We may not have the course you’re looking for. If you enquire or give us a call on +971 8000311193 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

We live in a world where every click and keystroke travels across invisible wires. This also means that your private information is just a few clicks or codes away from malicious actors. So what serves as the guardian of modern communication, from private messages to financial transactions? The answer is Data Encryption. Encryption acts like a resilient code, guarding your personal and professional data from prying eyes.
It’s the reason why you can send a secret message to your friend over the highly populated internet and yet no one else can see it. If you want to take a deep dive into What is Data Encryption, this blog is your go-to companion. It looks into the Data Encryption’s importance, examples, trends and more. So read on and build your foundation in the field of Data Encryption!
Table of Contents
1) What is Data Encryption?
2) How Encryption Works?
3) The Importance of Data Encryption
4) Encryption of Data in Transit vs Data at Rest
5) Examples of Encryption Algorithms
6) Advantages and Disadvantages of Encryption
7) Conclusion
What is Encryption?
Data Encryption is a security method used in Cryptography that transforms readable data into unreadable code, known as ciphertext. Only those with a secret key or password can access the original information. It safeguards data from unauthorised access, theft, or tampering.
Encryption protects both data at rest and in transit, and its effectiveness relies on keeping the decryption key secure from unauthorised users. It’s a cornerstone of Digital Security, protecting sensitive data such as passwords, credit card numbers, and personal communications from cybercriminals, hackers, and other malicious actors.
How Encryption Works?
Encryption converts readable plaintext into scrambled ciphertext using specialised cryptographic algorithms. Decryption keys, created through these algorithms, unlock the encoded data. Because modern systems use extremely large key combinations, guessing or brute-forcing them becomes practically impossible.
Early methods like the Caesar cipher used simple alphabet shifts to hide messages, but today’s encryption employs highly complex, computer-generated keys with hundreds or thousands of characters. This sophistication ensures strong security for digital information.
Types of Data Encryption
There are two major kinds of Data Encryption, each based on how Encryption keys are used. The choice depends on the use case, performance, and level of security required.
Symmetric Encryption (Private Encryption Key)
Symmetric Encryption employs a single private key for both encrypting and decrypting data. It is fast and efficient, commonly used for encrypting large datasets or stored files. However, key distribution must be secure to prevent unauthorised access.
Asymmetric Encryption (Public Encryption Key)
Asymmetric Encryption uses two keys: public key for encrypting data and private key to decrypt it. It is widely used in secure communications and digital signatures. This method ensures that even if the public key is shared, only the private key can unlock the data.
The Importance of Data Encryption
With the digital landscape inundated with data, data is more accessible and desirable to attackers than ever before, thus increasing the need for protection. Additionally, numerous businesses face data protection regulation requirements, which explicitly require Encryption. Here are the benefits of Data Encryption:
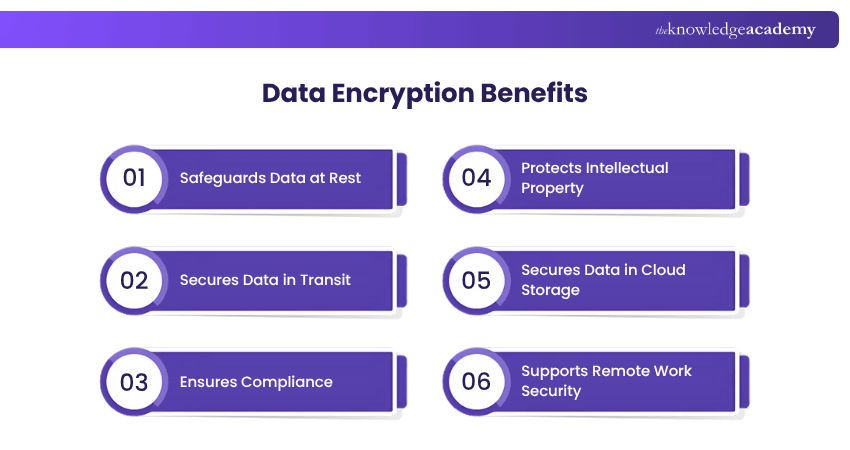
Safeguards Data at Rest
Data at rest refers to stored data on servers or devices. Encryption ensures that, even if accessed by unauthorised users, the data remains unreadable without the decryption key, protecting sensitive files from theft or misuse.
Secures Data in Transit
Data in transit is vulnerable to interception. Encryption secures this data by allowing only authorised recipients with the correct decryption key to access it, especially important for mobile devices and remote network communications.
Ensures Compliance
Many industries, like finance and healthcare, follow strict data protection rules. Using Data Encryption helps businesses meet regulations such as PCI DSS, reducing the risk of penalties and ensuring secure handling of sensitive customer information.
Protects Intellectual Property
Encryption safeguards intellectual property, such as trade secrets and proprietary data, from unauthorised access. Even if files are stolen, they remain undecipherable without the correct key, helping businesses avoid espionage and maintain a competitive edge.
Secures Data in Cloud Storage
Cloud storage offers convenience but poses security risks. Data Encryption ensures that even if cloud servers are compromised, the stored data remains secure and inaccessible to unauthorised users without the corresponding decryption keys.
Supports Remote Work Security
With remote work becoming common, the risk of data exposure increases. Encryption helps protect sensitive data on personal devices and networks, ensuring it remains secure even if the remote device or internet connection is compromised.
Stay ahead of digital manipulators by signing up for our comprehensive Social Engineering Training!
Encryption of Data in Transit vs Data at Rest
When it comes to the main categories of Data Encryption, you can find in-transit-based Encryption and Data Encryption at rest. These two types are explored below:
Encryption in Transit
Encryption in transit protects the data as it travels from one location to another, such as when you upload a file, send emails or make an online payment. During this journey, data is highly vulnerable to interception by hackers or unauthorised parties. Without in-transit Encryption, secure communication channels like HTTPS, VPNs, or TLS would be rendered unsafe, making your data open to tampering or theft.
Encryption at Rest
Encryption at rest secures data that is stored on a device or server, whether on a hard drive, database, mobile device, or Cloud storage. It protects information that’s not actively moving but remains valuable and sensitive. This kind of Encryption ensures that if a device is stolen or a server is hacked, the stored data remains inaccessible to unauthorised users. Encryption at rest is especially important for organisations handling financial records, customer information or intellectual property.
Examples of Encryption Algorithms
Encryption algorithms turn data into ciphertext. These algorithms use the Encryption key to predictably alter the data so that, even though the encrypted data appears random, it can be turned back into plaintext using the decryption key. Some of the best-known Encryption algorithms include the following:

