We may not have the course you’re looking for. If you enquire or give us a call on + 800 908601 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

In an ever more interlinked world, Cyber Security Risk takes top spot among the major challenges organisations need to deal with. There are vulnerabilities in every digital system that intruders can make use of. By comprehending these threats, companies are able to secure information, avoid interruptions, and enhance the confidence of their stakeholders. This blog directs you through the life cycle of a cyber threat and delineates the characteristics of successful risk management.
Table of Contents
1) What is Cyber Security?
2) What are the Key Cyber Risks and Security Threats?
3) Components of Cybersecurity Risk
4) Top Cybersecurity Risk Trends in 2026
5) Impact of cyber risk
6) Conclusion
What is Cyber Security Risk?
The term Cyber Security Risk is defined as the extent to which a company may be harmed or lose money as a result of cyber-attacks or data leaks. It enfolds the risk of confidential data being exposed, the disruption of the company's operations, or the loss of money. Those companies that are aware of this risk will have a better chance of safeguarding their assets, having a quick reaction to the situation, and minimising the losses.
What are the Key Cyber Risks and Security Threats?
The likelihood of an organisation undergoing exposure, loss or damage due to a cyber-attack or data breach that takes advantage of a vulnerability is called cybersecurity risk. The more companies rely on digital infrastructures and cloud services, the bigger the volume of confidential data and the higher the possibility that the threats would yield financial, operational or reputational losses.
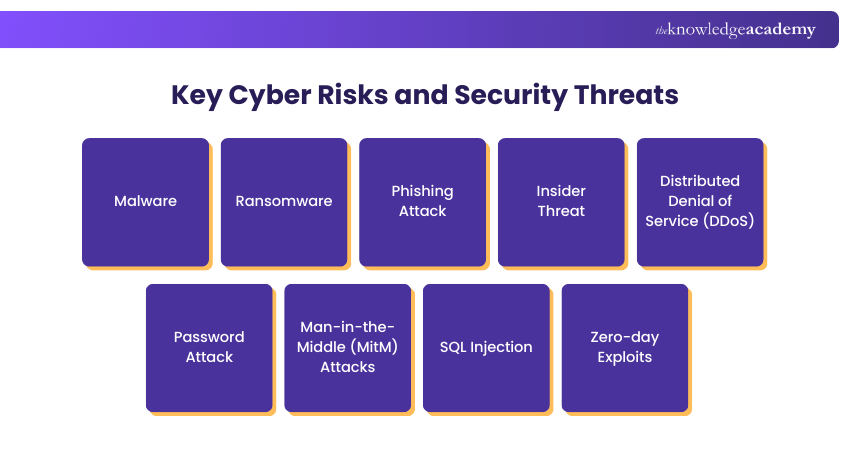
1) Malware
Malware is a term that encompasses all kinds of lethal software like viruses, spyware, worms, and trojans, which have been purposely developed to either invade or ruin computer systems. Moreover, hacked computers distribute their madness through emails, programs, or infected websites. Moreover, due to its rapid network-wide distribution, even one compromised device can expose the whole enterprise to danger.
2) Ransomware
Ransomware is a type of hacker software that either locks or encrypts a company's data and then asks for payment to release the data. It is like a company prison where the hostage is the main computer and the people in the office are paid ransom. However, this threat often translates into financial losses, a blackout, and a reduction in the company's reputation for a long time.
3) Phishing Attack
Phishing is the act of pretending to be a legitimate entity in order to get people to disclose their passwords or other confidential information by means of fake emails, messages, or websites. The reason phishing is so successful is that it appeals to people's behaviour, which is a very easy way to access any organisation, rather than through technical means.
Join the Certified Cyber Security Professional (CCS-PRO) Course to learn Phishing, Web Security, and Hacking.
4) Insider Threat
An insider threat is when the culprit is an employee, a contractor, or a vendor who has access to the system and misuses it either deliberately or accidentally. Insider threats are more difficult to detect and manage because they already have legitimate access.
5) Distributed Denial of Service (DDoS)
A Distributed Denial of Service attack (DDoS) paralyses a server, network, or website by flooding it with traffic from many different sources. This makes it impossible for the users who are supposed to be using the service to access it, and it can lead to a great deal of disruption.
6) Password Attack
Password attacks are hacking tactics that consist of guessing or deciphering the password to gain access to user accounts or to the system. Brute force, credential stuffing, and the use of weak or reused passwords are some of the common attacking methods. By the time attackers complete their process, they can take over users’ identities, traverse the systems, and access sensitive information.
7) Man-in-the-Middle (MitM) Attacks
MitM is a type of attack in which a hacker secretly listens in on the communication of two people. Therefore, they can take sensitive information or change data without the parties being aware. These kinds of attacks are extremely risky if they happen on an open network or if there is no encryption.
8) SQL Injection
An SQL injection attack occurs when a hacker injects harmful code into those input fields that are linked to a database. In case of success, he can read, modify, or even delete the data or take over the database with a superuser account. This flaw calls for the requirement of secure programming and stringent input validation.
9) Zero-day Exploits
Zero-day exploits are aimed at the flaws that have yet to be discovered by developers and security personnel. As there is no remedy or fix available, the attackers can easily bypass the security measures and break into the premises of the company. This scenario makes zero-day threats very risky as the companies do not have any prior protection.
Build threat investigation expertise with Malware Analysis Training for advanced cybersecurity defence.
Components of Cybersecurity Risk
Cyber Security Risks originate from the flaws or lapses that exist in the whole company's digital environment and can be taken advantage of to inflict harm of any type: financial, operational, or reputational.
