We may not have the course you’re looking for. If you enquire or give us a call on + 800 908601 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

A single cyber incident can compromise data, disrupt operations, and erode trust in seconds. In today’s digital landscape, protecting information requires more than reactive measures, it demands a structured security strategy.
A Cyber Security Framework provides that structure by defining clear functions and controls to manage risks. In this blog, we explain what Cyber Security Framework is, its core components, and how it helps organisations protect their data effectively.
Table of Contents
1) What is Cyber Security Framework?
2) Why are Cyber Security Frameworks Important for Your Organisation?
3) Top Cyber Security Frameworks to Consider
4) How To Implement and Maintain a Cyber Security Framework
5) Conclusion
What is Cyber Security Framework?
Most companies today emphasise developing concrete solutions for cyber-attacks across their systems, networks, software and devices. A Framework in Cyber Security provides plans and strategies for determining and building risk resistance by setting Cyber Security controls to increase the effectiveness of security measures.to increase the effectiveness of security measures.
Therefore, adopting different strategies to protect organisations from estimated risks and attacks is essential. However, there is no standardised platform to ensure Cyber Security; many alternatives exist. Understanding the Difference Between Antivirus and Internet Security helps organisations decide which solutions to implement based on their specific security needs.
Why are Cyber Security Frameworks Important for Your Organisation?
Cyber Security Frameworks are mandatory as they offer a systematic method of identifying, managing, and minimising security risks. Organisations do not respond to threats in a random way but adhere to specific processes that enhance security and efficiency in preparedness.
They also heighten compliance, accountability and resiliency of operations by aligning the security practice according to accepted standards. This will provide uniformity in risk control, improved response to incidents, and increased safeguarding of sensitive organisational information.
Identify, assess, and mitigate digital risks effectively with our Cyber Security Risk Management Course- Join now!
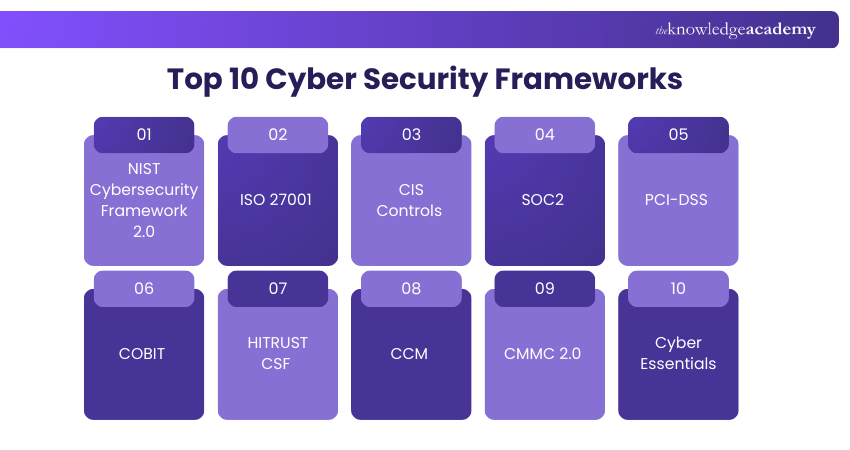
Top Cyber Security Frameworks to Consider
Choosing an appropriate Cyber Security Framework is at the core of enhancing security posture in your organisation. With the available multiple standards, knowing their characteristic of concentration and range of scope will allow you to select one of the standards that fits your regulatory, operational, and risk management requirements.
Ten of the most commonly adopted Cyber Security Frameworks that organisations use to improve protection and compliance are listed below:
1) NIST Cybersecurity Framework 2.0
The NIST Cybersecurity Framework 2.0 gives a wide-range advice on cyber risk management. It is designed with six major functions, namely Govern, Identify, Protect, Detect, Respond, and Recover. These functions assist organisations in incorporating governance, putting various safeguards, identifying an incident at the early stage and being resilient by being able to respond and recover planning.
2) ISO 27001
ISO 27001 is a globally recognised standard based on designing an Information Security Management System (ISMS). It mandates organisations to spot risks, put security control measures in place and keep a track of the information security practises and improvements. This Cyber Security Framework indicates that there are an organised risk management and a security to for sensitive information safeguarded.
3) CIS Controls
CIS Controls gives a sequence of actions with priorities available in the fight against the common cyber threats. They involve the necessary tasks, including asset listing, highly secured settings, and twenty-four monitoring. The framework provides viable and practical controls that can be used by organisations that want organised yet flexible security enhancements.
4) SOC2
SOC 2 assesses the organisational controls in the areas of security, availability, processing integrity, confidentiality and privacy. The assessment performed by an audit is to identify the fulfilment of the trust service requirements in defined systems and processes. It has a specific application where service givers are dealing with consumer records.
5) PCI-DSS
PCI-DSS outlines the security measures of organisations that process, store, or transmit information in payment cards. It requires encryption, access control, monitoring of the network, and a protective firewall. Compliance ensures secure handling of cardholder data and reduces fraud risk.
6) COBIT
COBIT is an information technology governance and management Cyber Security Framework which matches IT objectives to business objectives. It consists of control objectives, process models and maturity assessments. The framework improves accountability, transparency, and performance of IT governance.
7) HITRUST CSF
The HITRUST Common Security Framework (CSF) is a certifiable framework of standards, which is a combination of ISO, NIST, HIPAA and GDPR. This Cyber Security Framework will provide a dynamic method of compliance and risk management. Its combined structure allows its application in industries that process sensitive health and regulatory data.
8) CCM
The CCM is a cloud-based security controls model created to deal with cloud governance, risk and compliance. CCM Cyber Security Framework offers organised areas that govern safe cloud service deployment. Many companies across the world rely on CCM as a measure of cloud security practises.
9) CMMC 2.0
The Cybersecurity Maturity Model Certification (CMMC) 2.0 is a security model that was initiated by the U.S. Department of Defence to enhance security in the Defence Industrial Base. It establishes several maturity levels with particular practises needed. This Cyber Security Framework helps in ascertaining that contractors comply with the set security standards when using sensitive defence information.
10) Cyber Essentials
The Cyber Essentials is a certification scheme supported by the UK government and aims to secure organisations against general cyber attacks. It presupposes the use of minimum controls on firewalls, secure settings, and software upgrades. The scheme aids organisations in portraying some basic cybersecurity preparedness.
Develop core digital investigation skills with our Computer Forensics Foundation Training Course- Join now!
How to Implement and Maintain a Cyber Security Framework
A Cyber Security Framework is a structured process that needs to be executed in a disciplined manner and monitored continuously. It should be incorporated into the daily operations to deliver measurable risk reduction after it is chosen.
These are the keyways to implement and maintain a Cybersecurity Framework:
1) Identify Scope and Objectives: Provide an alignment between the framework and business objectives, risk appetite, and regulatory provisions.
2) Establish Governance Structures: Establish leadership and operational roles and responsibilities as well as accountability.
3) Risk Assessment: Determine assets, threats, vulnerabilities, and focus on mitigation processes.
4) Establish Controls and Policies: Have deployed administrative, physical, and technical controls that are necessitated by the framework.
5) Train Employees: Awareness and compliance with security policies and best practises of the workforce.
6) Carry Out Frequent Audits: determine performance, identify flaws and assess performance conformance.
7) Monitor And Improve Continuously: Enhance controls, policies and procedures to meet new threats and business requirements.
Strengthen your breach response strategy with our Incident Response Training Course - Sign up now!
Conclusion
A Cyber Security Framework provides the structure organisations need to manage evolving digital threats with clarity and consistency. By defining controls, aligning governance, and continuously monitoring risks, businesses can strengthen resilience and protect sensitive data effectively. Selecting the right framework and maintaining it through regular audits ensures long-term security readiness. Ultimately, a proactive approach to cyber security safeguards both operational continuity and organisational reputation.
Build a security-first culture and protect your organisation from everyday cyber threats with our Cyber Security Awareness - Join today!
Frequently Asked Questions
What are the Main Components of a Cyber Security Framework?

