examine existing security policies, procedures, and records to check whether they align with ISO/IEC 27001 requirements and identify any missing documentation.
3) Control Assessment: Compare current security controls with ISO/IEC 27001 Annex A controls to identify gaps, weaknesses, or controls that are not fully implemented.
4) Risk Assessment: Prioritise identified gaps based on the level of risk they pose to sensitive information and organisational assets.
5) Stakeholder Engagement: Involve key stakeholders, such as IT, security, and compliance teams, to ensure the analysis reflects actual practices and provides practical insights.
6) Findings Report: Document all identified gaps, associated risks, and recommended corrective actions in a structured report to guide the ISO 27001 implementation process.
Why is an ISO 27001 Gap Analysis Important?
An ISO 27001 Gap Analysis helps organisations evaluate how their current information security practices compare with the requirements of the ISO/IEC 27001 standard. By identifying weaknesses in existing controls and policies, it enables organisations to focus on high-impact improvements, such as strengthening access controls or updating security policies.
Also, it highlights compliance gaps and provides a clear roadmap for organisations preparing for ISO 27001 certification. By addressing these gaps, organisations can strengthen their Information Security Management System (ISMS) and build a more resilient framework for managing information security risks.
Benefits of an ISO 27001 Gap Analysis
An ISO 27001 Gap Analysis provides a comprehensive overview of your organisation's current security status by pinpointing areas of non-compliance. Here are the key pointers highlighting the benefits of an ISO 27001 Gap Analysis:
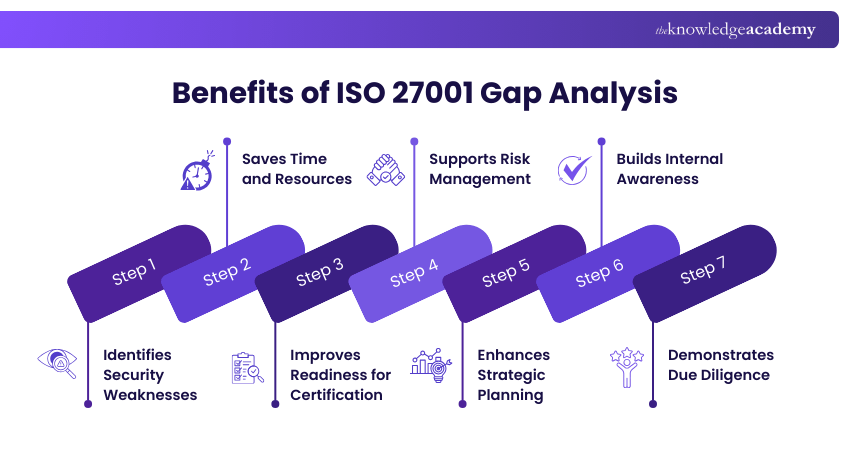
a) Identifies Security Weaknesses: Highlights missing or insufficient controls, enabling proactive measures to address vulnerabilities before they become threats.
b) Saves Time and Resources: Pinpoints areas needing attention, preventing wasted efforts on already compliant sections.
c) Improves Readiness for Certification: Serves as a rehearsal for the ISO 27001 audit, identifying areas for improvement before the actual assessment.
d) Supports Risk Management: Aligns your organisation's security posture with business risks, enhancing the robustness and relevance of your information security.
e) Enhances Strategic Planning: Provides a clear action plan with prioritised recommendations, facilitating resource allocation and setting achievable timelines.
f) Builds Internal Awareness: Raises awareness among employees and stakeholders about ISO 27001 requirements and their roles in compliance.
g) Demonstrates Due Diligence: Shows clients, partners, and regulators your commitment to protecting information and adhering to international best practices.
Lead your organisation’s ISO 27001 Certification confidently with ISO 27001 Lead Implementer Training now!
How to Perform an ISO 27001 Gap Analysis?
Conducting an ISO 27001 Gap Analysis requires following a structured approach. This helps organisations assess existing controls, identify weaknesses, and develop a clear plan for improving their ISMS. Let’s look at it below:
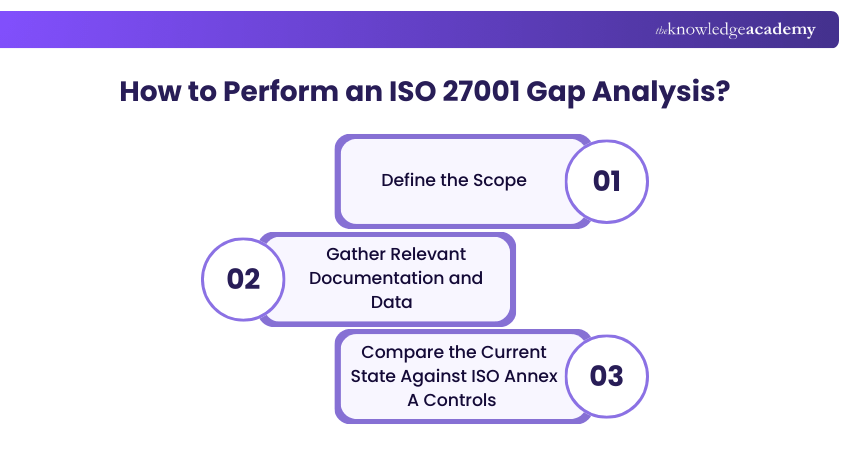
1) Define the Scope
Start by determining what the gap analysis will cover, such as specific departments, systems, or processes. Defining a clear scope keeps the analysis manageable and ensures actionable results. Organisations may analyse the entire organisation or begin with high-risk areas, such as systems handling sensitive data, access control processes, or business continuity functions.
2) Gather Relevant Documentation and Data
Gather the necessary information to evaluate current security practices accurately. This includes policies, procedures, system logs, previous audit reports, and an inventory of information assets. Also, key documents, such as access control policies, incident response plans, and the Statement of Applicability (SoA), should be reviewed.
3) Compare the Current State Against ISO Annex A Controls
Assess existing security controls against the controls listed in ISO/IEC 27001 Annex A, which cover areas such as access control, incident management, encryption, and supplier relationships. Determine whether each control is effectively implemented, aligned with organisational risks, and sufficient to meet the standard’s requirements.
Transform your career with our ISO 27001 Internal Auditor Training - book your spot now!
Challenges of Implementing ISO 27001 Gap Assessment
Implementing an ISO 27001 gap assessment poses several challenges that organisations must address for successful Information Security compliance. Some of them are mentioned below.
a) Resource and Budget Constraints: Allocating sufficient resources, time, and budget for a detailed assessment can be difficult. This can potentially result in incomplete evaluations.
b) Need for Skilled Professionals: Securing the necessary expertise and experienced professionals to perform the assessment can be time-consuming. This affects the thoroughness and accuracy of the evaluation.
c) Complexity of Documentation: Managing the detailed documentation of Information Security processes and controls to meet ISO 27001 Standards is complex and requires meticulous attention to detail.
d) Managing Third-party Relationships: Ensuring third-party compliance with ISO 27001 Standards introduces challenges in coordinating and verifying the security practices of external entities, necessitating effective management strategies.
e) Stakeholder Communication and Awareness: Getting consensus among stakeholders and developing a culture of Information Security awareness across the organisation are crucial but challenging and require strategic planning and ongoing commitment.
Empower your team with our ISO 27001 Foundation Training - Join us now!
What is the Difference Between a Gap Analysis and an Internal Audit?
A gap analysis evaluates an organisation’s current information security practices against the requirements of ISO/IEC 27001 to identify areas of non-compliance. Usually, it is conducted at the beginning of the implementation process to understand existing gaps and create a roadmap for improvements.
In contrast, an internal audit is a formal assessment carried out after the ISMS has been implemented. It verifies whether the ISMS complies with ISO 27001 requirements and is operating effectively. Internal audits are performed regularly, often before external certification audits, to ensure ongoing compliance and continual improvement.
Conclusion
An ISO 27001 Gap Analysis is important for enhancing Information Security and achieving certification. It identifies compliance gaps and provides a clear improvement roadmap. Despite challenges like resource constraints and the need for expertise, the benefits of a robust ISMS far outweigh the difficulties. This analysis is a valuable investment in the organisation's security and resilience.
Improve your Cyber Security expertise with our ISO 27001 Lead Auditor Training - Register now!
Frequently Asked Questions
How Long Does an ISO 27001 Gap Analysis Take?