a) Network Security: A thorough examination of the security measures in place for the network, including ports and configurations, to make sure that no one can hack or attack the network through those means.
b) DNS Health: This aspect of the assessment scrutinises not only the current DNS settings but also the history, with an aim of spotting misconfigurations and previous malicious acts that could potentially open up the organisation to threats.
c) Patching Cadence: It looks at the speed of applying security patches to systems and software in order to minimise the risk associated with vulnerability.
d) Endpoint Security: This component is concerned with the assessment of the security of devices such as laptops, desktops, and the like, in order to find out which ones are obsolete and which ones are risky.
e) IP Reputation and Malware Exposure: Assessment of the situation in terms of the company’s IP addresses or domains and their connection to malware, spam or any other activities that are suspicious.
f) Application Security: Conducting a thorough review of applications exposed to the public and web systems for outdated versions or known vulnerabilities that an attacker could exploit.
g) Information Leak Risk: Detection of the situation where sensitive information, such as passwords or internal documents, has been made available to the public or discovered on external forums.
h) Social Engineering and Human Factor Risk: It quantifies the extent of the organisation's susceptibility to phishing and other attacks that leverage human mistakes or manipulation.
i) Third Party and Vendor Risk: It investigates the security level of the suppliers and partners whose vulnerabilities may lead the organisation to face cyber threats.
Top Cybersecurity Risk Trends in 2026
The year 2026 is set to witness the continuous rise of Cyber Security Risks due to the extension of the digital footprint by companies and the increasing sophistication of the attackers, among other factors. The urgency of having better visibility, quicker response, and better management of interconnected digital environments. Key trends are listed below:
a) Rising Supply Chain Risk: More reliance on third parties raises the possibility that a vendor’s security flaw could impact the whole company.
b) Growing Hybrid Work Exposure: Attackers can invade through remote access, home networks, and unmanaged devices, which are the main areas of attack nowadays.
c) Increase in AI-Driven Attacks: Cybercriminals are leveraging artificial intelligence to speed up processes such as scanning, finding vulnerabilities, and even creating more persuasive phishing waves.
d) Larger Attack Surface: The use of cloud services, the integration of various applications, and the presence of many digital access points have created numerous avenues for exploitation.
e) Shift to Continuous Monitoring: Organisations must have real-time monitoring of their systems and those of their vendors to catch risks early and avert incidents.
Impact of Cyber Risk
Cyber Security Risks, when associated with the failure of systems, loss of data or interruption of operations, can bring about direct financial losses as well as business disruption. The costs that the organisations have to bear due to the security incident include incident response, remediation, legal, and regulatory fines.
Customer trust can be undermined, and a brand’s reputation can suffer through Cyber Security Risk in the long run, thus making it more difficult to keep customers or get new business. Loss of trust may finally lead to diminished market share and revenue in the long term.
Conclusion
Cyber Security Risk has been evolving alongside the digital transformation and interconnection of systems in companies. To be safe against threats, the establishments need to implement robust controls, carry out constant monitoring, and create awareness among the staff. The right method will always help the firms to lessen their vulnerabilities and keep a strong security stance.
Advance investigation skills with Digital Forensics Training for real world cybercrime analysis
Frequently Asked Questions
What is Cybersecurity Risk Management?

Cybersecurity Risk Management involves spotting, assessing and reducing risks to the digital infrastructure and sensitive data of an organisation, thus minimising the chances and consequences of cyber incidents.
What is high risk in Cyber Security?

High risk in Cyber Security refers to vulnerabilities or threats with significant potential for harm to an organisation's digital assets. This includes sophisticated malware, unpatched software, weak passwords, and human errors. Failure to address high-risk factors can lead to data breaches, financial losses, and reputational damage. Implementing robust security measures is crucial to mitigate these risks and safeguard sensitive information.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 19 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Courses, including the Cyber Security Awareness Training, Certified Cyber Security Professional (CCS-PRO) Course, and Digital Forensics Training. These courses cater to different skill levels, providing comprehensive insights into Symmetric Encryption.
Our IT Security & Data Protection Blogs cover a range of topics related to Cyber Security, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your IT Security & Data Protection skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Cyber Security Risk Management
Cyber Security Risk Management
Fri 28th Aug 2026
Fri 16th Oct 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