A cyber security framework typically consists of risk assessment, the establishment of policies and procedures, implementation of security controls, continuous monitoring and threat detection, incident response planning, and ongoing improvement. Together, these elements form a structured and resilient approach to managing cyber security risks.
How Can a Cyber Security Framework Help Protect my Organisation Against Cyber Threats?

A cyber security framework enables organisations to systematically identify and evaluate risks and vulnerabilities across their systems and operations. By applying its recommended standards and best practices, organisations can enhance their security posture and reduce the likelihood of threats such as data breaches, malware infections, and phishing attacks.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Cyber Security Courses, including the Cyber Security Awareness Course, Fraud Analytics Training Course, and Cyber Security Risk Management Course. These courses cater to different skill levels, providing comprehensive insights into Importance of Cyber Security.
Our IT Security & Data Protection Blogs cover a range of topics related to Cyber Security, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Cyber Security skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

John Davies is a cybersecurity expert specialising in governance, risk management, and compliance. With over 15 years in the field, he has led enterprise-wide security programmes across finance, healthcare and public sector organisations. His content provides practical guidance on building secure environments, managing risk and aligning with regulatory frameworks.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Certified Cyber Security Professional (CCS-PRO)
Certified Cyber Security Professional (CCS-PRO)
Fri 28th Aug 2026
Fri 25th Sep 2026





 Top Rated Course
Top Rated Course





 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


