We may not have the course you’re looking for. If you enquire or give us a call on 01344 203999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

In today’s digital age, safeguarding information is not just an IT task but a business imperative. Organisations face evolving cyber threats, making it important to identify vulnerabilities before they become costly breaches.
A thorough ISO 27001 Risk Assessment helps businesses pinpoint potential risks, implement strong controls, and keep sensitive data protected. In this blog, we will explore the steps, benefits, and best practices for this essential process.
Table of Contents
1) What is ISO 27001 Risk Assessment?
2) When Should you Conduct a Risk Assessment Under ISO 27001?
3) A Step-by-step Guide to the Risk Assessment Procedure
4) Examples of Risk Treatment
5) Difference Between Risk Assessment and Risk Treatment in ISO 27001?
6) Risk Management Procedure for Small or Medium Sized Organisations
7) Conclusion
What is ISO 27001 Risk Assessment?
An ISO 27001 Risk Assessment is a mandatory step for achieving ISO 27001 Certification. It involves identifying potential Information Security risks within your organisation. It involves assessing the likelihood of each risk occurring and estimating the potential impact on your operations.
It can offer a strategy that outlines how you'll address each risk to protect your business. Together, the Risk Assessment and risk treatment plan form the foundation of your ISO 27001 Risk management process.
Key Takeaways:
1) Defining clear criteria for evaluating risks
2) Identifying risks across all information assets within the ISMS scope
3) Assigning a responsible owner for each Risk
4) Establishing a consistent and repeatable Assessment process
When Should you Conduct a Risk Assessment Under ISO 27001?
A risk assessment isn’t a one‑time task, it’s an ongoing activity that supports continual improvement of your information security management system. However, there are specific times when conducting a risk assessment is especially important:
a) Before Implementing ISO 27001 as part of the Certification Process: This helps establish your baseline risk profile and informs which controls you need to apply.
b) Before Strategic Business Changes or Planned Shifts in your Security Landscape: Major initiatives like new systems, mergers, or infrastructure updates can introduce new risks that need evaluation.
c) After Security Incidents: Following any breach, incident, or near miss, reassessing risk helps you understand root causes and strengthen protections.
d) On a Regular Basis, Typically Annually: Recurring assessments let you stay ahead of evolving threats and maintain a clear view of your organisation’s risk profile and security posture.
This structured approach ensures your ISO 27001 Risk Assessment remains timely, relevant, and aligned with business and security objectives.
A Step-by-step Guide to the Risk Assessment Procedure
Risk Assessment is one of the most critical parts of implementing an Information Security Management System (ISMS) under ISO 27001. It ensures you understand your organisation’s security risks and manage them effectively. Here is the entire process step by step:
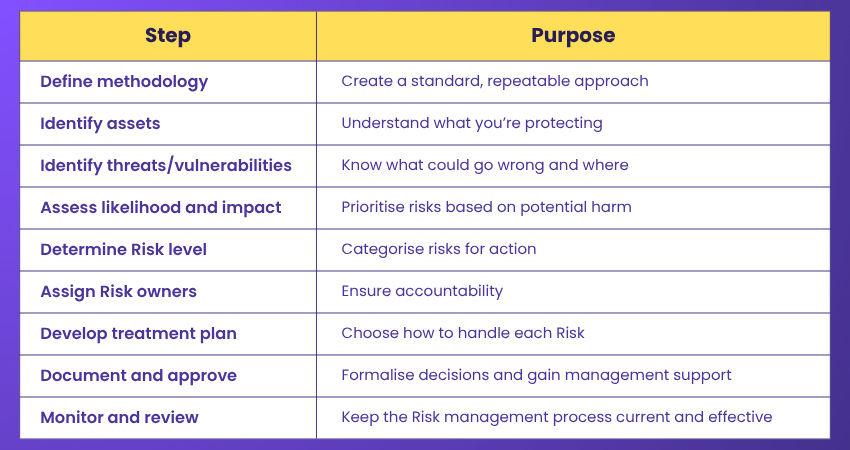
Step 1: Define the Risk Assessment Methodology
Before assessing any risks, you must establish how the Risk will be evaluated. Steps to follow:
1) Define how you’ll measure likelihood and impact (like on a scale from 1–5 or low/medium/high).
2) Determine what level of Risk is acceptable to the organisation. For instance, low risks might be acceptable, but medium or high risks will require action.
3) Choose Assessment type: Decide whether to use:
a) Qualitative Assessment (based on expert judgment and descriptive levels)
b) Quantitative Assessment (based on numbers, probabilities, and monetary values)
c) Hybrid method (combining both)
Tip: It ensures consistency, repeatability, and objectivity across all Risk Assessments
Step 2: Identify Information Assets
List every asset that is within the scope of your ISMS. Each asset should have an owner, someone responsible for protecting it. These can include:
1) Hardware like laptops, servers, mobile devices
2) Software including operating systems, cloud platforms, applications
3) Data as in customer data, intellectual property, contracts
4) People including staff, third-party vendors, consultants
5) Processes like communication protocols, payroll systems
6) Facilities as in data centres, office buildings