An ISO 27001 Gap Analysis takes a few days to several weeks, depending on the organisation’s size, scope, and existing security controls. With experienced consultants, it may take 5–10 days, while organisations conducting the analysis internally may require several weeks to review controls and documentation.
What is an ISO 27001 Gap Analysis Checklist?

An ISO 27001 Gap Analysis checklist is a tool used to compare an organisation’s current security practices with the requirements of ISO/IEC 27001:2022. It helps identify weak controls, prioritise improvements, and guide remediation.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various ISO 27001 Training, including the ISO 27001 Foundation Training, ISO 27001 Lead Auditor Training, and ISO 27001 Internal Auditor Training. These courses cater to different skill levels, providing comprehensive insights into Information Security Management.
Our IT Security and Data Protection Blogs cover a range of topics related to ISO 27001, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Information Security skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

Hailey Davis is an ISO compliance expert with over 10 years of experience in audit, quality management systems (QMS), and regulatory compliance. She has worked with various industries, including manufacturing, healthcare, and technology, ensuring organisations achieve and maintain ISO certifications. Hailey’s content provides practical, actionable insights on navigating compliance challenges and improving business processes.
View Detail
Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 ISO 27001 Foundation
ISO 27001 Foundation
Mon 6th Jul 2026
Mon 3rd Aug 2026
Mon 7th Sep 2026
Mon 5th Oct 2026
Mon 2nd Nov 2026
Mon 7th Dec 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


