 To help and support our clients we are providing a limited number of 250 daily discount codes. Hurry, first come, first served!
To help and support our clients we are providing a limited number of 250 daily discount codes. Hurry, first come, first served!
CCSP Training FAQs
CCSP Training focuses on securing cloud environments through governance, risk management, and compliance practices. It builds the knowledge required to design, manage, and protect cloud-based systems effectively.
The training covers Cloud Concepts and Architecture, Cloud Data Security, Cloud Platform Security, Cloud Application Security, Cloud Security Operations, Legal, Risk, and Compliance. These domains provide a complete view of cloud security management.
The prerequisites for the CCSP Courses are based on the course specifications. Check the respective course page of the course that you are planning to take to know about its prerequisites.
Our CCSP Training is ideal for Cloud Security Professionals, IT Managers, Security Architects, and Risk or Compliance Specialists. It also suits professionals responsible for securing cloud-based systems.
In this CCSP Courses, delegates will receive intensive training from our experienced instructors, along with a digital delegate pack containing key notes to assist in completing the training.
The duration of CCSP Courses varies. Please visit our course pages for specific information.
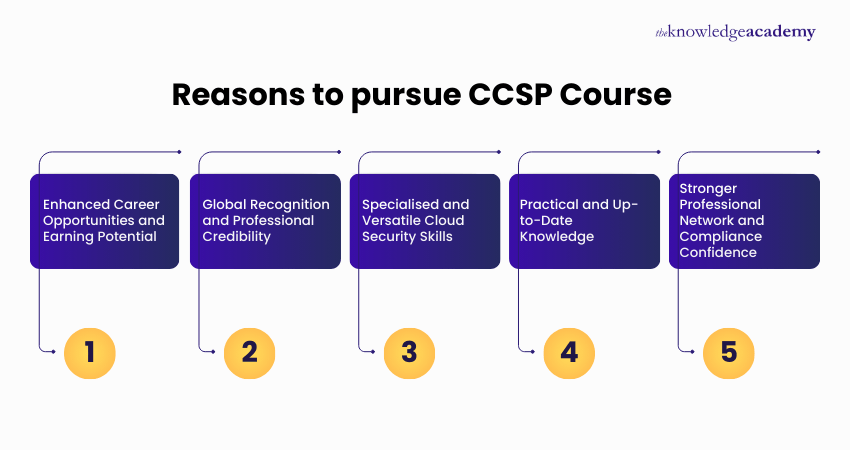
Delegates gain practical knowledge of cloud security, improve risk and compliance oversight, and strengthen their ability to manage secure cloud environments. The training supports confident decision-making in cloud-focused roles.
Delegates can pursue roles such as Cloud Security Specialist, Security Architect, Risk and Compliance Lead, or Cloud Governance Manager. These roles focus on protecting cloud platforms and organisational data.
Yes, The Knowledge Academy offers support via phone & email before attending, during, and after the CCSP Training. Our customer support team is available to assist and promptly resolve any issues you may encounter.
Delegates learn how to secure cloud platforms, manage cloud risk, implement governance controls, and protect sensitive data. The course also addresses operational security and compliance requirements.
CCSP Training is delivered through instructor-led classroom sessions and live virtual learning. Flexible delivery options allow delegates to choose the format that best suits their needs.
If you are unable to access your CCSP Courses, contact the support team at The Knowledge Academy via our customer service email or phone number provided on our website for prompt assistance and resolution of your issue.
CCSP training covers cloud security frameworks, data protection, compliance, threat mitigation, and risk management, making it essential for professionals securing cloud-based environments.
The Knowledge Academy in Mali stands out as a prestigious training provider known for its extensive course offerings, expert instructors, adaptable learning formats, and industry recognition. It's a dependable option for those seeking this course.
Please see our CCSP Training available in Mali
The Knowledge Academy is one of the Leading global training provider for CCSP Training.
The training fees for CCSP Training in Mali starts from $4695

Why we're the go to training provider for you

Best price in the industry
You won't find better value in the marketplace. If you do find a lower price, we will beat it.

Trusted & Approved
Recognised by leading certification bodies, we deliver training you can trust.

Many delivery methods
Flexible delivery methods are available depending on your learning style.
High quality resources
Resources are included for a comprehensive learning experience.




"Really good course and well organised. Trainer was great with a sense of humour - his experience allowed a free flowing course, structured to help you gain as much information & relevant experience whilst helping prepare you for the exam"
Joshua Davies, Thames Water


















 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