Tip: Use an asset register or inventory to keep this organised and up to date
Step 3: Identify Threats and Vulnerabilities
The next step is to determine what could go wrong with each asset. This step helps you understand where the risks are coming from. Key areas are:
1) Threats are potential events that can cause harm like hacking, human error, fire
2) Vulnerabilities are weaknesses that could be exploited like outdated software
3) Identify internal organisational threats like poor password policies
4) Examples are asset like Customer database and threat as in Data breach
5) Vulnerabilities are there which includes Unencrypted backups
Tip: Engage technical teams to uncover hidden vulnerabilities you may overlook
Know your weak spots before hackers do with our ISO 27001 Lead Auditor - Register today!
Step 4: Assess Likelihood and Impact
Accessing likelihood and positive impact, output is a prioritised list of risks. Assign a value to each identified Risk based on:
1) Likelihood: How probable is it that this Risk will occur?
2) Impact: If it happens, how severe would the effect be on your organisation?
3) The combination of likelihood and impact gives you a Risk rating or Risk score
4) Ensures that your organisation focuses on real, high-priority risks
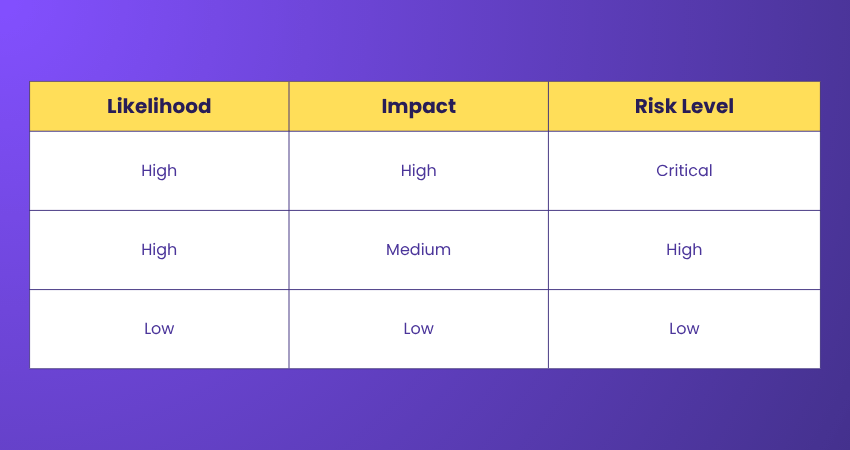
Tip: Use a simple matrix to visualise and compare Risk levels across assets
Step 5: Determine the Risk Level
Using the results from Step 4, calculate or rank the overall Risk level. It can be done by combining the likelihood and impact scores. This gives you a Risk register with categorised risks.
1) Low Risk may be accepted or monitored
2) Medium Risk may require treatment
3) High Risk must be treated immediately
4) It ensures compliance with ISO 27001 requirements
5) It forms the foundation for the next step, risk treatment planning
Tip: Standardise your scoring system to ensure consistency across departments
Step 6: Assign Risk Owners
Once each Risk has been identified, evaluated, and prioritised, the next essential step is to assign a Risk owner to every identified Risk. Steps are:
1) This ensures that someone is responsible for monitoring and managing
2) It treats the Risk as part of your ISO 27001 compliance process
3) Helps to evaluate the impact on their area of responsibility
4) Essential for ISO 27001 audits as each Risk are assigned and actively managed
Tip: Choose Risk owners who can implement controls, not just oversee them
Step 7: Create a Risk Treatment Plan
List all selected controls in a Risk Treatment Plan. These should align with ISO 27001 Annex A controls where applicable. Once you understand the risks, you must decide how to address them, as ISO 27001 requires choosing a treatment option for each unacceptable risk.
1) Avoid the risk by stopping or removing the activity causing it
2) Reduce the risk by implementing controls to lower likelihood or impact
3) Transfer the risk by shifting responsibility to a third party such as insurance or outsourcing
4) Accept the risk by acknowledging and monitoring it when it falls within acceptable limits
Tip: Align every treatment action with ISO 27001 Annex A controls for compliance and audit readiness.
Step 8: Approve and Document the Plan
This step demonstrates your commitment to ISO 27001 Compliance and shows auditors that you have a well-structured process in place. It is one of the crucial steps to document your findings and treatment decisions. This includes:
1) Your Risk Assessment report will be needed
2) Risk treatment plan is the most essential one to document
3) Control implementation strategies to approve the plan
4) Approval from top management is the key one
Tip: Use this step to secure buy-in and funding for critical control implementations
Step 9: Review, Monitor, and Conduct an Internal Audit
Regular review and monitoring ensure your ISMS remains effective and adapts to changing risks. Internal audits confirm that your ISMS meets ISO 27001 requirements and is being maintained properly.
1) Review the ISMS at planned intervals to keep it updated and effective.
2) Monitor controls and risk treatments continuously to track performance.
3) Conduct internal audits to assess whether the ISMS complies with ISO 27001 and internal requirements.
4) Document audit findings and report them to management for improvement actions.
Tip: Schedule internal audits at predetermined intervals to ensure consistent compliance and ongoing ISMS improvement.
Examples of Risk Treatment
Here are some of the real-life examples of Risk Treatment:

1) Risk Avoidance
Action: Stop the activity that causes the Risk.
Example: Discontinue the use of outdated legacy systems that pose unmatchable security vulnerabilities.
Tip: Use this when the Risk is too high and there’s no effective way to reduce it.
2) Risk Reduction
Action: Apply controls to reduce the likelihood or impact of the risk.
Example: Install firewalls, antivirus software, or enforce multi-factor authentication to prevent unauthorised access.
Tip: This is the most common treatment method in ISO 27001.
3) Risk Transfer
Action: Shift the Risk to a third party.
Example: Purchase cyber insurance or outsource data storage to a certified cloud provider.
Tip: This doesn’t eliminate the Risk as it shares responsibility.
4) Risk Acceptance
Action: Acknowledge the Risk and take no immediate action.
Example: Accepting a low-level Risk of phishing email delivery after awareness training and email filtering.
Tip: Accept only if the Risk falls within your defined Risk tolerance.
Difference Between Risk Assessment and Risk Treatment in ISO 27001?
In ISO 27001, a risk assessment helps you identify, analyse, and evaluate threats, vulnerabilities, and their potential impact on your information assets to understand which risks matter most. Once these risks are prioritised, risk treatment focuses on deciding how to address them by choosing options such as mitigation, avoidance, transfer, or acceptance and documenting these actions in a formal treatment plan.
Risk Management Procedure for Small or Medium Sized Organisations
Effective Risk Management is essential for SMEs to protect sensitive information, maintain customer trust, and comply with regulations like ISO 27001. The process doesn't have to be overly complex, it just needs to be systematic, consistent, and documented.
Here's how to approach it step-by-step:
1) Decide which parts of the business the Risk process will cover like IT or HR
2) Appoint a Risk Owner or Manager. In small teams, this could be the CEO or IT lead
3) List critical assets like hardware, data, staff roles, and third-party services
4) For each asset, identify what could go wrong and why like data breach
5) Score each Risk using Impact (1–5) and Likelihood (1–5), then calculate total Risk score
6) Record all risks, their scores, owners, and planned treatments in a simple spreadsheet
7) Choose to Avoid, Reduce, Transfer, or Accept each Risk, based on its score
8) Implement realistic safeguards like encryption, backups, or access restrictions
9) Reassess risks periodically or after changes, and update the Risk register as needed
10) Keep all Assessments and reviews for ISO 27001 compliance and internal accountability
Conclusion
Hope this blog helped you gain clarity and confidence as you work toward strengthening your organisation’s security posture. By applying these principles consistently, you set the foundation for long‑term resilience and smarter decision‑making. Remember that ISO 27001 Risk Assessment is part of an ongoing journey, and every improvement you make today contributes to a safer tomorrow.
Build core auditing and compliance skills with the ISO 27001 Internal Auditor Training – Join now!
Frequently Asked Questions
How does ISO 27001 Risk Assessment Differ from Other Risk Management Frameworks?

ISO 27001's Risk Assessment is specific to information security within an Information Security Management System, focusing on confidentiality, integrity, and availability, requiring periodic ISMS reviews, distinguishing it from broader Risk management frameworks.
How Often Should Risk Assessments be Conducted Under ISO 27001?

Under ISO 27001, Risk Assessments should be conducted at regular intervals or when significant changes occur that could affect information security. This ensures the ISMS remains effective and responsive to new threats, aligning with the organisation's evolving security posture and compliance requirements.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000+ online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like Blogs, eBooks, Interview Questions and Videos. Tailoring learning experiences further, professionals can unlock greater value through a wide range of special discounts, seasonal deals, and Exclusive Offers.
What is the Knowledge Pass, and how does it work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are the related courses and blogs provided by The Knowledge Academy?

The Knowledge Academy offers various ISO 27001 Training, including the ISO 27001 Foundation, ISO 27001 Lead Auditor Course Outline and the ISO 27001 Internal Auditor. These courses cater to different skill levels, providing comprehensive insights into Multi-Factor Authentication (MFA).
Our IT Security & Data Protection Blogs cover a range of topics related to technological advancements, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Risk Assessment skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.

The Knowledge Academy is a world-leading provider of professional training courses, offering globally recognised qualifications across a wide range of subjects. With expert trainers, up-to-date course material, and flexible learning options, we aim to empower professionals and organisations to achieve their goals through continuous learning.

Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 ISO 27001 Foundation
ISO 27001 Foundation
Mon 1st Jun 2026
Mon 3rd Aug 2026
Mon 12th Oct 2026
Mon 14th Dec 2026





 Top Rated Course
Top Rated Course








 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