1) 3DES Encryption: 3DES, short for Triple Data Encryption Standard, is a symmetric key algorithm, where data is passed through the original DES algorithm three times throughout the Encryption process. Triple DES is a reliable hardware Encryption solution for financial services and other industries.
2) AES encryption: AES, short for Advanced Encryption Standard, was created to update the original DES algorithm. Some of the more common applications of this algorithm include messaging apps such as WhatsApp or Signal and the file archiver program called WinZip.
3) RSA Encryption: RSA, short for Rivest, Shamir, and Adleman (surnames of the mathematicians who described this algorithm), was the first Asymmetric Encryption algorithm available to the public. RSA's popularity is due to its key length.
4) Twofish Encryption: Used in software and hardware, Twofish is deemed one of the fastest of its kind. Since Twofish is not patented, it's freely available to anyone and can be found bundled in Encryption programs such as GPG, PhotoEncrypt, and the open-source software TrueCrypt.
5) RC4 Encryption: This one is used in WPA and WEP, which are Encryption protocols used in wireless routers.
Want to become a pro in identifying and mitigating digital threats? Sign up for our Cyber Security Risk Management Course now!
Advantages and Disadvantages of Encryption
Encryption strengthens data security by protecting information as it moves, rests, and gets processed across digital systems. It supports privacy, safeguards modern cloud environments, and helps organisations meet strict regulatory requirements.
Advantages of Encryption
1) Protects data across devices: Data constantly travels between devices, applications, and servers. Encryption, combined with authentication, ensures that this moving data remains safe from interception during transfers.
2) Ensures data integrity: Encryption prevents unauthorised users from viewing, altering, or exploiting sensitive information. It helps keep documents, transactions, and communications intact, reducing risks like fraud and tampering.
3) Protects digital transformations: As more organisations adopt cloud services, encryption plays a vital role in securing data in transit, at rest, and during processing. Advanced encryption options and managed key services further enhance cloud security.
4) Helps meet compliance requirements: Many regulations mandate strong encryption, including HIPAA, PCI DSS, GDPR, and FCPA. Using encryption helps organisations handle sensitive healthcare, financial, and retail data while maintaining compliance.
Disadvantages of Encryption
1) Ransomware: Cybercriminals can misuse encryption to lock an organisation’s data and demand payment for access. When attackers encrypt stolen data, it becomes a powerful tool for extortion.
2) Key management: Encryption is only effective if keys are protected. Lost, stolen, or poorly managed keys can result in data loss or breaches, making secure key management systems essential for organisations.
3) Quantum computing: Future quantum computers could break many current encryption methods due to their processing power. Although quantum threats are still emerging, “quantum-resistant” algorithms are now being developed and adopted to prepare for this shift.
Unlock the code to cyber confidence. Sign up for our Certified Encryption Specialist Certification and guard the digital frontier with ease!
Conclusion
In a world where digital threats are slowly but surely overshadowing every other kind of threat, Data Encryption is the ultimate defence against unauthorised access. This process ensures privacy and security by transforming sensitive information into unreadable code. More than just a smart choice, understanding What is Data Encryption and embracing its powers as detailed in this blog is essential for fortifying your digital life.
Become more effective in responding to cyber threats with our up-to-date Cyber Security Awareness Course - Sign up now!
Frequently Asked Questions
Can Encrypted Data be Hacked?

Encrypted data can be hacked, but it's extremely difficult without the decryption key. Strong Encryption algorithms make brute-force attacks nearly impossible. However, weak passwords, poor key management, or software vulnerabilities can still expose encrypted data to risk.
What Happens to Your Data When it is Encrypted?

When your data is encrypted, it transforms its original, readable form into an unreadable format called ciphertext. This process ensures that only authorised parties with the right decryption key can access sensitive data.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 19 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Courses, including the Cyber Security Awareness Course and the Fraud Analytics Training Course. These courses cater to different skill levels, providing comprehensive insights into Cyber Resilience Framework.
Our IT Security & Data Protection Blogs cover a range of topics related to data security, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your data protection skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

The Knowledge Academy is a world-leading provider of professional training courses, offering globally recognised qualifications across a wide range of subjects. With expert trainers, up-to-date course material, and flexible learning options, we aim to empower professionals and organisations to achieve their goals through continuous learning.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Introduction to System and Network Security
Introduction to System and Network Security
Fri 28th Aug 2026
Fri 13th Nov 2026





 Top Rated Course
Top Rated Course








 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


