 To help and support our clients we are providing a limited number of 250 daily discount codes. Hurry, first come, first served!
To help and support our clients we are providing a limited number of 250 daily discount codes. Hurry, first come, first served!
EC – Council Certification Training FAQs
EC-Council Certification Training equips individuals with the skills and knowledge needed to detect, prevent, and respond to cyber threats, enhancing their capabilities in ethical hacking and information security.
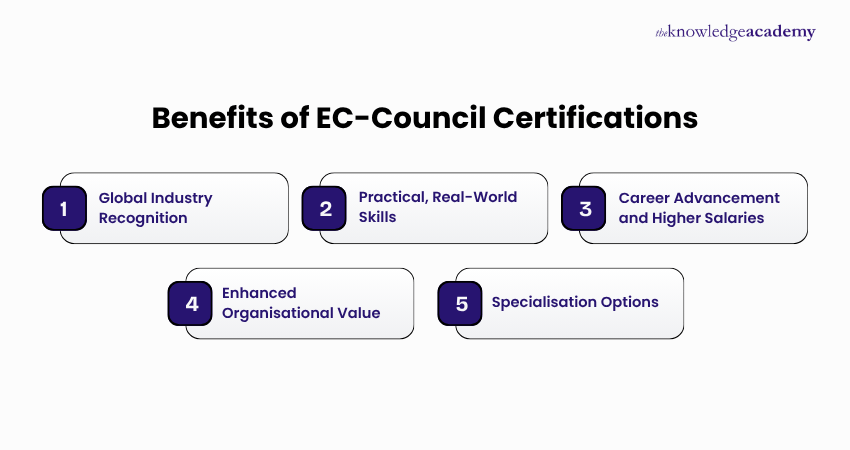
You should choose EC-Council Training to gain globally recognised credentials in cybersecurity, enhance your ethical hacking skills, and improve your career prospects in the growing field of information security.
EC-Council Training can benefit your organisation by strengthening its cybersecurity defences, ensuring compliance with industry standards, and equipping staff with the skills to identify and mitigate cyber threats effectively.
The prerequisites for the EC-Council Certification Training are based on the course specifications and the target group of professionals it serves. Check the respective course page of the course that you are planning to take to know about its prerequisites.
The duration of these EC-Council Courses varies. Please visit our course pages for specific information.
After this EC-Council Training, you will gain skills in ethical hacking, penetration testing, network security, threat analysis, and vulnerability assessment, along with in-depth knowledge of cybersecurity tools, techniques, and best practices.
EC-Council Certification offers career benefits such as industry recognition, enhanced job opportunities, higher earning potential, and the ability to work in specialised cybersecurity roles across various sectors worldwide.
EC-Council Certification is important for cybersecurity professionals as it validates their expertise, demonstrates a commitment to industry standards, and equips them to effectively combat evolving cyber threats and attacks.
Yes, EC-Council Training can be taken online, offering flexibility and convenience for delegates to study from anywhere while still gaining comprehensive, instructor-led or self-paced cybersecurity training.
EC-Council Courses cover topics such as ethical hacking, penetration testing, network security, cryptography, malware analysis, incident response, digital forensics, and security policies and procedures.
An EC-Council Certification is valid for three years. You can renew it by earning continuing education credits through approved activities and submitting them via the EC-Council Aspen portal.
EC-Council Certifications are globally recognised and focus heavily on practical, hands-on skills in ethical hacking and cybersecurity, making them highly respected alongside other industry certifications like CompTIA and CISSP.
EC-Council Training addresses current cybersecurity threats by teaching up-to-date attack methodologies, defence strategies, and real-world simulations, enabling professionals to proactively identify, mitigate, and respond to emerging cyber risks.
EC-Council Certification exams typically consist of multiple-choice questions, scenario-based assessments, and practical challenges, designed to test both theoretical knowledge and hands-on cybersecurity skills in a timed environment.
There are various EC-Council Certifications available, including Certified Ethical Hacker (CEH), Certified Network Defender (CND), Computer Hacking Forensic Investigator (CHFI), and Licensed Penetration Tester (LPT) Master, among others.
What makes EC-Council Training different from other cybersecurity training programs?
Industries such as Finance, Healthcare, Government, Defence, Information Technology, and Telecommunications require professionals with EC-Council Certification to safeguard sensitive data and defend against cyber threats.
With an EC-Council Certification, you can apply for roles such as ethical hacker, cybersecurity analyst, network security engineer, penetration tester, incident responder, and information security specialist.
Yes, EC-Council Courses are suitable for beginners, especially foundational certifications like CND and CEH, which introduce core cybersecurity concepts, tools, and practices in a structured and accessible manner.
Some EC-Council Certifications require relevant work experience or completion of official training, while others, like CEH, allow candidates without experience to qualify through accredited course completion.
Yes, EC-Council Training can help in career advancement by enhancing your cybersecurity expertise, earning industry-recognised credentials, and opening doors to higher-level roles with better salary prospects.
To choose the right EC-Council Course for your career, assess your current skills, career goals, and area of interest—such as ethical hacking, network defence, or forensics—and match them accordingly.
Yes, EC-Council Courses can help you transition into a cybersecurity career by providing essential knowledge, practical skills, and recognised certifications that validate your readiness for industry roles.
Yes, EC-Council Training is suitable for non-technical professionals, especially entry-level courses, as they build foundational cybersecurity knowledge and gradually introduce technical concepts in an accessible manner.
Yes, you can take an EC-Council Course without prior cybersecurity knowledge, particularly beginner-friendly options like CND and CEH, which are designed to build skills from the ground up.
The Knowledge Academy in Saudi Arabia stands out as a prestigious training provider known for its extensive course offerings, expert instructors, adaptable learning formats, and industry recognition. It's a dependable option for those seeking this course.
Please see our EC – Council Certification Training available in Saudi Arabia
The Knowledge Academy is one of the Leading global training provider for EC – Council Certification Training.
The training fees for EC – Council Certification Training in Saudi Arabia starts from SAR

Why we're the go to training provider for you

Best price in the industry
You won't find better value in the marketplace. If you do find a lower price, we will beat it.

Trusted & Approved
Recognised by leading certification bodies, we deliver training you can trust.

Many delivery methods
Flexible delivery methods are available depending on your learning style.
High quality resources
Resources are included for a comprehensive learning experience.




"Really good course and well organised. Trainer was great with a sense of humour - his experience allowed a free flowing course, structured to help you gain as much information & relevant experience whilst helping prepare you for the exam"
Joshua Davies, Thames Water



















 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


